|
Case Officer
In intelligence organizations, agent handling is the management of so-called agents (called secret agents or spies in common parlance), principal agents, and agent networks (called "assets") by intelligence officers typically known as case officers. Human intelligence A primary purpose of intelligence organizations is to penetrate a target with a human agent, or a network of human agents. Such agents can either infiltrate the target, or be recruited "in place". Case officers are professionally trained employees of intelligence organizations that manage human agents and human agent networks. Intelligence that derives from such human sources is known by the abbreviation HUMINT. Sometimes, agent handling is done indirectly, through "principal agents" that serve as proxies for case officers. It is not uncommon, for example, for a case officer to manage a number of principal agents, who in turn handle agent networks, which are preferably organized in a cellular fashion. In such ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Intelligence Agency
An intelligence agency is a government agency responsible for the collection, analysis, and exploitation of information in support of law enforcement, national security, military, public safety, and foreign policy objectives. Means of information gathering are both overt and covert and may include espionage, communication interception, cryptanalysis, cooperation with other institutions, and evaluation of public sources. The assembly and propagation of this information is known as intelligence analysis or intelligence assessment. Intelligence agencies can provide the following services for their national governments. * Give early warning of impending crisis; * Serve national and international crisis management by helping to discern the intentions of current or potential opponents; * Inform national defense planning and military operations ( military intelligence); * Protect sensitive information secrets, both of their own sources and activities, and those of other state a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Coercion
Coercion () is compelling a party to act in an involuntary manner by the use of threats, including threats to use force against a party. It involves a set of forceful actions which violate the free will of an individual in order to induce a desired response. These actions may include extortion, blackmail, or even torture and sexual assault. For example, a bully may demand lunch money from a student where refusal results in the student getting beaten. In common law systems, the act of violating a law while under coercion is codified as a duress crime. Coercion can be used as leverage to force the victim to act in a way contrary to their own interests. Coercion can involve not only the infliction of bodily harm, but also psychological abuse (the latter intended to enhance the perceived credibility of the threat). The threat of further harm may also lead to the acquiescence of the person being coerced. The concepts of coercion and persuasion are similar, but various factors d ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Countersurveillance
Countersurveillance refers to measures that are usually undertaken by the public to prevent surveillance, including covert surveillance. Countersurveillance may include electronic methods such as technical surveillance counter-measures, which is the process of detecting surveillance devices. It can also include covert listening devices, visual surveillance devices, and countersurveillance software to thwart unwanted cybercrime, such as accessing computing and mobile devices for various nefarious reasons (e.g. theft of financial, personal or corporate data). More often than not, countersurveillance will employ a set of actions (countermeasures) that, when followed, reduce the risk of surveillance. Countersurveillance is different from sousveillance (inverse surveillance), as the latter does not necessarily aim to prevent or reduce surveillance. Types Technical surveillance counter-measures Electronic countermeasures Most bugs emit some form of electromagnetic radiation, usua ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Surveillance
Surveillance is the monitoring of behavior, many activities, or information for the purpose of information gathering, influencing, managing or directing. This can include observation from a distance by means of electronic equipment, such as closed-circuit television (CCTV), or interception of electronically transmitted information like Internet traffic. It can also include simple technical methods, such as Human intelligence (intelligence gathering), human intelligence gathering and postal interception. Surveillance is used by citizens for protecting their neighborhoods. And by governments for intelligence gathering - including espionage, prevention of crime, the protection of a process, person, group or object, or the investigation of crime. It is also used by criminal organizations to plan and commit crimes, and by businesses to Industrial espionage, gather intelligence on criminals, their competitors, suppliers or customers. Religious organisations charged with detecting he ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
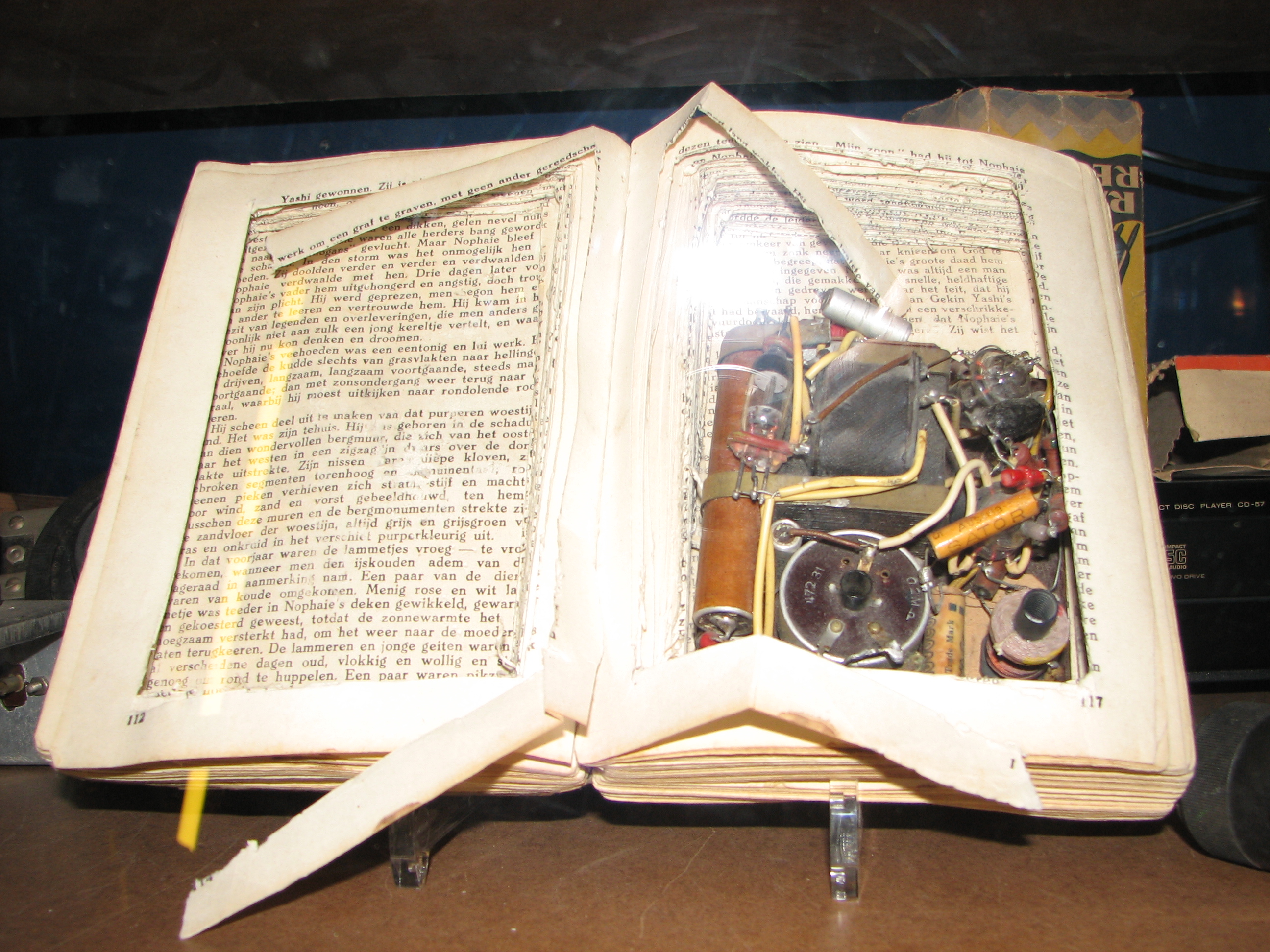
Dead Drop
A dead drop or dead letter box is a method of espionage tradecraft used to pass items or information between two individuals (e.g., a case officer and an agent, or two agents) using a secret location. By avoiding direct meetings, individuals can maintain operational security. This method stands in contrast to the live drop, so-called because two persons meet to exchange items or information. Spies and their handlers have been known to perform dead drops using various techniques to hide items (such as money, secrets or instructions) and to signal that the drop has been made. Although the signal and location by necessity must be agreed upon in advance, the signal may or may not be located close to the dead drop itself. The operatives may not necessarily know one another or ever meet. Considerations The location and nature of the dead drop must enable retrieval of the hidden item without the operatives being spotted by a member of the public, the police, or other security forc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Concealment Device
Concealment devices or diversion safes are used to hide things for the purpose of secrecy or security. They are made from an ordinary household object such as a book, a soda can, a candle, a can, or something as small as a coin. The idea is that such an inconspicuous object would not be expected to contain anything of worth. Examples in espionage include dead drop spikes for transferring items to other people, and hollowed-out coins or hollowed out teeth for concealing something - such as microfilm or a suicide pill. Examples in smuggling include suitcases with false bottoms for hiding contraband. During World War II MI9 was responsible for creating many concealment devices for "escape aids" to assist prisoners of war to escape. Examples Ammunition Starting in the First World War and still continuing today, military personnel use ammunition casings to hide small amounts of critical information e.g. encryption/recognition codes or navigational grid references etc. The hi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
One-time Pad
In cryptography, the one-time pad (OTP) is an encryption technique that cannot be cracked, but requires the use of a single-use pre-shared key that is not smaller than the message being sent. In this technique, a plaintext is paired with a random secret key (also referred to as ''a one-time pad''). Then, each bit or character of the plaintext is encrypted by combining it with the corresponding bit or character from the pad using modular addition. The resulting ciphertext will be impossible to decrypt or break if the following four conditions are met: #The key must be at least as long as the plaintext. #The key must be random ( uniformly distributed in the set of all possible keys and independent of the plaintext), entirely sampled from a non-algorithmic, chaotic source such as a hardware random number generator. It is not sufficient for OTP keys to pass statistical randomness tests as such tests cannot measure entropy, and the number of bits of entropy must be at least ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptography
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security (data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. Cryptography prior to the modern age was effectively synony ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Communication
Communication (from la, communicare, meaning "to share" or "to be in relation with") is usually defined as the transmission of information. The term may also refer to the message communicated through such transmissions or the field of inquiry studying them. There are many disagreements about its precise definition. John Peters argues that the difficulty of defining communication emerges from the fact that communication is both a universal phenomenon and a specific discipline of institutional academic study. One definitional strategy involves limiting what can be included in the category of communication (for example, requiring a "conscious intent" to persuade). By this logic, one possible definition of communication is the act of developing meaning among entities or groups through the use of sufficiently mutually understood signs, symbols, and semiotic conventions. An important distinction is between verbal communication, which happens through the use of a language, and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Blackmail
Blackmail is an act of coercion using the threat of revealing or publicizing either substantially true or false information about a person or people unless certain demands are met. It is often damaging information, and it may be revealed to family members or associates rather than to the general public. These acts can also involve using threats of physical, mental or emotional harm, or of criminal prosecution, against the victim or someone close to the victim. It is normally carried out for personal gain, most commonly of position, money, or property. Blackmail may also be considered a form of extortion. Although the two are generally synonymous, extortion is the taking of personal property by threat of future harm. Blackmail is the use of threat to prevent another from engaging in a lawful occupation and writing libelous letters or letters that provoke a breach of the peace, as well as use of intimidation for purposes of collecting an unpaid debt. In many jurisdictions, bl ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Espionage
Espionage, spying, or intelligence gathering is the act of obtaining secret or confidential information ( intelligence) from non-disclosed sources or divulging of the same without the permission of the holder of the information for a tangible benefit. A person who commits espionage is called an ''espionage agent'' or ''spy''. Any individual or spy ring (a cooperating group of spies), in the service of a government, company, criminal organization, or independent operation, can commit espionage. The practice is clandestine, as it is by definition unwelcome. In some circumstances, it may be a legal tool of law enforcement and in others, it may be illegal and punishable by law. Espionage is often part of an institutional effort by a government or commercial concern. However, the term tends to be associated with state spying on potential or actual enemies for military purposes. Spying involving corporations is known as industrial espionage. One of the most effective ways t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |