|
Cross-zone Scripting
Cross-zone scripting is a browser exploit taking advantage of a vulnerability within a zone-based security solution. The attack allows content (scripts) in unprivileged zones to be executed with the permissions of a privileged zone - i.e. a privilege escalation within the client (web browser) executing the script. The vulnerability could be: * a web browser bug which under some conditions allows content (scripts) in one zone to be executed with the permissions of a higher privileged zone. * a web browser configuration error; unsafe sites listed in privileged zones. * a cross-site scripting vulnerability within a privileged zone A common attack scenario involves two steps. The first step is to use a cross-zone scripting vulnerability to get scripts executed within a privileged zone. To complete the attack, then perform malicious actions on the computer using insecure ActiveX components. This type of vulnerability has been exploited to silently install various malware (such as spy ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Browser Exploit
A browser exploit is a form of malicious code that takes advantage of a flaw or vulnerability in an operating system or piece of software with the intent to breach browser security to alter a user's browser settings without their knowledge. Malicious code may exploit ActiveX, HTML, images, Java, JavaScript, and other Web technologies and cause the browser to run arbitrary code. Symptoms Users whose web browsers have fallen victim of a successful browser exploit may find their homepage, search page, and/or favorites have been changed. Other signs include Internet settings options within the browser being altered, access being blocked to specific functions, and the redirection of incorrectly typed URL prefixes. Prevention There are multiple ways users can protect their web browsers from falling victim to a browser exploit. Such things include installing firewall software, keeping software updated, being cautious when downloading files, and not opening email attachments from unknow ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Vulnerability (computer Science)
Vulnerabilities are flaws in a computer system that weaken the overall security of the device/system. Vulnerabilities can be weaknesses in either the hardware itself, or the software that runs on the hardware. Vulnerabilities can be exploited by a threat actor, such as an attacker, to cross privilege boundaries (i.e. perform unauthorized actions) within a computer system. To exploit a vulnerability, an attacker must have at least one applicable tool or technique that can connect to a system weakness. In this frame, vulnerabilities are also known as the attack surface. Vulnerability management is a cyclical practice that varies in theory but contains common processes which include: discover all assets, prioritize assets, assess or perform a complete vulnerability scan, report on results, remediate vulnerabilities, verify remediation - repeat. This practice generally refers to software vulnerabilities in computing systems. Agile vulnerability management refers preventing attacks ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Privilege Escalation
Privilege escalation is the act of exploiting a bug, a design flaw, or a configuration oversight in an operating system or software application to gain elevated access to resources that are normally protected from an application or user. The result is that an application with more privileges than intended by the application developer or system administrator can perform unauthorized actions. Background Most computer systems are designed for use with multiple user accounts, each of which has abilities known as privileges. Common privileges include viewing and editing files or modifying system files. Privilege escalation means users receive privileges they are not entitled to. These privileges can be used to delete files, view private information, or install unwanted programs such as viruses. It usually occurs when a system has a bug that allows security to be bypassed or, alternatively, has flawed design assumptions about how it will be used. Privilege escalation occurs in tw ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cross-site Scripting
Cross-site scripting (XSS) is a type of security vulnerability that can be found in some web applications. XSS attacks enable attackers to inject client-side scripts into web pages viewed by other users. A cross-site scripting vulnerability may be used by attackers to bypass access controls such as the same-origin policy. Cross-site scripting carried out on websites accounted for roughly 84% of all security vulnerabilities documented by Symantec up until 2007.During the second half of 2007, 11,253 site-specific cross-site vulnerabilities were documented by XSSed, compared to 2,134 "traditional" vulnerabilities documented by Symantec, in XSS effects vary in range from petty nuisance to significant security risk, depending on the sensitivity of the data handled by the vulnerable site and the nature of any security mitigation implemented by the site's owner network. Background Security on the web depends on a variety of mechanisms, including an underlying concept of trust known ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. By contrast, software that causes harm due to some deficiency is typically described as a software bug. Malware poses serious problems to individuals and businesses on the Internet. According to Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 669,947,865 in 2017, which is twice as many malware variants as in 2016. Cybercrime, which includes malware attacks as well as other crimes committed by computer, was predicted to cost the world economy $6 trillion USD in 2021, and is increasing at a rate of 15% per year. Many types of malware exist, including computer viruses, worms, Trojan ho ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Spyware
Spyware (a portmanteau for spying software) is software with malicious behaviour that aims to gather information about a person or organization and send it to another entity in a way that harms the user—for example, by violating their privacy or endangering their device's security. This behaviour may be present in malware as well as in legitimate software. Websites may engage in spyware behaviours like web tracking. Hardware devices may also be affected. Spyware is frequently associated with advertising and involves many of the same issues. Because these behaviors are so common, and can have non-harmful uses, providing a precise definition of spyware is a difficult task.FTC Report (2005)." History The first recorded use of the term :wikt:spyware, spyware occurred on October 16, 1995 in a Usenet post that poked fun at Microsoft's business model.Vossen, Roland (attributed); October 21, 1995Win 95 Source code in c!!posted to rec..programmer; retrieved from groups.google.co ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
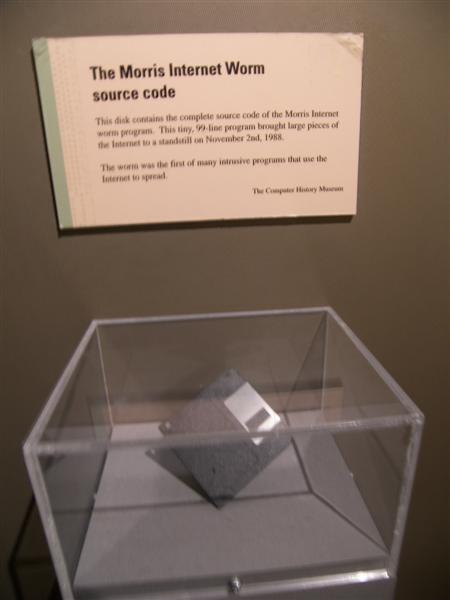
Computer Worm
A computer worm is a standalone malware computer program that replicates itself in order to spread to other computers. It often uses a computer network to spread itself, relying on security failures on the target computer to access it. It will use this machine as a host to scan and infect other computers. When these new worm-invaded computers are controlled, the worm will continue to scan and infect other computers using these computers as hosts, and this behaviour will continue. Computer worms use recursive methods to copy themselves without host programs and distribute themselves based on the law of exponential growth, thus controlling and infecting more and more computers in a short time. Worms almost always cause at least some harm to the network, even if only by consuming bandwidth, whereas viruses almost always corrupt or modify files on a targeted computer. Many worms are designed only to spread, and do not attempt to change the systems they pass through. However, as ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Explorer
Internet Explorer (formerly Microsoft Internet Explorer and Windows Internet Explorer, commonly abbreviated IE or MSIE) is a series of graphical user interface, graphical web browsers developed by Microsoft which was used in the Microsoft Windows, Windows line of operating systems (in Windows 11, Windows Server Insider Build 22463 and Windows Server Insider Build 25110, it is replaced by the Chromium (web browser), Chromium version of Microsoft Edge). Starting in 1995, It was first released as part of the add-on package Microsoft Plus!, Plus! for Windows 95 that year. Later versions were available as free downloads, or in-service packs, and included in the original equipment manufacturer (OEM) service releases of Windows 95 and later versions of Windows. Microsoft spent over per year on Internet Explorer in the late 1990s, with over 1,000 people involved in the project by 1999. New feature development for the browser was discontinued in 2016 in favor of new browser Microsoft Ed ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
ActiveX
ActiveX is a deprecated software framework created by Microsoft that adapts its earlier Component Object Model (COM) and Object Linking and Embedding (OLE) technologies for content downloaded from a network, particularly from the World Wide Web. Microsoft introduced ActiveX in 1996. In principle, ActiveX is not dependent on Microsoft Windows operating systems, but in practice, most ActiveX controls only run on Windows. Most also require the client to be running on an x86-based computer because ActiveX controls contain compiled code. ActiveX is still supported as of Windows 10 through Internet Explorer 11, while ActiveX is not supported in their default web browser Microsoft Edge (which has a different, incompatible extension system, as it is based on Google's Chromium project). ActiveX controls ActiveX was one of the major technologies used in component-based software engineering. Compared with JavaBeans, ActiveX supports more programming languages, but JavaBeans supports mor ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Explorer 6
Microsoft Internet Explorer 6 (IE6) is a graphical web browser developed by Microsoft for Windows operating systems. Released on August 24, 2001, it is the sixth, and by now discontinued, version of Internet Explorer and the successor to Internet Explorer 5. It was the default browser in Windows XP (later default was Internet Explorer 8) and Windows Server 2003 and can replace previous versions of Internet Explorer on Windows NT 4.0, Windows 98, Windows 2000 and Windows ME but unlike version 5, this version does not support Windows 95 or an earlier version. IE6 SP2+ and IE7 were only included (IE6 SP2+) in or available ( IE7) for Windows XP SP2+. Despite dominating market share (attaining a peak of 90% in mid-2004), this version of Internet Explorer has been widely criticized for its security issues and lack of support for modern web standards, making frequent appearances in "worst tech products of all time" lists, with '' PC World'' labeling it "the least secure softw ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Web Security Exploits
Web most often refers to: * Spider web, a silken structure created by the animal * World Wide Web or the Web, an Internet-based hypertext system Web, WEB, or the Web may also refer to: Computing * WEB, a literate programming system created by Donald Knuth * GNOME Web, a Web browser * Web.com, a web-design company * Webs (web hosting), a Web hosting and website building service Engineering * Web (manufacturing), continuous sheets of material passed over rollers ** Web, a roll of paper in offset printing * Web, the vertical element of an I-beam or a rail profile * Web, the interior beams of a truss Films * ''Web'' (2013 film), a documentary * ''Webs'' (film), a 2003 science-fiction movie * ''The Web'' (film), a 1947 film noir * Charlotte's Web (2006 film) Literature * ''Web'' (comics), a MLJ comicbook character (created 1942) * ''Web'' (novel), by John Wyndham (1979) * The Web (series), a science fiction series (1997–1999) * World English Bible, a public-domain Bible ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |