|
Polipo
Polipo is a lightweight caching and forwarding web proxy server. It has a wide variety of uses, from aiding security by filtering traffic; to caching web, DNS and other computer network lookups for a group of people sharing network resources; to speeding up a web server by caching repeated requests. It can be configured to use on-disk cache and serve cached content when offline and perform various forms of content filtering. To minimize latency, Polipo both pipelines multiple resource requests and multiplexes multiple transactions onto the same TCP/IP connection. Polipo is HTTP 1.1-compliant, supports IPv4, IPv6, traffic filtering and privacy-enhancement. Polipo is free software released under the MIT License. Polipo ceased to be maintained on 6 November 2016 due to the increasingly widespread use of encryption (i.e. HTTPS) making caching proxies obsolete. Design Polipo is designed to be used as a personal web cache or a web cache shared among a few users to boost in ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
HTTP Pipelining
HTTP pipelining is a feature of HTTP/1.1 which allows multiple HTTP requests to be sent over a single TCP connection without waiting for the corresponding responses. HTTP/1.1 requires servers to respond to pipelined requests correctly, with non-pipelined but valid responses even if server does not support HTTP pipelining. Despite this requirement, many legacy HTTP/1.1 servers do not support pipelining correctly, forcing most HTTP clients to not use HTTP pipelining. The technique was superseded by multiplexing via HTTP/2, which is supported by most modern browsers. In HTTP/3, multiplexing is accomplished via QUIC which replaces TCP. This further reduces loading time, as there is no head-of-line blocking even if some packets are lost. Motivation and limitations The pipelining of requests results in a dramatic improvement in the loading times of HTML pages, especially over high latency connections such as satellite Internet connections. The speedup is less apparent on broadband ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Forward Proxy H2g2bob
Forward is a relative direction, the opposite of backward. Forward may also refer to: People * Forward (surname) Sports * Forward (association football) * Forward (basketball), including: ** Point forward ** Power forward (basketball) ** Small forward * Forward (ice hockey) ** Power forward (ice hockey) * In rugby football: ** Forwards (rugby league), in rugby league football ** Forwards (rugby union), in rugby union football * Forward Sports, a Pakistan sportswear brand * BK Forward, a Swedish club for association football and bandy Politics * Avante (political party) (Portuguese for ''forward''), a political party in Brazil * Forward (Belgium), a political party in Belgium * Forward (Denmark), a political party in Denmark * Forward (Greenland), a political party in Greenland * Forward Party (United States), a centrist American political party * Kadima (Hebrew for ''forward''), a political party in Israel * La République En Marche! (sometimes translated as ''Forward!''), a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Web Server
A web server is computer software and underlying hardware that accepts requests via HTTP (the network protocol created to distribute web content) or its secure variant HTTPS. A user agent, commonly a web browser or web crawler, initiates communication by making a request for a web page or other resource using HTTP, and the server responds with the content of that resource or an error message. A web server can also accept and store resources sent from the user agent if configured to do so. The hardware used to run a web server can vary according to the volume of requests that it needs to handle. At the low end of the range are embedded systems, such as a router that runs a small web server as its configuration interface. A high-traffic Internet website might handle requests with hundreds of servers that run on racks of high-speed computers. A resource sent from a web server can be a preexisting file (static content) available to the web server, or it can be generated ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
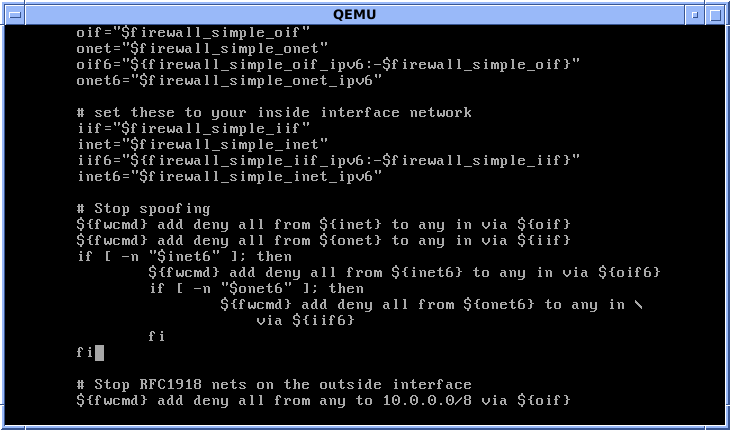
Shell Script
A shell script is a computer program designed to be run by a Unix shell, a command-line interpreter. The various dialects of shell scripts are considered to be scripting languages. Typical operations performed by shell scripts include file manipulation, program execution, and printing text. A script which sets up the environment, runs the program, and does any necessary cleanup or logging, is called a wrapper. The term is also used more generally to mean the automated mode of running an operating system shell; each operating system uses a particular name for these functions including batch files (MSDos-Win95 stream, OS/2), command procedures (VMS), and shell scripts (Windows NT stream and third-party derivatives like 4NT—article is at cmd.exe), and mainframe operating systems are associated with a number of terms. Shells commonly present in Unix and Unix-like systems include the Korn shell, the Bourne shell, and GNU Bash. While a Unix operating system may have a different d ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
User (computing)
A user is a person who utilizes a computer or network service. A user often has a user account and is identified to the system by a username (or user name). Other terms for username include login name, screenname (or screen name), account name, nickname (or nick) and handle, which is derived from the identical citizens band radio term. Some software products provide services to other systems and have no direct end users. End user End users are the ultimate human users (also referred to as operators) of a software product. The end user stands in contrast to users who support or maintain the product such as sysops, database administrators and computer technicians. The term is used to abstract and distinguish those who only use the software from the developers of the system, who enhance the software for end users. In user-centered design, it also distinguishes the software operator from the client who pays for its development and other stakeholders who may not directly ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
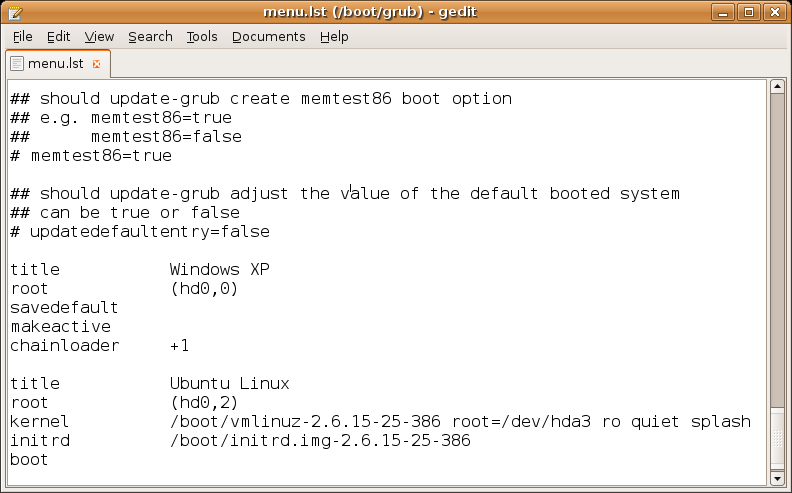
Configuration File
In computing, configuration files (commonly known simply as config files) are computer file, files used to configure the Parameter (computer programming), parameters and Initialization (programming), initial settings for some computer programs. They are used for user application software, applications, Server (computing), server processes and operating system settings. Some applications provide tools to create, modify, and verify the syntax of their configuration files; these sometimes have graphical interfaces. For other programs, system administrators may be expected to create and modify files by hand using a text editor, which is possible because many are human-editable plain text files. For server processes and operating-system settings, there is often no standard tool, but operating systems may provide their own graphical interfaces such as YaST or debconf. Some computer programs only read their configuration files at Booting, startup. Others periodically check the configur ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Keyboard
A computer keyboard is a peripheral input device modeled after the typewriter keyboard which uses an arrangement of buttons or keys to act as mechanical levers or electronic switches. Replacing early punched cards and paper tape technology, interaction via teleprinter-style keyboards have been the main input method for computers since the 1970s, supplemented by the computer mouse since the 1980s. Keyboard keys (buttons) typically have a set of characters engraved or printed on them, and each press of a key typically corresponds to a single written symbol. However, producing some symbols may require pressing and holding several keys simultaneously or in sequence. While most keys produce characters (letters, numbers or symbols), other keys (such as the escape key) can prompt the computer to execute system commands. In a modern computer, the interpretation of key presses is generally left to the software: the information sent to the computer, the scan code, tells it only whi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Command-line Interface
A command-line interpreter or command-line processor uses a command-line interface (CLI) to receive commands from a user in the form of lines of text. This provides a means of setting parameters for the environment, invoking executables and providing information to them as to what actions they are to perform. In some cases the invocation is conditional based on conditions established by the user or previous executables. Such access was first provided by computer terminals starting in the mid-1960s. This provided an interactive environment not available with punched cards or other input methods. Today, many users rely upon graphical user interfaces and menu-driven interactions. However, some programming and maintenance tasks may not have a graphical user interface and use a command line. Alternatives to the command-line interface include text-based user interface menus (for example, IBM AIX SMIT), keyboard shortcuts, and various desktop metaphors centered on the pointer (usual ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
HTTPS
Hypertext Transfer Protocol Secure (HTTPS) is an extension of the Hypertext Transfer Protocol (HTTP). It is used for secure communication over a computer network, and is widely used on the Internet. In HTTPS, the communication protocol is encrypted using Transport Layer Security (TLS) or, formerly, Secure Sockets Layer (SSL). The protocol is therefore also referred to as HTTP over TLS, or HTTP over SSL. The principal motivations for HTTPS are authentication of the accessed website, and protection of the privacy and integrity of the exchanged data while in transit. It protects against man-in-the-middle attacks, and the bidirectional encryption of communications between a client and server protects the communications against eavesdropping and tampering. The authentication aspect of HTTPS requires a trusted third party to sign server-side digital certificates. This was historically an expensive operation, which meant fully authenticated HTTPS connections were usually found only ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IPv6
Internet Protocol version 6 (IPv6) is the most recent version of the Internet Protocol (IP), the communication protocol, communications protocol that provides an identification and location system for computers on networks and routes traffic across the Internet. IPv6 was developed by the Internet Engineering Task Force (IETF) to deal with the long-anticipated problem of IPv4 address exhaustion, and is intended to replace IPv4. In December 1998, IPv6 became a Draft Standard for the IETF, which subsequently ratified it as an Internet Standard on 14 July 2017. Devices on the Internet are assigned a unique IP address for identification and location definition. With the rapid growth of the Internet after commercialization in the 1990s, it became evident that far more addresses would be needed to connect devices than the IPv4 address space had available. By 1998, the IETF had formalized the successor protocol. IPv6 uses 128-bit addresses, theoretically allowing 2128, or approximatel ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IPv4
Internet Protocol version 4 (IPv4) is the fourth version of the Internet Protocol (IP). It is one of the core protocols of standards-based internetworking methods in the Internet and other packet-switched networks. IPv4 was the first version deployed for production on SATNET in 1982 and on the ARPANET in January 1983. It is still used to route most Internet traffic today, even with the ongoing deployment of Internet Protocol version 6 (IPv6), its successor. IPv4 uses a 32-bit address space which provides 4,294,967,296 (232) unique addresses, but large blocks are reserved for special networking purposes. History Internet Protocol version 4 is described in IETF publication RFC 791 (September 1981), replacing an earlier definition of January 1980 (RFC 760). In March 1982, the US Department of Defense decided on the Internet Protocol Suite (TCP/IP) as the standard for all military computer networking. Purpose The Internet Protocol is the protocol that defines and enables internet ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
HTTP 1
The Hypertext Transfer Protocol (HTTP) is an application layer protocol in the Internet protocol suite model for distributed, collaborative, hypermedia information systems. HTTP is the foundation of data communication for the World Wide Web, where hypertext documents include hyperlinks to other resources that the user can easily access, for example by a mouse click or by tapping the screen in a web browser. Development of HTTP was initiated by Tim Berners-Lee at CERN in 1989 and summarized in a simple document describing the behavior of a client and a server using the first HTTP protocol version that was named 0.9. That first version of HTTP protocol soon evolved into a more elaborated version that was the first draft toward a far future version 1.0. Development of early HTTP Requests for Comments (RFCs) started a few years later and it was a coordinated effort by the Internet Engineering Task Force (IETF) and the World Wide Web Consortium (W3C), with work later moving to the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |