|
Authenticated Received Chain
Authenticated Received Chain (ARC) is an email Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic ( digital) version of, or counterpart to, mail, at a time when "mail" mean ... authentication system designed to allow an intermediate mail server like a mailing list or forwarding service to sign an email's original authentication results. This allows a receiving service to validate an email when the email's SPF and DKIM records are rendered invalid by an intermediate server's processing. ARC is defined in RFC 8617, published in July 2019, as "Experimental". Overview DMARC allows a sender's domain to indicate that their emails are protected by SPF and/or DKIM, and tells a receiving service what to do if neither of those authentication methods passes - such as to reject the message. However, a strict DMARC policy may block legitimate emails sent through a mai ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
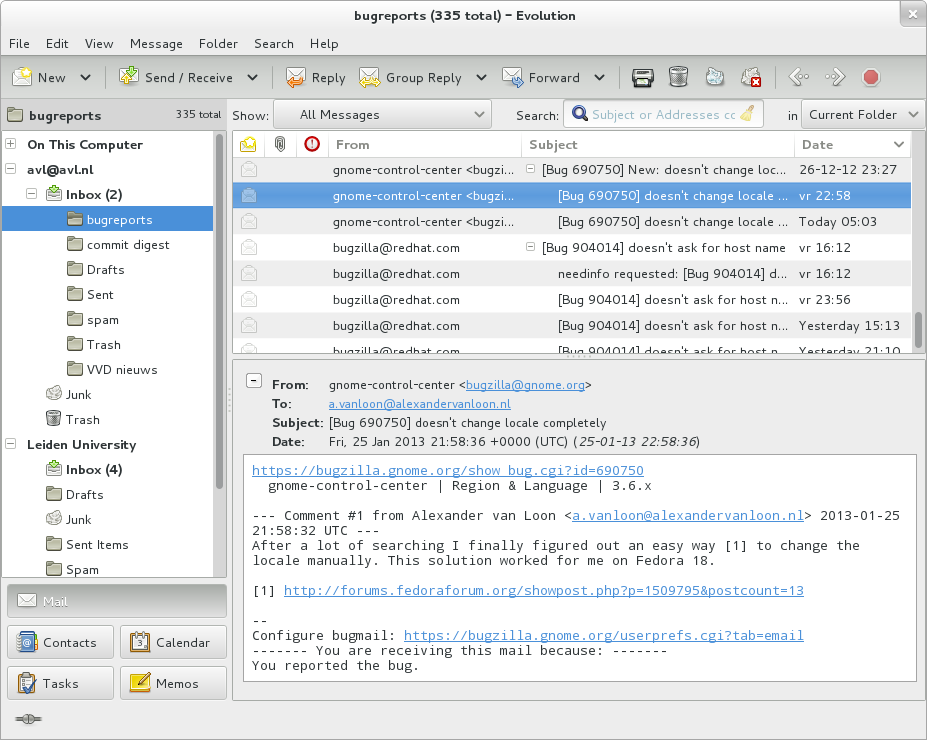
Email
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic ( digital) version of, or counterpart to, mail, at a time when "mail" meant only physical mail (hence '' e- + mail''). Email later became a ubiquitous (very widely used) communication medium, to the point that in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries. ''Email'' is the medium, and each message sent therewith is also called an ''email.'' The term is a mass noun. Email operates across computer networks, primarily the Internet, and also local area networks. Today's email systems are based on a store-and-forward model. Email servers accept, forward, deliver, and store messages. Neither the users nor their computers are required to be online simu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Sender Policy Framework
Sender Policy Framework (SPF) is an email authentication method designed to detect forging sender addresses during the delivery of the email. SPF alone, though, is limited to detecting a forged sender claim in the envelope of the email, which is used when the mail gets bounced. Only in combination with DMARC can it be used to detect the forging of the visible sender in emails ( email spoofing), a technique often used in phishing and email spam. SPF allows the receiving mail server to check during mail delivery that a mail claiming to come from a specific domain is submitted by an IP address authorized by that domain's administrators. The list of authorized sending hosts and IP addresses for a domain is published in the DNS records for that domain. Sender Policy Framework is defined in RFC 7208 dated April 2014 as a "proposed standard". History The first public mention of the concept was in 2000 but went mostly unnoticed. No mention was made of the concept again until a firs ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
DKIM
DomainKeys Identified Mail (DKIM) is an email authentication method designed to detect forged sender addresses in email ( email spoofing), a technique often used in phishing and email spam. DKIM allows the receiver to check that an email claimed to have come from a specific domain was indeed authorized by the owner of that domain. It achieves this by affixing a digital signature, linked to a domain name, to each outgoing email message. The recipient system can verify this by looking up the sender's public key published in the DNS. A valid signature also guarantees that some parts of the email (possibly including attachments) have not been modified since the signature was affixed. Usually, DKIM signatures are not visible to end-users, and are affixed or verified by the infrastructure rather than the message's authors and recipients. DKIM is an Internet Standard. It is defined in RFC 6376, dated September 2011; with updates in RFC 8301 and RFC 8463. Overview The nee ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
DMARC
Domain-based Message Authentication, Reporting and Conformance (DMARC) is an email authentication protocol. It is designed to give email domain owners the ability to protect their domain from unauthorized use, commonly known as email spoofing. The purpose and primary outcome of implementing DMARC is to protect a domain from being used in business email compromise attacks, phishing email, email scams and other cyber threat activities. Once the DMARC DNS entry is published, any receiving email server can authenticate the incoming email based on the instructions published by the domain owner within the DNS entry. If the email passes the authentication, it will be delivered and can be trusted. If the email fails the check, depending on the instructions held within the DMARC record the email could be delivered, quarantined or rejected. For example, one email forwarding service delivers the mail, but as "From: no-reply@". DMARC extends two existing email authentication mechanisms, Se ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Bounce Address
{{No footnotes, date=June 2016 A bounce address is an email address to which bounce messages are delivered. There are many variants of the name, none of them used universally, including return path, reverse path, envelope from, envelope sender, MAIL FROM, 5321-FROM, return address, From_, Errors-to, etc. It is not uncommon for a single document to use several of these names. All of these names refer to the email address provided with the MAIL FROM command during the SMTP session. Background information Ordinarily, the bounce address is not seen by email users and, without standardization of the name, it may cause confusion. If an email message is thought of as resembling a traditional paper letter in an envelope, then the "header fields", such as To:, From:, and Subject:, along with the body of the message are analogous to the letterhead and body of a letter - and are normally all presented and visible to the user. However, the envelope in this analogy is the contents of t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Rewriting
In mathematics, computer science, and logic, rewriting covers a wide range of methods of replacing subterms of a formula with other terms. Such methods may be achieved by rewriting systems (also known as rewrite systems, rewrite engines, or reduction systems). In their most basic form, they consist of a set of objects, plus relations on how to transform those objects. Rewriting can be non-deterministic. One rule to rewrite a term could be applied in many different ways to that term, or more than one rule could be applicable. Rewriting systems then do not provide an algorithm for changing one term to another, but a set of possible rule applications. When combined with an appropriate algorithm, however, rewrite systems can be viewed as computer programs, and several theorem provers and declarative programming languages are based on term rewriting. Example cases Logic In logic, the procedure for obtaining the conjunctive normal form (CNF) of a formula can be implemented as a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
John Levine
John R. Levine is an Internet author and consultant specializing in email infrastructure, spam filtering, and software patents. He chaired the Anti-Spam Research Group ( ASRG) of the Internet Research Task Force (IRTF), is president of CAUCE (the Coalition Against Unsolicited Commercial Email), is a member of the ICANN (Internet Corporation For Assigned Names and Numbers) Stability and Security Advisory Committee, and runs Taughannock Networks. He has co-authored many books, including ''The Internet For Dummies'' (with Carol Baroudi and Margaret Levine Young), ''UNIX For Dummies'' (with Margaret Levine Young), ''Fighting Spam for Dummies'' (with Margaret Levine Young, Ray Everett-Church), and ''flex & bison'' (O'Reilly). He was also the mayor of the village of Trumansburg, New York, United States from March 2004 until March 2007. Levine graduated from Yale University in 1975 and earned his Ph.D. in computer science from Yale in 1984 with a thesis about the design and implem ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email Authentication
Email authentication, or validation, is a collection of techniques aimed at providing verifiable information about the origin of email messages by validating the domain ownership of any message transfer agents (MTA) who participated in transferring and possibly modifying a message. The original base of Internet email, Simple Mail Transfer Protocol (SMTP), has no such feature, so forged sender addresses in emails (a practice known as email spoofing) have been widely used in phishing, email spam, and various types of fraud. To combat this, many competing email authentication proposals have been developed, but only fairly recently have three been widely adopted – SPF, DKIM and DMARC. The results of such validation can be used in automated email filtering, or can assist recipients when selecting an appropriate action. This article does not cover user authentication of email submission and retrieval. Rationale In the early 1980s, when Simple Mail Transfer Protocol (SMTP) was des ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Architecture
World Wide Web topology is the network topology of the World Wide Web, as seen as a network of web pages connected by hyperlinks. The Jellyfish and Bow Tie models are two attempts at modeling the topology of hyperlinks between web pages. Models of web page topology Jellyfish Model The simplistic Jellyfish model of the World Wide Web centers around a large strongly connected core of high-degree web pages that form a clique A clique ( AusE, CanE, or ), in the social sciences, is a group of individuals who interact with one another and share similar interests. Interacting with cliques is part of normative social development regardless of gender, ethnicity, or popula ...; pages such that there is a path from any page within the core to any other page. In other words, starting from any node within the core, it is possible to visit any other node in the core just by clicking hyperlinks. From there, a distinction is made between pages of single degree and those of higher order de ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Governance
Internet governance consists of a system of laws, rules, policies and practices that dictate how its board members manage and oversee the affairs of any internet related- regulatory body. This article describes how the Internet was and is currently governed, some inherent controversies, and ongoing debates regarding how and why the Internet should or should not be governed in future. (Internet governance should not be confused with e-governance, which refers to governmental use of technology in its governing duties.) Background No one person, company, organization or government runs the Internet. It is a globally distributed network comprising many voluntarily interconnected autonomous networks. It operates without a central governing body with each constituent network setting and enforcing its own policies. Its governance is conducted by a decentralized and international multistakeholder network of interconnected autonomous groups drawing from civil society, the private secto ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Network Addressing
Network, networking and networked may refer to: Science and technology * Network theory, the study of graphs as a representation of relations between discrete objects * Network science, an academic field that studies complex networks Mathematics * Networks, a graph with attributes studied in network theory ** Scale-free network, a network whose degree distribution follows a power law ** Small-world network, a mathematical graph in which most nodes are not neighbors, but have neighbors in common * Flow network, a directed graph where each edge has a capacity and each edge receives a flow Biology * Biological network, any network that applies to biological systems * Ecological network, a representation of interacting species in an ecosystem * Neural network, a network or circuit of neurons Technology and communication * Artificial neural network, a computing system inspired by animal brains * Broadcast network, radio stations, television stations, or other electronic media outlet ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |