|
EnRUPT
EnRUPT is a block cipher and a family of cryptographic algorithms based on XXTEA. EnRUPT hash function was submitted to SHA-3 competition The NIST hash function competition was an open competition held by the US National Institute of Standards and Technology (NIST) to develop a new hash function called SHA-3 to complement the older SHA-1 and SHA-2. The competition was formally ann ... but it wasn't selected to the second round. References Broken block ciphers Feistel ciphers Articles with example C code {{crypto-stub ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SHA-3 Competition
The NIST hash function competition was an open competition held by the US National Institute of Standards and Technology (NIST) to develop a new hash function called SHA-3 to complement the older SHA-1 and SHA-2. The competition was formally announced in the ''Federal Register'' on November 2, 2007. "NIST is initiating an effort to develop one or more additional hash algorithms through a public competition, similar to the development process for the Advanced Encryption Standard (AES)." The competition ended on October 2, 2012 when NIST announced that Keccak would be the new SHA-3 hash algorithm. The winning hash function has been published as NIST FIPS 202 the "SHA-3 Standard", to complement FIPS 180-4, the '' Secure Hash Standard''. The NIST competition has inspired other competitions such as the Password Hashing Competition. Process Submissions were due October 31, 2008 and the list of candidates accepted for the first round was published on December 9, 2008. NIST held a con ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
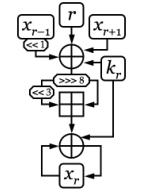
Algorithm Diagram For EnRUPT
In mathematics and computer science, an algorithm () is a finite sequence of rigorous instructions, typically used to solve a class of specific problems or to perform a computation. Algorithms are used as specifications for performing calculations and data processing. More advanced algorithms can perform automated deductions (referred to as automated reasoning) and use mathematical and logical tests to divert the code execution through various routes (referred to as automated decision-making). Using human characteristics as descriptors of machines in metaphorical ways was already practiced by Alan Turing with terms such as "memory", "search" and "stimulus". In contrast, a heuristic is an approach to problem solving that may not be fully specified or may not guarantee correct or optimal results, especially in problem domains where there is no well-defined correct or optimal result. As an effective method, an algorithm can be expressed within a finite amount of space and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Feistel Cipher
In cryptography, a Feistel cipher (also known as Luby–Rackoff block cipher) is a symmetric structure used in the construction of block ciphers, named after the German-born physicist and cryptographer Horst Feistel, who did pioneering research while working for IBM; it is also commonly known as a Feistel network. A large proportion of block ciphers use the scheme, including the US Data Encryption Standard, the Soviet/Russian GOST and the more recent Blowfish and Twofish ciphers. In a Feistel cipher, encryption and decryption are very similar operations, and both consist of iteratively running a function called a "round function" a fixed number of times. History Many modern symmetric block ciphers are based on Feistel networks. Feistel networks were first seen commercially in IBM's Lucifer cipher, designed by Horst Feistel and Don Coppersmith in 1973. Feistel networks gained respectability when the U.S. Federal Government adopted the DES (a cipher based on Lucifer, with changes m ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Broken Block Ciphers
Broken may refer to: Literature * ''Broken'' (Armstrong novel), a 2006 novel by Kelley Armstrong in the ''Women of the Otherworld'' series * ''Broken'' (Slaughter novel), a 2010 novel by Karin Slaughter Music Albums * '' Broken (And Other Rogue States)'', a 2005 album by Luke Doucet * ''Broken'' (MBLAQ EP) (2014) * ''Broken'' (Nine Inch Nails EP), (1992) * ''Broken'' (Soulsavers album) (2009) * ''Broken'' (Straight Faced album) (1996) Songs * "Broken" (Jake Bugg song) (2013) * "Broken" (Sam Clark song) (2009) * "Broken" (Coldplay song) (2019) * "Broken" (Elisa song) (2003) * "Broken" (Lifehouse song) (2008) * "Broken" (lovelytheband song) (2017) * "Broken" (Kate Ryan song) (2011) * "Broken" (Seether song) (2004) * "Broken" (Slander and Kompany song) (2019) * "Broken", by 12 Stones from ''12 Stones'' * "Broken", by All That Remains from ''Victim of the New Disease'' * "Broken", by David Archuleta from '' Begin'' * "Broken", by Bad Religion from '' The Pro ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Feistel Ciphers
Feistel is a German surname. Notable people with the surname include: *Horst Feistel (1915–1990), German American cryptographer **Feistel cipher, a construction for designing modern ciphers *Magdalena Feistel Magdalena Feistel (born Magdalena Mróz 22 August 1970) is a former Polish tennis player. She holds the record for most Fed Cup ties played for Poland (24; 43 matches) and most Fed Cup wins for Poland (23). In her career, she won one singles ... (born 1970), Polish tennis player {{surname, Feistel German-language surnames ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |