|
EAX Mode
EAX mode (encrypt-then-authenticate-then-translate) is a mode of operation for cryptographic block ciphers. It is an Authenticated Encryption with Associated Data (AEAD) algorithm designed to simultaneously provide both authentication and privacy of the message (authenticated encryption) with a two-pass scheme, one pass for achieving privacy and one for authenticity for each block. EAX mode was submitted on October 3, 2003 to the attention of NIST in order to replace CCM as standard AEAD mode of operation, since CCM mode lacks some desirable attributes of EAX and is more complex. Encryption and authentication EAX is a flexible nonce-using two-pass AEAD scheme with no restrictions on block cipher primitive to be used, nor on block size, and supports arbitrary-length messages. Authentication tag length is arbitrarily sizeable up to the used cipher's block size. The block cipher primitive is used in CTR mode for encryption and as OMAC for authentication over each block through ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mode Of Operation
In cryptography, a block cipher mode of operation is an algorithm that uses a block cipher to provide information security such as confidentiality or authenticity. A block cipher by itself is only suitable for the secure cryptographic transformation (encryption or decryption) of one fixed-length group of bits called a block. A mode of operation describes how to repeatedly apply a cipher's single-block operation to securely transform amounts of data larger than a block. Most modes require a unique binary sequence, often called an initialization vector (IV), for each encryption operation. The IV has to be non-repeating and, for some modes, random as well. The initialization vector is used to ensure distinct ciphertexts are produced even when the same plaintext is encrypted multiple times independently with the same key. Block ciphers may be capable of operating on more than one block size, but during transformation the block size is always fixed. Block cipher modes operate on ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
CTR Mode
In cryptography, a block cipher mode of operation is an algorithm that uses a block cipher to provide information security such as confidentiality or authenticity. A block cipher by itself is only suitable for the secure cryptographic transformation (encryption or decryption) of one fixed-length group of bits called a block. A mode of operation describes how to repeatedly apply a cipher's single-block operation to securely transform amounts of data larger than a block. Most modes require a unique binary sequence, often called an initialization vector (IV), for each encryption operation. The IV has to be non-repeating and, for some modes, random as well. The initialization vector is used to ensure distinct ciphertexts are produced even when the same plaintext is encrypted multiple times independently with the same key. Block ciphers may be capable of operating on more than one block size, but during transformation the block size is always fixed. Block cipher modes operate on ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Stefan Lucks
Stefan Lucks is a researcher in the fields of communications security and cryptography. Lucks is known for his attack on Triple DES, and for extending Lars Knudsen's Square attack to Twofish, a cipher outside the Square family, thus generalising the attack into integral cryptanalysis. He has also co-authored attacks on AES, LEVIATHAN, and the E0 cipher used in Bluetooth devices, as well as publishing strong password-based key agreement schemes. Lucks graduated from the University of Dortmund in 1992, and received his PhD at the University of Göttingen in 1997. After leaving the University of Mannheim Lucks now heads the Chair of Media Security at Bauhaus University, Weimar. Together with Niels Ferguson, Bruce Schneier and others he developed the Skein hash function as a candidate for the NIST hash function competition The NIST hash function competition was an open competition held by the US National Institute of Standards and Technology (NIST) to develop a new hash f ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
ANSI C12
The American National Standards Institute (ANSI ) is a private non-profit organization that oversees the development of voluntary consensus standards for products, services, processes, systems, and personnel in the United States. The organization also coordinates U.S. standards with international standards so that American products can be used worldwide. ANSI accredits standards that are developed by representatives of other standards organizations, government agencies, consumer groups, companies, and others. These standards ensure that the characteristics and performance of products are consistent, that people use the same definitions and terms, and that products are tested the same way. ANSI also accredits organizations that carry out product or personnel certification in accordance with requirements defined in international standards. The organization's headquarters are in Washington, D.C. ANSI's operations office is located in New York City. The ANSI annual operating b ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
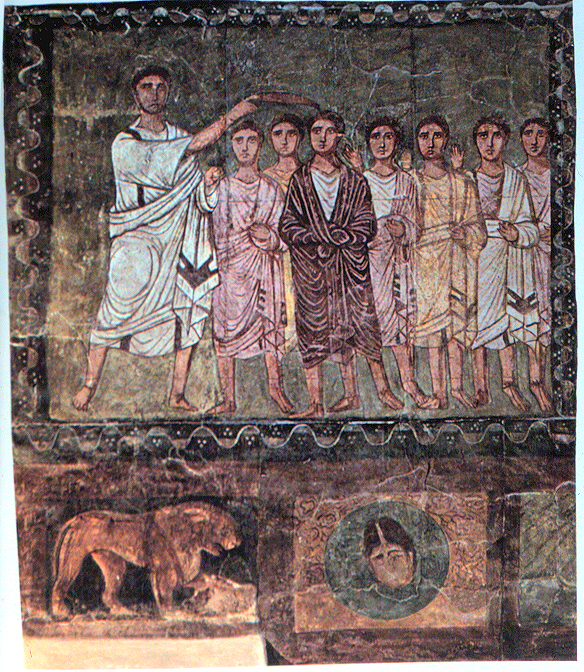
David A
David (; , "beloved one") (traditional spelling), , ''Dāwūd''; grc-koi, Δαυΐδ, Dauíd; la, Davidus, David; gez , ዳዊት, ''Dawit''; xcl, Դաւիթ, ''Dawitʿ''; cu, Давíдъ, ''Davidŭ''; possibly meaning "beloved one". was, according to the Hebrew Bible, the third king of the United Kingdom of Israel. In the Books of Samuel, he is described as a young shepherd and harpist who gains fame by slaying Goliath, a champion of the Philistines, in southern Canaan. David becomes a favourite of Saul, the first king of Israel; he also forges a notably close friendship with Jonathan, a son of Saul. However, under the paranoia that David is seeking to usurp the throne, Saul attempts to kill David, forcing the latter to go into hiding and effectively operate as a fugitive for several years. After Saul and Jonathan are both killed in battle against the Philistines, a 30-year-old David is anointed king over all of Israel and Judah. Following his rise to power, David ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Phillip Rogaway
Phillip Rogaway is a professor of computer science at the University of California, Davis. He graduated from Beverly Hills High School, and later earned a BA in computer science from UC Berkeley and completed his PhD in cryptography at MIT, in the Theory of Computation group. He has taught at UC Davis since 1994. He was awarded the Paris Kanellakis Award in 2009 and the first Levchin Prize for Real World Cryptography in 2016. Rogaway received an NSF CAREER award in 1996, which the NSA had attempted to prevent by influencing the NSF. He has been interviewed in multiple media outlets regarding his stance on the ethical obligations that cryptographers and computer scientists have to serve to the public good, specifically in the areas of internet privacy and digital surveillance. Rogaway's papers cover topics including: * CMAC * Concrete security * DES and DES-X * Format-preserving encryption * OCB mode * Random oracle model * SEAL * UMAC * Zero-knowledge proofs In cryptogr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mihir Bellare
Mihir Bellare is a cryptographer and professor at the University of California San Diego. He has published several seminal papers in the field of cryptography (notably in the area of provable security), many of which were co-written with Phillip Rogaway. Bellare has published a number of papers in the field of Format-Preserving Encryption. His students include Michel Abdalla, Chanathip Namprempre, Tadayoshi Kohno and Anton Mityagin. Bellare is one of the authors of skein. In 2003 Bellare was a recipient of RSA's Sixth Annual Conference Award for outstanding contributions in the field of mathematics for his research in cryptography. In 2013 he became a Fellow of the Association for Computing Machinery. In 2019 he was awarded Levchin Prize for Real-World Cryptography for his outstanding contributions to the design and analysis of real-world cryptosystems, including the development of random oracle model, modes of operation, HMAC, and models for key exchange. Bellare's papers cover ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
One-key MAC
One-key MAC (OMAC) is a message authentication code constructed from a block cipher much like the CBC-MAC algorithm. Officially there are two OMAC algorithms (OMAC1 and OMAC2) which are both essentially the same except for a small tweak. OMAC1 is equivalent to CMAC, which became an NIST recommendation in May 2005. It is free for all uses: it is not covered by any patents. In cryptography, CMAC is a block cipher-based message authentication code algorithm. It may be used to provide assurance of the authenticity and, hence, the integrity of data. This mode of operation fixes security deficiencies of CBC-MAC (CBC-MAC is secure only for fixed-length messages). The core of the CMAC algorithm is a variation of CBC-MAC that Black and Rogaway proposed and analyzed under the name XCBC and submitted to NIST. The XCBC algorithm efficiently addresses the security deficiencies of CBC-MAC, but requires three keys. Iwata and Kurosawa proposed an improvement of XCBC and named the resulting algor ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptographic Nonce
In cryptography, a nonce is an arbitrary number that can be used just once in a cryptographic communication. It is often a random or pseudo-random number issued in an authentication protocol to ensure that old communications cannot be reused in replay attacks. They can also be useful as initialization vectors and in cryptographic hash functions. Definition A nonce is an arbitrary number used only once in a cryptographic communication, in the spirit of a nonce word. They are often random or pseudo-random numbers. Many nonces also include a timestamp to ensure exact timeliness, though this requires clock synchronisation between organisations. The addition of a client nonce ("cnonce") helps to improve the security in some ways as implemented in digest access authentication. To ensure that a nonce is used only once, it should be time-variant (including a suitably fine-grained timestamp in its value), or generated with enough random bits to ensure a insignificantly low chance of re ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
International Association For Cryptologic Research
International is an adjective (also used as a noun) meaning "between nations". International may also refer to: Music Albums * ''International'' (Kevin Michael album), 2011 * ''International'' (New Order album), 2002 * ''International'' (The Three Degrees album), 1975 *''International'', 2018 album by L'Algérino Songs * The Internationale, the left-wing anthem * "International" (Chase & Status song), 2014 * "International", by Adventures in Stereo from ''Monomania'', 2000 * "International", by Brass Construction from ''Renegades'', 1984 * "International", by Thomas Leer from ''The Scale of Ten'', 1985 * "International", by Kevin Michael from ''International'' (Kevin Michael album), 2011 * "International", by McGuinness Flint from ''McGuinness Flint'', 1970 * "International", by Orchestral Manoeuvres in the Dark from '' Dazzle Ships'', 1983 * "International (Serious)", by Estelle from '' All of Me'', 2012 Politics * Political international, any transnational organization of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
EAX Block Cipher Mode Of Operation , class 5 digital telephone switch typically used in former GTE service areas
{{Disambiguation ...
EAX may refer to: * EAX mode, a mode of operation for cryptographic block ciphers * EAX register, a 32-bit processor register of x86 CPUs * Environmental Audio Extensions, a number of digital signal processing presets for audio, found in Sound Blaster sound cards * GTD-5 EAX The GTD-5 EAX (General Telephone Digital Number 5 Electronic Automatic Exchange) is the Class 5 telephone switch, Class 5 telephone switch developed by GTE Automatic Electric Laboratories. This Digital data, digital telephone exchange, central off ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
CCM Mode
CCM mode (counter with cipher block chaining message authentication code; counter with CBC-MAC) is a mode of operation for cryptographic block ciphers. It is an authenticated encryption algorithm designed to provide both authentication and confidentiality. CCM mode is only defined for block ciphers with a block length of 128 bits. The nonce of CCM must be carefully chosen to never be used more than once for a given key. This is because CCM is a derivation of counter (CTR) mode and the latter is effectively a stream cipher. Encryption and authentication As the name suggests, CCM mode combines counter (CTR) mode for confidentiality with cipher block chaining message authentication code (CBC-MAC) for authentication. These two primitives are applied in an "authenticate-then-encrypt" manner: CBC-MAC is first computed on the message to obtain a message authentication code (MAC), then the message and the MAC are encrypted using counter mode. The main insight is that the same encry ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |