|
Android Privacy Guard
Android Privacy Guard (APG) is a free and open-source app for the Android operating system that provides strong, user-based encryption which is compatible with the Pretty Good Privacy (PGP) and GNU Privacy Guard (GPG) programs. This allows users to encrypt, decrypt, digitally sign, and verify signatures for text, emails, and other files. The application allows the user to store the credentials of other users with whom they interact, and to encrypt files such that only a specified user can decrypt them. In the same manner, if a file is received from another user and its credentials are saved, the receiver can verify the authenticity of that file and decrypt it if necessary. The specific implementation in APG relies on the Spongy Castle APIs. APG has not been updated since March 2014 and is no longer under active development. The development has been picked up by OpenKeychain. Reception After its initial release in June 2010, it has gained a strong following with over 200 ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyanogenmod
CyanogenMod ( ; CM) is a discontinued open-source operating system for mobile devices, based on the Android mobile platform. It was developed as free and open-source software based on the official releases of Android by Google, with added original and third-party code, and based on a rolling release development model. Although only a subset of total CyanogenMod users elected to report their use of the firmware, on 23 March 2015, some reports indicated that over 50 million people ran CyanogenMod on their phones. It was also frequently used as a starting point by developers of other ROMs. In 2013, the founder, Stefanie Kondik, obtained venture funding under the name Cyanogen Inc. to allow commercialization of the project. However, the company did not, in her view, capitalize on the project's success, and in 2016 she left or was forced out as part of a corporate restructure, which involved a change of CEO, closure of offices and projects, and cessation of services, and therefore l ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email
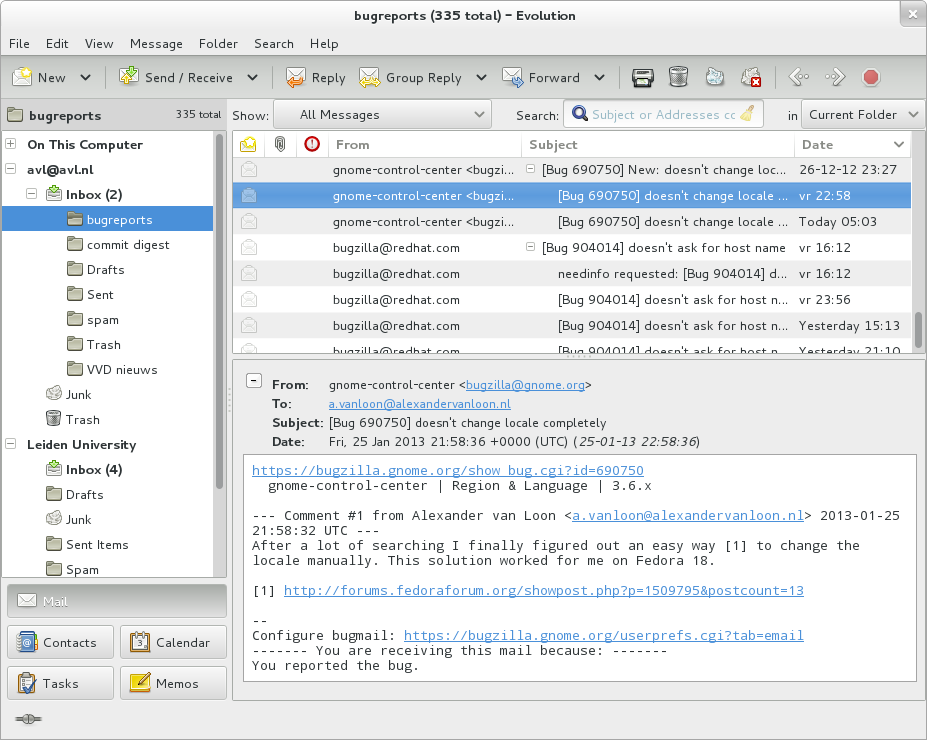
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic ( digital) version of, or counterpart to, mail, at a time when "mail" meant only physical mail (hence '' e- + mail''). Email later became a ubiquitous (very widely used) communication medium, to the point that in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries. ''Email'' is the medium, and each message sent therewith is also called an ''email.'' The term is a mass noun. Email operates across computer networks, primarily the Internet, and also local area networks. Today's email systems are based on a store-and-forward model. Email servers accept, forward, deliver, and store messages. Neither the users nor their computers are required to be online simult ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Free And Open-source Android Software
Free may refer to: Concept * Freedom, having the ability to do something, without having to obey anyone/anything * Freethought, a position that beliefs should be formed only on the basis of logic, reason, and empiricism * Emancipate, to procure political rights, as for a disenfranchised group * Free will, control exercised by rational agents over their actions and decisions * Free of charge, also known as gratis. See Gratis vs libre. Computing * Free (programming), a function that releases dynamically allocated memory for reuse * Free format, a file format which can be used without restrictions * Free software, software usable and distributable with few restrictions and no payment * Freeware, a broader class of software available at no cost Mathematics * Free object ** Free abelian group ** Free algebra ** Free group ** Free module ** Free semigroup * Free variable People * Free (surname) * Free (rapper) (born 1968), or Free Marie, American rapper and media personal ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
YubiKey
The YubiKey is a hardware authentication device manufactured by Yubico to protect access to computers, networks, and online services that supports one-time passwords (OTP), public-key cryptography, and authentication, and the Universal 2nd Factor (U2F) and FIDO2 protocols developed by the FIDO Alliance. It allows users to securely log into their accounts by emitting one-time passwords or using a FIDO-based public/private key pair generated by the device. YubiKey also allows for storing static passwords for use at sites that do not support one-time passwords. Google, Amazon, Microsoft, Twitter, and Facebook use YubiKey devices to secure employee accounts as well as end user accounts. Some password managers support YubiKey. Yubico also manufactures the Security Key, a similar lower cost device with only FIDO2/WebAuthn and FIDO/U2F support. The YubiKey implements the HMAC-based One-time Password Algorithm (HOTP) and the Time-based One-time Password Algorithm (TOTP), and identifie ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Near Field Communication
Near-field communication (NFC) is a set of communication protocols that enables communication between two electronic devices over a distance of 4 cm (1 in) or less. NFC offers a low-speed connection through a simple setup that can be used to bootstrap more-capable wireless connections. Like other "proximity card" technologies, NFC is based on inductive coupling between two so-called antennas present on NFC-enabled devices—for example a smartphone and a printer—communicating in one or both directions, using a frequency of 13.56 MHz in the globally available unlicensed radio frequency ISM band using the ISO/IEC 18000-3 air interface standard at data rates ranging from 106 to 424 kbit/s. The standards were provided by the NFC Forum. The forum was responsible for promoting the technology and setting standards and certifies device compliance. Secure communications are available by applying encryption algorithms as is done for credit cards and if they fit the crite ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Fork (software Development)
In software engineering, a project fork happens when developers take a copy of source code from one software package and start independent development on it, creating a distinct and separate piece of software. The term often implies not merely a development branch, but also a split in the developer community; as such, it is a form of schism. Grounds for forking are varying user preferences and stagnated or discontinued development of the original software. Free and open-source software is that which, by definition, may be forked from the original development team without prior permission, and without violating copyright law. However, licensed forks of proprietary software (''e.g.'' Unix) also happen. Etymology The word "fork" has been used to mean "to divide in branches, go separate ways" as early as the 14th century. In the software environment, the word evokes the fork system call, which causes a running process to split itself into two (almost) identical copies that (ty ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Global Surveillance Disclosures (2013–present)
Ongoing news reports in the international media have revealed operational details about the Anglophone cryptographic agencies' global surveillance of both foreign and domestic nationals. The reports mostly emanate from a cache of top secret documents leaked by ex-NSA contractor Edward Snowden, which he obtained whilst working for Booz Allen Hamilton, one of the largest contractors for defense and intelligence in the United States. In addition to a trove of U.S. federal documents, Snowden's cache reportedly contains thousands of Australian, British, Canadian and New Zealand intelligence files that he had accessed via the exclusive "Five Eyes" network. In June 2013, the first of Snowden's documents were published simultaneously by ''The Washington Post'' and ''The Guardian'', attracting considerable public attention. The disclosure continued throughout 2013, and a small portion of the estimated full cache of documents was later published by other media outlets worldwide, most ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
K-9 Mail
K-9 Mail is free and open source email client for Android. It is designed as an alternative to the stock email clients included with the platform; it supports both POP3 and IMAP protocols and supports IMAP IDLE for real-time notifications. The project is named after the ''Doctor Who'' character K9. In 2015 the project received $86,000 of funding from the Open Technology Fund. On 13 June 2022, it was announced that K-9 Mail had been taken over by MZLA Technologies Corporation, a subsidiary of the Mozilla Foundation with current maintainer Christian Ketterer joining the team, and plans for K-9 Mail to be rebranded as Thunderbird for Android following the completion of a feature roadmap, including sync with Thunderbird on PC, integrating Thunderbird's automated account setup system, message filtering, and improvements to folders. Reception This application has been downloaded from the Google Play Store between 5 million and 10 million times since its release and has been rated b ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
OpenKeychain
OpenKeychain is a free and open-source mobile app for the Android operating system that provides strong, user-based encryption which is compatible with the OpenPGP standard. This allows users to encrypt, decrypt, sign, and verify signatures for text, emails, and files. The app allows the user to store the public keys of other users with whom they interact, and to encrypt files such that only a specified user can decrypt them. In the same manner, if a file is received from another user and its public keys are saved, the receiver can verify the authenticity of that file and decrypt it if necessary. As of August 2021, it is no longer actively developed. K-9 Mail Support Together with K-9 Mail, it supports end-to-end encrypted emails via the OpenPGP INLINE and PGP/MIME formats. The developers of OpenKeychain and K-9 Mail are trying to change the way user interfaces for email encryption are designed. They propose to remove the ability to create encrypted-only emails and hide the case ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Bouncy Castle (cryptography)
Bouncy Castle is a collection of APIs used in cryptography. It includes APIs for both the Java and the C# programming languages. The APIs are supported by a registered Australian charitable organization: Legion of the Bouncy Castle Inc. Bouncy Castle is Australian in origin and therefore American restrictions on the export of cryptography from the United States do not apply to it. History Bouncy Castle started when two colleagues were tired of having to re-invent a set of cryptography libraries each time they changed jobs working in server-side Java SE. One of the developers was active in Java ME (J2ME at that time) development as a hobby and a design consideration was to include the greatest range of Java VMs for the library, including those on J2ME. This design consideration led to the architecture that exists in Bouncy Castle. The project, founded in May 2000, was originally written in Java only, but added a C# API in 2004. The original Java API consisted of approximatel ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer File
A computer file is a computer resource for recording data in a computer storage device, primarily identified by its file name. Just as words can be written to paper, so can data be written to a computer file. Files can be shared with and transferred between computers and mobile devices via removable media, networks, or the Internet. Different types of computer files are designed for different purposes. A file may be designed to store an Image, a written message, a video, a computer program, or any wide variety of other kinds of data. Certain files can store multiple data types at once. By using computer programs, a person can open, read, change, save, and close a computer file. Computer files may be reopened, modified, and copied an arbitrary number of times. Files are typically organized in a file system, which tracks file locations on the disk and enables user access. Etymology The word "file" derives from the Latin ''filum'' ("a thread"). "File" was used in the conte ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |