Y2K bug on:
[Wikipedia]
[Google]
[Amazon]
 The year 2000 problem, also known as the Y2K problem, Y2K scare, millennium bug, Y2K bug, Y2K glitch, Y2K error, or simply Y2K refers to potential computer errors related to the formatting and storage of calendar data for dates in and after the year 2000. Many
The year 2000 problem, also known as the Y2K problem, Y2K scare, millennium bug, Y2K bug, Y2K glitch, Y2K error, or simply Y2K refers to potential computer errors related to the formatting and storage of calendar data for dates in and after the year 2000. Many
 Storage of a combined date and time within a fixed binary field is often considered a solution, but the possibility for software to misinterpret dates remains because such date and time representations must be relative to some known origin. Rollover of such systems is still a problem but can happen at varying dates and can fail in various ways. For example:
* An upscale grocer's 1997 credit-card caused crash of their 10 cash registers, repeatedly, due to year 2000 expiration dates, and was the source of the first Y2K-related lawsuit.
* The
Storage of a combined date and time within a fixed binary field is often considered a solution, but the possibility for software to misinterpret dates remains because such date and time representations must be relative to some known origin. Rollover of such systems is still a problem but can happen at varying dates and can fail in various ways. For example:
* An upscale grocer's 1997 credit-card caused crash of their 10 cash registers, repeatedly, due to year 2000 expiration dates, and was the source of the first Y2K-related lawsuit.
* The
 A feature of US government outreach was Y2K websites including Y2K.GOV, many of which have become inaccessible in the years since 2000. Some of these websites have been archived by the
A feature of US government outreach was Y2K websites including Y2K.GOV, many of which have become inaccessible in the years since 2000. Some of these websites have been archived by the 
 * The United States established the ''Year 2000 Information and Readiness Disclosure Act'', which limited the liability of businesses who had properly disclosed their Y2K readiness.
* Insurance companies sold insurance policies covering failure of businesses due to Y2K problems.
* Attorneys organized and mobilized for Y2K class action lawsuits (which were not pursued).
* Survivalist-related businesses (gun dealers, surplus and sporting goods) anticipated increased business in the final months of 1999 in an event known as the Y2K scare.
* The Long Now Foundation, which (in their words) "seeks to promote 'slower/better' thinking and to foster creativity in the framework of the next 10,000 years", has a policy of anticipating the
* The United States established the ''Year 2000 Information and Readiness Disclosure Act'', which limited the liability of businesses who had properly disclosed their Y2K readiness.
* Insurance companies sold insurance policies covering failure of businesses due to Y2K problems.
* Attorneys organized and mobilized for Y2K class action lawsuits (which were not pursued).
* Survivalist-related businesses (gun dealers, surplus and sporting goods) anticipated increased business in the final months of 1999 in an event known as the Y2K scare.
* The Long Now Foundation, which (in their words) "seeks to promote 'slower/better' thinking and to foster creativity in the framework of the next 10,000 years", has a policy of anticipating the
(accessed 12 January 2015) It has been suggested that on
Center for Y2K and Society Records
Charles Babbage Institute, University of Minnesota. Documents activities of Center for Y2K and Society (based in Washington, D.C.) working with non-profit institutions and foundations to respond to possible societal impacts of the Y2K computer problem: helping the poor and vulnerable as well as protecting human health and the environment. Records donated by executive director, Norman L. Dean.
International Y2K Cooperation Center Records, 1998ŌĆō2000
Charles Babbage Institute, University of Minnesota. Collection contains the materials of the International Y2K Cooperation Center. Includes country reports, news clippings, country questionnaires, country telephone directories, background materials, audio visual materials and papers of Bruce W. McConnell, director of IY2KCC.
Preparing for an Apocalypse: Y2K
Charles Babbage Institute, University of Minnesota. A web exhibit curated by Stephanie H. Crowe
BBC: Y2K coverage
''In The Beginning there Was the Nerd''
ŌĆō BBC Radio documentary about the history of computers and the millennium bug 10 years after using archival recordings.
ŌĆō Radio documentary by American Public Media, on the history and legacy of the millennium bug five years on.
CBC Digital Archives ŌĆō The Eve of the Millennium
How the UK coped with the millennium bug
Ćö CNN {{DEFAULTSORT:Year 2000 problem Problem 2000 in Internet culture Calendars COBOL Doomsday scenarios Technology hazards Software bugs Year 02000 problem Turn of the third millennium
 The year 2000 problem, also known as the Y2K problem, Y2K scare, millennium bug, Y2K bug, Y2K glitch, Y2K error, or simply Y2K refers to potential computer errors related to the formatting and storage of calendar data for dates in and after the year 2000. Many
The year 2000 problem, also known as the Y2K problem, Y2K scare, millennium bug, Y2K bug, Y2K glitch, Y2K error, or simply Y2K refers to potential computer errors related to the formatting and storage of calendar data for dates in and after the year 2000. Many programs
Program, programme, programmer, or programming may refer to:
Business and management
* Program management, the process of managing several related projects
* Time management
* Program, a part of planning
Arts and entertainment Audio
* Progra ...
represented four-digit years with only the final two digits, making the year 2000 indistinguishable from 1900. Computer systems' inability to distinguish dates correctly had the potential to bring down worldwide infrastructures for industries ranging from banking to air travel.
In the years leading up to the turn of the century (millennium), the public gradually became aware of the "Y2K scare", and individual companies predicted the global damage caused by the bug would require anything between $400 million and $600 billion to rectify. A lack of clarity regarding the potential dangers of the bug led some to stock up on food, water, and firearms, purchase backup generators, and withdraw large sums of money in anticipation of a computer-induced apocalypse
Apocalypse () is a literary genre in which a supernatural being reveals cosmic mysteries or the future to a human intermediary. The means of mediation include dreams, visions and heavenly journeys, and they typically feature symbolic imager ...
.
Contrary to published expectations, few major errors occurred in 2000. Supporters of the Y2K remediation effort argued that this was primarily due to the pre-emptive action of many computer programmers and information technology
Information technology (IT) is the use of computers to create, process, store, retrieve, and exchange all kinds of data . and information. IT forms part of information and communications technology (ICT). An information technology syste ...
experts. Companies and organizations in some countries, but not all, had checked, fixed, and upgraded their computer systems to address the problem. Then- U.S. president Bill Clinton
William Jefferson Clinton (n├® Blythe III; born August 19, 1946) is an American politician who served as the 42nd president of the United States from 1993 to 2001. He previously served as governor of Arkansas from 1979 to 1981 and again ...
, who organized efforts to minimize the damage in the United States, labeled Y2K as "the first challenge of the 21st century successfully met", and retrospectives on the event typically commend the programmers who worked to avert the anticipated disaster.
Critics pointed out that even in countries where very little had been done to fix software, problems were minimal. The same was true in sectors such as schools and small businesses where compliance with Y2K policies was patchy at best.
Background
Y2K is anumeronym
A numeronym is a number-based word. Most commonly, a numeronym is a word where a number is used to form an abbreviation (albeit not an acronym or an initialism). Pronouncing the letters and numbers may sound similar to the full word, as in " K9" ( ...
and was the common abbreviation for the year 2000 software problem. The abbreviation combines the letter ''Y'' for "year", the number 2 and a capitalized version of ''k'' for the SI unit prefix kilo meaning 1000; hence, ''2K'' signifies 2000. It was also named the "millennium bug" because it was associated with the popular (rather than literal) rollover of the millennium
A millennium (plural millennia or millenniums) is a period of one thousand years, sometimes called a kiloannus, kiloannum (ka), or kiloyear (ky). Normally, the word is used specifically for periods of a thousand years that begin at the starting ...
, even though most of the problems could have occurred at the end of ''any'' century.
''Computerworld
''Computerworld'' (abbreviated as CW) is an ongoing decades old professional publication which in 2014 "went digital." Its audience is information technology (IT) and business technology professionals, and is available via a publication website ...
''s 1993 three-page "Doomsday 2000" article by Peter de Jager was called "the information-age equivalent of the midnight ride of Paul Revere" by ''The New York Times''.
The problem was the subject of the early book ''Computers in Crisis'' by Jerome and Marilyn Murray (Petrocelli, 1984; reissued by McGraw-Hill
McGraw Hill is an American educational publishing company and one of the "big three" educational publishers that publishes educational content, software, and services for pre-K through postgraduate education. The company also publishes refere ...
under the title ''The Year 2000 Computing Crisis'' in 1996). Its first recorded mention on a Usenet
Usenet () is a worldwide distributed discussion system available on computers. It was developed from the general-purpose Unix-to-Unix Copy (UUCP) dial-up network architecture. Tom Truscott and Jim Ellis conceived the idea in 1979, and it wa ...
newsgroup is from 18 January 1985 by Spencer Bolles.
The acronym Y2K has been attributed to Massachusetts programmer David Eddy in an e-mail sent on 12 June 1995. He later said, "People were calling it CDC (Century Date Change), FADL (Faulty Date Logic). There were other contenders. Y2K just came off my fingertips."
The problem started because on both mainframe computers and later personal computers, storage was expensive, from as low as $10 per kilobyte, to in many cases as much as or even more than US$100 per kilobyte. It was therefore very important for programmers to minimize usage. Since computers only gained wide usage in the 20th century, programs could simply prefix "19" to the year of a date, allowing them to only store the last two digits of the year instead of four. As space on disc and tape was also expensive, these strategies saved money by reducing the size of stored data files and databases in exchange for becoming unusable past the year 2000.
This meant that programs facing two-digit years could not distinguish between dates in 1900 and 2000. Dire warnings at times were in the mode of:
The Y2K problem is the electronic equivalent of the El Ni├▒o and there will be nasty surprises around the globe. :ŌĆö John Hamre, United States Deputy Secretary of DefenseOptions on the De Jager Year 2000 Index, "the first index enabling investors to manage risk associated with the ... computer problem linked to the year 2000" began trading mid-March 1997. Special committees were set up by governments to monitor remedial work and contingency planning, particularly by crucial infrastructures such as telecommunications, utilities and the like, to ensure that the most critical services had fixed their own problems and were prepared for problems with others. While some commentators and experts argued that the coverage of the problem largely amounted to scaremongering, it was only the safe passing of the main event itself, 1 January 2000, that fully quelled public fears. Some experts who argued that scaremongering was occurring, such as Ross Anderson, professor of
security engineering
Security engineering is the process of incorporating security controls into an information system so that the controls become an integral part of the systemŌĆÖs operational capabilities. It is similar to other systems engineering activities in th ...
at the University of Cambridge Computer Laboratory, have since claimed that despite sending out hundreds of press releases about research results suggesting that the problem was not likely to be as big as some had suggested, they were largely ignored by the media. In a similar vein, the Microsoft Press book ''Running Office 2000 Professional'', published in May 1999, accurately predicted that most personal computer hardware and software would be unaffected by the year 2000 problem. Authors Michael Halvorson and Michael Young characterized most of the worries as popular hysteria, an opinion echoed by Microsoft Corp.
Programming problem
The practice of using two-digit dates for convenience predates computers, but was never a problem until stored dates were used in calculations.Bit conservation need
Business data processing was done using unit record equipment and punched cards, most commonly the 80-column variety employed by IBM, which dominated the industry. Many tricks were used to squeeze needed data into fixed-field 80-character records. Saving two digits for every date field was significant in this effort. In the 1960s, computer memory and mass storage were scarce and expensive. Early core memory cost one dollar per bit. Popular commercial computers, such as the IBM 1401, shipped with as little as 2 kilobytes of memory. Programs often mimicked card processing techniques. Commercial programming languages of the time, such asCOBOL
COBOL (; an acronym for "common business-oriented language") is a compiled English-like computer programming language designed for business use. It is an imperative, procedural and, since 2002, object-oriented language. COBOL is primarily u ...
and RPG, processed numbers in their character representations. Over time, the punched cards were converted to magnetic tape
Magnetic tape is a medium for magnetic storage made of a thin, magnetizable coating on a long, narrow strip of plastic film. It was developed in Germany in 1928, based on the earlier magnetic wire recording from Denmark. Devices that use magnet ...
and then disc files, but the structure of the data usually changed very little.
Data was still input using punched cards until the mid-1970s. Machine architectures, programming languages and application designs were evolving rapidly. Neither managers nor programmers of that time expected their programs to remain in use for many decades, and the possibility that these programs would both remain in use and cause problems when interacting with databases - a new type of program with different characteristics - went largely uncommented upon.
Early attention
The first person known to publicly address this issue was Bob Bemer, who had noticed it in 1958 as a result of work on genealogical software. He spent the next twenty years trying to make programmers, IBM, the government of the United States and theInternational Organization for Standardization
The International Organization for Standardization (ISO ) is an international standard development organization composed of representatives from the national standards organizations of member countries. Membership requirements are given in A ...
aware of the problem, with little result. This included the recommendation that the COBOL picture clause
COBOL (; an acronym for "common business-oriented language") is a compiled English-like computer programming language designed for business use. It is an imperative, procedural and, since 2002, object-oriented language. COBOL is primarily us ...
should be used to specify four digit years for dates.
In the 1980s, the brokerage industry began to address this issue, mostly because of bonds with maturity dates beyond the year 2000. By 1987 the New York Stock Exchange
The New York Stock Exchange (NYSE, nicknamed "The Big Board") is an American stock exchange in the Financial District of Lower Manhattan in New York City. It is by far the world's largest stock exchange by market capitalization of its liste ...
had reportedly spent over $20 million, including "a team of 100" programmers on Y2K.
Despite magazine articles on the subject from 1970 onward, the majority of programmers and managers only started recognizing Y2K as a looming problem in the mid-1990s, but even then, inertia and complacency caused it to be mostly unresolved until the last few years of the decade. In 1989, Erik Naggum was instrumental in ensuring that internet mail used four digit representations of years by including a strong recommendation to this effect in the internet host requirements document . On April Fools' Day 1998, some companies set their mainframe computer dates to 2001, so that "the wrong date will be perceived as good fun instead of bad computing" while having a full day of testing.
While using 3-digit years and 3-digit dates within that year was used by some, others chose to use the number of days since a fixed date, such as 1 January 1900. Inaction was not an option, and risked major failure. Embedded systems with similar date logic were expected to malfunction and cause utilities and other crucial infrastructure to fail.
Saving space on stored dates persisted into the Unix era, with most systems representing dates to a single 32-bit word, typically representing dates as elapsed seconds from some fixed date, which causes the similar Y2K38 problem.
Resulting bugs from date programming
 Storage of a combined date and time within a fixed binary field is often considered a solution, but the possibility for software to misinterpret dates remains because such date and time representations must be relative to some known origin. Rollover of such systems is still a problem but can happen at varying dates and can fail in various ways. For example:
* An upscale grocer's 1997 credit-card caused crash of their 10 cash registers, repeatedly, due to year 2000 expiration dates, and was the source of the first Y2K-related lawsuit.
* The
Storage of a combined date and time within a fixed binary field is often considered a solution, but the possibility for software to misinterpret dates remains because such date and time representations must be relative to some known origin. Rollover of such systems is still a problem but can happen at varying dates and can fail in various ways. For example:
* An upscale grocer's 1997 credit-card caused crash of their 10 cash registers, repeatedly, due to year 2000 expiration dates, and was the source of the first Y2K-related lawsuit.
* The Microsoft Excel
Microsoft Excel is a spreadsheet developed by Microsoft for Microsoft Windows, Windows, macOS, Android (operating system), Android and iOS. It features calculation or computation capabilities, graphing tools, pivot tables, and a macro (comp ...
spreadsheet program had a very elementary Y2K problem: Excel (in both Windows and Mac versions, when they are set to start at 1900) incorrectly set the year 1900 as a leap year for compatibility with Lotus 1-2-3. In addition, the years 2100, 2200, and so on, were regarded as leap years. This bug was fixed in later versions, but since the epoch
In chronology and periodization, an epoch or reference epoch is an instant in time chosen as the origin of a particular calendar era. The "epoch" serves as a reference point from which time is measured.
The moment of epoch is usually decided ...
of the Excel timestamp was set to the meaningless date of 0 January
Several non-standard dates are used in calendars. Some are used sarcastically, some for scientific or mathematical purposes, and some for exceptional or fictional calendars.
January 0
January 0 or 0 January is an alternative name for December 31 ...
1900 in previous versions, the year 1900 is still regarded as a leap year to maintain backward compatibility.
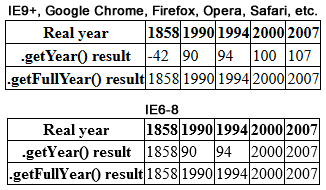
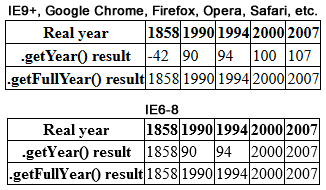
* In the C programming language
''The C Programming Language'' (sometimes termed ''K&R'', after its authors' initials) is a computer programming book written by Brian Kernighan and Dennis Ritchie, the latter of whom originally designed and implemented the language, as well a ...
, the standard library function to extract the year from a timestamp returns the year minus 1900. Many programs using functions from C, such as Perl
Perl is a family of two high-level, general-purpose, interpreted, dynamic programming languages. "Perl" refers to Perl 5, but from 2000 to 2019 it also referred to its redesigned "sister language", Perl 6, before the latter's name was offic ...
and Java
Java (; id, Jawa, ; jv, Ļ”ŚĻ”«; su, ) is one of the Greater Sunda Islands in Indonesia. It is bordered by the Indian Ocean to the south and the Java Sea to the north. With a population of 151.6 million people, Java is the world's mo ...
, two programming languages widely used in web development, incorrectly treated this value as the last two digits of the year. On the web this was usually a harmless presentation bug, but it did cause many dynamically generated web pages to display 1 January 2000 as "1/1/19100", "1/1/100", or other variants, depending on the display format.
* JavaScript
JavaScript (), often abbreviated as JS, is a programming language that is one of the core technologies of the World Wide Web, alongside HTML and CSS. As of 2022, 98% of websites use JavaScript on the client side for webpage behavior, of ...
was changed due to concerns over the Y2K bug, and the return value for years changed and thus differed between versions from sometimes being a four digit representation and sometimes a two-digit representation forcing programmers to rewrite already working code to make sure web pages worked for all versions.
* Older applications written for the commonly used UNIX Source Code Control System failed to handle years that began with the digit "2".
* In the Windows 3.x file manager, dates displayed as 1/1/19:0 for 1/1/2000 (because the colon is the character after "9" in the ASCII
ASCII ( ), abbreviated from American Standard Code for Information Interchange, is a character encoding standard for electronic communication. ASCII codes represent text in computers, telecommunications equipment, and other devices. Because ...
character set). An update was available.
* Some software, such as Math Blaster Episode I: In Search of Spot which only treats years as two-digit values instead of four, will give a given year as "1900", "1901", and so on, depending on the last two digits of the present year.
Similar date bugs
4 January 1975
The date of 4 January 1975 overflowed the 12-bit field that had been used in the Decsystem 10 operating systems. There were numerous problems and crashes related to this bug while an alternative format was developed.9 September 1999
Even before 1 January 2000 arrived, there were also some worries about 9 September 1999 (albeit less than those generated by Y2K). Because this date could also be written in the numeric format 9/9/99, it could have conflicted with the date value9999, frequently used to specify an unknown date. It was thus possible that database programs might act on the records containing unknown dates on that day. Data entry operators commonly entered 9999 into required fields for an unknown future date, (e.g., a termination date for cable television or telephone service), in order to process computer forms using CICS software. Somewhat similar to this is the end-of-file code 9999, used in older programming languages. While fears arose that some programs might unexpectedly terminate on that date, the bug was more likely to confuse computer operators than machines.
Leap years
Normally, a year is a leap year if it is evenly divisible by four. A year divisible by 100 is not a leap year in the Gregorian calendar unless it is also divisible by 400. For example, 1600 was a leap year, but 1700, 1800 and 1900 were not. Some programs may have relied on the oversimplified rule that "a year divisible by four is a leap year". This method works fine for the year 2000 (because it is a leap year), and will not become a problem until 2100, when older legacy programs will likely have long since been replaced. Other programs contained incorrect leap year logic, assuming for instance that no year divisible by 100 could be a leap year. An assessment of this ''leap year problem'' including a number of real-life code fragments appeared in 1998. For information on why century years are treated differently, seeGregorian calendar
The Gregorian calendar is the calendar used in most parts of the world. It was introduced in October 1582 by Pope Gregory XIII as a modification of, and replacement for, the Julian calendar. The principal change was to space leap years d ...
.
Year 2010 problem
Some systems had problems once the year rolled over to 2010. This was dubbed by some in the media as the "Y2K+10" or "Y2.01K" problem. The main source of problems was confusion between hexadecimal number encoding andbinary-coded decimal
In computing and electronic systems, binary-coded decimal (BCD) is a class of binary encodings of decimal numbers where each digit is represented by a fixed number of bits, usually four or eight. Sometimes, special bit patterns are used ...
encodings of numbers. Both hexadecimal and BCD encode the numbers 0ŌĆō9 as 0x0ŌĆō0x9. BCD encodes the number 10 as 0x10, while hexadecimal encodes the number 10 as 0x0A; 0x10 interpreted as a hexadecimal encoding represents the number 16.
For example, because the SMS protocol uses BCD for dates, some mobile phone software incorrectly reported dates of SMSes as 2016 instead of 2010. Windows Mobile
Windows Mobile is a discontinued family of mobile operating systems developed by Microsoft for smartphones and personal digital assistants.
Its origin dated back to Windows CE in 1996, though Windows Mobile itself first appeared in 2000 as Pock ...
is the first software reported to have been affected by this glitch; in some cases WM6 changes the date of any incoming SMS message sent after 1 January 2010 from the year 2010 to 2016.
Other systems affected include EFTPOS terminals, and the PlayStation 3
The PlayStation 3 (PS3) is a home video game console developed by Sony Interactive Entertainment, Sony Computer Entertainment. The successor to the PlayStation 2, it is part of the PlayStation brand of consoles. It was first released on Novemb ...
(except the Slim model).
The most important occurrences of such a glitch were in Germany, where up to 20 million bank cards became unusable, and with Citibank Belgium, whose digipass customer identification chips failed.
Year 2022 problem
Known as the Y2K22 bug. The maximum value of a signed 32-bit integer, as used in many computer systems, is 2147483647. Systems using an integer to represent a 10 character date-based field, where the leftmost two characters are the 2-digit year, ran into an issue on 1 January 2022 when the leftmost characters needed to be '22', i.e. values from 2200000001 needed to be represented. Microsoft's Exchange server was one of the most famous and significant systems affected by the Y22 bug. The problem caused emails to be stuck on transport queues on Exchange Server 2016 and Exchange Server 2019, reporting the following error: ŌĆ£The FIP-FS ŌĆ£MicrosoftŌĆØ Scan Engine failed to load. PID: 23092, Error Code: 0x80004005. Error Description: Can't convert ŌĆ£2201010001ŌĆØ to long.ŌĆØYear 2038 problem
Many systems use Unix time and store it in a signed 32-bit integer. This data type is only capable of representing integers between ŌłÆ(2) and (2)ŌłÆ1, treated as number of seconds since the epoch at 1 January 1970 at 00:00:00 UTC. These systems can only represent times between 13 December 1901 at 20:45:52 UTC and 19 January 2038 at 03:14:07 UTC. If these systems are not updated and fixed, then dates all across the world that rely on Unix time will wrongfully display the year as 1901 beginning at 03:14:08 UTC on 19 January 2038.Programming solutions
Several very different approaches were used to solve the year 2000 problem in legacy systems. Several of them follow: ; Date expansion : Two-digit years were expanded to include the century (becoming four-digit years) in programs, files, and databases. This was considered the "purest" solution, resulting in unambiguous dates that are permanent and easy to maintain. This method was costly, requiring massive testing and conversion efforts, and usually affecting entire systems. ; Date windowing : Two-digit years were retained, and programs determined the century value only when needed for particular functions, such as date comparisons and calculations. (The century "window" refers to the 100-year period to which a date belongs.) This technique, which required installing small patches of code into programs, was simpler to test and implement than date expansion, thus much less costly. While not a permanent solution, windowing fixes were usually designed to work for many decades. This was thought acceptable, as older legacy systems tend to eventually get replaced by newer technology. ; Date compression : Dates can be compressed into binary 14-bit numbers. This allows retention of data structure alignment, using aninteger
An integer is the number zero (), a positive natural number (, , , etc.) or a negative integer with a minus sign ( ŌłÆ1, ŌłÆ2, ŌłÆ3, etc.). The negative numbers are the additive inverses of the corresponding positive numbers. In the languag ...
value for years. Such a scheme is capable of representing 16384 different years; the exact scheme varies by the selection of epoch
In chronology and periodization, an epoch or reference epoch is an instant in time chosen as the origin of a particular calendar era. The "epoch" serves as a reference point from which time is measured.
The moment of epoch is usually decided ...
.
; Date re-partitioning
: In legacy databases whose size could not be economically changed, six-digit year/month/day codes were converted to three-digit years (with 1999 represented as 099 and 2001 represented as 101, etc.) and three-digit days (ordinal date
An ordinal date is a calendar date typically consisting of a ''year'' and a day of the year or ordinal day number (or simply ordinal day or day number), an ordinal number ranging between 1 and 366 (starting on January 1), though year may sometime ...
in year). Only input and output instructions for the date fields had to be modified, but most other date operations and whole record operations required no change. This delays the eventual roll-over problem to the end of the year 2899.
; Software kits
: Software kits, such as those listed in CNN.com's ''Top 10 Y2K fixes for your PC'': ("most ... free") which was topped by the $50 ''Millennium Bug Kit''.
; Bridge programs
: Date servers where Call statements are used to access, add or update date fields.
Documented errors
Before 2000
* On 1 January 1999, taxi meters in Singapore stopped working, while in Sweden, incorrect taxi fares were given. * On 28 December 1999, 10,000 card swipe machines issued byHSBC
HSBC Holdings plc is a British multinational universal bank and financial services holding company. It is the largest bank in Europe by total assets ahead of BNP Paribas, with US$2.953 trillion as of December 2021. In 2021, HSBC had $10.8 tr ...
and manufactured by Racal stopped processing credit and debit card transactions. The stores relied on paper transactions until the machines started working again on 1 January.
On 1 January 2000
When 1 January 2000 arrived, there were problems generally regarded as minor. Consequences did not always result exactly at midnight. Some programs were not active at that moment and problems would only show up when they were invoked. Not all problems recorded were directly linked to Y2K programming in acausality
Causality (also referred to as causation, or cause and effect) is influence by which one event, process, state, or object (''a'' ''cause'') contributes to the production of another event, process, state, or object (an ''effect'') where the cau ...
; minor technological glitches occur on a regular basis.
Reported problems include:
* In Australia, bus ticket validation machines in two states failed to operate.
* In Ishikawa, Japan, radiation monitoring equipment failed at midnight. Officials said there was no risk to the public.
* In Onagawa
is a town located in Miyagi Prefecture, Japan. , the town had an estimated population of 6,319, and a population density of 97 persons per km2 in 3,110 households. The total area of the town is .
Geography
Onagawa is located on the rugged ...
, Japan, an alarm sounded at a nuclear power plant at two minutes after midnight.
* In Japan, at two minutes past midnight, the telecommunications carrier Osaka Media Port found errors in the date management part of the company's network. The problem was fixed by 02:43 and no services were disrupted.
* In Japan, NTT Mobile Communications Network ( NTT Docomo), Japan's largest cellular operator, reported that some models of mobile telephones were deleting new messages received, rather than the older messages, as the memory filled up.
* In France, the national weather forecasting service, M├®t├®o-France
M├®t├®o-France is the French national meteorological service.
Organisation
The organisation was established by decree in June 1993 and is a department of the Ministry of Transportation. It is headquartered in Paris but many domestic operations ...
, said a Y2K bug made the date on a webpage show a map with Saturday's weather forecast as "01/01/19100".
* In Sheffield
Sheffield is a city in South Yorkshire, England, whose name derives from the River Sheaf which runs through it. The city serves as the administrative centre of the City of Sheffield. It is historically part of the West Riding of Yorkshire ...
, United Kingdom, a Y2K bug caused miscalculation of the mothers' age and sent incorrect risk assessments for Down syndrome
Down syndrome or Down's syndrome, also known as trisomy 21, is a genetic disorder caused by the presence of all or part of a third copy of chromosome 21. It is usually associated with physical growth delays, mild to moderate intellectual d ...
to 154 pregnant women. As a direct result two abortions were carried out, and four babies with Down syndrome were also born to mothers who had been told they were in the low-risk group.
* In the United States, the US Naval Observatory
United States Naval Observatory (USNO) is a scientific and military facility that produces geopositioning, navigation and timekeeping data for the United States Navy and the United States Department of Defense. Established in 1830 as the Depo ...
, which runs the master clock that keeps the country's official time, gave the date on its website as 1 Jan 19100.
*In the United States, as a direct result of the Y2K glitch, at midnight computers at a ground control station ceased processing information from an unspecified number of spy satellites. The military implemented a contingency plan by 03:00 am, and restored all normal functionality in approximately two days.
* In the United States, 150 Delaware Lottery racino
A racino is a combined race track and casino. In some cases, the gambling is limited to slot machines, but many locations are beginning to include table games such as blackjack, poker, and roulette.
In 2003, Joe Bob Briggs described the eco ...
slot machines stopped working.
After January 2000
On 29 February and 1 March 2000
Problems were reported on February 29 2000, Y2K's first Leap Year Day, and 1 March 2000. These were mostly minor. * In Japan, around five percent of post office cash dispensers failed to work and data from weather bureau computers was corrupted, causing them to release inaccurate readings. * In Bulgaria, police documents were issued with expiration dates of 29 February 2005 and 29 February 2010 (which are not leap years) and the system defaulted to 1900. * In the United States, the Coast Guard's message processing system was affected. * At Reagan National Airport, check-in lines lengthened after baggage handling programs were affected. * AtOffutt Air Force Base
Offutt Air Force Base is a U.S. Air Force base south of Omaha, adjacent to Bellevue in Sarpy County, Nebraska. It is the headquarters of the U.S. Strategic Command (USSTRATCOM), the 557th Weather Wing, and the 55th Wing (55 WG) of the Ai ...
south of Omaha, Nebraska
Omaha ( ) is the largest city in the U.S. state of Nebraska and the county seat of Douglas County. Omaha is in the Midwestern United States on the Missouri River, about north of the mouth of the Platte River. The nation's 39th-largest ...
, on February 29th records of aircraft maintenance parts could not be accessed.
On 31 December 2000 or 1 January 2001
Some software did not correctly recognize 2000 as a leap year, and so worked on the basis of the year having 365 days. On the last day of 2000 (day 366) these systems exhibited various errors. These were generally minor. *In Norway, some trains were delayed until their clocks were put back by a month. *The Swedish bankNordbanken
Nordea Bank Abp, commonly referred to as Nordea, is a European financial services group operating in northern Europe and based in Helsinki, Finland. The name is a blend of the words "Nordic" and "idea". The bank is the result of the successive ...
reported that its online and physical banking systems went down 5 times between December 27, 2000, and January 3rd, 2001, which was believed to be due to the Y2K glitch.
*A "Y2K-like bug" affected a New York City government wireless system that was down for 10 days because of a GPS system's date-rollover problem. Infrastructure affected included "traffic lights, license-plate readers used by cops and other key functions."
*A large number of cash registers at the convenience store chain 7-Eleven
7-Eleven, Inc., stylized as 7-ELEVE, is a multinational chain of retail convenience stores, headquartered in Dallas, Texas. The chain was founded in 1927 as an ice house storefront in Dallas. It was named Tote'm Stores between 1928 and 1946. A ...
stopped working for card transactions on January 1st, 2001, despite not having had any prior glitches. 7-Eleven reported the registers had been restored to complete functionality within two days.
*In Multnomah County, Oregon, in early January approximately 3,000 residents received jury duty summonses for dates in 1901. Due to using two-digit years when entering the summons dates, courthouse employees had not seen that the computer had inaccurately rolled over the year.
Since 2000
Since 2000, various issues have occurred due to errors involving overflows. An issue with time tagging caused the destruction of the NASA ''Deep Impact'' spacecraft. Some software used a process called date windowing to fix the issue by interpreting years 00-19 as 2000ŌĆō2019 and 20ŌĆō99 as 1920ŌĆō1999. As a result, a new wave of problems started appearing in 2020, including parking meters in New York City refusing to accept credit cards, issues with Novituspoint of sale
The point of sale (POS) or point of purchase (POP) is the time and place at which a retail transaction is completed. At the point of sale, the merchant calculates the amount owed by the customer, indicates that amount, may prepare an invoice f ...
units, and some utility companies printing bills listing the year 1920.
Government responses
Bulgaria
Although only two digits are allocated for the birth year in the Bulgarian national identification number, the year 1900 problem and subsequently the Y2K problem were addressed by the use of unused values above 12 in the month range. For all persons born before 1900, the month is stored as the calendar month plus 20, and for all persons born in or after 2000, the month is stored as the calendar month plus 40.Canada
Canadian Prime MinisterJean Chr├®tien
Joseph Jacques Jean Chr├®tien (; born January 11, 1934) is a Canadian lawyer and politician who served as the 20th prime minister of Canada from 1993 to 2003.
Born and raised in Shawinigan, Shawinigan Falls, Quebec, Chr├®tien is a law gradua ...
's most important cabinet ministers were ordered to remain in the capital Ottawa
Ottawa (, ; Canadian French: ) is the capital city of Canada. It is located at the confluence of the Ottawa River and the Rideau River in the southern portion of the province of Ontario. Ottawa borders Gatineau, Quebec, and forms the c ...
, and gathered at 24 Sussex Drive
24 Sussex Drive, originally called ''Gorffwysfa'' and usually referred to simply as 24 Sussex, is the official residence of the prime minister of Canada, located in the New Edinburgh neighbourhood of Ottawa, Ontario. Built between 1866 and 1868 by ...
, the prime minister's residence, to watch the clock. 13,000 Canadian troops were also put on standby.
Netherlands
The Dutch Government promoted Y2K Information Sharing and Analysis Centers (ISACs) to share readiness between industries, without threat of antitrust violations or liability based on information shared.Norway and Finland
Norway and Finland changed their national identification number, to indicate the century in which a person was born. In both countries, the birth year was historically indicated by two digits only. This numbering system had already given rise to a similar problem, the " Year 1900 problem", which arose due to problems distinguishing between people born in the 20th and 19th centuries. Y2K fears drew attention to an older issue, while prompting a solution to a new problem. In Finland, the problem was solved by replacing the hyphen ("-") in the number with the letter "A" for people born in the 21st century (for people born before 1900, the sign was already "+"). In Norway, the range of the individual numbers following the birth date was altered from 0ŌĆō499 to 500ŌĆō999.Romania
Romania also changed its national identification number in response to the Y2K problem, due to the birth year being represented by only two digits. Before 2000, the first digit, which shows the person's gender, was 1 for males and 2 for females. Starting from 1 January 2000, the Romanian national identification number starts with 5 for males and 6 for females.Uganda
The Ugandan government responded to the Y2K threat by setting up a Y2K Task Force. In August 1999 an independent international assessment by the World Bank International Y2k Cooperation Centre found that Uganda's website was in the top category as "highly informative". This put Uganda in the "top 20" out of 107 national governments, and on a par with the United States, United Kingdom, Canada, Australia and Japan, and ahead of Germany, Italy, Austria, Switzerland which were rated as only "somewhat informative". The report said that "Countries which disclose more Y2K information will be more likely to maintain public confidence in their own countries and in the international markets."United States
In 1998, the United States government responded to the Y2K threat by passing the Year 2000 Information and Readiness Disclosure Act, by working with private sector counterparts in order to ensure readiness, and by creating internal continuity of operations plans in the event of problems and set limits to certain potential liabilities of companies with respect to disclosures about their year 2000 program. The effort was coordinated by the President's Council on Year 2000 Conversion, headed byJohn Koskinen
John Andrew Koskinen (born June 30, 1939) is an American businessman and public official. He served as the non-executive chairman of Freddie Mac from September 2008 to December 2011, retiring from the board in February 2012. On December 20, 2013, K ...
, in coordination with the then-independent Federal Emergency Management Agency
The Federal Emergency Management Agency (FEMA) is an agency of the United States Department of Homeland Security (DHS), initially created under President Jimmy Carter by Presidential Reorganization Plan No. 3 of 1978 and implemented by two Ex ...
(FEMA), and an interim Critical Infrastructure Protection Group, then in the Department of Justice, now in Homeland Security
Homeland security is an American national security term for "the national effort to ensure a homeland that is safe, secure, and resilient against terrorism and other hazards where American interests, aspirations, and ways of life can thrive" t ...
.
The US government followed a three-part approach to the problem: (1) outreach and advocacy, (2) monitoring and assessment, and (3) contingency planning and regulation.
 A feature of US government outreach was Y2K websites including Y2K.GOV, many of which have become inaccessible in the years since 2000. Some of these websites have been archived by the
A feature of US government outreach was Y2K websites including Y2K.GOV, many of which have become inaccessible in the years since 2000. Some of these websites have been archived by the National Archives and Records Administration
The National Archives and Records Administration (NARA) is an " independent federal agency of the United States government within the executive branch", charged with the preservation and documentation of government and historical records. It ...
or the Wayback Machine
The Wayback Machine is a digital archive of the World Wide Web founded by the Internet Archive, a nonprofit based in San Francisco, California. Created in 1996 and launched to the public in 2001, it allows the user to go "back in time" and see ...
.
Each federal agency had its own Y2K task force which worked with its private sector counterparts; the FCC had the FCC Year 2000 Task Force.
Most industries had contingency plans that relied upon the internet for backup communications. As no federal agency had clear authority with regard to the internet at this time (it had passed from the US Department of Defense to the US National Science Foundation and then to the US Department of Commerce), no agency was assessing the readiness of the internet itself. Therefore, on 30 July 1999, the White House held the White House Internet Y2K Roundtable.
The U.S. government also established the Center for Year 2000 Strategic Stability as a joint operation with the Russian Federation. It was a liaison operation designed to mitigate the possibility of false positive readings in each nation's nuclear attack early warning systems.

International cooperation
The International Y2K Cooperation Center (IY2KCC) was established at the behest of national Y2K coordinators from over 120 countries when they met at the First Global Meeting of National Y2K Coordinators at the United Nations in December 1998. IY2KCC established an office in Washington, D.C. in March 1999. Funding was provided by the World Bank, and Bruce W. McConnell was appointed as director. IY2KCC's mission was to "promote increased strategic cooperation and action among governments, peoples, and the private sector to minimize adverse Y2K effects on the global society and economy." Activities of IY2KCC were conducted in six areas: * National Readiness: Promoting Y2K programs worldwide * Regional Cooperation: Promoting and supporting co-ordination within defined geographic areas * Sector Cooperation: Promoting and supporting co-ordination within and across defined economic sectors * Continuity and Response Cooperation: Promoting and supporting co-ordination to ensure essential services and provisions for emergency response * Information Cooperation: Promoting and supporting international information sharing and publicity * Facilitation and Assistance: Organizing global meetings of Y2K coordinators and to identify resources IY2KCC closed down in March 2000.Private sector response
Year 10,000 problem
In computer science, time formatting and storage bugs are a class of software bugs that may cause time and date calculation or display to be improperly handled. These are most commonly manifestations of arithmetic overflow, but can also be the ...
by writing all years with five digits. For example, they list "01996" as their year of founding.
* While there was no one comprehensive internet Y2K effort, multiple internet trade associations and organisations banded together to form the Internet Year 2000 Campaign. This effort partnered with the White House's Internet Y2K Roundtable.
The Y2K issue was a major topic of discussion in the late 1990s and as such showed up in most popular media. A number of "Y2K disaster" books were published such as ''Deadline Y2K'' by Mark Joseph. Movies such as ''Y2K: Year to Kill'' capitalized on the currency of Y2K, as did numerous TV shows, comic strips, and computer games.
Fringe group responses
A variety of fringe groups and individuals such as those within some fundamentalist religious organizations,survivalists
Survivalism is a social movement of individuals or groups (called survivalists or preppers) who proactively prepare for emergencies, such as natural disasters, as well as other disasters causing disruption to social order (that is, civil disord ...
, cults
In modern English, ''cult'' is usually a pejorative term for a social group that is defined by its unusual religious, spiritual, or philosophical beliefs and rituals, or its common interest in a particular personality, object, or goal. This ...
, anti-social movements, self-sufficiency
Self-sustainability and self-sufficiency are overlapping states of being in which a person or organization needs little or no help from, or interaction with, others. Self-sufficiency entails the self being enough (to fulfill needs), and a self-s ...
enthusiasts, communes and those attracted to conspiracy theories, embraced Y2K as a tool to engender fear and provide a form of evidence for their respective theories. End-of-the-world scenarios and apocalyptic themes were common in their communication.
Interest in the survivalist movement peaked in 1999 in its second wave for that decade, triggered by Y2K fears. In the time before extensive efforts were made to rewrite computer programming codes to mitigate the possible impacts, some writers such as Gary North, Ed Yourdon
Edward Nash Yourdon (April 30, 1944 ŌĆō January 20, 2016) was an American software engineer, computer consultant, author and lecturer, and software engineering methodology pioneer. He was one of the lead developers of the structured analysis tech ...
, James Howard Kunstler, and Ed Yardeni anticipated widespread power outages, food and gasoline shortages, and other emergencies. North and others raised the alarm because they thought Y2K code fixes were not being made quickly enough. While a range of authors responded to this wave of concern, two of the most survival-focused texts to emerge were ''Boston on Y2K'' (1998) by Kenneth W. Royce, and Mike Oehler's ''The Hippy Survival Guide to Y2K''.
Y2K was also exploited by some fundamentalist and charismatic
Charisma () is a personal quality of presence or charm that compels its subjects.
Scholars in sociology, political science, psychology, and management reserve the term for a type of leadership seen as extraordinary; in these fields, the term "ch ...
Christian leaders throughout the Western world, particularly in North America and Australia. Their promotion of the perceived risks of Y2K was combined with end times thinking and apocalyptic prophecies in an attempt to influence followers. The ''New York Times
''The New York Times'' (''the Times'', ''NYT'', or the Gray Lady) is a daily newspaper based in New York City with a worldwide readership reported in 2020 to comprise a declining 840,000 paid print subscribers, and a growing 6 million paid ...
'' reported in late 1999, "The Rev. Jerry Falwell
Jerry Laymon Falwell Sr. (August 11, 1933 ŌĆō May 15, 2007) was an American Baptist pastor, televangelism, televangelist, and conservatism in the United States, conservative activist. He was the founding pastor of the Thomas Road Baptist Church, ...
suggested that Y2K would be the confirmation of Christian prophecy
In religion, a prophecy is a message that has been communicated to a person (typically called a ''prophet'') by a supernatural entity. Prophecies are a feature of many cultures and belief systems and usually contain divine will or law, or p ...
ŌĆēŌĆöŌĆēGod's instrument to shake this nation, to humble this nation. The Y2K crisis might incite a worldwide revival that would lead to the rapture
The rapture is an Christian eschatology, eschatological position held by some Christians, particularly those of American evangelicalism, consisting of an Eschatology, end-time event when all Christian believers who are alive, along with resurre ...
of the church. Along with many survivalists, Mr. Falwell advised stocking up on food and guns". Adherents in these movements were encouraged to engage in food hoarding, take lessons in self-sufficiency, and the more extreme elements planned for a total collapse of modern society. The ''Chicago Tribune
The ''Chicago Tribune'' is a daily newspaper based in Chicago, Illinois, United States, owned by Tribune Publishing. Founded in 1847, and formerly self-styled as the "World's Greatest Newspaper" (a slogan for which WGN radio and television ar ...
'' reported that some large fundamentalist churches, motivated by Y2K, were the sites for flea market
A flea market (or swap meet) is a type of street market that provides space for vendors to sell previously-owned (second-hand) goods. This type of market is often seasonal. However, in recent years there has been the development of 'formal ...
-like sales of paraphernalia designed to help people survive a social order crisis ranging from gold coins to wood-burning stoves. Betsy Hart
Betsy Hart aka Betsy Meade (born c. 1963) is a professional writer for the conservative organization The Heritage Foundation, syndicated columnist for the Scripps Howard News and conservative commentator who is a frequent contributor to CNN and the ...
, writing for the ''Deseret News
The ''Deseret News'' () is the oldest continuously operating publication in the American west. Its multi-platform products feature journalism and commentary across the fields of politics, culture, family life, faith, sports, and entertainment. Th ...
'', reported that a lot of the more extreme evangelicals used Y2K to promote a political agenda in which downfall of the government was a desired outcome in order to usher in Christ's reign. She also noted that, "the cold truth is that preaching chaos is profitable and calm doesn't sell many tapes or books". These types of fears and conspiracies were described dramatically by New Zealand-based Christian prophetic author and preacher Barry Smith in his publication, "I Spy with my Little Eye", where he dedicated a whole chapter to Y2K. Some expected, at times through so-called prophecies, that Y2K would be the beginning of a worldwide Christian revival.
It became clear in the aftermath that leaders of these fringe groups had used fears of apocalyptic outcomes to manipulate followers into dramatic scenes of mass repentance or renewed commitment to their groups, additional giving of funds and more overt commitment to their respective organizations or churches. The ''Baltimore Sun
''The Baltimore Sun'' is the largest general-circulation daily newspaper based in the U.S. state of Maryland and provides coverage of local and regional news, events, issues, people, and industries.
Founded in 1837, it is currently owned by Tr ...
'' noted this in their article, "Apocalypse NowŌĆēŌĆöŌĆēY2K spurs fears", where they reported the increased call for repentance in the populace in order to avoid God's wrath. Christian leader, Col Stringer, in his commentary has published, "Fear-creating writers sold over 45 million books citing every conceivable catastrophe from civil war, planes dropping from the sky to the end of the civilized world as we know it. Reputable preachers were advocating food storage and a "head for the caves" mentality. No banks failed, no planes crashed, no wars or civil war started. And yet not one of these prophets of doom has ever apologized for their scare-mongering tactics." Some prominent North American Christian ministries and leaders generated huge personal and corporate profits through sales of Y2K preparation kits, generators, survival guides, published prophecies and a wide range of other associated merchandise. Christian journalist, Rob Boston, has documented this in his article "False Prophets, Real ProfitsŌĆēŌĆöŌĆēReligious Right Leaders' Wild Predictions of Y2K Disaster Didn't Come True, But They Made Money Anyway".
Cost
The total cost of the work done in preparation for Y2Kwhich was well underway by 1996: is estimated at over US$300 billion ($ billion as of January 2018, once inflation is taken into account). IDC calculated that the US spent an estimated $134 billion ($ billion) preparing for Y2K, and another $13 billion ($ billion) fixing problems in 2000 and 2001. Worldwide, $308 billion ($ billion) was estimated to have been spent on Y2K remediation.Remedial work organization
The remedial work was driven by customer demand for solutions. Software suppliers, mindful of their potential legal liability, responded with remedial effort. Software subcontractors were required to certify that their software components were free of date-related problems, which drove further work down the supply chain. By 1999, many corporations required their suppliers to certify, often on their own variation of a basic form, that all of their software is Y2K compliant. Some merely accepted remedial updates and then signed. Many businesses or even whole countries who spent little effort themselves nonetheless suffered only minor problems.Results
There are two ways to view the events of 2000 from the perspective of its aftermath:Supporting view
This view holds that the vast majority of problems were fixed correctly, and the money spent was at least partially justified. The situation was essentially one of preemptive alarm. Those who hold this view claim that the lack of problems at the date change reflects the completeness of the project, and that many computer applications would not have continued to function into the 21st century without correction or remediation. Expected problems that were not seen by small businesses and small organizations were prevented by Y2K fixes embedded in routine updates to operating system and utility software that were applied several years before 31 December 1999. The extent to which larger industry and government fixes averted issues that would have more significant impacts had they not been fixed, were typically not disclosed or widely reported.James Christie, (12 January 2015), Y2K ŌĆō why I know it was a real problem, 'Claro Testing Blog'(accessed 12 January 2015) It has been suggested that on
11 September 2001
The September 11 attacks, commonly known as 9/11, were four coordinated suicide terrorist attacks carried out by al-Qaeda against the United States on Tuesday, September 11, 2001. That morning, nineteen terrorists hijacked four commerc ...
, infrastructure in New York City (including subways, phone service, and financial transactions) was able to continue operation because of the redundant networks established in the event of Y2K bug impact and the contingency plans devised by companies. The terrorist attacks and the following prolonged blackout to lower Manhattan
Lower Manhattan (also known as Downtown Manhattan or Downtown New York) is the southernmost part of Manhattan, the central borough for business, culture, and government in New York City, which is the most populated city in the United States with ...
had minimal effect on global banking systems. Backup systems were activated at various locations around the region, many of which had been established to deal with a possible complete failure of networks in Manhattan's Financial District on 31 December 1999.
Opposing view
The contrary view asserts that there were no, or very few, critical problems to begin with. This view also asserts that there would have been only a few minor mistakes and that a "fix on failure" approach would have been the most efficient and cost-effective way to solve these problems as they occurred. International Data Corporation estimated that the US might have wasted $40 billion. Sceptics of the need for a massive effort pointed to the absence of Y2K-related problems occurring before 1 January 2000, even though the 2000 financial year commenced in 1999 in many jurisdictions, and a wide range of forward-looking calculations involved dates in 2000 and later years. Estimates undertaken in the leadup to 2000 suggested that around 25% of all problems should have occurred before 2000. Critics of large-scale remediation argued during 1999 that the absence of significant reported problems in non-compliant small firms was evidence that there had been, and would be, no serious problems needing to be fixed in ''any'' firm, and that the scale of the problem had therefore been severely overestimated. Countries such as South Korea and Russia invested little to nothing in Y2K remediation, yet had the same negligible Y2K problems as countries that spent enormous sums of money. Western countries anticipated such severe problems in Russia that many issued travel advisories and evacuated non-essential staff Critics also cite the lack of Y2K-related problems in schools, many of which undertook little or no remediation effort. By 1 September 1999, only 28% of US schools had achieved compliance for mission critical systems, and a government report predicted that "Y2K failures could very well plague the computers used by schools to manage payrolls, student records, online curricula, and building safety systems". Similarly, there were few Y2K-related problems in an estimated 1.5 million small businesses that undertook no remediation effort. On 3 January 2000 (the first weekday of the year), the Small Business Administration received an estimated 40 calls from businesses with computer issues, similar to the average. None of the problems were critical..See also
*512k day
Border Gateway Protocol (BGP) is a standardized exterior gateway protocol designed to exchange routing and reachability information among autonomous systems (AS) on the Internet. BGP is classified as a path-vector routing protocol, and it make ...
: an event in 2014, involving a software limitation in network routers
* IPv4 address exhaustion, problems caused by the limited allocation size for numeric internet addresses
* ISO 8601, an international standard for representing dates and times, which mandates the use of (at least) four digits for the year
* " Life's a Glitch, Then You Die" is a "Treehouse of Horror segment" from ''The Simpsons'' eleventh season. The segment sees Homer forget to make his company's computers Y2K-compliant and this caused a virus to be unleashed upon the world
* Perpetual calendar, a calendar valid for many years, including before and after 2000
* '' Y2K'', a 1999 American made-for-television science fiction
Science fiction (sometimes shortened to Sci-Fi or SF) is a genre of speculative fiction which typically deals with imaginative and futuristic concepts such as advanced science and technology, space exploration, time travel, parallel uni ...
-thriller film
Thriller film, also known as suspense film or suspense thriller, is a broad film genre that evokes excitement and suspense in the audience. The suspense element found in most films' plots is particularly exploited by the filmmaker in this genre. ...
directed by Dick Lowry
* YEAR2000, a configuration setting supported by some versions of DR-DOS to overcome Year 2000 BIOS bugs
* Millennium celebrations, a worldwide, coordinated series of events to celebrate and commemorate the end of 1999 and the start of the year 2000 in the Gregorian calendar.
Notes
References
External links
Center for Y2K and Society Records
Charles Babbage Institute, University of Minnesota. Documents activities of Center for Y2K and Society (based in Washington, D.C.) working with non-profit institutions and foundations to respond to possible societal impacts of the Y2K computer problem: helping the poor and vulnerable as well as protecting human health and the environment. Records donated by executive director, Norman L. Dean.
International Y2K Cooperation Center Records, 1998ŌĆō2000
Charles Babbage Institute, University of Minnesota. Collection contains the materials of the International Y2K Cooperation Center. Includes country reports, news clippings, country questionnaires, country telephone directories, background materials, audio visual materials and papers of Bruce W. McConnell, director of IY2KCC.
Preparing for an Apocalypse: Y2K
Charles Babbage Institute, University of Minnesota. A web exhibit curated by Stephanie H. Crowe
BBC: Y2K coverage
''In The Beginning there Was the Nerd''
ŌĆō BBC Radio documentary about the history of computers and the millennium bug 10 years after using archival recordings.
ŌĆō Radio documentary by American Public Media, on the history and legacy of the millennium bug five years on.
CBC Digital Archives ŌĆō The Eve of the Millennium
How the UK coped with the millennium bug
Ćö CNN {{DEFAULTSORT:Year 2000 problem Problem 2000 in Internet culture Calendars COBOL Doomsday scenarios Technology hazards Software bugs Year 02000 problem Turn of the third millennium