Mobile security, or mobile device security, is the protection of
smartphone
A smartphone is a mobile phone with advanced computing capabilities. It typically has a touchscreen interface, allowing users to access a wide range of applications and services, such as web browsing, email, and social media, as well as multi ...
s, tablets, and
laptop
A laptop computer or notebook computer, also known as a laptop or notebook, is a small, portable personal computer (PC). Laptops typically have a Clamshell design, clamshell form factor (design), form factor with a flat-panel computer scree ...
s from threats associated with
wireless computing.
It has become increasingly important in
mobile computing
Mobile computing is human–computer interaction in which a computer is expected to be transported during normal usage and allow for transmission of data, which can include voice and video transmissions. Mobile computing involves mobile commun ...
. The
security
Security is protection from, or resilience against, potential harm (or other unwanted coercion). Beneficiaries (technically referents) of security may be persons and social groups, objects and institutions, ecosystems, or any other entity or ...
of personal and business information now stored on
smartphones
A smartphone is a mobile phone with advanced computing capabilities. It typically has a touchscreen interface, allowing users to access a wide range of applications and services, such as web browsing, email, and social media, as well as mult ...
is of particular concern.
Increasingly, users and businesses use smartphones not only to communicate, but also to plan and organize their work and private life. Within companies, these technologies are causing profound changes in the organization of
information systems
An information system (IS) is a formal, sociotechnical, organizational system designed to collect, process, store, and distribute information. From a sociotechnical perspective, information systems comprise four components: task, people, structu ...
and have therefore become the source of new risks. Indeed, smartphones collect and compile an increasing amount of sensitive information to which access must be controlled to protect the
privacy
Privacy (, ) is the ability of an individual or group to seclude themselves or information about themselves, and thereby express themselves selectively.
The domain of privacy partially overlaps with security, which can include the concepts of a ...
of the
user
Ancient Egyptian roles
* User (ancient Egyptian official), an ancient Egyptian nomarch (governor) of the Eighth Dynasty
* Useramen, an ancient Egyptian vizier also called "User"
Other uses
* User (computing), a person (or software) using an ...
and the
intellectual property
Intellectual property (IP) is a category of property that includes intangible creations of the human intellect. There are many types of intellectual property, and some countries recognize more than others. The best-known types are patents, co ...
of the company.
The majority of attacks are aimed at smartphones. These attacks take advantage of vulnerabilities discovered in smartphones that can result from different modes of communication, including
Short Message Service
Short Message Service, commonly abbreviated as SMS, is a text messaging service component of most telephone, Internet and mobile device systems. It uses standardized communication protocols that let mobile phones exchange short text messages, ...
(SMS, text messaging),
Multimedia Messaging Service
Multimedia Messaging Service (MMS) is a standard way to send messages that include multimedia content to and from a mobile phone over a cellular network. Users and providers may refer to such a message as a PXT, a picture message, or a multimedia ...
(MMS),
wireless connections,
Bluetooth
Bluetooth is a short-range wireless technology standard that is used for exchanging data between fixed and mobile devices over short distances and building personal area networks (PANs). In the most widely used mode, transmission power is li ...
, and
GSM
The Global System for Mobile Communications (GSM) is a family of standards to describe the protocols for second-generation (2G) digital cellular networks, as used by mobile devices such as mobile phones and Mobile broadband modem, mobile broadba ...
, the de facto international standard for mobile communications. Smartphone operating systems or browsers are another weakness. Some
malware
Malware (a portmanteau of ''malicious software'')Tahir, R. (2018)A study on malware and malware detection techniques . ''International Journal of Education and Management Engineering'', ''8''(2), 20. is any software intentionally designed to caus ...
makes use of the common user's limited knowledge. Only 2.1% of users reported having first-hand contact with
mobile malware, according to a 2008 McAfee study, which found that 11.6% of users had heard of someone else being harmed by the problem. Yet, it is predicted that this number will rise.
As of December 2023, there were about 5.4 million global mobile cyberattacks per month. This is a 147% increase from the previous year.
Security
countermeasures are being developed and applied to smartphones, from security best practices in software to the dissemination of information to end users. Countermeasures can be implemented at all levels, including
operating system
An operating system (OS) is system software that manages computer hardware and software resources, and provides common daemon (computing), services for computer programs.
Time-sharing operating systems scheduler (computing), schedule tasks for ...
development, software design, and user behavior modifications.
Challenges of smartphone mobile security
Threats
A smartphone user is exposed to various threats when they use their phone. In just the last two quarters of 2012, the number of unique mobile threats grew by 261%, according to
ABI Research.
These threats can disrupt the operation of the smartphone and transmit or modify user data. Applications must guarantee privacy and integrity of the information they handle. In addition, since some apps could themselves be malware, their functionality and activities should be limited (for example, restricting the apps from accessing location information via the
Global Positioning System
The Global Positioning System (GPS) is a satellite-based hyperbolic navigation system owned by the United States Space Force and operated by Mission Delta 31. It is one of the global navigation satellite systems (GNSS) that provide ge ...
(GPS), blocking access to the user's address book, preventing the transmission of data on the network, or sending SMS messages that are billed to the user).
Malicious apps can also be
installed without the owners' permission or knowledge.
Vulnerability
Vulnerability refers to "the quality or state of being exposed to the possibility of being attacked or harmed, either physically or emotionally." The understanding of social and environmental vulnerability, as a methodological approach, involves ...
in mobile devices refers to aspects of system security that are susceptible to attacks. A vulnerability occurs when there is system weakness, an attacker has access to the weakness, and the attacker has competency to exploit the weakness.
Potential attackers began looking for vulnerabilities when Apple's
iPhone
The iPhone is a line of smartphones developed and marketed by Apple that run iOS, the company's own mobile operating system. The first-generation iPhone was announced by then–Apple CEO and co-founder Steve Jobs on January 9, 2007, at ...
and the first
Android devices came onto the market. Since the introduction of apps (particularly mobile banking apps), which are vital targets for hackers,
malware
Malware (a portmanteau of ''malicious software'')Tahir, R. (2018)A study on malware and malware detection techniques . ''International Journal of Education and Management Engineering'', ''8''(2), 20. is any software intentionally designed to caus ...
has been rampant. The Department of Homeland Security's
cybersecurity
Computer security (also cybersecurity, digital security, or information technology (IT) security) is a subdiscipline within the field of information security. It consists of the protection of computer software, systems and networks from thr ...
department claims that the number of vulnerable points in smartphone operating systems has increased. As mobile phones are connected to utilities and appliances,
hacker
A hacker is a person skilled in information technology who achieves goals and solves problems by non-standard means. The term has become associated in popular culture with a security hackersomeone with knowledge of bug (computing), bugs or exp ...
s,
cybercriminals, and even intelligence officials have access to these devices.
Starting in 2011, it became increasingly popular to let employees use their own devices for work-related purposes. The Crowd Research Partners study, published in 2017, reports that during 2017, most businesses that mandated the use of mobile devices were subjected to malware attacks and breaches. It has become common for rogue applications to be installed on user devices without the user's permission. They breach privacy, which hinders the effectiveness of the devices.
Since the recent rise of mobile attacks, hackers have increasingly targeted smartphones through credential theft and snooping. The number of attacks targeting smartphones and other devices has risen by 50 percent. According to the study,
mobile banking applications are responsible for the increase in attacks.
Malware—such as
ransomware
Ransomware is a type of malware that Encryption, encrypts the victim's personal data until a ransom is paid. Difficult-to-trace Digital currency, digital currencies such as paysafecard or Bitcoin and other cryptocurrency, cryptocurrencies are com ...
,
worms
The World Register of Marine Species (WoRMS) is a taxonomic database that aims to provide an authoritative and comprehensive catalogue and list of names of marine organisms.
Content
The content of the registry is edited and maintained by scien ...
,
botnet
A botnet is a group of Internet-connected devices, each of which runs one or more Internet bot, bots. Botnets can be used to perform distributed denial-of-service attack, distributed denial-of-service (DDoS) attacks, steal data, send Spamming, sp ...
s,
Trojans, and
viruses
A virus is a submicroscopic infectious agent that replicates only inside the living cells of an organism. Viruses infect all life forms, from animals and plants to microorganisms, including bacteria and archaea. Viruses are found in almo ...
—have been developed to exploit vulnerabilities in mobile devices. Malware is distributed by attackers so they can gain access to private information or digitally harm a user. For example, should malware breach a user's banking service, it may be able to access their transaction information, their rights to
log in, and their money. Some malware is developed with anti-detection techniques to avoid detection. Attackers who use malware can avoid detection by hiding
malicious code.
Trojan-droppers can also avoid detection of malware. Despite the fact that the malware inside a device does not change, the dropper generates new
hashes each time. Additionally, droppers can also create a multitude of files, which can lead to the creation of viruses. Android mobile devices are prone to Trojan-droppers. The banking Trojans also enable attacks on the banking applications on the phone, which leads to the theft of data for use in stealing money and funds.
Jailbreaks for
iOS
Ios, Io or Nio (, ; ; locally Nios, Νιός) is a Greek island in the Cyclades group in the Aegean Sea. Ios is a hilly island with cliffs down to the sea on most sides. It is situated halfway between Naxos and Santorini. It is about long an ...
devices work by disabling the signing of codes on iPhones so that applications not downloaded from the App Store can be operated. In this way, all the protection layers offered by iOS are disrupted, exposing the device to malware. These outside applications don't run in a
sandbox
A sandbox is a sandpit, a wide, shallow playground construction to hold sand, often made of wood or plastic.
Sandbox or sand box may also refer to:
Arts, entertainment, and media
* Sandbox (band), a Canadian rock music group
* Sandbox (Gu ...
, which exposes potential security problems. Some attack vectors change the mobile devices' configuration settings by installing malicious credentials and
virtual private network
Virtual private network (VPN) is a network architecture for virtually extending a private network (i.e. any computer network which is not the public Internet) across one or multiple other networks which are either untrusted (as they are not con ...
s (VPNs) to direct information to malicious systems. In addition,
spyware
Spyware (a portmanteau for spying software) is any malware that aims to gather information about a person or organization and send it to another entity in a way that harms the user by violating their privacy, endangering their device's securit ...
can be installed on mobile devices in order to track an individual.
Triade malware comes pre-installed on some mobile devices. In addition to Haddad, there is Lotoor, which exploits vulnerabilities in the system to repackage legitimate applications.
The devices are also vulnerable due to spyware and leaky behaviors through applications. Mobile devices are also effective conveyance systems for malware threats, breaches of information, and thefts.
Wi-Fi interference technologies can also attack mobile devices through potentially insecure networks. By compromising the network, hackers are able to gain access to key data. Devices connected to public networks are at risk of attacks. A VPN, on the other hand, can be used to secure networks. As soon as a system is threatened, an active VPN will operate. There are also social engineering techniques, such as
phishing
Phishing is a form of social engineering and a scam where attackers deceive people into revealing sensitive information or installing malware such as viruses, worms, adware, or ransomware. Phishing attacks have become increasingly sophisticate ...
, in which unsuspecting victims are sent links to lead them to malicious websites. The attackers can then hack into the victim's device and copy all of its information.
Some mobile device attacks can be prevented. For example, containerization allows the creation of a hardware infrastructure that separates business data from other data. Additionally, network protection detects malicious traffic and rogue access points. Data security is also ensured through authentication.
There are a number of threats to mobile devices, including annoyance, stealing money, invading privacy, propagation, and malicious tools.
There are three prime targets for attackers:
# Data – Smartphones are devices for data management and may contain sensitive data like
credit card numbers, authentication information, private information, activity logs (calendar, call logs).
# Identity – Smartphones are highly customizable, so the device or its contents can easily be associated with a specific person.
# Availability – Attacking a smartphone can limit or deprive a user's access to it.
Attacks on mobile security systems include:
*
Botnet
A botnet is a group of Internet-connected devices, each of which runs one or more Internet bot, bots. Botnets can be used to perform distributed denial-of-service attack, distributed denial-of-service (DDoS) attacks, steal data, send Spamming, sp ...
s – Attackers infect multiple machines with malware that victims generally acquire via e-mail attachments or from compromised applications or websites. The malware then gives hackers remote control of "zombie" devices, which can then be instructed to perform harmful acts.
[
* Malicious applications – Hackers upload malicious programs or games to third-party smartphone application marketplaces. The programs steal personal information and open backdoor communication channels to install additional applications and cause other problems.][
* Malicious links on social networks – An effective way to spread malware where hackers can place Trojans, spyware, and backdoors.][
* ]Spyware
Spyware (a portmanteau for spying software) is any malware that aims to gather information about a person or organization and send it to another entity in a way that harms the user by violating their privacy, endangering their device's securit ...
– Hackers use this to hijack phones, allowing them to hear calls, see text messages and e-mails, and track a user's location through GPS updates.[
The source of these attacks are the same actors found in the non-mobile computing space:
* Professionals, whether commercial or military, who focus on the three targets mentioned above. They steal sensitive data from the general public, as well as undertake industrial ]espionage
Espionage, spying, or intelligence gathering, as a subfield of the intelligence field, is the act of obtaining secret or confidential information ( intelligence). A person who commits espionage on a mission-specific contract is called an ...
. They will also use the identity of those attacked to achieve other attacks.
* Thieves who want to gain income through data or identities they have stolen. The thieves will attack many people to increase their potential income.
* Black hat hackers who specifically attack availability. Their goal is to develop viruses
A virus is a submicroscopic infectious agent that replicates only inside the living cells of an organism. Viruses infect all life forms, from animals and plants to microorganisms, including bacteria and archaea. Viruses are found in almo ...
, and cause damage to the device.Grey hat
A grey hat (greyhat or gray hat) is a computer hacker or computer security expert who may sometimes violate laws or typical ethical standards, but usually does not have the malicious intent typical of a black hat hacker.
The term came into u ...
hackers do not intend on damaging the device or stealing data.
Consequences
When a smartphone is infected by an attacker, the attacker can attempt several things:
* The attacker can manipulate the smartphone as a zombie machine: a machine with which the attacker can communicate and send commands which will be used to send unsolicited messages (spam
Spam most often refers to:
* Spam (food), a consumer brand product of canned processed pork of the Hormel Foods Corporation
* Spamming, unsolicited or undesired electronic messages
** Email spam, unsolicited, undesired, or illegal email messages
...
) via SMS or email.
* The attacker can easily force the smartphone to make phone calls. For example, one can use the API
An application programming interface (API) is a connection between computers or between computer programs. It is a type of software interface, offering a service to other pieces of software. A document or standard that describes how to build ...
(library that contains the basic functions not present in the smartphone) PhoneMakeCall by Microsoft
Microsoft Corporation is an American multinational corporation and technology company, technology conglomerate headquartered in Redmond, Washington. Founded in 1975, the company became influential in the History of personal computers#The ear ...
, which collects telephone numbers from any source (such as yellow pages
The yellow pages are Telephone directory, telephone directories of business, businesses, organized by category rather than alphabetically by business name, in which advertising is sold. The directories were originally printed on yellow paper, ...
) and then calls them. The attacker can use this method to call paid services, resulting in charges to the smartphone owner. Dangerously, the smartphone could call and disrupt emergency service
Emergency services and rescue services are organizations that ensure public safety, security, and health by addressing and resolving different emergencies. Some of these agencies exist solely for addressing certain types of emergencies, while oth ...
s.
* A compromised smartphone can record conversations between the user and others and send them to a third party. This can cause user privacy and industrial security problems.
* An attacker can also steal a user's identity, usurp their identity (with a copy of the user's SIM card or even the telephone itself), and thus impersonate the owner. This raises security concerns in countries where smartphones can be used to place orders, view bank accounts, or are used as an identity card.
* The attacker can reduce the usability of the smartphone, by discharging the battery. For example, they can launch an application that will run continuously on the smartphone processor, requiring a lot of energy and draining the battery. Frank Stajano and Ross Anderson first described this form of attack, calling it an attack of "battery exhaustion" or "sleep deprivation torture".
* The attacker can make the smartphone unusable. This attack can delete the boot scripts, resulting in a phone without a functioning operating system
An operating system (OS) is system software that manages computer hardware and software resources, and provides common daemon (computing), services for computer programs.
Time-sharing operating systems scheduler (computing), schedule tasks for ...
; modify certain files to make it unusable, such as a script that launches at startup that forces the smartphone to restart; or embed a startup application that will empty the battery.
* The attacker can remove the user's data, whether personal (photos, music, videos) or professional (contacts, calendars, notes).
Attacks based on communication
Attacks based on SMS and MMS
Some attacks derive from flaws in the management of Short Message Service
Short Message Service, commonly abbreviated as SMS, is a text messaging service component of most telephone, Internet and mobile device systems. It uses standardized communication protocols that let mobile phones exchange short text messages, ...
(SMS) and Multimedia Messaging Service
Multimedia Messaging Service (MMS) is a standard way to send messages that include multimedia content to and from a mobile phone over a cellular network. Users and providers may refer to such a message as a PXT, a picture message, or a multimedia ...
(MMS).
Some mobile phone models have problems in managing binary SMS messages. By sending an ill-formed block, it is possible to cause the phone to restart, leading to the denial-of-service attacks. If a user with a Siemens S55 received a text message containing a Chinese character
Chinese characters are logographs used to write the Chinese languages and others from regions historically influenced by Chinese culture. Of the four independently invented writing systems accepted by scholars, they represent the only on ...
, it would lead to a denial of service.
In another case, while the standard requires that the maximum size of a Nokia Mail address is 32 characters, some Nokia
Nokia Corporation is a Finnish multinational corporation, multinational telecommunications industry, telecommunications, technology company, information technology, and consumer electronics corporation, originally established as a pulp mill in 1 ...
phones did not verify this standard, so if a user enters an email address over 32 characters, that leads to complete dysfunction of the e-mail handler and puts it out of commission. This attack is called "curse of silence".
A study on the safety of the SMS infrastructure revealed that SMS messages sent from the Internet
The Internet (or internet) is the Global network, global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a internetworking, network of networks ...
can be used to perform a distributed denial of service (DDoS) attack against the mobile telecommunications
Mobile telephony is the provision of wireless Telephony, telephone services to Mobile phone, mobile phones, distinguishing it from fixed-location telephony provided via landline phones. Traditionally, telephony specifically refers to Telephon ...
infrastructure of a big city. The attack exploits the delays in the delivery of messages to overload the network.
Another potential attack could begin with a phone that sends an MMS to other phones, with an attachment. This attachment is infected with a virus. Upon receipt of the MMS, the user can choose to open the attachment. If it is opened, the phone is infected, and the virus sends an MMS with an infected attachment to all the contacts in the address book. There is a real-world example of this attack: the virus Commwarrior sends MMS messages (including an infected file) to all recipients in a mobile phone's address book. If a recipient installs the infected file, the virus repeats, sending messages to recipients taken from the new address book.
Attacks based on communication networks
GSM networks
The attacker may try to break the encryption
In Cryptography law, cryptography, encryption (more specifically, Code, encoding) is the process of transforming information in a way that, ideally, only authorized parties can decode. This process converts the original representation of the inf ...
of a GSM mobile network. The network encryption algorithms belong to the family of algorithms called A5. Due to the policy of security through obscurity
In security engineering, security through obscurity is the practice of concealing the details or mechanisms of a system to enhance its security. This approach relies on the principle of hiding something in plain sight, akin to a magician's slei ...
, it has not been possible to openly test the robustness of these algorithms. There were originally two variants of the algorithm: A5/1 and A5/2 (stream ciphers), where the former was designed to be relatively strong, and the latter was purposely designed to be weak to allow easy cryptanalysis
Cryptanalysis (from the Greek ''kryptós'', "hidden", and ''analýein'', "to analyze") refers to the process of analyzing information systems in order to understand hidden aspects of the systems. Cryptanalysis is used to breach cryptographic se ...
and eavesdropping. ETSI
The European Telecommunications Standards Institute (ETSI) is an independent, not-for-profit, standardization organization operating in the field of Information and communications technology, information and communications. ETSI supports the de ...
forced some countries (typically outside Europe) to use A5/2. Since the encryption algorithm was made public, it was proved to be breakable: A5/2 could be broken on the fly, and A5/1 in about 6 hours. In July 2007, the 3GPP
The 3rd Generation Partnership Project (3GPP) is an umbrella term for a number of standards organizations which develop protocols for mobile telecommunications. Its best known work is the development and maintenance of:
* GSM and related 2G and ...
approved a change request to prohibit the implementation of A5/2 in any new mobile phones, decommissioning the algorithm; it is no longer implemented in mobile phones.
Stronger public algorithms have been added to the GSM standard: the A5/3 and A5/4 (Block cipher
In cryptography, a block cipher is a deterministic algorithm that operates on fixed-length groups of bits, called ''blocks''. Block ciphers are the elementary building blocks of many cryptographic protocols. They are ubiquitous in the storage a ...
s), otherwise known as KASUMI or UEA1 published by ETSI. If the network does not support A5/1, or any other A5 algorithm implemented by the phone, then the base station can specify A5/0 which is the null algorithm, whereby the radio traffic is sent unencrypted. Even if mobile phones are able to use 3G or 4G (which have much stronger encryption than 2G GSM), the base station can downgrade the radio communication to 2G GSM and specify A5/0 (no encryption). This is the basis for eavesdropping attacks on mobile radio networks using a fake base station commonly called an IMSI catcher.
In addition, tracing of mobile terminals is difficult since each time the mobile terminal is accessing or being accessed by the network, a new temporary identity (TMSI) is allocated to the mobile terminal. The TMSI is used as the identity of the mobile terminal the next time it accesses the network. The TMSI is sent to the mobile terminal in encrypted messages.
Once the encryption algorithm of GSM is broken, the attacker can intercept all unencrypted communications made by the victim's smartphone.
Wi-Fi
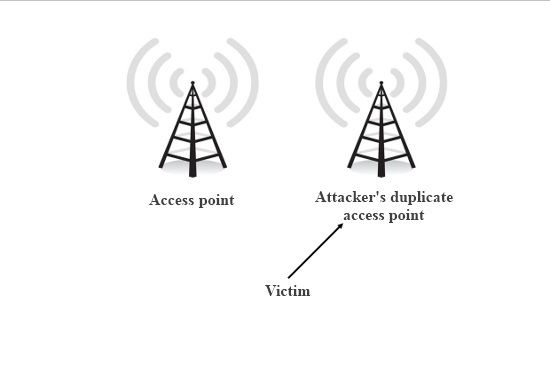 An attacker can try to eavesdrop on Wi-Fi communications to derive information (e.g., username, password). This type of attack is not unique to smartphones, but they are very vulnerable to these attacks because often Wi-Fi is their only means of communication and access the internet. The security of wireless networks (
An attacker can try to eavesdrop on Wi-Fi communications to derive information (e.g., username, password). This type of attack is not unique to smartphones, but they are very vulnerable to these attacks because often Wi-Fi is their only means of communication and access the internet. The security of wireless networks (WLAN
A wireless LAN (WLAN) is a wireless computer network that links two or more devices using wireless communication to form a local area network (LAN) within a limited area such as a home, school, computer laboratory, campus, or office buildin ...
) is thus an important subject.
Initially, wireless networks were secured by WEP keys. The weakness of WEP is its short encryption key, which is the same for all connected clients. In addition, several reductions in the search space of the keys have been found by researchers. Now, most wireless networks are protected by the WPA security protocol. WPA is based on the Temporal Key Integrity Protocol
Temporal Key Integrity Protocol (TKIP ) is a security protocol used in the IEEE 802.11 wireless networking standard. TKIP was designed by the IEEE 802.11i task group and the Wi-Fi Alliance as an interim solution to replace Wired Equivalent Privac ...
(TKIP), which was designed to allow migration from WEP to WPA on the equipment already deployed. The major improvements in security are the dynamic encryption keys. For small networks, the WPA uses a " pre-shared key" which is based on a shared key. Encryption can be vulnerable if the length of the shared key is short. With limited opportunities for input (i.e., only the numeric keypad), mobile phone users might define short encryption keys that contain only numbers. This increases the likelihood that an attacker succeeds with a brute-force attack. The successor to WPA, called WPA2, is supposed to be safe enough to withstand a brute force attack.
The ability to access free and fast Wi-Fi gives a business an edge over those who do not. Free Wi-Fi is usually provided by organizations such as airports, coffee shops, and restaurants for a number of reasons, including encouraging customers to spend more time and money on the premises, and helping users stay productive.
Bluetooth
Security issues related to Bluetooth on mobile devices have been studied and have shown numerous problems on different phones. One easy to exploit vulnerability
Vulnerability refers to "the quality or state of being exposed to the possibility of being attacked or harmed, either physically or emotionally." The understanding of social and environmental vulnerability, as a methodological approach, involves ...
is that unregistered services do not require authentication, and vulnerable applications have a virtual serial port used to control the phone. An attacker only needed to connect to the port to take full control of the device.
In another example, an attacker sends a file via Bluetooth to a phone within range with Bluetooth in discovery mode. If the recipient accepts, a virus is transmitted. An example of this is a worm called Cabir. The worm searches for nearby phones with Bluetooth in discoverable mode and sends itself to the target device. The user must accept the incoming file and install the program, after which the worm infects the machine.
Attacks based on vulnerabilities in software applications
Other attacks are based on flaws in the OS or applications on the phone.
Web browser
The mobile web browser is an emerging attack vector for mobile devices. Just as common Web browsers, mobile web browsers are extended from pure web navigation with widgets and plug-ins or are completely native mobile browsers.
Jailbreaking the iPhone with firmware 1.1.1 was based entirely on vulnerabilities on the web browser. In this case, there was a vulnerability based on a stack-based buffer overflow in a library used by the web browser ( LibTIFF). A similar vulnerability in the web browser for Android was discovered in October 2008.library
A library is a collection of Book, books, and possibly other Document, materials and Media (communication), media, that is accessible for use by its members and members of allied institutions. Libraries provide physical (hard copies) or electron ...
, but significantly differed in that Android's sandboxing architecture limited the effects of this vulnerability to the Web browser process.
Smartphones are also victims of classic Web piracy
Piracy is an act of robbery or criminal violence by ship or boat-borne attackers upon another ship or a coastal area, typically with the goal of stealing cargo and valuable goods, or taking hostages. Those who conduct acts of piracy are call ...
such as phishing, malicious websites, and background-running software. The big difference is that smartphones do not yet have strong antivirus software
Antivirus software (abbreviated to AV software), also known as anti-malware, is a computer program used to prevent, detect, and remove malware.
Antivirus software was originally developed to detect and remove computer viruses, hence the name ...
available.wiki
A wiki ( ) is a form of hypertext publication on the internet which is collaboratively edited and managed by its audience directly through a web browser. A typical wiki contains multiple pages that can either be edited by the public or l ...
s are some of the most common interactive websites. Due to the tremendous growth of the Internet, there has been a rapid rise in the number of security breaches experienced by individuals and businesses.
Mobile browser users can balance usage and caution in several ways,antivirus
Antivirus software (abbreviated to AV software), also known as anti-malware, is a computer program used to prevent, detect, and remove malware.
Antivirus software was originally developed to detect and remove computer viruses, hence the name ...
and anti-spyware programs is the most effective way of protecting the computer, as they offer protection against malware, spyware, and viruses. Additionally, they use firewalls, which are typically installed between trusted networks or devices and the Internet. By acting as a web server, the firewall prevents external users from accessing the internal computer system.
Operating system
Sometimes it is possible to overcome the security safeguards by modifying the operating system
An operating system (OS) is system software that manages computer hardware and software resources, and provides common daemon (computing), services for computer programs.
Time-sharing operating systems scheduler (computing), schedule tasks for ...
(OS) itself, such as the manipulation of firmware
In computing
Computing is any goal-oriented activity requiring, benefiting from, or creating computer, computing machinery. It includes the study and experimentation of algorithmic processes, and the development of both computer hardware, h ...
and malicious signature certificates. These attacks are difficult.
In 2004, vulnerabilities in virtual machine
In computing, a virtual machine (VM) is the virtualization or emulator, emulation of a computer system. Virtual machines are based on computer architectures and provide the functionality of a physical computer. Their implementations may involve ...
s running on certain devices were revealed. It was possible to bypass the bytecode
Bytecode (also called portable code or p-code) is a form of instruction set designed for efficient execution by a software interpreter. Unlike human-readable source code, bytecodes are compact numeric codes, constants, and references (normal ...
verifier and access the native underlying operating system.Symbian
Symbian is a discontinued mobile operating system (OS) and computing platform designed for smartphones. It was originally developed as a proprietary software OS for personal digital assistants in 1998 by the Symbian Ltd. consortium. Symbian OS ...
Platform Security Architecture (PSA) is based on a central configuration file called SWIPolicy. In 2008, it was possible to manipulate the Nokia firmware before it was installed. In fact, some downloadable versions of this file were human-readable, so it was possible to modify and change the image of the firmware. This vulnerability was solved by an update from Nokia.
In theory, smartphones have an advantage over hard drives since the OS files are in read-only memory
Read-only memory (ROM) is a type of non-volatile memory used in computers and other electronic devices. Data stored in ROM cannot be electronically modified after the manufacture of the memory device. Read-only memory is useful for storing sof ...
(ROM) and cannot be changed by malware. However, in some systems it was possible to circumvent this: in the Symbian OS
Symbian is a discontinued mobile operating system (OS) and computing platform designed for smartphones. It was originally developed as a proprietary software OS for personal digital assistants in 1998 by the Symbian Ltd. consortium. Symbian OS ...
, it was possible to overwrite a file with a file of the same name. On the Windows OS, it was possible to change a pointer from a general configuration file to an editable file.
When an application is installed, the signing of this application is verified by a series of certificates. One can create a valid signature
A signature (; from , "to sign") is a depiction of someone's name, nickname, or even a simple "X" or other mark that a person writes on documents as a proof of identity and intent. Signatures are often, but not always, Handwriting, handwritt ...
without using a valid certificate and add it to the list. In the Symbian OS, all certificates are in the directory . With firmware changes explained above, it is very easy to insert a seemingly valid but malicious certificate.
Android is the OS that has been attacked the most, because it has the largest userbase. A cybersecurity company reported to have blocked about 18 million attacks in 2016.
Attacks based on hardware vulnerabilities
Electromagnetic waveforms
In 2015, researchers at the French government agency '' Agence nationale de la sécurité des systèmes d'information'' (ANSSI, ) demonstrated the capability to trigger the voice interface of certain smartphones remotely by using "specific electromagnetic
In physics, electromagnetism is an interaction that occurs between particles with electric charge via electromagnetic fields. The electromagnetic force is one of the four fundamental forces of nature. It is the dominant force in the interacti ...
waveforms".[
* ] The exploit took advantage of antenna-properties of headphone wires while plugged into the audio-output jacks of the vulnerable smartphones and effectively spoofed audio input to inject commands via the audio interface.
Juice jacking
Juice jacking is a physical or hardware vulnerability specific to mobile platforms. Utilizing the dual purpose of the USB charge port, many devices have been susceptible to having data exfiltrated from, or malware installed onto, a mobile device by utilizing malicious charging kiosks set up in public places or hidden in normal charge adapters.
Jailbreaking and rooting
Jailbreaking is also a physical access vulnerability, in which a mobile device user hacks into device to unlock it, exploiting weaknesses in the operating system. Mobile device users take control of their own device by jailbreaking it, allowing them to customize the interface by installing applications, change system settings that are not allowed on the devices, tweak OS processes, and run uncertified programs. This openness exposes the device to a variety of malicious attacks which can compromise private data.
Password cracking
In 2010, researchers from the University of Pennsylvania investigated the possibility of cracking a device's password through a smudge attack
A smudge attack is an information extraction attack that Password cracking, discerns the password input of a touchscreen device such as a smartphone or tablet computer from fingerprint smudges. A team of researchers at the University of Pennsylvan ...
(literally imaging the finger smudges on the screen to discern the user's password).[
] The researchers were able to discern the device password up to 68% of the time under certain conditions.[ Outsiders may perform over-the-shoulder surveillance on victims, such as watching specific keystrokes or pattern gestures, to unlock device password or passcode.
]
Malicious software (malware)
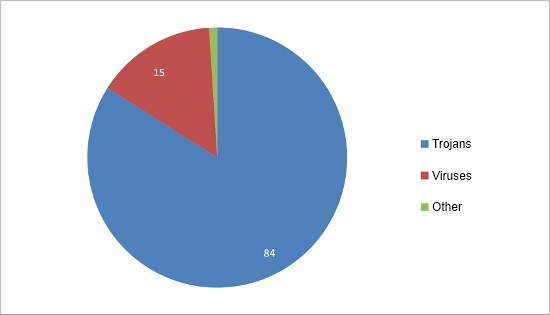 As smartphones are a permanent point of access to the Internet (they are often turned on), they can be compromised with malware as easily as computers. A
As smartphones are a permanent point of access to the Internet (they are often turned on), they can be compromised with malware as easily as computers. A malware
Malware (a portmanteau of ''malicious software'')Tahir, R. (2018)A study on malware and malware detection techniques . ''International Journal of Education and Management Engineering'', ''8''(2), 20. is any software intentionally designed to caus ...
is a computer program that aims to harm the system in which it resides.
Trojans, worms
The World Register of Marine Species (WoRMS) is a taxonomic database that aims to provide an authoritative and comprehensive catalogue and list of names of marine organisms.
Content
The content of the registry is edited and maintained by scien ...
and viruses
A virus is a submicroscopic infectious agent that replicates only inside the living cells of an organism. Viruses infect all life forms, from animals and plants to microorganisms, including bacteria and archaea. Viruses are found in almo ...
are all considered malware. A Trojan is a program on a device that allows external users to connect discreetly. A worm is a program that reproduces on multiple computers across a network. A virus is a malicious software designed to spread to other computers by inserting itself into legitimate programs and running programs in parallel.
Malware is far less numerous and serious to smartphones as it is to computers. Nonetheless, recent studies show that the evolution of malware in smartphones have rocketed in the last few years posing a threat to analysis and detection.
Problematic common apps and pre-installed software
Various common apps installed by millions can intrude on privacy, even if they were installed from a trusted software distribution service like the Google Play Store. For example, in 2022 it was shown that the popular app TikTok
TikTok, known in mainland China and Hong Kong as Douyin (), is a social media and Short-form content, short-form online video platform owned by Chinese Internet company ByteDance. It hosts user-submitted videos, which may range in duration f ...
collects a lot of data and is required to make it available to the Chinese Communist Party
The Communist Party of China (CPC), also translated into English as Chinese Communist Party (CCP), is the founding and One-party state, sole ruling party of the People's Republic of China (PRC). Founded in 1921, the CCP emerged victorious in the ...
(CCP) due to a national security law. This includes personal information on millions of Americans.
The firmware and "stock software" preinstalled on devices – and updated with preinstalled software – can also have undesired components or privacy-intruding default configurations or substantial security vulnerabilities. In 2019, Kryptowire identified Android devices with malicious firmware that collected and transmitted sensitive data without users' consent.
Analysis of data traffic by popular smartphones running variants of Android found substantial by-default data collection and sharing with no opt-out by pre-installed software. This issue also can't be addressed by conventional security patches. Outgoing Internet traffic can be analyzed with packet analyzer
A packet analyzer (also packet sniffer or network analyzer) is a computer program or computer hardware such as a packet capture appliance that can analyze and log traffic that passes over a computer network or part of a network. Packet capt ...
s and with firewall apps like the NetGuard firewall app for Android that allows reading blocked traffic logs.
Malware attacks
Typically, an attack on a smartphone made by malware takes place in three phases: the infection of a host, the accomplishment of its goal, and the spread of the malware to other systems. Malware often uses the resources offered by infected smartphones. It will use the output devices such as Bluetooth or infrared
Infrared (IR; sometimes called infrared light) is electromagnetic radiation (EMR) with wavelengths longer than that of visible light but shorter than microwaves. The infrared spectral band begins with the waves that are just longer than those ...
, but it may also use the address book or email address of the person to infect the user's acquaintances. The malware exploits the trust that is given to data sent by an acquaintance.
Infection
Infection is the method used by malware to gain access to the smartphone; it may exploit an internal vulnerability or rely on the gullibility of the user. Infections are classified into four classes according to their degree of user interaction:
# Explicit permission – The most benign interaction is to ask the user if it is allowed to infect the machine, clearly indicating its potential malicious behavior. This is typical behavior of a proof of concept
A proof of concept (POC or PoC), also known as proof of principle, is an inchoate realization of a certain idea or method in order to demonstrate its feasibility or viability. A proof of concept is usually small and may or may not be complete ...
malware.
# Implied permission – This infection is based on the fact that the user has a habit of installing software. Most Trojans try to seduce the user into installing attractive applications (like games or useful applications) that actually contain malware.
# Common interaction – This infection is related to a common behavior, such as opening an MMS or email.
# No interaction – The device is infected without the user taking action. This class of infection is the most dangerous, as it is both unapproved and automatic.
Accomplishment of its goal
Once the malware has infected a phone, it will also seek to accomplish its goal, which is usually one of the following:
* Monetary damages – The attacker can steal user data and either sell them to the same user or sell to a third party.
* Data or device damage – Malware can partially damage the device or delete or modify data on the device.
* Concealed damage – The two aforementioned types of damage are detectable, but the malware can also leave a backdoor for future attacks or even conduct wiretaps.
Spread to other systems
Once the malware has infected a smartphone, it aims to spread to a new host. This usually occurs to proximate devices via Wi-Fi, Bluetooth, or infrared; or to remote networks via telephone calls, SMS, or emails.

Examples
Viruses and Trojans
* Cabir (also known as Caribe, SybmOS/Cabir, Symbian/Cabir, and EPOC.cabir) is the name of a computer worm developed in 2004, designed to infect mobile phones running Symbian OS
Symbian is a discontinued mobile operating system (OS) and computing platform designed for smartphones. It was originally developed as a proprietary software OS for personal digital assistants in 1998 by the Symbian Ltd. consortium. Symbian OS ...
. It is believed to have been the first computer worm able to infect mobile phones.
* Commwarrior, created on March 7, 2005, was the first worm able to infect many machines from MMS. It is sent as COMMWARRIOR.ZIP containing the file COMMWARRIOR.SIS. When this file is executed, Commwarrior attempts to connect to nearby devices by Bluetooth or infrared under a random name. It then attempts to send MMS message to the contacts in the smartphone with different header messages for each person, who receive the MMS and often open them without further verification.
* Phage was the first Palm OS
Palm OS (also known as Garnet OS) is a discontinued mobile operating system initially developed by Palm, Inc., for personal digital assistants (PDAs) in 1996. Palm OS was designed for ease of use with a touchscreen-based graphical user interface. ...
virus discovered. It transfers to the Palm from a PC via synchronization
Synchronization is the coordination of events to operate a system in unison. For example, the Conductor (music), conductor of an orchestra keeps the orchestra synchronized or ''in time''. Systems that operate with all parts in synchrony are sa ...
. It infects all applications in the smartphone and embeds its own code to function without the user and the system detecting it. From the system's perspective, all the applications behave as expected.
* RedBrowser is a Trojan based on Java
Java is one of the Greater Sunda Islands in Indonesia. It is bordered by the Indian Ocean to the south and the Java Sea (a part of Pacific Ocean) to the north. With a population of 156.9 million people (including Madura) in mid 2024, proje ...
. The Trojan masquerades as a program called "RedBrowser" which allows the user to visit WAP sites without a WAP connection. During application installation, the user sees a request on their phone that the application needs permission to send messages. If the user accepts, RedBrowser can send SMS to paid call centers. This program uses the smartphone's connection to social networks (e.g., Facebook
Facebook is a social media and social networking service owned by the American technology conglomerate Meta Platforms, Meta. Created in 2004 by Mark Zuckerberg with four other Harvard College students and roommates, Eduardo Saverin, Andre ...
, Twitter
Twitter, officially known as X since 2023, is an American microblogging and social networking service. It is one of the world's largest social media platforms and one of the most-visited websites. Users can share short text messages, image ...
) to get the contact information for the user's acquaintances (provided the required permissions have been given) and will send them messages.
* WinCE.PmCryptic.A is a malicious software on Windows Mobile which aims to earn money for its authors. It uses the infestation of memory cards that are inserted in the smartphone to spread more effectively.
* CardTrap is a virus that is available on different types of smartphones, which aims to deactivate the system and third-party applications. It works by replacing the files used to start the smartphone and applications to prevent them from executing. There are different variants of this virus such as Cardtrap.A for SymbOS devices. It also infects the memory card with malware capable of infecting Windows
Windows is a Product lining, product line of Proprietary software, proprietary graphical user interface, graphical operating systems developed and marketed by Microsoft. It is grouped into families and subfamilies that cater to particular sec ...
.
* Ghost Push is malicious software on Android OS which automatically roots
A root is the part of a plant, generally underground, that anchors the plant body, and absorbs and stores water and nutrients.
Root or roots may also refer to:
Art, entertainment, and media
* ''The Root'' (magazine), an online magazine focusin ...
the Android device and installs malicious applications directly to system partition. It then unroots the device to prevent users from removing the threat by master reset (the threat can be removed only by reflashing). It cripples the system resources, executes quickly, and is hard to detect.
Ransomware
Mobile ransomware is a type of malware that locks users out of their mobile devices in a pay-to-unlock-your-device ploy. It has significantly grown as a threat category since 2014. Mobile users are often less security-conscious – particularly as it pertains to scrutinizing applications and web links – and trust the mobile device's native protection capability.
Mobile ransomware poses a significant threat to businesses reliant on instant access and availability of their proprietary information and contacts. The likelihood of a traveling businessman paying a ransom to unlock their device is significantly higher since they are at a disadvantage given inconveniences such as timeliness and less direct access to IT staff. Recent ransomware attacks have caused many Internet-connected devices to not work and are costly for companies to recover from.
Spyware
* Pegasus
Pegasus (; ) is a winged horse in Greek mythology, usually depicted as a white stallion. He was sired by Poseidon, in his role as horse-god, and foaled by the Gorgon Medusa. Pegasus was the brother of Chrysaor, both born from Medusa's blood w ...
– In 2021, journalists and researchers reported the discovery of spyware developed and distributed by a private company which can and has been used to infect both iOS and Android smartphones often – partly via use of 0-day exploits – without the need for any user-interaction or significant clues to the user. The spyware is then used to exfiltrate data, track user locations, capture film through its camera, and activate the microphone at any time.
* Flexispy is a Symbian application that can be considered a Trojan. The program sends all information received and sent from the smartphone to a Flexispy server. It was originally created to protect children and spy on adulterous spouses.
Portability of malware across platforms
Attackers can make their malware target multiple platforms. Some malware attacks operating systems but is able to spread across different systems.
To begin with, malware can use runtime environments like Java virtual machine
A Java virtual machine (JVM) is a virtual machine that enables a computer to run Java programs as well as programs written in other languages that are also compiled to Java bytecode. The JVM is detailed by a specification that formally descr ...
or the .NET Framework. They can also use other libraries present in many operating systems. Some malware carries several executable files in order to run in multiple environments, utilizing these during the propagation process. In practice, this type of malware requires a connection between the two operating systems to use as an attack vector. Memory cards can be used for this purpose, or synchronization software can be used to propagate the virus.
Countermeasures
Mobile security is divided into different categories, as methods do not all act at the same level and are designed to prevent different threats. These methods range from the management of security by the operating system (protecting the system from corruption by an application) to the behavioral education of the user (preventing the installation of a suspicious software).
Security in operating systems
The first layer of security in a smartphone is the operating system
An operating system (OS) is system software that manages computer hardware and software resources, and provides common daemon (computing), services for computer programs.
Time-sharing operating systems scheduler (computing), schedule tasks for ...
. Beyond needing to handle the usual roles (e.g., resource management
In organizational studies, resource management is the efficient and effective development of an organization's resources when they are needed. Such resources may include the financial resources, inventory, human skills, production resources, or ...
, scheduling processes) on the device, it must also establish the protocols for introducing external applications and data without introducing risk.
A central paradigm in mobile operating systems is the idea of a sandbox
A sandbox is a sandpit, a wide, shallow playground construction to hold sand, often made of wood or plastic.
Sandbox or sand box may also refer to:
Arts, entertainment, and media
* Sandbox (band), a Canadian rock music group
* Sandbox (Gu ...
. Since smartphones are currently designed to accommodate many applications, they must have mechanisms to ensure these applications are safe for the phone itself, for other applications and data on the system, and for the user. If a malicious program reaches a mobile device, the vulnerable area presented by the system must be as small as possible. Sandboxing extends this idea to compartmentalize different processes, preventing them from interacting and damaging each other. Based on the history of operating systems, sandboxing has different implementations. For example, where iOS
Ios, Io or Nio (, ; ; locally Nios, Νιός) is a Greek island in the Cyclades group in the Aegean Sea. Ios is a hilly island with cliffs down to the sea on most sides. It is situated halfway between Naxos and Santorini. It is about long an ...
will focus on limiting access to its public API for applications from the App Store by default, Managed Open In allows you to restrict which apps can access which types of data. Android bases its sandboxing on its legacy of Linux
Linux ( ) is a family of open source Unix-like operating systems based on the Linux kernel, an kernel (operating system), operating system kernel first released on September 17, 1991, by Linus Torvalds. Linux is typically package manager, pac ...
and TrustedBSD
FreeBSD is a free-software Unix-like operating system descended from the Berkeley Software Distribution (BSD). The first version was released in 1993 developed from 386BSD, one of the first fully functional and free Unix clones on affordable h ...
.
The following points highlight mechanisms implemented in operating systems, especially Android.
; Rootkit detectors
: The intrusion of a rootkit
A rootkit is a collection of computer software, typically malicious, designed to enable access to a computer or an area of its software that is not otherwise allowed (for example, to an unauthorized user) and often masks its existence or the exist ...
in the system is a great danger in the same way as on a computer. It is important to prevent such intrusions, and to be able to detect them as often as possible. Indeed, there is concern that with this type of malicious program, an attacker could partially or completely bypass the device security, or acquire administrator rights. If this happens, nothing prevents the attacker from studying or disabling the safety features that were circumvented, deploying the applications they want, or disseminating a method of intrusion by a rootkit to a wider audience.
: An example of a defense mechanism against this is the chain of trust (such as in iOS). This mechanism relies on signatures from applications required to start the operating system, and a certificate signed by the manufacturer (Apple). In the event that the signature checks are inconclusive, the device detects this and stops the boot-up. If the operating system is compromised due to jailbreaking, rootkit detection may not work if it is disabled by the jailbreak method or software is loaded after jailbreak disables Rootkit Detection.
; Process isolation
: Android uses mechanisms of user process isolation inherited from Linux. Each application has a user associated with it, and a tuple ( UID, GID). This approach serves as a sandbox: while applications can be malicious, they cannot get out of the sandbox reserved for them by their identifiers, and thus cannot interfere with the proper functioning of the system. For example, since it is impossible for a process to end the process of another user, an application can thus not stop the execution of another application.
; File permissions
: From the legacy of Linux, filesystem permissions mechanisms also help with sandboxing. Permissions prevent a process from editing any files it wants. It is therefore not possible to freely corrupt files necessary for the operation of another application or system. Furthermore, in Android there is the method of locking memory permissions. It is not possible to change the permissions of files installed on the SD card from the phone, and consequently it is impossible to install applications.
; Memory protection
: In the same way as on a computer, memory protection prevents privilege escalation
Privilege escalation is the act of exploiting a Software bug, bug, a Product defect, design flaw, or a configuration oversight in an operating system or software application to gain elevated access to resource (computer science), resources that ar ...
. This could occur if a process managed to reach an area allocated to other processes, where it could write in the memory of a process with rights superior to its own (with 'root' in the worst case) and perform actions beyond its permissions. It would suffice to insert function calls are authorized by the privileges of the malicious application.
; Development through runtime environments
: Software is often developed in high-level languages, which can control what is being done by a running program. For example, Java virtual machine
A Java virtual machine (JVM) is a virtual machine that enables a computer to run Java programs as well as programs written in other languages that are also compiled to Java bytecode. The JVM is detailed by a specification that formally descr ...
s continuously monitor the actions of the execution threads they manage, monitor and assign resources, and prevent malicious actions. Buffer overflows can be prevented by these controls.
Security software
Above the operating system security, there is a layer of security software. This layer is composed of individual components to strengthen various vulnerabilities: prevent malware, intrusions, the identification of a user as a human, and user authentication. It contains software components that have learned from their experience with computer security; however, on smartphones, this software must deal with greater constraints (see limitations).
; Antivirus and firewall
: An antivirus software can be deployed on a device to verify that it is not infected by a known threat, usually by signature detection software that detects malicious executable files. A mobile antivirus product would scan files and compare them against a database of known mobile malware code signatures.Turing test
The Turing test, originally called the imitation game by Alan Turing in 1949,. Turing wrote about the ‘imitation game’ centrally and extensively throughout his 1950 text, but apparently retired the term thereafter. He referred to ‘ iste ...
is used to distinguish between a human and a virtual user, often in the form of a CAPTCHA
Completely Automated Public Turing Test to tell Computers and Humans Apart (CAPTCHA) ( ) is a type of challenge–response authentication, challenge–response turing test used in computing to determine whether the user is human in order to de ...
.
; Biometric identification
: Another method to use is biometrics
Biometrics are body measurements and calculations related to human characteristics and features. Biometric authentication (or realistic authentication) is used in computer science as a form of identification and access control. It is also used t ...
, a technique of identifying a person by means of their morphology (e.g., by recognition of the face or eye) or their behavior (e.g., their signature or way of writing). One advantage of using biometric security is that users can avoid having to remember a password or other secret combination to authenticate and prevent malicious users from accessing their devices. In a system with strong biometric security, only the primary user can access the smartphone.
Resource monitoring in the smartphone
Should a malicious application pass the security barriers, it can take the actions for which it was designed. However, this activity can be sometimes detected by monitoring the various resources used on the phone. Depending on the goals of the malware, the consequences of infection are not always the same; all malicious applications are not intended to harm the devices on which they are deployed.
The following resources are only indications and do not provide certainty about the legitimacy of the activity of an application. However, these criteria can help target suspicious applications, especially if several criteria are combined.
; Battery
: Some malware is aimed at exhausting the energy resources of the phone. Monitoring the energy consumption of the phone can be a way to detect certain malware applications.
; Memory usage
: Memory usage is inherent in any application. However, if one finds that an unnecessary or unexpected proportion of memory is used by an application, it may be flagged as suspicious.
; Network traffic
: As part of normal operation on a smartphone, many applications are bound to connect via the network. However, an application using a lot of bandwidth can be strongly suspected of attempting to communicate a lot of information and disseminate data to many other devices. This observation only allows a suspicion, because some legitimate applications can be very resource-intensive in terms of network communications, the best example being streaming video
Video on demand (VOD) is a media distribution system that allows users to access videos, television shows and films digitally on request. These multimedia are accessed without a traditional video playback device and a typical static broadcasting ...
.
; Services
: One can monitor the activity of various services of a smartphone. During certain moments, some services should not be active, and if one is detected, the application should be suspected. For example, the sending of an SMS when the user is filming video: this communication does not make sense and is suspicious; malware may attempt to send SMS while its activity is masked.
Network surveillance
Network traffic Network traffic or data traffic is the amount of data moving across a network at a given point of time. Network data in computer networks is mostly encapsulated in network packets, which provide the load in the network. Network traffic is the main ...
exchanged by phones can be monitored. One can place safeguards in network routing points in order to detect abnormal behavior. As the mobile's use of network protocols is much more constrained than that of a computer, expected network data streams can be predicted (e.g., the protocol for sending an SMS), which permits detection of anomalies in mobile networks.
; Spam filters
: Similar to email exchanges, spam
Spam most often refers to:
* Spam (food), a consumer brand product of canned processed pork of the Hormel Foods Corporation
* Spamming, unsolicited or undesired electronic messages
** Email spam, unsolicited, undesired, or illegal email messages
...
can be detected through means of mobile communications (SMS, MMS). It is therefore possible to detect and minimize this kind of attempt by filters deployed on network infrastructure that is relaying these messages.
; Encryption of stored or transmitted information
: Because it is always possible that data exchanged can be intercepted, communications and information storage rely on encryption to prevent a malicious entity from using any data obtained during communications. However, this poses the problem of key exchange for encryption algorithms, which requires a secure channel.
; Telecom network monitoring
: The networks for SMS and MMS exhibit predictable behavior, and there is not as much liberty compared with what one can do with protocols such as TCP or UDP. This implies that one cannot predict the flow of data from common web protocols; a protocol might generate very little traffic by consulting simple pages (rarely) or generate heavy traffic by using video streaming. On the other hand, messages exchanged via mobile phone have a framework and a specific model, and the user does not, in a normal case, have the freedom to intervene in the details of these communications. Therefore, if an abnormality is found in the flux of network data in the mobile networks, the potential threat can be quickly detected.
Manufacturer surveillance
In the production and distribution chain for mobile devices, manufacturers are responsibility for ensuring that devices are delivered in a basic configuration without vulnerabilities. Most users are not experts and many of them are not aware of the existence of security vulnerabilities, so the device configuration as provided by manufacturers will be retained by many users. Some smartphone manufacturers add Titan M2s (a security hardware chip) to increase mobile security.
; Remove debug mode
: Phones are sometimes set in a debug mode during manufacturing, but this mode must be disabled before the phone is sold. This mode allows access to features not intended for routine use by a user. Due to the speed of development and production, distractions occur, and some devices are sold in debug mode. This kind of deployment exposes mobile devices to exploits that utilize this oversight.
; Default settings
: When a smartphone is sold, its default settings must be correct, and not leave security gaps. The default configuration is not always changed, so a good initial setup is essential for users. There are, for example, default configurations that are vulnerable to denial-of-service attacks.
; Security audit of apps
: App stores have emerged alongside smartphones. Both users and providers are tasked with examining the immense volume of apps available, from different points of view (e.g., security, content). Security audits should be particularly cautious, because if a fault is not detected, the application can spread very quickly within a few days, and infect a significant number of devices.
; Detect suspicious applications demanding rights
: When installing applications, it is good to warn the user against sets of permissions that, grouped together, seem potentially dangerous, or at least suspicious. Frameworks like such as Kirin, on Android, attempt to detect and prohibit certain sets of permissions.
; Revocation procedures
: First developed for Android, a process known as 'remote revocation' can remotely and globally uninstall an application from any device that has it. This means the spread of a malicious application that evaded security checks can be immediately stopped when the threat is discovered.
; Avoid heavily customized systems
: Manufacturers are tempted to overlay custom layers on existing operating systems, with the dual purpose of offering customized options and disabling or charging for certain features. This has the dual effect of risking the introduction of new bugs in the system, coupled with an incentive for users to modify the systems to circumvent the manufacturer's restrictions. These systems are rarely as stable and reliable as the original and may suffer from phishing attempts or other exploits.
; Improve software patch processes
: New versions of various software components of a smartphone, including operating systems, are regularly published. These 'patches' correct flaws over time. Nevertheless, manufacturers often do not deploy these updates to their devices in a timely fashion, and sometimes not at all. Thus, vulnerabilities can persist when they could be corrected; while they exist and are generally known, they are easily exploitable.
User awareness
The user has a large responsibility in the cycle of security. This can be as simple as using a password, or as detailed as precisely controlling which permissions are granted to applications. This precaution is especially important if the user is an employee of a company who stores business data on the device.
Much malicious behavior is allowed by user carelessness. Smartphone users were found to ignore security messages during application installation, especially during application selection and checking application reputation, reviews, security, and agreement messages. A recent survey by internet security
Internet security is a branch of computer security. It encompasses the Internet, browser security, web site security, and network security as it applies to other applications or operating systems as a whole. Its objective is to establish rules ...
experts BullGuard showed a lack of insight concerning the rising number of malicious threats affecting mobile phones, with 53% of users claiming that they are unaware of security software for smartphones. A further 21% argued that such protection was unnecessary, and 42% admitted it hadn't crossed their mind ("Using APA," 2011). These statistics show that consumers are not concerned about security risks because they believe it is not a serious problem. However, in truth, smartphones are effectively handheld computers and are just as vulnerable.
The following are precautions that a user can take to manage security on a smartphone:
; Be skeptical
: A user should not believe everything that may be presented, as some information may be wrong, misleading, phishing, or attempting to distribute a malicious application. It is therefore advisable to check an application's reputation before buying or installing it.
; Permissions given to applications
: The mass distribution of applications necessitates different permissions mechanisms for each operating system. It is necessary to clarify these permissions mechanisms to users, as they differ between systems and can be confusing. In addition, it is rarely feasible (or possible) to modify large sets of permissions requested by an application. However, this can be a source of risk because a user can grant an application excessive rights beyond what is necessary. For example, a note-taking application does not require access to the geolocation service to function. During installation, the user must consider an application's privileges and should not accept the installation if the requested rights are inconsistent.
; Be careful
: A user's phone can be protected through simple gestures and precautions, such as locking the smartphone when it is not in use, not leaving the device unattended, not blindly trusting applications, not storing sensitive data, or encrypting sensitive data that cannot be separated from the device.
;Disconnect unused peripheral devices
:According to ''NIST Guidelines for Managing the Security of Mobile Devices 2013'', it is recommended to "Restrict user and application access to hardware, such as the digital camera, GPS, Bluetooth interface, USB interface, and removable storage". This can include removing permissions and configurations for unused peripheral devices.
Enable Android Device Encryption
:The latest Android smartphones come with a built-in encryption setting for securing all the information saved on your device. This makes it difficult for a hacker to extract and decipher the information in case your device is compromised. It can be accessed via: ''Settings → Security → Encrypt Phone + Encrypt SD Card.''
; Ensure data
: Smartphones have significant memory capacity and can carry several gigabytes of data. The user must be careful about what data it carries and whether they should be protected (such as files containing bank information or business data). The user must have the prudence to avoid the transmission of sensitive data on a smartphone, which can be easily stolen. Furthermore, when a user gets rid of a device, they must be sure to remove all personal data first.
These precautions reduce the ability for people or malicious applications to exploit a user's smartphone. If users are careful, many attacks can be defeated, especially phishing and applications seeking only to obtain rights on a device.
Centralized storage
One form of mobile protection allows companies to control the delivery and storage of text messages, by hosting the messages on a company server, rather than on the sender or receiver's phone. When certain conditions are met, such as an expiration date, the messages are deleted.
Limitations
The security mechanisms mentioned in this article are to a large extent inherited from knowledge and experience with computer security. The elements composing the two device types are similar, and there are common measures that can be used, such as antivirus software and firewalls. However, the implementation of these solutions is not necessarily possible (or is at least highly constrained) within a mobile device. The reason for this difference is the technical resources available to computers and mobile devices: even though the computing power of smartphones is becoming faster, they have other limitations:
* Single-task system – Some operating systems, including some still commonly used, are single-tasking. Only the foreground task is executed. It is difficult to introduce applications such as antivirus and firewall on such systems, because they cannot perform their monitoring while the user is operating the device, when monitoring is most needed.
* Energy autonomy – A critical limitation for smartphones is energy autonomy. It is important that security mechanisms not consume too much battery resources, which could dramatically undermine the smartphone's autonomy and usage.
* Network – Directly related to battery life, network utilization should not be too high. From the point of view of energy consumption, network utilization is one of the most expensive resources. Nonetheless, some calculations may need to be relocated to remote servers in order to preserve the battery. This balance can make implementation of certain intensive computation mechanisms a delicate situation.
Furthermore, it is common that even if updates exist, or can be developed, they are not always deployed. For example, a user may not be aware of operating system updates; or a user may discover known vulnerabilities that are not corrected until the end of a long development cycle, which allows time to exploit the loopholes.
Next generation of mobile security
The following mobile environments are expected to make up future security frameworks:
; Rich operating system: This category will contain traditional mobile operating systems like Android, iOS, Symbian OS, or Windows Phone. They will provide the traditional functionality and security of an OS to the applications.
;Secure Operating System (Secure OS): This category features a secure kernel which will run in parallel with a fully featured Rich OS, on the same processor core. It will include drivers for the Rich OS ("normal world") to communicate with the secure kernel ("secure world"). The trusted infrastructure could include interfaces like the display or keypad to regions of PCI-E address space and memories.
;Trusted Execution Environment (TEE): This environment will be made up of hardware and software. It helps control of access rights and houses sensitive applications, which need to be isolated from the Rich OS. It effectively acts as a firewall between the "normal world" and "secure world".
; Secure Element (SE): The SE consists of tamper-resistant hardware and associated software or separate isolated hardware. It can provide high levels of security and work in tandem with the TEE. The SE will be mandatory for hosting proximity payment applications or official electronic signatures. SE may connect, disconnect, block peripheral devices, and operate separate set of hardware.
; Security Applications (SA): Numerous security applications are available on app stores, providing protection from viruses and performing vulnerability assessment.
See also
* Browser security
* Computer security
Computer security (also cybersecurity, digital security, or information technology (IT) security) is a subdiscipline within the field of information security. It consists of the protection of computer software, systems and computer network, n ...
* Information security
Information security is the practice of protecting information by mitigating information risks. It is part of information risk management. It typically involves preventing or reducing the probability of unauthorized or inappropriate access to data ...
* Mobile Malware
* Phone hacking
Phone hacking is the practice of exploring a mobile device, often using computer exploits to analyze everything from the lowest memory and CPU levels up to the highest file system and process levels. Modern open source tooling has become f ...
* Telephone tapping
Wiretapping, also known as wire tapping or telephone tapping, is the monitoring of telephone and Internet-based conversations by a third party, often by covert means. The wire tap received its name because, historically, the monitoring connecti ...
* Wireless Public Key Infrastructure (WPKI)
* Wireless security
* Defense strategy (computing)
In computing, defense strategy is a concept and practice used by computer designers, users, and IT personnel to reduce computer security risks.
Common strategies
Boundary protection
Boundary protection employs security measures and devices to p ...
*
Notes
References
Books
*
*
*
*
Articles
*
*
*
*
*
*
*
*
*
*
*
*
*
*
*
*
*
*
*
*
*
*
*
*
*
*
*
Websites
*
*
Further reading
*
*
*
*
*
*
*
*
*
*
{{Malware
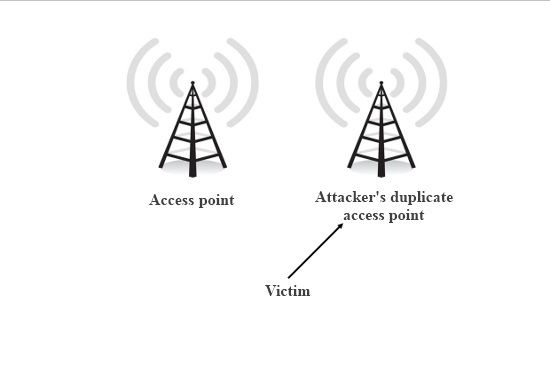 An attacker can try to eavesdrop on Wi-Fi communications to derive information (e.g., username, password). This type of attack is not unique to smartphones, but they are very vulnerable to these attacks because often Wi-Fi is their only means of communication and access the internet. The security of wireless networks (
An attacker can try to eavesdrop on Wi-Fi communications to derive information (e.g., username, password). This type of attack is not unique to smartphones, but they are very vulnerable to these attacks because often Wi-Fi is their only means of communication and access the internet. The security of wireless networks (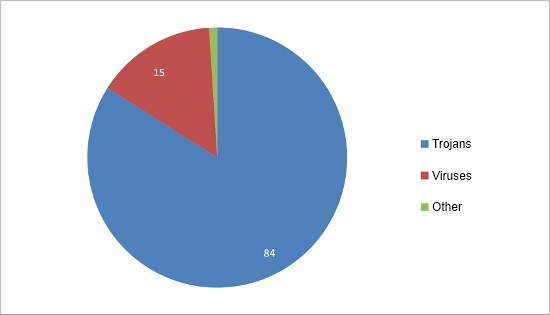 As smartphones are a permanent point of access to the Internet (they are often turned on), they can be compromised with malware as easily as computers. A
As smartphones are a permanent point of access to the Internet (they are often turned on), they can be compromised with malware as easily as computers. A 