|
Anti-computer Forensics
Anti-computer forensics or counter-forensics are techniques used to obstruct forensic analysis. Definition Anti-forensics has only recently been recognized as a legitimate field of study. Within this field of study, numerous definitions of anti-forensics abound. One of the more widely known and accepted definitions comes from Marc Rogers of Purdue University. Rogers uses a more traditional "crime scene" approach when defining anti-forensics. "Attempts to negatively affect the existence, amount and/or quality of evidence from a crime scene, or make the analysis and examination of evidence difficult or impossible to conduct."Rogers, D. M. (2005). Anti-Forensic Presentation given to Lockheed Martin. San Diego. One of the earliest detailed presentations of anti-forensics, in Phrack Magazine in 2002, defines anti-forensics as "the removal, or hiding, of evidence in an attempt to mitigate the effectiveness of a forensics investigation".The Grugq (2002). Phrack Magazine. A more abbrev ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Forensics
Computer forensics (also known as computer forensic science) is a branch of digital forensic science pertaining to evidence found in computers and digital storage media. The goal of computer forensics is to examine digital media in a forensically sound manner with the aim of identifying, preserving, recovering, analyzing and presenting facts and opinions about the digital information. Although it is most often associated with the investigation of a wide variety of computer crime, computer forensics may also be used in civil proceedings. The discipline involves similar techniques and principles to data recovery, but with additional guidelines and practices designed to create a legal audit trail. Evidence from computer forensics investigations is usually subjected to the same guidelines and practices of other digital evidence. It has been used in a number of high-profile cases and is accepted as reliable within U.S. and European court systems. Overview In the early 1980s person ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Industrial Security Program
The National Industrial Security Program, or NISP, is the nominal authority in the United States for managing the needs of private industry to access classified information. The NISP was established in 1993 by Executive Order 12829. The National Security Council nominally sets policy for the NISP, while the Director of the Information Security Oversight Office is nominally the authority for implementation. Under the ISOO, the Secretary of Defense is nominally the Executive Agent, but the NISP recognizes four different Cognizant Security Agencies, all of which have equal authority: the Department of Defense, the Department of Energy, the Central Intelligence Agency, and the Nuclear Regulatory Commission The Nuclear Regulatory Commission (NRC) is an independent agency of the United States government tasked with protecting public health and safety related to nuclear energy. Established by the Energy Reorganization Act of 1974, the NRC began operat .... Defense Counterintelligen ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Metasploit Framework
The Metasploit Project is a computer security project that provides information about security vulnerabilities and aids in penetration testing and IDS signature development. It is owned by Boston, Massachusetts-based security company Rapid7. Its best-known sub-project is the open-source Metasploit Framework, a tool for developing and executing exploit code against a remote target machine. Other important sub-projects include the Opcode Database, shellcode archive and related research. The Metasploit Project includes anti-forensic and evasion tools, some of which are built into the Metasploit Framework. Metasploit is pre-installed in the Kali Linux operating system. History Metasploit was created by H. D. Moore in 2003 as a portable network tool using Perl. By 2007, the Metasploit Framework had been completely rewritten in Ruby. On October 21, 2009, the Metasploit Project announced that it had been acquired by Rapid7, a security company that provides unified vulnerability ma ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Misinformation
Misinformation is incorrect or misleading information. It differs from disinformation, which is ''deliberately'' deceptive. Rumors are information not attributed to any particular source, and so are unreliable and often unverified, but can turn out to be either true or false. Even if later retracted, misinformation can continue to influence actions and memory. People may be more prone to believe misinformation because they are emotionally connected to what they are listening to or are reading. The role of social media has made information readily available to us at anytime, and it connects vast groups of people along with their information at one time. Advances in technology has impacted the way we communicate information and the way misinformation is spread. Misinformation has impacts on our societies' ability to receive information which then influences our communities, politics, and medical field. History Early examples include the insults and smears spread among political rival ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IP Address Spoofing
In computer networking, IP address spoofing or IP spoofing is the creation of Internet Protocol (IP) packets with a false source IP address, for the purpose of impersonating another computing system. Background The basic protocol for sending data over the Internet network and many other computer networks is the Internet Protocol (IP). The protocol specifies that each IP packet must have a header which contains (among other things) the IP address of the sender of the packet. The source IP address is normally the address that the packet was sent from, but the sender's address in the header can be altered, so that to the recipient it appears that the packet came from another source. The protocol requires the receiving computer to send back a response to the source IP address therefore spoofing is mainly used when the sender can anticipate the network response or does not care about the response. The source IP address provides only limited information about the sender. It may p ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Degaussing
Degaussing is the process of decreasing or eliminating a remnant magnetic field. It is named after the gauss, a unit of magnetism, which in turn was named after Carl Friedrich Gauss. Due to magnetic hysteresis, it is generally not possible to reduce a magnetic field completely to zero, so degaussing typically induces a very small "known" field referred to as bias. Degaussing was originally applied to reduce ships' magnetic signatures during World War II. Degaussing is also used to reduce magnetic fields in cathode ray tube monitors and to destroy data held on magnetic storage. Ships' hulls The term was first used by then-Commander Charles F. Goodeve, Royal Canadian Naval Volunteer Reserve, during World War II while trying to counter the German magnetic naval mines that were wreaking havoc on the British fleet. The mines detected the increase in the magnetic field when the steel in a ship concentrated the Earth's magnetic field over it. Admiralty scientists, including Goodeve, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hdparm
hdparm is a command line program for Linux to set and view ATA hard disk drive hardware parameters and test performance. It can set parameters such as drive caches, sleep mode, power management, acoustic management, and DMA settings. GParted and Parted Magic both include ''hdparm''. Changing hardware parameters from suboptimal conservative defaults to their optimal settings can improve performance greatly. For example, turning on DMA can, in some instances, double or triple data throughput. There is, however, no reliable method for determining the optimal settings for a given controller-drive combination, except careful trial and error. Depending on the given parameters, ''hdparm'' can cause computer crashes or render the data on the disk inaccessible. Usage examples hdparm has to be run with special privileges, otherwise it will either not be found or the requested actions will not be executed properly. Display information of the hard drive: sudo hdparm -I /dev/sda ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Srm (Unix)
srm (or Secure Remove) is a command line utility for Unix-like computer systems for secure file deletion. srm removes each specified file by overwriting, renaming, and truncating it before unlinking. This prevents other people from undeleting or recovering any information about the file from the command line. Platform-specific behaviours and bugs Filesystems with hard links Attempting to secure delete a file with multiple hard links results in a warning from srm stating that the current access path has been unlinked, but the data itself was not overwritten or truncated. This is an undocumented feature of srm 1.2.8 on Mac OS X 10.9, and is erroneously documented in 1.2.11 as a behaviour activated by the OpenBSD rm-compatible option -P. However, in both the OS X and SourceForge srm implementations, the behaviour of unlinking but not overwriting multi-linked files is always active, as long as the platform reports hard links. srm 1.2.8 on Mac OS X 10.9 has a -n option, which ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Shred (Unix)
is a command on Unix-like operating systems that can be used to securely delete files and devices so that it is extremely difficult to recover them, even with specialized hardware and technology; assuming it's even possible to recover the file at all. It is a part of GNU Core Utilities. Being based on the Gutmann method paper, it suffers from the same criticisms and possible shortcomings. Background For efficiency, the process of erasing a file from storage using the command usually only erases the file's file-system entry while keeping the content of the file intact. This frequently allows commonly available software to recover the "erased" file's data. If the file data is stored on magnetic media such as a HDD, even if the file is overwritten, residual magnetic fields may allow data recovery using specialist hardware equipment (this claim is disputed; see ). To prevent this, overwrites the contents of a file multiple times, using patterns chosen to maximize destru ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
AT Attachment
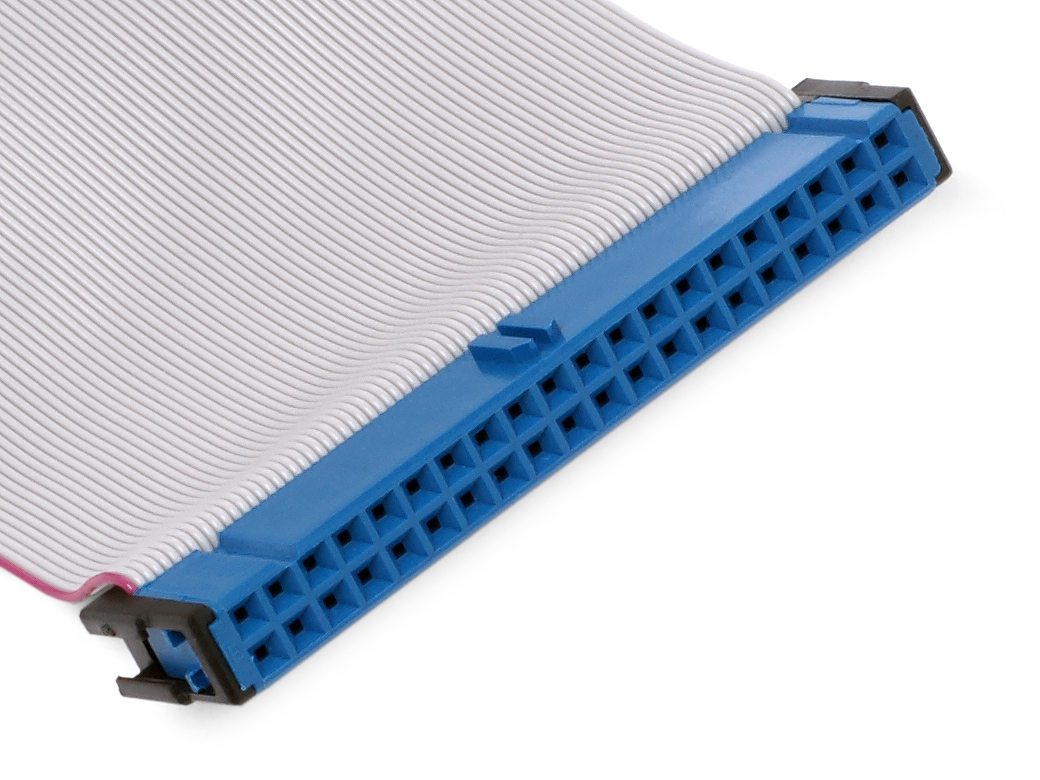
Parallel ATA (PATA), originally , also known as IDE, is a standard interface designed for IBM PC-compatible computers. It was first developed by Western Digital and Compaq in 1986 for compatible hard drives and CD or DVD drives. The connection is used for storage devices such as hard disk drives, floppy disk drives, and optical disc drives in computers. The standard is maintained by the X3/INCITS committee. It uses the underlying (ATA) and Packet Interface ( ATAPI) standards. The Parallel ATA standard is the result of a long history of incremental technical development, which began with the original AT Attachment interface, developed for use in early PC AT equipment. The ATA interface itself evolved in several stages from Western Digital's original Integrated Drive Electronics (IDE) interface. As a result, many near-synonyms for ATA/ATAPI and its previous incarnations are still in common informal use, in particular Extended IDE (EIDE) and Ultra ATA (UATA). After the intr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Security Agency
The National Security Agency (NSA) is a national-level intelligence agency of the United States Department of Defense, under the authority of the Director of National Intelligence (DNI). The NSA is responsible for global monitoring, collection, and processing of information and data for foreign and domestic intelligence and counterintelligence purposes, specializing in a discipline known as signals intelligence (SIGINT). The NSA is also tasked with the protection of U.S. communications networks and information systems. The NSA relies on a variety of measures to accomplish its mission, the majority of which are clandestine. The existence of the NSA was not revealed until 1975. The NSA has roughly 32,000 employees. Originating as a unit to decipher coded communications in World War II, it was officially formed as the NSA by President Harry S. Truman in 1952. Between then and the end of the Cold War, it became the largest of the U.S. intelligence organizations in terms of pers ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Institute Of Standards And Technology
The National Institute of Standards and Technology (NIST) is an agency of the United States Department of Commerce whose mission is to promote American innovation and industrial competitiveness. NIST's activities are organized into physical science laboratory programs that include nanoscale science and technology, engineering, information technology, neutron research, material measurement, and physical measurement. From 1901 to 1988, the agency was named the National Bureau of Standards. History Background The Articles of Confederation, ratified by the colonies in 1781, provided: The United States in Congress assembled shall also have the sole and exclusive right and power of regulating the alloy and value of coin struck by their own authority, or by that of the respective states—fixing the standards of weights and measures throughout the United States. Article 1, section 8, of the Constitution of the United States, ratified in 1789, granted these powers to the new Congr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |