|
Dnsbl
A Domain Name System blocklist, Domain Name System-based blackhole list, Domain Name System blacklist (DNSBL) or real-time blackhole list (RBL) is a service for operation of mail servers to perform a check via a Domain Name System (DNS) query whether a sending host's IP address is blacklisted for email spam. Most mail server software can be configured to check such lists, typically rejecting or flagging messages from such sites. A DNSBL is a software mechanism, rather than a specific list or policy. Dozens of DNSBLs exist. They use a wide array of criteria for listing and delisting addresses. These may include listing the addresses of zombie computers or other machines being used to send spam, Internet service providers (ISPs) who willingly host spammers, or those which have sent spam to a honeypot system. Since the creation of the first DNSBL in 1998, the operation and policies of these lists have frequently been controversial, both in Internet advocacy circles and occasionally ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
The Spamhaus Project
The Spamhaus Project is an international organisation based in the Principality of Andorra, founded in 1998 by Steve Linford to track email spammers and spam-related activity. The name ''spamhaus'', a pseudo-German expression, was coined by Linford to refer to an internet service provider, or other firm, which spams or knowingly provides service to spammers. Anti-spam lists The Spamhaus Project is responsible for compiling several widely used anti-spam lists. Many internet service providers and email servers use the lists to reduce the amount of spam that reaches their users. In 2006, the Spamhaus services protected 650 million email users, including the European Parliament, US Army, the White House and Microsoft, from billions of spam emails a day. Spamhaus distributes the lists in the form of DNS-based Blacklists ( DNSBLs) and Whitelists ( DNSWLs). The lists are offered as a free public service to low-volume mail server operators on the Internet. Commercial spam filtering ser ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Black Hole (networking)
In networking, a black hole refers to a place in the network where incoming or outgoing traffic is silently discarded (or "dropped"), without informing the source that the data did not reach its intended recipient. When examining the topology of the network, the black holes themselves are invisible, and can only be detected by monitoring the lost traffic; hence the name as astronomical Black holes cannot be directly observed. Dead addresses The most common form of black hole is simply an IP address that specifies a host machine that is not running or an address to which no host has been assigned. Even though TCP/IP provides a means of communicating the delivery failure back to the sender via ICMP, traffic destined for such addresses is often just dropped. Note that a dead address will be undetectable only to protocols that are both connectionless and unreliable (e.g., UDP). Connection-oriented or reliable protocols (TCP, RUDP) will either fail to connect to a dead addr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SURBL
SURBL (previously stood for Spam URI RBL) is a collection of URI DNSBL lists of Uniform Resource Identifier (URI) hosts, typically web site domains, that appear in unsolicited messages. SURBL can be used to search incoming e-mail message bodies for spam payload links to help evaluate whether the messages are unsolicited. For example, if ''http://www.example.com'' is listed, then e-mail messages with a message body containing this URI may be classified as unsolicited. URI DNSBLs differ from prior DNSBLs, which commonly list mail sending IP addresses. SURBL is a specific instance of the general URI DNSBL list type. Lists SURBL provides lists of different types: * ABUSE - spam and abuse sites * PH - phishing sites * MW - malware sites * CR - cracked sites All lists are gathered into ''multi.surbl.org''. Usage A DNS query of a domain or IP address taken from a URI can be sent in the form of ''spamdomain.example.multi.surbl.org'' or ''4.3.2.1.multi.surbl.org''. The multi DNS z ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email Spam
Email spam, also referred to as junk email, spam mail, or simply spam, is unsolicited messages sent in bulk by email (spamming). The name comes from a Monty Python sketch in which the name of the canned pork product Spam is ubiquitous, unavoidable, and repetitive. Email spam has steadily grown since the early 1990s, and by 2014 was estimated to account for around 90% of total email traffic. Since the expense of the spam is borne mostly by the recipient, it is effectively postage due advertising. This makes it an excellent example of a negative externality. The legal definition and status of spam varies from one jurisdiction to another, but nowhere have laws and lawsuits been particularly successful in stemming spam. Most email spam messages are commercial in nature. Whether commercial or not, many are not only annoying as a form of attention theft, but also dangerous because they may contain links that lead to phishing web sites or sites that are hosting malware or includ ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Osirusoft
The Spam Prevention Early Warning System (SPEWS) was an anonymous service that maintained a list of IP address ranges belonging to internet service providers (ISPs) that host spammers and show little action to prevent their abuse of other networks' resources. It could be used by Internet sites as an additional source of information about the senders of unsolicited bulk email, better known as spam. SPEWS is no longer active. A successor, the Anonymous Postmaster Early Warning System (APEWS), appeared in January 2007. Overview SPEWS itself published a large text file containing its listings, and operated a database where web users could query the reasons for a listing. Users of SPEWS could access these data via DNS for use by software for DNSBL anti-spam techniques. For instance, many mail sites used the SPEWS data provided at spews.relays.osirusoft.com. All DNSBLs hosted by Osirusoft were shut down on August 27, 2003 after several weeks of denial of service attacks. A num ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Spam Prevention Early Warning System
The Spam Prevention Early Warning System (SPEWS) was an anonymous service that maintained a list of IP address ranges belonging to internet service providers (ISPs) that host spammers and show little action to prevent their abuse of other networks' resources. It could be used by Internet sites as an additional source of information about the senders of unsolicited bulk email, better known as spam. SPEWS is no longer active. A successor, the Anonymous Postmaster Early Warning System (APEWS), appeared in January 2007. Overview SPEWS itself published a large text file containing its listings, and operated a database where web users could query the reasons for a listing. Users of SPEWS could access these data via DNS for use by software for DNSBL anti-spam techniques. For instance, many mail sites used the SPEWS data provided at spews.relays.osirusoft.com. All DNSBLs hosted by Osirusoft were shut down on August 27, 2003 after several weeks of denial of service attacks. A num ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Mail Abuse Prevention System
The Mail Abuse Prevention System (MAPS) is an organization that provides anti-spam support by maintaining a DNSBL. They provide five black lists, categorising why an address or an IP block is listed: * Real-time Blackhole List (RBL), the one for which MAPS is probably best known. * Dialup Users List (DUL), blocks of addresses that include many SOHO users. * Relay Spam Stopper (RSS), spam relays, e.g. ''hijacked'' servers. * Open Proxy Servers (OPS), naively open SMTP servers. * Non-confirming Mailing List (NML), marketers who use opt-out strategy. The acronym MAPS is spam spelled backwards. History MAPS was founded in 1996 as a non-profit organization to pioneer innovative anti-spam techniques (e-mail). The early history of MAPS is the History of DNSBLs itself. Dave Rand and Paul Vixie, well known Internet software engineers, started keeping a list of IP addresses which had sent out spam or engaged in other behavior they found objectionable. The list became known as the ''Real ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Open Relay Behavior-modification System
Open Relay Behavior-modification System (ORBS), created and run by Alan Brown in New Zealand, was one of the first DNS-based Blackhole Lists (DNSBL), a means by which an internet domain may publish a list of IP addresses, in a database which can be easily queried automatically by other computer programs on the Internet. The ORBS list was used to blacklist IP addresses that were open mail relays, third-party mail servers through which spammers can relay their messages and thus attempt to obfuscate the source of the spam. Controversy The ORBS list was controversial for a number of reasons. Many people felt that the methods ORBS employed to scan the Internet for open mail servers could be abusive. ORBS used probes to test for open relays without permission, sometimes over and over again. Some claimed that testing of their networks continued even after they asked ORBS to stop, others claimed that relayed spam didn't stop either. In some cases the tests interfered with mail servers ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Open Mail Relay
An open mail relay is a Simple Mail Transfer Protocol (SMTP) server configured in such a way that it allows anyone on the Internet to send e-mail through it, not just mail destined to or originating from known users. This used to be the default configuration in many mail servers; indeed, it was the way the Internet was initially set up, but open mail relays have become unpopular because of their exploitation by spammers and worms. Many relays were closed, or were placed on blacklists by other servers. History and technology Until the 1990s, mail servers were commonly intentionally configured as open relays; in fact, this was frequently the installation default setting. The traditional store and forward method of relaying e-mail to its destination required that it was passed from computer to computer (through and beyond the Internet) via modems on telephone lines. For many early networks, such as UUCPNET, FidoNet and BITNET, lists of machines that were open relays were a core pa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Comparison Of Mail Servers
The comparison of mail servers covers mail transfer agents (MTAs), mail delivery agents, and other computer software that provide e-mail services. Unix-based mail servers are built using a number of components because a Unix-style environment is, by default, a toolbox operating system. A stock Unix-like server already has internal mail; more traditional ones also come with a full MTA already part of the standard installation. To allow the server to send external emails, an MTA such as Sendmail, Postfix, or Exim is required. Mail is read either through direct access (shell login) or mailbox protocols like POP and IMAP. Unix-based MTA software largely acts to enhance or replace the respective system's native MTA. Microsoft Windows servers do not natively implement e-mail, thus Windows-based MTAs have to supply all the necessary aspects of e-mail-related functionality. Feature comparison Authentication Antispam features See also * Comparison of email clients * L ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
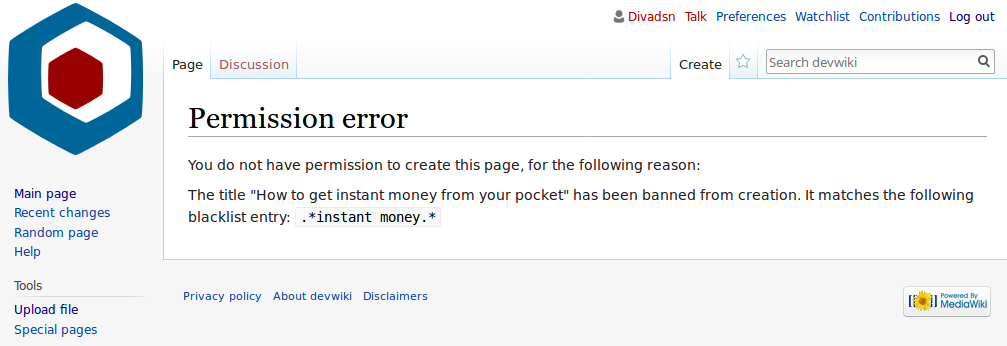
Blacklist (computing)
In computing, a blacklist, disallowlist, blocklist, or denylist is a basic access control mechanism that allows through all elements (email addresses, users, passwords, URLs, IP addresses, domain names, file hashes, etc.), except those explicitly mentioned. Those items on the list are denied access. The opposite is a whitelist, allowlist, or passlist, in which only items on the list are let through whatever gate is being used. A greylist contains items that are temporarily blocked (or temporarily allowed) until an additional step is performed. Blacklists can be applied at various points in a security architecture, such as a host, web proxy, DNS servers, email server, firewall, directory servers or application authentication gateways. The type of element blocked is influenced by the access control location. DNS servers may be well-suited to block domain names, for example, but not URLs. A firewall is well-suited for blocking IP addresses, but less so for blocking malicious fi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Spamassassin
Apache SpamAssassin is a computer program used for e-mail spam filtering. It uses a variety of spam-detection techniques, including DNS and fuzzy checksum techniques, Bayesian filtering, external programs, blacklists and online databases. It is released under the Apache License 2.0 and is a part of the Apache Foundation since 2004. The program can be integrated with the mail server to automatically filter all mail for a site. It can also be run by individual users on their own mailbox and integrates with several mail programs. Apache SpamAssassin is highly configurable; if used as a system-wide filter it can still be configured to support per-user preferences. History Apache SpamAssassin was created by Justin Mason, who had maintained a number of patches against an earlier program named ''filter.plx'' by Mark Jeftovic, which in turn was begun in August 1997. Mason rewrote all of Jeftovic's code from scratch and uploaded the resulting codebase to SourceForge on April 20, 2 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |