|
Cyber Criminals
A cybercrime is a crime that involves a computer or a computer network.Moore, R. (2005) "Cyber crime: Investigating High-Technology Computer Crime," Cleveland, Mississippi: Anderson Publishing. The computer may have been used in committing the crime, or it may be the target. Cybercrime may harm someone's security or finances. There are many privacy concerns surrounding cybercrime when confidential information is intercepted or disclosed, lawfully or otherwise. Internationally, both governmental and non-state actors engage in cybercrimes, including espionage, financial theft, and other cross-border crimes. Cybercrimes crossing international borders and involving the actions of at least one nation-state are sometimes referred to as cyberwarfare. Warren Buffett describes cybercrime as the "number one problem with mankind" and said that cybercrime "poses real risks to humanity." A 2014 report sponsored by McAfee estimated that cybercrime resulted in $445 billion in annual damage ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Crime
In ordinary language, a crime is an unlawful act punishable by a state or other authority. The term ''crime'' does not, in modern criminal law, have any simple and universally accepted definition,Farmer, Lindsay: "Crime, definitions of", in Cane and Conoghan (editors), ''The New Oxford Companion to Law'', Oxford University Press, 2008 (), p. 263Google Books). though statutory definitions have been provided for certain purposes. The most popular view is that crime is a category created by law; in other words, something is a crime if declared as such by the relevant and applicable law. One proposed definition is that a crime or offence (or criminal offence) is an act harmful not only to some individual but also to a community, society, or the state ("a public wrong"). Such acts are forbidden and punishable by law. The notion that acts such as murder, rape, and theft are to be prohibited exists worldwide. What precisely is a criminal offence is defined by the criminal law of ea ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hack (computer Security)
A security hacker is someone who explores methods for breaching defenses and exploiting weaknesses in a computer system or network. Hackers may be motivated by a multitude of reasons, such as profit, protest, information gathering, challenge, recreation, or evaluation of a system weaknesses to assist in formulating defenses against potential hackers. The subculture that has evolved around hackers is often referred to as the "computer underground". Longstanding controversy surrounds the meaning of the term " hacker." In this controversy, computer programmers reclaim the term ''hacker'', arguing that it refers simply to someone with an advanced understanding of computers and computer networks and that ''cracker'' is the more appropriate term for those who break into computers, whether computer criminals ( black hats) or computer security experts ( white hats). A 2014 article noted that "the black-hat meaning still prevails among the general public". History Birth of subc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Charles Scribner's Sons
Charles Scribner's Sons, or simply Scribner's or Scribner, is an American publisher based in New York City, known for publishing American authors including Henry James, Ernest Hemingway, F. Scott Fitzgerald, Kurt Vonnegut, Marjorie Kinnan Rawlings, Stephen King, Robert A. Heinlein, Thomas Wolfe, George Santayana, John Clellon Holmes, Don DeLillo, and Edith Wharton. The firm published '' Scribner's Magazine'' for many years. More recently, several Scribner titles and authors have garnered Pulitzer Prizes, National Book Awards and other merits. In 1978 the company merged with Atheneum and became The Scribner Book Companies. In turn it merged into Macmillan in 1984. Simon & Schuster bought Macmillan in 1994. By this point only the trade book and reference book operations still bore the original family name. After the merger, the Macmillan and Atheneum adult lists were merged into Scribner's and the Scribner's children list was merged into Atheneum. The former imprint, no ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Terrorism
Terrorism, in its broadest sense, is the use of criminal violence to provoke a state of terror or fear, mostly with the intention to achieve political or religious aims. The term is used in this regard primarily to refer to intentional violence during peacetime or in the context of war against non-combatants (mostly civilians and neutral military personnel). The terms "terrorist" and "terrorism" originated during the French Revolution of the late 18th century but became widely used internationally and gained worldwide attention in the 1970s during the Troubles in Northern Ireland, the Basque conflict, and the Israeli–Palestinian conflict. The increased use of suicide attacks from the 1980s onwards was typified by the 2001 September 11 attacks in the United States. There are various different definitions of terrorism, with no universal agreement about it. Terrorism is a charged term. It is often used with the connotation of something that is "morally wrong". Governments ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Classified Information
Classified information is material that a government body deems to be sensitive information that must be protected. Access is restricted by law or regulation to particular groups of people with the necessary security clearance and need to know, and mishandling of the material can incur criminal penalties. A formal security clearance is required to view or handle classified material. The clearance process requires a satisfactory background investigation. Documents and other information must be properly marked "by the author" with one of several (hierarchical) levels of sensitivity—e.g. restricted, confidential, secret, and top secret. The choice of level is based on an impact assessment; governments have their own criteria, including how to determine the classification of an information asset and rules on how to protect information classified at each level. This process often includes security clearances for personnel handling the information. Some corporations and non-gove ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Extortion
Extortion is the practice of obtaining benefit through coercion. In most jurisdictions it is likely to constitute a criminal offence; the bulk of this article deals with such cases. Robbery is the simplest and most common form of extortion, although making unfounded threats in order to obtain an unfair business advantage is also a form of extortion. Extortion is sometimes called the " protection racket" because the racketeers often phrase their demands as payment for "protection" from (real or hypothetical) threats from unspecified other parties; though often, and almost always, such "protection" is simply abstinence of harm from the same party, and such is implied in the "protection" offer. Extortion is commonly practiced by organized crime. In some jurisdictions, actually obtaining the benefit is not required to commit the offense, and making a threat of violence which refers to a requirement of a payment of money or property to halt future violence is sufficient to co ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Identity Theft
Identity theft occurs when someone uses another person's personal identifying information, like their name, identifying number, or credit card number, without their permission, to commit fraud or other crimes. The term ''identity theft'' was coined in 1964. Since that time, the definition of identity theft has been statutorily defined throughout both the U.K. and the U.S. as the theft of personally identifiable information. Identity theft deliberately uses someone else's identity as a method to gain financial advantages or obtain credit and other benefits, and perhaps to cause other person's disadvantages or loss. The person whose identity has been stolen may suffer adverse consequences, especially if they are falsely held responsible for the perpetrator's actions. Personally identifiable information generally includes a person's name, date of birth, social security number, driver's license number, bank account or credit card numbers, PINs, electronic signatures, fingerprints, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Carding (fraud)
Carding is a term describing the trafficking and unauthorized use of Credit card fraud, credit cards. The stolen credit cards or credit card numbers are then used to buy prepaid gift cards to cover up the tracks. Activities also encompass Identity theft, exploitation of personal data, and money laundering techniques. Modern carding sites have been described as full-service commercial entities. Acquisition There are a great many of methods to acquire credit card and associated financial and personal data. The earliest known carding methods have also included Information diving, "trashing" for financial data, raiding Letter box, mail boxes and Inside job, working with insiders. Some bank card numbers can be semi-automatically generated based on known sequences via a "BIN attack". Carders might attempt a "distributed guessing attack" to discover valid numbers by submitting numbers across a high number of ecommerce sites simultaneously. Today, various methodologies include ATM sk ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Bank Fraud
Bank fraud is the use of potentially illegal means to obtain money, assets, or other property owned or held by a financial institution, or to obtain money from depositors by fraudulently posing as a bank or other financial institution. In many instances, bank fraud is a criminal offence. While the specific elements of particular banking fraud laws vary depending on jurisdictions, the term bank fraud applies to actions that employ a scheme or artifice, as opposed to bank robbery or theft. For this reason, bank fraud is sometimes considered a white-collar crime. Types of bank fraud Accounting fraud In order to hide serious financial problems, some businesses have been known to use fraudulent bookkeeping to overstate sales and income, inflate the worth of the company's assets, or state a profit when the company is operating at a loss. These tampered records are then used to seek investment in the company's bond or security issues or to make fraudulent loan applications in a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
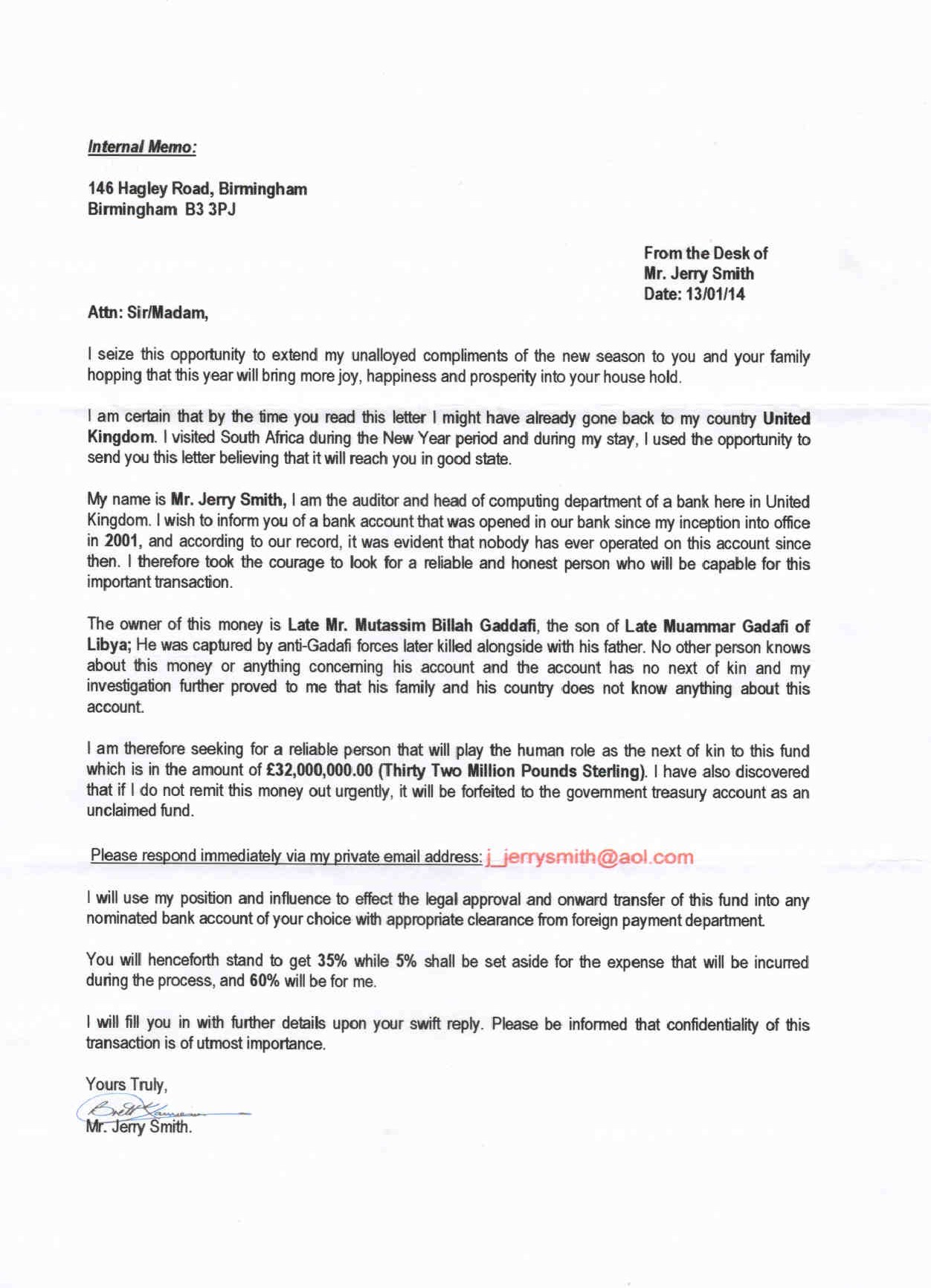
Advance-fee Scam
An advance-fee scam is a form of fraud and is one of the most common types of confidence tricks. The scam typically involves promising the victim a significant share of a large sum of money, in return for a small up-front payment, which the fraudster claims will be used to obtain the large sum. If a victim makes the payment, the fraudster either invents a series of further fees for the victim to pay or simply disappears. FBI. The Federal Bureau of Investigation (FBI) states that "An advance fee scheme occurs when the victim pays money to someone in anticipation of receiving something of greater value - such as a loan, contract, investment, or gift - and then receives little or nothing in return." There are many variations of this type of scam, including the Nigerian prince scam, also known as a 419 scam. The number "419" refers to the section of the Nigerian Criminal Code dealing with fraud and the charges and penalties for such offenders. The scam has been used with fax and trad ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Phishing
Phishing is a type of social engineering where an attacker sends a fraudulent (e.g., spoofed, fake, or otherwise deceptive) message designed to trick a person into revealing sensitive information to the attacker or to deploy malicious software on the victim's infrastructure like ransomware. Phishing attacks have become increasingly sophisticated and often transparently mirror the site being targeted, allowing the attacker to observe everything while the victim is navigating the site, and transverse any additional security boundaries with the victim. As of 2020, phishing is by far the most common attack performed by cybercriminals, the FBI's Internet Crime Complaint Centre recording over twice as many incidents of phishing than any other type of computer crime. The first recorded use of the term "phishing" was in the cracking toolkit AOHell created by Koceilah Rekouche in 1995; however, it is possible that the term was used before this in a print edition of the hacker magaz ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Spyware
Spyware (a portmanteau for spying software) is software with malicious behaviour that aims to gather information about a person or organization and send it to another entity in a way that harms the user—for example, by violating their privacy or endangering their device's security. This behaviour may be present in malware as well as in legitimate software. Websites may engage in spyware behaviours like web tracking. Hardware devices may also be affected. Spyware is frequently associated with advertising and involves many of the same issues. Because these behaviors are so common, and can have non-harmful uses, providing a precise definition of spyware is a difficult task.FTC Report (2005)." History The first recorded use of the term :wikt:spyware, spyware occurred on October 16, 1995 in a Usenet post that poked fun at Microsoft's business model.Vossen, Roland (attributed); October 21, 1995Win 95 Source code in c!!posted to rec..programmer; retrieved from groups.google. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |







.jpg)