|
Ngrep
ngrep (network grep) is a network packet analyzer written by Jordan Ritter. It has a command-line interface, and relies upon the pcap library and the GNU regex library. ngrep supports Berkeley Packet Filter ( BPF) logic to select network sources or destinations or protocols, and also allows matching patterns or regular expressions in the data payload of packets using GNU grep syntax, showing packet data in a human-friendly way. ngrep is an open source application, and the source code is available to download from the ngrep site on SourceForge. It can be compiled and ported to multiple platforms, it works in many UNIX-like operating systems: Linux, Solaris, illumos, BSD, AIX, and also works on Microsoft Windows. Functionality ngrep is similar to tcpdump, but it has the ability to look for a regular expression in the payload of the packet, and show the matching packets on a screen or console. It allows users to see all unencrypted traffic being passed over the network, by p ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Jordan Ritter
Jordan Ritter (born February 1, 1978) is an American serial entrepreneur, software architect and angel investor. He is best known for his work at Napster, the file-sharing service he co-founded along with Shawn Fanning and others. His time at Napster was documented in Joseph Menn's book ''All the Rave: The Rise and Fall of Shawn Fanning's Napster'' and Alex Winter's film Downloaded. Early life Jordan Ritter was born in Northridge, California and grew up in Texas and Florida. Ritter skipped the 5th grade when he was 10, and later went on to graduate from the International Baccalaureate Program at Hillsborough High School. Ritter attended college at Lehigh University on scholarship, starting as a sophomore and pursuing a double major in music and computer science. He dropped out in 1998, relocating to Boston, Massachusetts to begin his career in computer security. Career Netect Ritter started out in the computer security industry, working as a paid hacker for the B ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Tcpdump
tcpdump is a data-network packet analyzer computer program that runs under a command line interface. It allows the user to display TCP/IP and other packets being transmitted or received over a network to which the computer is attached. Distributed under the BSD license, tcpdump is free software. Tcpdump works on most Unix-like operating systems: Linux, Solaris, FreeBSD, DragonFly BSD, NetBSD, OpenBSD, OpenWrt, macOS, HP-UX 11i, and AIX. In those systems, tcpdump uses the libpcap library to capture packets. The port of tcpdump for Windows is called WinDump; it uses WinPcap, the Windows version of libpcap. History tcpdump was originally written in 1988 by Van Jacobson, Sally Floyd, Vern Paxson and Steven McCanne who were, at the time, working in the Lawrence Berkeley Laboratory Network Research Group. By the late 1990s there were numerous versions of tcpdump distributed as part of various operating systems, and numerous patches that were not well coordinated. Michael ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Wireshark
Wireshark is a free and open-source packet analyzer. It is used for network troubleshooting, analysis, software and communications protocol development, and education. Originally named Ethereal, the project was renamed Wireshark in May 2006 due to trademark issues. Wireshark is cross-platform, using the Qt widget toolkit in current releases to implement its user interface, and using pcap to capture packets; it runs on Linux, macOS, BSD, Solaris, some other Unix-like operating systems, and Microsoft Windows. There is also a terminal-based (non-GUI) version called TShark. Wireshark, and the other programs distributed with it such as TShark, are free software, released under the terms of the GNU General Public License version 2 or any later version. Functionality Wireshark is very similar to tcpdump, but has a graphical front-end and integrated sorting and filtering options. Wireshark lets the user put network interface controllers into promiscuous mode (if supported b ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Packet Analyzer
A packet analyzer, also known as packet sniffer, protocol analyzer, or network analyzer, is a computer program or computer hardware such as a packet capture appliance, that can intercept and log traffic that passes over a computer network or part of a network. Packet capture is the process of intercepting and logging traffic. As data streams flow across the network, the analyzer captures each packet and, if needed, decodes the packet's raw data, showing the values of various fields in the packet, and analyzes its content according to the appropriate RFC or other specifications. A packet analyzer used for intercepting traffic on wireless networks is known as a wireless analyzer or WiFi analyzer. While a packet analyzer can also be referred to as a network analyzer or protocol analyzer these terms can also have other meanings. Protocol analyzer can technically be a broader, more general class that includes packet analyzers/sniffers. However, the terms are frequently used i ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Grep
grep is a command-line utility for searching plain-text data sets for lines that match a regular expression. Its name comes from the ed command ''g/re/p'' (''globally search for a regular expression and print matching lines''), which has the same effect. grep was originally developed for the Unix operating system, but later available for all Unix-like systems and some others such as OS-9. History Before it was named, grep was a private utility written by Ken Thompson to search files for certain patterns. Doug McIlroy, unaware of its existence, asked Thompson to write such a program. Responding that he would think about such a utility overnight, Thompson actually corrected bugs and made improvements for about an hour on his own program called s (short for "search"). The next day he presented the program to McIlroy, who said it was exactly what he wanted. Thompson's account may explain the belief that grep was written overnight. Thompson wrote the first version in PDP-11 asse ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Packet Analyzer
A packet analyzer, also known as packet sniffer, protocol analyzer, or network analyzer, is a computer program or computer hardware such as a packet capture appliance, that can intercept and log traffic that passes over a computer network or part of a network. Packet capture is the process of intercepting and logging traffic. As data streams flow across the network, the analyzer captures each packet and, if needed, decodes the packet's raw data, showing the values of various fields in the packet, and analyzes its content according to the appropriate RFC or other specifications. A packet analyzer used for intercepting traffic on wireless networks is known as a wireless analyzer or WiFi analyzer. While a packet analyzer can also be referred to as a network analyzer or protocol analyzer these terms can also have other meanings. Protocol analyzer can technically be a broader, more general class that includes packet analyzers/sniffers. However, the terms are frequently used i ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Pcap
In the field of computer network administration, pcap is an application programming interface (API) for capturing network traffic. While the name is an abbreviation of ''packet capture'', that is not the API's proper name. Unix-like systems implement pcap in the ''libpcap'' library; for Windows, there is a port of libpcap named ''WinPcap'' that is no longer supported or developed, and a port named ''Npcap'' for Windows 7 and later that is still supported. Monitoring software may use libpcap, WinPcap, or Npcap to capture network packets traveling over a computer network and, in newer versions, to transmit packets on a network at the link layer, and to get a list of network interfaces for possible use with libpcap, WinPcap, or Npcap. The pcap API is written in C, so other languages such as Java, .NET languages, and scripting languages generally use a wrapper; no such wrappers are provided by libpcap or WinPcap itself. C++ programs may link directly to the C API or use a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Regular Expression
A regular expression (shortened as regex or regexp; sometimes referred to as rational expression) is a sequence of characters that specifies a search pattern in text. Usually such patterns are used by string-searching algorithms for "find" or "find and replace" operations on strings, or for input validation. Regular expression techniques are developed in theoretical computer science and formal language theory. The concept of regular expressions began in the 1950s, when the American mathematician Stephen Cole Kleene formalized the concept of a regular language. They came into common use with Unix text-processing utilities. Different syntaxes for writing regular expressions have existed since the 1980s, one being the POSIX standard and another, widely used, being the Perl syntax. Regular expressions are used in search engines, in search and replace dialogs of word processors and text editors, in text processing utilities such as sed and AWK, and in lexical ana ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Promiscuous Mode
In computer networking, promiscuous mode is a mode for a wired network interface controller (NIC) or wireless network interface controller (WNIC) that causes the controller to pass all traffic it receives to the central processing unit (CPU) rather than passing only the frames that the controller is specifically programmed to receive. This mode is normally used for packet sniffing that takes place on a router or on a computer connected to a wired network or one being part of a wireless LAN. Interfaces are placed into promiscuous mode by software bridges often used with hardware virtualization. In IEEE 802 networks such as Ethernet or IEEE 802.11, each frame includes a destination MAC address. In non-promiscuous mode, when a NIC receives a frame, it drops it unless the frame is addressed to that NIC's MAC address or is a broadcast or multicast addressed frame. In promiscuous mode, however, the NIC allows all frames through, thus allowing the computer to read frames inten ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Berkeley Packet Filter
The Berkeley Packet Filter (BPF) is a technology used in certain computer operating systems for programs that need to, among other things, analyze network traffic. It provides a raw interface to data link layers, permitting raw link-layer packets to be sent and received. In addition, if the driver for the network interface supports promiscuous mode, it allows the interface to be put into that mode so that all packets on the network can be received, even those destined to other hosts. BPF supports filtering packets, allowing a userspace process to supply a filter program that specifies which packets it wants to receive. For example, a tcpdump process may want to receive only packets that initiate a TCP connection. BPF returns only packets that pass the filter that the process supplies. This avoids copying unwanted packets from the operating system kernel to the process, greatly improving performance. The filter program is in the form of instructions for a virtual machine, which a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
UNIX-like
A Unix-like (sometimes referred to as UN*X or *nix) operating system is one that behaves in a manner similar to a Unix system, although not necessarily conforming to or being certified to any version of the Single UNIX Specification. A Unix-like application is one that behaves like the corresponding Unix command or shell. Although there are general philosophies for Unix design, there is no technical standard defining the term, and opinions can differ about the degree to which a particular operating system or application is Unix-like. Some well-known examples of Unix-like operating systems include Linux and BSD. These systems are often used on servers, as well as on personal computers and other devices. Many popular applications, such as the Apache web server and the Bash shell, are also designed to be used on Unix-like systems. One of the key features of Unix-like systems is their ability to support multiple users and processes simultaneously. This allows users to run mult ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
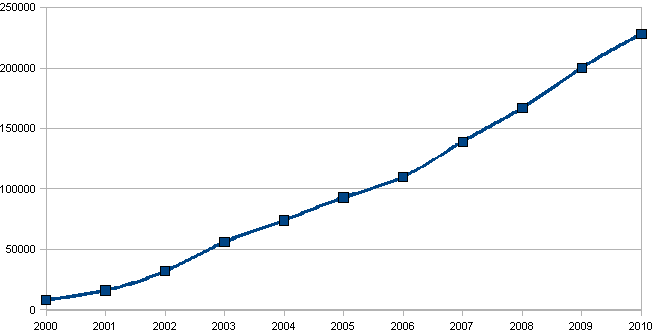
SourceForge
SourceForge is a web service that offers software consumers a centralized online location to control and manage open-source software projects and research business software. It provides source code repository hosting, bug tracking, mirroring of downloads for load balancing, a wiki for documentation, developer and user mailing lists, user-support forums, user-written reviews and ratings, a news bulletin, micro-blog for publishing project updates, and other features. SourceForge was one of the first to offer this service free of charge to open-source projects. Since 2012, the website has run on Apache Allura software. SourceForge offers free hosting and free access to tools for developers of free and open-source software. , the SourceForge repository claimed to host more than 502,000 projects and had more than 3.7 million registered users. Concept SourceForge is a web-based source code repository. It acts as a centralized location for free and open-source softwar ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |