|
Endpoint Security
Endpoint security or endpoint protection is an approach to the protection of computer networks that are remotely bridged to client devices. The connection of endpoint devices such as laptops, tablets, mobile phones, and other wireless devices to corporate networks creates attack paths for security threats. Endpoint security attempts to ensure that such devices follow compliance to standards. The endpoint security space has evolved since the 2010s away from limited antivirus software and into more advanced, comprehensive defenses. This includes next-generation antivirus, threat detection, investigation, and response, device management, data loss prevention (DLP), patch management, and other considerations to face evolving threats. Corporate network security Endpoint security management is a software approach that helps to identify and manage the users' computer and data access over a corporate network. This allows the network administrator to restrict the use of sensitive ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Network
A computer network is a collection of communicating computers and other devices, such as printers and smart phones. In order to communicate, the computers and devices must be connected by wired media like copper cables, optical fibers, or by wireless communication. The devices may be connected in a variety of network topologies. In order to communicate over the network, computers use agreed-on rules, called communication protocols, over whatever medium is used. The computer network can include personal computers, Server (computing), servers, networking hardware, or other specialized or general-purpose Host (network), hosts. They are identified by network addresses and may have hostnames. Hostnames serve as memorable labels for the nodes and are rarely changed after initial assignment. Network addresses serve for locating and identifying the nodes by communication protocols such as the Internet Protocol. Computer networks may be classified by many criteria, including the tr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Virtual LAN
A virtual local area network (VLAN) is any broadcast domain that is partitioned and isolated in a computer network at the data link layer ( OSI layer 2).IEEE 802.1Q-2011, ''1.4 VLAN aims and benefits'' In this context, virtual refers to a physical object recreated and altered by additional logic, within the local area network. Basically, a VLAN behaves like a virtual switch or network link that can share the same physical structure with other VLANs while staying logically separate from them. VLANs work by applying tags to network frames and handling these tags in networking systems, in effect creating the appearance and functionality of network traffic that, while on a single physical network, behaves as if it were split between separate networks. In this way, VLANs can keep network applications separate despite being connected to the same physical network, and without requiring multiple sets of cabling and networking devices to be deployed. VLANs allow network administrator ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Sandbox (computer Security)
In computer security, a sandbox is a security mechanism for separating running programs, usually in an effort to mitigate system failures and/or software vulnerabilities from spreading. The sandbox metaphor derives from the concept of a child's sandbox—a play area where children can build, destroy, and experiment without causing any real-world damage. It is often used to kill untested or untrusted programs or code, possibly from unverified or untrusted third parties, suppliers, users or websites, without risking harm to the host machine or operating system. A sandbox typically provides a tightly controlled set of resources for guest programs to run in, such as storage and memory scratch space. Network access, the ability to inspect the host system, or read from input devices are usually disallowed or heavily restricted. In the sense of providing a highly controlled environment, sandboxes may be seen as a specific example of virtualization. Sandboxing is frequently used to t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Of Things
Internet of things (IoT) describes devices with sensors, processing ability, software and other technologies that connect and exchange data with other devices and systems over the Internet or other communication networks. The IoT encompasses Electronic engineering, electronics, Telecommunications engineering, communication, and computer science engineering. "Internet of things" has been considered a misnomer because devices do not need to be connected to the public internet; they only need to be connected to a network and be individually addressable. The field has evolved due to the convergence of multiple technologies, including ubiquitous computing, commodity sensors, and increasingly powerful embedded systems, as well as machine learning.Hu, J.; Niu, H.; Carrasco, J.; Lennox, B.; Arvin, F.,Fault-tolerant cooperative navigation of networked UAV swarms for forest fire monitoring Aerospace Science and Technology, 2022. . Older fields of embedded systems, wireless sensor netw ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Remote Desktop Protocol
Remote Desktop Protocol (RDP) is a proprietary protocol developed by Microsoft Corporation which provides a user with a graphical interface to connect to another computer over a network connection. The user employs RDP client software for this purpose, while the other computer must run RDP server software. Several clients exist for most versions of Microsoft Windows (including Windows Mobile but the support has ended), Linux (for example Remmina), Unix, macOS, iOS, Android, and other operating systems. RDP servers are built into the server and professional editions of Windows operating systems but not home editions; an RDP server for Unix and OS X also exists (for example xrdp). By default, the server listens on TCP port 3389 Microsoft KB article 306759, revision 2.2. and UDP port 3389. Microsoft currently refers to their official RDP client software as Remote Desktop Connection, formerly "Terminal Services Client". The protocol is an extension of the ITU-T T.128 applic ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Vulnerability (computer Security)
Vulnerabilities are flaws or weaknesses in a system's design, implementation, or management that can be exploited by a malicious actor to compromise its security. Despite a system administrator's best efforts to achieve complete correctness, virtually all hardware and software contain Software bug, bugs where the system does not behave as expected. If the bug could enable an attacker to compromise the confidentiality, Data integrity, integrity, or availability of system resources, it can be considered a vulnerability. Insecure software development practices as well as design factors such as complexity can increase the burden of vulnerabilities. Vulnerability management is a process that includes identifying systems and prioritizing which are most important, scanning for vulnerabilities, and taking action to secure the system. Vulnerability management typically is a combination of remediation, mitigation, and acceptance. Vulnerabilities can be scored for severity according to the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Peer-to-peer
Peer-to-peer (P2P) computing or networking is a distributed application architecture that partitions tasks or workloads between peers. Peers are equally privileged, equipotent participants in the network, forming a peer-to-peer network of Node (networking), nodes. In addition, a personal area network (PAN) is also in nature a type of Decentralized computing, decentralized peer-to-peer network typically between two devices. Peers make a portion of their resources, such as processing power, disk storage, or network bandwidth, directly available to other network participants, without the need for central coordination by servers or stable hosts. Peers are both suppliers and consumers of resources, in contrast to the traditional client–server model in which the consumption and supply of resources are divided. While P2P systems had previously been used in many application domains, the architecture was popularized by the Internet file sharing system Napster, originally released in ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malvertising
Malvertising (a portmanteau of "malicious software (malware) advertising") is the use of online advertising to spread malware. It typically involves injecting malicious or malware-laden advertisements into legitimate online advertising networks and webpages. Because advertising content can be inserted into high-profile and reputable websites, malvertising provides malefactors an opportunity to push their attacks to web users who might not otherwise see the ads, due to firewalls, more safety precautions, or the like. Malvertising is "attractive to attackers because they 'can be easily spread across a large number of legitimate websites without directly compromising those websites'." Malvertising can be extremely hard to combat because it can quietly work its way into a webpage or webpage advertisement and spread unknowingly: "The interesting thing about infections delivered through malvertising is that it does not require any user action (like clicking) to compromise the system ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Phishing
Phishing is a form of social engineering and a scam where attackers deceive people into revealing sensitive information or installing malware such as viruses, worms, adware, or ransomware. Phishing attacks have become increasingly sophisticated and often transparently mirror the site being targeted, allowing the attacker to observe everything while the victim navigates the site, and transverses any additional security boundaries with the victim. As of 2020, it is the most common type of cybercrime, with the Federal Bureau of Investigation's Internet Crime Complaint Center reporting more incidents of phishing than any other type of cybercrime. The term "phishing" was first recorded in 1995 in the cracking toolkit AOHell, but may have been used earlier in the hacker magazine '' 2600''. It is a variation of ''fishing'' and refers to the use of lures to "fish" for sensitive information. Measures to prevent or reduce the impact of phishing attacks include legislation, user educa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Corporate Security
A chief security officer (CSO) is an organization's most senior executive accountable for the development and oversight of policies and programs intended for the mitigation and/or reduction of compliance, operational, strategic, financial and reputational security risk strategies relating to the protection of people, intellectual assets and tangible property. The accountabilities of the CSO include, but are not necessarily limited to: * In cooperation with the organization’s executive leadership team(s), directs the development of an effective strategy to assess and mitigate risk (foreign and domestic), manage crises and incidents, maintain continuity of operations, and safeguard the organization. * Directs staff in identifying, developing, implementing, and maintaining security processes, practices, and policies throughout the organization to reduce risks, respond to incidents, and limit exposure and liability in all areas of information, financial, physical, personal, an ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Payment Card
Payment cards are part of a payment system issued by financial institutions, such as a bank, to a customer that enables its owner (the cardholder) to access the funds in the customer's designated bank accounts, or through a credit account and make payments by electronic transfer with a payment terminal and access automated teller machines (ATMs). Such cards are known by a variety of names, including bank cards, ATM cards, client cards, key cards or cash cards. There are a number of types of payment cards, the most common being credit cards, debit cards, charge cards, and prepaid cards. Most commonly, a payment card is electronically linked to an account or accounts belonging to the cardholder. These accounts may be deposit accounts or loan or credit accounts, and the card is a means of authenticating the cardholder. However, stored-value cards store money on the card itself and are not necessarily linked to an account at a financial institution. The largest global card pa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Software As A Service
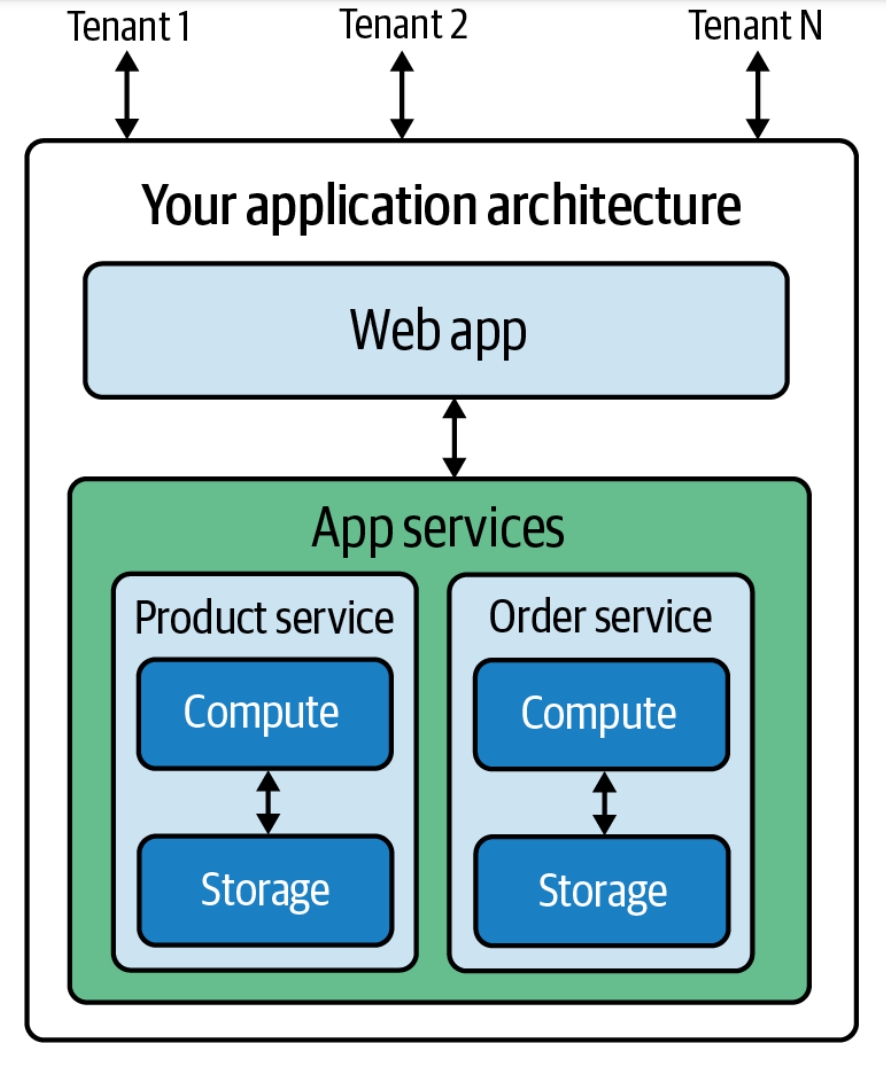
Software as a service (SaaS ) is a cloud computing service model where the provider offers use of application software to a client and manages all needed physical and software resources. SaaS is usually accessed via a web application. Unlike other software delivery models, it separates "the possession and ownership of software from its use". SaaS use began around 2000, and by 2023 was the main form of software application deployment. Unlike most self-hosted software products, only one version of the software exists and only one operating system and configuration is supported. SaaS products typically run on rented infrastructure as a service (IaaS) or platform as a service (PaaS) systems including hardware and sometimes operating systems and middleware, to accommodate rapid increases in usage while providing instant and continuous availability to customers. SaaS customers have the abstraction of limitless computing resources, while economy of scale drives down the cost. Sa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |