|
DomPlayer
3wPlayer is malware that disguises itself as a Media player. It can infect computers running Microsoft Windows. It is designed to exploit users who download video files, instructing them to download and install the program in order to view the video. The 3wPlayer employs a form of social engineering to infect computers. Seemingly desirable video files, such as recent movies, are released via BitTorrent or other distribution channels. These files resemble conventional AVI files, but are engineered to display a message when played on most media player programs, instructing the user to visit the 3wPlayer website and download the software to view the video. The 3wPlayer is infected with Trojan.Win32.Obfuscated.en According to Symantec, 3wPlayer "may download" a piece of adware they refer to as Adware.Lop, which "adds its own toolbar and search button to Internet Explorer". A Perl script posted online can reportedly decrypt 3wplayer files back into AVI. This claim has been tested wi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Divocodec
3wPlayer is malware that disguises itself as a Media player. It can infect computers running Microsoft Windows. It is designed to exploit users who download video files, instructing them to download and install the program in order to view the video. The 3wPlayer employs a form of social engineering to infect computers. Seemingly desirable video files, such as recent movies, are released via BitTorrent or other distribution channels. These files resemble conventional AVI files, but are engineered to display a message when played on most media player programs, instructing the user to visit the 3wPlayer website and download the software to view the video. The 3wPlayer is infected with Trojan.Win32.Obfuscated.en According to Symantec, 3wPlayer "may download" a piece of adware they refer to as Adware.Lop, which "adds its own toolbar and search button to Internet Explorer". A Perl script posted online can reportedly decrypt 3wplayer files back into AVI. This claim has been tested wi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. By contrast, software that causes harm due to some deficiency is typically described as a software bug. Malware poses serious problems to individuals and businesses on the Internet. According to Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 669,947,865 in 2017, which is twice as many malware variants as in 2016. Cybercrime, which includes malware attacks as well as other crimes committed by computer, was predicted to cost the world economy $6 trillion USD in 2021, and is increasing at a rate of 15% per year. Many types of malware exist, including computer viruses, worms, Trojan horses, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
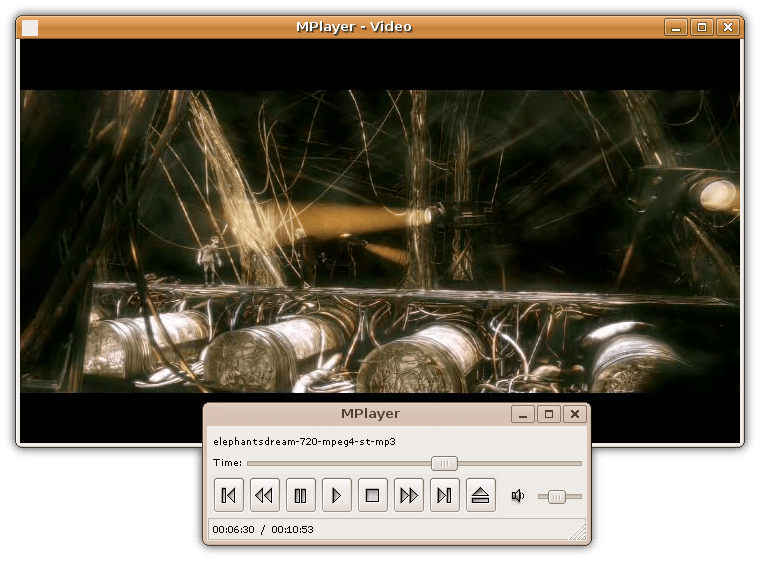
Media Player (software)
Media player software is a type of application software for playing multimedia computer files like audio and video files. Media players commonly display standard media controls, media control icons known from physical devices such as tape recorders and Compact Disc player, CD players, such as play ( ), pause ( ), fastforward (⏩️), backforward (⏪), and stop ( ) buttons. In addition, they generally have progress bars (or "playback bars"), which are Slider (computing), sliders to locate the current position in the duration of the media file. Mainstream operating system, operating systems have at least one default media player. For example, Windows comes with Windows Media Player, Microsoft Movies & TV and Groove Music, while macOS comes with QuickTime Player and Music (software), Music. Linux distributions come with different media players, such as SMPlayer, Amarok (software), Amarok, Audacious (software), Audacious, Banshee (media ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Microsoft Windows
Windows is a group of several proprietary graphical operating system families developed and marketed by Microsoft. Each family caters to a certain sector of the computing industry. For example, Windows NT for consumers, Windows Server for servers, and Windows IoT for embedded systems. Defunct Windows families include Windows 9x, Windows Mobile, and Windows Phone. The first version of Windows was released on November 20, 1985, as a graphical operating system shell for MS-DOS in response to the growing interest in graphical user interfaces (GUIs). Windows is the most popular desktop operating system in the world, with 75% market share , according to StatCounter. However, Windows is not the most used operating system when including both mobile and desktop OSes, due to Android's massive growth. , the most recent version of Windows is Windows 11 for consumer PCs and tablets, Windows 11 Enterprise for corporations, and Windows Server 2022 for servers. Genealogy By marketing ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Social Engineering (security)
Social engineering may refer to: * Social engineering (political science), a means of influencing particular attitudes and social behaviors on a large scale * Social engineering (security), obtaining confidential information by manipulating and/or deceiving people and artificial intelligence See also * Cultural engineering * Manufacturing Consent (other) * Mass media * Noble lie * Propaganda * Social dynamics * Social software * Social technology * Urban planning Urban planning, also known as town planning, city planning, regional planning, or rural planning, is a technical and political process that is focused on the development and design of land use and the built environment, including air, water, ... {{disambiguation Social science disambiguation pages ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Audio Video Interleave
Audio Video Interleave (also Audio Video Interleaved and known by its initials and filename extension AVI, usually pronounced ), is a proprietary multimedia container format and Windows standard introduced by Microsoft in November 1992 as part of its Video for Windows software. AVI files can contain both audio and video data in a file container that allows synchronous audio-with-video playback. Like the DVD video format, AVI files support multiple streaming audio and video, although these features are seldom used. Many AVI files use the file format extensions developed by the Matrox OpenDML group in February 1996. These files are supported by Microsoft, and are unofficially called "AVI 2.0". In 2010 the US government's National Archives and Records Administration defined AVI as the official wrapper for preserving digital video. History Publishers faced a predicament regarding how they should distribute videos on CD-ROMs. Thirty seconds of video displayed in 24-bit color an ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Perl
Perl is a family of two high-level, general-purpose, interpreted, dynamic programming languages. "Perl" refers to Perl 5, but from 2000 to 2019 it also referred to its redesigned "sister language", Perl 6, before the latter's name was officially changed to Raku in October 2019. Though Perl is not officially an acronym, there are various backronyms in use, including "Practical Extraction and Reporting Language". Perl was developed by Larry Wall in 1987 as a general-purpose Unix scripting language to make report processing easier. Since then, it has undergone many changes and revisions. Raku, which began as a redesign of Perl 5 in 2000, eventually evolved into a separate language. Both languages continue to be developed independently by different development teams and liberally borrow ideas from each other. The Perl languages borrow features from other programming languages including C, sh, AWK, and sed; They provide text processing facilities without the arbitrary data-le ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Decrypt
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can decipher a ciphertext back to plaintext and access the original information. Encryption does not itself prevent interference but denies the intelligible content to a would-be interceptor. For technical reasons, an encryption scheme usually uses a pseudo-random encryption key generated by an algorithm. It is possible to decrypt the message without possessing the key but, for a well-designed encryption scheme, considerable computational resources and skills are required. An authorized recipient can easily decrypt the message with the key provided by the originator to recipients but not to unauthorized users. Historically, various forms of encryption have been used to aid in cryptography. Early encryption techniques were often used in military ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Codec
A codec is a device or computer program that encodes or decodes a data stream or signal. ''Codec'' is a portmanteau of coder/decoder. In electronic communications, an endec is a device that acts as both an encoder and a decoder on a signal or data stream, and hence is a type of codec. ''Endec'' is a portmanteau of encoder/decoder. A coder or encoder encodes a data stream or a signal for transmission or storage, possibly in encrypted form, and the decoder function reverses the encoding for playback or editing. Codecs are used in videoconferencing, streaming media, and video editing applications. History In the mid-20th century, a codec was a device that coded analog signals into digital form using pulse-code modulation (PCM). Later, the name was also applied to software for converting between digital signal formats, including companding functions. Examples An audio codec converts analog audio signals into digital signals for transmission or encodes them for storage. A receiv ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Polymorphic Code
In computing, polymorphic code is code that uses a polymorphic engine to mutate while keeping the original algorithm intact - that is, the ''code'' changes itself every time it runs, but the ''function'' of the code (its semantics) will not change at all. For example, the simple math expressions 3+1 and 6-2 both achieve the same result, yet run with different machine code in a CPU. This technique is sometimes used by computer viruses, shellcodes and computer worms to hide their presence. Encryption is the most common method to hide code. With encryption, the main body of the code (also called its payload) is encrypted and will appear meaningless. For the code to function as before, a decryption function is added to the code. When the code is ''executed'', this function reads the payload and decrypts it before executing it in turn. Encryption alone is not polymorphism. To gain polymorphic behavior, the encryptor/decryptor pair is mutated with each copy of the code. This allows di ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Virtual Memory
In computing, virtual memory, or virtual storage is a memory management technique that provides an "idealized abstraction of the storage resources that are actually available on a given machine" which "creates the illusion to users of a very large (main) memory". The computer's operating system, using a combination of hardware and software, maps memory addresses used by a program, called '' virtual addresses'', into ''physical addresses'' in computer memory. Main storage, as seen by a process or task, appears as a contiguous address space or collection of contiguous segments. The operating system manages virtual address spaces and the assignment of real memory to virtual memory. Address translation hardware in the CPU, often referred to as a memory management unit (MMU), automatically translates virtual addresses to physical addresses. Software within the operating system may extend these capabilities, utilizing, e.g., disk storage, to provide a virtual address space that ca ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |