Nethack on:
[Wikipedia]
[Google]
[Amazon]
''NetHack'' is an
 ''NetHack'' features a variety of items:
''NetHack'' features a variety of items: ' s identification of items is almost identical to ''' s. For example, a newly discovered potion may be referred to as a "pink potion" with no other clues as to its identity. Players can perform a variety of actions and tricks to deduce, or at least narrow down, the identity of the potion. The most obvious is the somewhat risky tactic of simply drinking it. All items of a certain type will have the same description. For instance, all "scrolls of enchant weapon" may be labeled "TEMOV", and once one has been identified, all "scrolls of enchant weapon" found later will be labeled unambiguously as such. Starting a new game will scramble the items descriptions again, so the "silver ring" that is a "ring of levitation" in one game might be a "ring of hunger" in another.
File:NetHack for Windows Screenshot.png, ''NetHack'' for Microsoft Windows in "tiles mode"
File:Vultures-2.1.0 screenshot.jpg, ''Vulture's Eye'' offers an isometric perspective
File:NeXTSTEP Nethack.png, ''NetHack'' on
A Guide to the Mazes of Menace (Guidebook for ''NetHack'')
*
*
The NetHack Wiki
NAO website
/dev/null NetHack Tournament
* *
''NetHack''
at SourceForge.net
Hall of Fame – ''NetHack''
at
open source
Open source is source code that is made freely available for possible modification and redistribution. Products include permission to use the source code, design documents, or content of the product. The open-source model is a decentralized so ...
single-player roguelike
Roguelike (or rogue-like) is a subgenre of role-playing computer games traditionally characterized by a dungeon crawl through procedurally generated levels, turn-based gameplay, grid-based movement, and permanent death of the player charac ...
video game
Video games, also known as computer games, are electronic games that involves interaction with a user interface or input device such as a joystick, controller, keyboard, or motion sensing device to generate visual feedback. This feedba ...
, first released in 1987 and maintained by the NetHack DevTeam. The game is a fork
In cutlery or kitchenware, a fork (from la, furca 'pitchfork') is a utensil, now usually made of metal, whose long handle terminates in a head that branches into several narrow and often slightly curved tine (structural), tines with which one ...
of the 1982 game ''Hack
Hack may refer to:
Arts, entertainment, and media Games
* ''Hack'' (Unix video game), a 1984 roguelike video game
* ''.hack'' (video game series), a series of video games by the multimedia franchise ''.hack''
Music
* ''Hack'' (album), a 199 ...
'', itself inspired by the 1980 game ''Rogue
A rogue is a person or entity that flouts accepted norms of behavior.
Rogue or rogues may also refer to:
Companies
* Rogue Ales, a microbrewery in Newport, Oregon
* Rogue Arts, a film production company
* Rogue Entertainment, a software co ...
''. The player takes the role as one of several pre-defined character class
In tabletop games and video games, a character class is a job or profession commonly used to differentiate the abilities of different game characters.
In role-playing games (RPGs), character classes aggregate several abilities and aptitudes, ...
es to descend through multiple dungeon floors, fighting monsters and collecting treasure, to recover the "Amulet of Yendor" at the lowest floor and then escape.
As an exemplar of the traditional "roguelike" game, ''NetHack'' features turn-based
In video and other games, the passage of time must be handled in a way that players find fair and easy to understand. This is usually done in one of the two ways: real-time and turn-based.
Real-time
Real-time games have game time progress cont ...
, grid-based hack and slash
Hack and slash, also known as hack and slay (H&S or HnS) or slash 'em up, refers to a type of gameplay that emphasizes combat with melee-based weapons (such as swords or blades). They may also feature projectile-based weapons as well (such a ...
dungeon crawl
A dungeon crawl is a type of scenario in fantasy role-playing games in which heroes navigate a labyrinth environment (a " dungeon"), battling various monsters, avoiding traps, solving puzzles, and looting any treasure they may find. Video games a ...
ing gameplay, procedurally generated
In computing, procedural generation is a method of creating data algorithmically as opposed to manually, typically through a combination of human-generated assets and algorithms coupled with computer-generated randomness and processing power. In ...
dungeons and treasure, and permadeath
Permadeath or permanent death is a game mechanic in both tabletop games and video games in which player characters who lose all of their health are considered dead and cannot be used anymore. Depending on the situation, this could require the p ...
, requiring the player to restart the game anew should the player character
A player character (also known as a playable character or PC) is a fictional character in a video game or tabletop role-playing game whose actions are controlled by a player rather than the rules of the game. The characters that are not control ...
die. The game uses simple ASCII
ASCII ( ), abbreviated from American Standard Code for Information Interchange, is a character encoding standard for electronic communication. ASCII codes represent text in computers, telecommunications equipment, and other devices. Because ...
graphics by default so as to display readily on a wide variety of computer displays
A computer monitor is an output device that displays information in pictorial or textual form. A discrete monitor comprises a visual display, support electronics, power supply, housing, electrical connectors, and external user controls.
Th ...
, but can use curses
A curse (also called an imprecation, malediction, execration, malison, anathema, or commination) is any expressed wish that some form of adversity or misfortune will befall or attach to one or more persons, a place, or an object. In particular ...
with box-drawing characters
Box-drawing characters, also known as line-drawing characters, are a form of semigraphics widely used in text user interfaces to draw various geometric frames and boxes. Box-drawing characters typically only work well with monospaced fonts. ...
, as well as substitute graphical tilesets on machines with graphics. While ''Rogue'', ''Hack'' and other earlier roguelikes stayed true to a high fantasy
High fantasy, or epic fantasy, is a subgenre of fantasy defined by the epic nature of its setting or by the epic stature of its characters, themes, or plot.Brian Stableford, ''The A to Z of Fantasy Literature'', (p. 198), Scarecrow Press, ...
setting, ''NetHack'' introduced humorous and anachronistic
An anachronism (from the Greek , 'against' and , 'time') is a chronological inconsistency in some arrangement, especially a juxtaposition of people, events, objects, language terms and customs from different time periods. The most common type ...
elements over time, including popular cultural reference to works such as ''Discworld
''Discworld'' is a comic fantasy"Humorous Fantasy" in David Pringle, ed., ''The Ultimate Encyclopedia of Fantasy'' (pp.31-33). London, Carlton,2006. book series written by the English author Terry Pratchett, set on the Discworld, a flat ...
'' and ''Raiders of the Lost Ark
''Raiders of the Lost Ark'' is a 1981 American action-adventure film directed by Steven Spielberg and written by Lawrence Kasdan, based on a story by George Lucas and Philip Kaufman. It stars Harrison Ford, Karen Allen, Paul Freeman, Ro ...
''.
It is identified as one of the "major roguelikes" by John Harris. Comparing it with ''Rogue'', ''Engadget
''Engadget'' ( ) is a multilingual technology blog network with daily coverage of gadgets and consumer electronics. ''Engadget'' manages ten blogs four of which are written in English and six have international versions with independent editor ...
''s Justin Olivetti wrote that it took its exploration aspect and "made it far richer with an encyclopedia of objects, a larger vocabulary, a wealth of pop culture mentions, and a puzzler's attitude." In 2000, ''Salon
Salon may refer to:
Common meanings
* Beauty salon, a venue for cosmetic treatments
* French term for a drawing room, an architectural space in a home
* Salon (gathering), a meeting for learning or enjoyment
Arts and entertainment
* Salon ( ...
'' described it as "one of the finest gaming experiences the computing world has to offer".
Gameplay
Before starting a game, players choose their character'srace
Race, RACE or "The Race" may refer to:
* Race (biology), an informal taxonomic classification within a species, generally within a sub-species
* Race (human categorization), classification of humans into groups based on physical traits, and/or s ...
, role
A role (also rôle or social role) is a set of connected behaviors, rights, moral obligation, obligations, beliefs, and social norm, norms as conceptualized by people in a social situation. It is an expected or free or continuously changing behavi ...
, sex, and alignment
Alignment may refer to:
Archaeology
* Alignment (archaeology), a co-linear arrangement of features or structures with external landmarks
* Stone alignment, a linear arrangement of upright, parallel megalithic standing stones
Biology
* Struc ...
, or allow the game to assign the attributes randomly. There are traditional fantasy roles such as knight
A knight is a person granted an honorary title of knighthood by a head of state (including the Pope) or representative for service to the monarch, the Christian denomination, church or the country, especially in a military capacity. Knighthood ...
, wizard, rogue
A rogue is a person or entity that flouts accepted norms of behavior.
Rogue or rogues may also refer to:
Companies
* Rogue Ales, a microbrewery in Newport, Oregon
* Rogue Arts, a film production company
* Rogue Entertainment, a software co ...
, and priest
A priest is a religious leader authorized to perform the sacred rituals of a religion, especially as a mediatory agent between humans and one or more deities. They also have the authority or power to administer religious rites; in partic ...
; but there are also unusual roles, including archaeologist
Archaeology or archeology is the scientific study of human activity through the recovery and analysis of material culture. The archaeological record consists of artifacts, architecture, biofacts or ecofacts, sites, and cultural landsca ...
, tourist
Tourism is travel for pleasure or business; also the theory and practice of touring, the business of attracting, accommodating, and entertaining tourists, and the business of operating tours. The World Tourism Organization defines tourism ...
, and caveman
The caveman is a stock character representative of primitive humans in the Paleolithic. The popularization of the type dates to the early 20th century, when Neanderthals were influentially described as "simian" or " ape-like" by Marcellin Bo ...
. The player character
A player character (also known as a playable character or PC) is a fictional character in a video game or tabletop role-playing game whose actions are controlled by a player rather than the rules of the game. The characters that are not control ...
's role and alignment dictate which deity
A deity or god is a supernatural being who is considered divine or sacred. The ''Oxford Dictionary of English'' defines deity as a god or goddess, or anything revered as divine. C. Scott Littleton defines a deity as "a being with powers greate ...
the character serves in the game, "how other monsters react toward you", as well as character skills and attributes.
After the player character is created, the main objective is introduced. To win the game, the player must retrieve the Amulet of Yendor, found at the lowest level of the dungeon, and offer it to their deity. Successful completion of this task rewards the player with the gift of immortality
Immortality is the concept of eternal life. Some modern species may possess biological immortality.
Some scientists, futurists, and philosophers have theorized about the immortality of the human body, with some suggesting that human immorta ...
, and the player is said to "ascend", attaining the status of demigod
A demigod or demigoddess is a part-human and part-divine offspring of a deity and a human, or a human or non-human creature that is accorded divine status after death, or someone who has attained the "divine spark" ( spiritual enlightenment). A ...
. Along the path to the amulet, a number of sub-quests must be completed, including one class-specific quest.
There are 3 major antagonists in NetHack; the Luciferesque god Moloch, who stole the Amulet Of Yendor from the creator god
A creator deity or creator god (often called the Creator) is a deity responsible for the creation of the Earth, world, and universe in human religion and mythology. In monotheism, the single God is often also the creator. A number of monolatri ...
Marduk
Marduk (Cuneiform: dAMAR.UTU; Sumerian: ''amar utu.k'' "calf of the sun; solar calf"; ) was a god from ancient Mesopotamia and patron deity of the city of Babylon. When Babylon became the political center of the Euphrates valley in the time of ...
, the high priest/priestess of Moloch, who holds the Amulet of Yendor, and the most prominent antagonist, the Wizard of Yendor, who will stalk the player throughout the rest of the game after the first encounter by resurrecting and attacking them periodically.
The player's character is, unless they opt not to be, accompanied by a pet animal, typically a kitten
A kitten is a juvenile cat. After being born, kittens display primary altriciality and are totally dependent on their mothers for survival. They normally do not open their eyes for seven to ten days. After about two weeks, kittens develop q ...
or little dog, although knights begin with a saddle
The saddle is a supportive structure for a rider of an animal, fastened to an animal's back by a girth. The most common type is equestrian. However, specialized saddles have been created for oxen, camels and other animals. It is not kno ...
d pony
A pony is a type of small horse ('' Equus ferus caballus''). Depending on the context, a pony may be a horse that is under an approximate or exact height at the withers, or a small horse with a specific conformation and temperament. Compared ...
. Pets grow from fighting, and they can be changed by various means. Most of the other monsters may also be tamed using magic or food.
Dungeon levels
''NetHacks dungeon spans about fifty primary levels, most of which areprocedurally generated
In computing, procedural generation is a method of creating data algorithmically as opposed to manually, typically through a combination of human-generated assets and algorithms coupled with computer-generated randomness and processing power. In ...
when the player character enters them for the first time. A typical level contains a way "up" and "down" to other levels. These may be stairways, ladders, trapdoors, etc. Levels also contain several "rooms" joined by corridors. These rooms are randomly generated rectangles (as opposed to the linear corridors) and may contain features such as altars, shops, fountains, traps, thrones, pools of water, and sinks based on the randomly generated features of the room. Some specific levels follow one of many fixed designs or contain fixed elements. Later versions of the game added special branches of dungeon levels. These are optional routes that may feature more challenging monsters but can reward more desirable treasure to complete the main dungeon. Levels, once generated, remained persistent, in contrast to games that followed ''Moria
Moria may refer to:
Arts and entertainment
* Moria (Middle-earth), fictional location in the works of J. R. R. Tolkien
* '' Moria: The Dwarven City'', a 1984 fantasy role-playing game supplement
* ''Moria'' (1978 video game), a dungeon-crawler g ...
''-style of level generation.
Items and tools
 ''NetHack'' features a variety of items:
''NetHack'' features a variety of items: weapon
A weapon, arm or armament is any implement or device that can be used to deter, threaten, inflict physical damage, harm, or kill. Weapons are used to increase the efficacy and efficiency of activities such as hunting, crime, law enforcement, s ...
s (melee
A melee ( or , French: mêlée ) or pell-mell is disorganized hand-to-hand combat in battles fought at abnormally close range with little central control once it starts. In military aviation, a melee has been defined as " air battle in which ...
or ranged), armor
Armour (British English) or armor (American English; see spelling differences) is a covering used to protect an object, individual, or vehicle from physical injury or damage, especially direct contact weapons or projectiles during combat, or f ...
to protect the player, scroll
A scroll (from the Old French ''escroe'' or ''escroue''), also known as a roll, is a roll of papyrus, parchment, or paper containing writing.
Structure
A scroll is usually partitioned into pages, which are sometimes separate sheets of papyrus ...
s and spellbooks to read, potion
A potion () is a liquid "that contains medicine, poison, or something that is supposed to have magic powers.” It derives from the Latin word ''potus'' which referred to a drink or drinking. The term philtre is also used, often specifically ...
s to quaff, wands, rings, amulets, and an assortment of tool
A tool is an object that can extend an individual's ability to modify features of the surrounding environment or help them accomplish a particular task. Although many animals use simple tools, only human beings, whose use of stone tools dates b ...
s, such as keys and lamps.
''NetHack''Rogue
A rogue is a person or entity that flouts accepted norms of behavior.
Rogue or rogues may also refer to:
Companies
* Rogue Ales, a microbrewery in Newport, Oregon
* Rogue Arts, a film production company
* Rogue Entertainment, a software co ...
''Blessings and curses
As in many other roguelike games, all items in ''NetHack'' are either "blessed
Blessed may refer to:
* The state of having received a blessing
* Blessed, a title assigned by the Roman Catholic Church to someone who has been beatified
Film and television
* ''Blessed'' (2004 film), a 2004 motion picture about a supernatural ...
", "uncursed", or "curse
A curse (also called an imprecation, malediction, execration, malison, anathema, or commination) is any expressed wish that some form of adversity or misfortune will befall or attach to one or more persons, a place, or an object. In particula ...
d". The majority of items are found uncursed, but the blessed or cursed status of an item is unknown until it is identified or detected through other means.
Generally, a blessed item will be more powerful than an uncursed item, and a cursed item will be less powerful, with the added disadvantage that once it has been equipped by the player, it cannot be easily unequipped. Where an object would bestow an effect upon the character, a curse will generally make the effect harmful, or increase the amount of harm done. However, there are very specific exceptions. For example, drinking a cursed "potion of gain level" will make the character literally rise through the ceiling to the level above, instead of gaining an experience level
An experience point (often abbreviated as exp or XP) is a unit of measurement used in some tabletop role-playing games (RPGs) and role-playing video games to quantify a player character's life experience and progression through the game. Experien ...
.
Character death
As in other roguelike games, ''NetHack'' featurespermadeath
Permadeath or permanent death is a game mechanic in both tabletop games and video games in which player characters who lose all of their health are considered dead and cannot be used anymore. Depending on the situation, this could require the p ...
: expired characters cannot be revived.
Although ''NetHack'' can be completed without any artificial limitations, experienced players can attempt "conducts" for an additional challenge. These are voluntary restrictions on actions taken, such as using no wishes, following a vegetarian
Vegetarianism is the practice of abstaining from the consumption of meat (red meat, poultry, seafood, insects, and the flesh of any other animal). It may also include abstaining from eating all by-products of animal slaughter.
Vegetariani ...
or vegan
Veganism is the practice of abstaining from the use of animal product—particularly in diet—and an associated philosophy that rejects the commodity status of animals. An individual who follows the diet or philosophy is known as a vegan. ...
diet, or even killing no monsters. While conducts are generally tracked by the game and are displayed at death or ascension, unofficial conducts are practiced within the community.
When a player dies, the cause of death and score is created and added to the list where the player's character is ranked against other previous characters. The prompt "Do you want your possessions identified?" is given by default at the end of any game, allowing the player to learn any unknown properties of the items in their inventory at death. The player's attributes (such as resistances, luck, and others), conduct (usually self-imposed challenges, such as playing as an atheist or a vegetarian), and a tally of creatures killed, may also be displayed.
The game sporadically saves a level on which a character has died and then integrates that level into a later game. This is done via "bones files", which are saved on the computer hosting the game. A player using a publicly hosted copy of the game can thus encounter the remains and possessions of many other players, although many of these possessions may have become cursed.
Because of the numerous ways that a player-character could die between a combination of their own actions as well as from reactions from the game's interacting systems, players frequently refer to untimely deaths as "Yet Another Stupid Death" (YASD). Such deaths are considered part of learning to play ''NetHack'' as to avoid conditions where the same death may happen again.
''NetHack'' does allow players to save the game so that one does not have to complete the game in one session, but on opening a new game, the previous save file is subsequently wiped as to enforce the permadeath option. One option some players use is to make a backup copy of the save game file before playing a game, and, should their character die, restoring from the copied version, a practice known as "save scumming". Additionally, players can also manipulate the "bones files" in a manner not intended by the developers. While these help the player to learn the game and get around limits of permadeath, both are considered forms of cheating the game.
Culture around spoilers
''NetHack'' is largely based on discovering secrets and tricks during gameplay. It can take years for one to become well-versed in them, and even experienced players routinely discover new ones. A number of ''NetHack'' fan sites and discussion forums offer lists of game secrets known as "spoilers".Interface
''NetHack'' was originally created with only a simple ASCIItext-based user interface
In computing, text-based user interfaces (TUI) (alternately terminal user interfaces, to reflect a dependence upon the properties of computer terminals and not just text), is a retronym describing a type of user interface (UI) common as an ear ...
, although the option to use something more elaborate was added later in its development. Interface elements such as the environment, entities, and objects are represented by arrangements of ASCII
ASCII ( ), abbreviated from American Standard Code for Information Interchange, is a character encoding standard for electronic communication. ASCII codes represent text in computers, telecommunications equipment, and other devices. Because ...
or Extended ASCII
Extended ASCII is a repertoire of character encodings that include (most of) the original 96 ASCII character set, plus up to 128 additional characters. There is no formal definition of "extended ASCII", and even use of the term is sometimes critic ...
glyphs, " DECgraphics", or " IBMgraphics" mode. In addition to the environment, the interface also displays character and situational information.
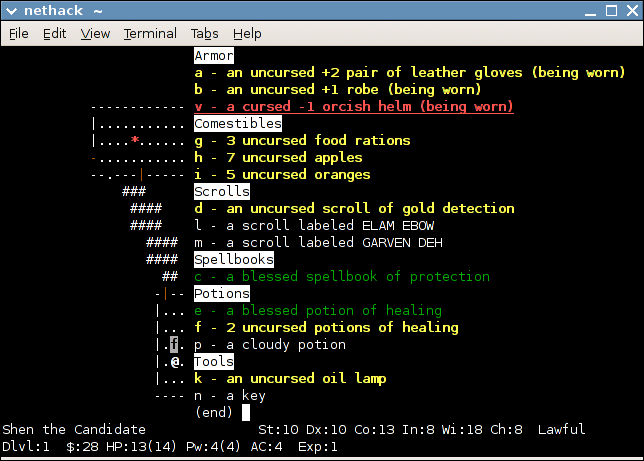
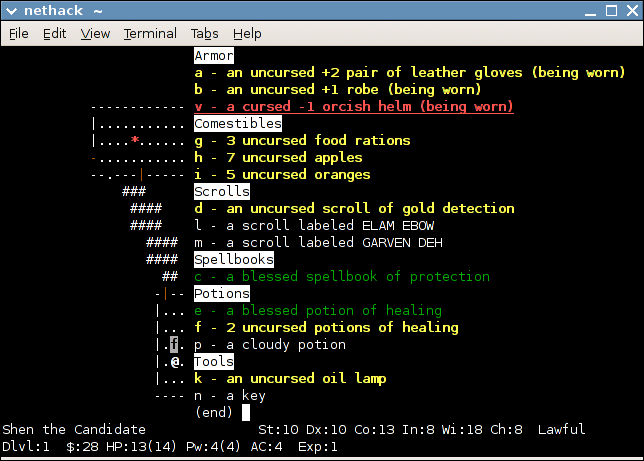
A detailed example:
You see here a silver ring.
------------
##....._.....,
, ...........# ------
#..........., , ....,
--------------- ###------------ , ...(,
, ..%..........., ########## ###-@...,
, ...%...........### # ## , ....,
+.......<......, ### ### , ..!.,
--------------- # # ------
### ###
# #
---.----- ###
, ......., #
, ........####
, .......,
, .......,
---------
Hacker the Conjurer St:11 Dx:13 Co:12 In:11 Wi:18 Ch:11 Neutral
Dlvl:3 $:120 HP:39(41) Pw:36(36) AC:6 Exp:5 T:1073
The player (the '@' sign, a wizard in this case) has entered the level via the stairs (the '<' sign) and killed a few monsters, leaving their corpses (the '%' signs) behind. Exploring, the player has uncovered three rooms joined by corridors (the '#' signs): one with an altar (the '_' sign), another empty, and the final one (that the player is currently in) containing a potion (the '!' sign) and chest (the '(' sign). The player has just moved onto a square containing a silver ring. Parts of the level are still unexplored (probably accessible through the door to the west (the '+' sign)) and the player has yet to find the downstairs (a '>' sign) to the next level.
Apart from the original termcap
Termcap (''terminal capability'') is a software library and database used on Unix-like computers. It enables programs to use display computer terminals in a device-independent manner, which greatly simplifies the process of writing portable text ...
interface shown above, there are other interfaces that replace standard screen representations with two-dimensional
In mathematics, a plane is a Euclidean ( flat), two-dimensional surface that extends indefinitely. A plane is the two-dimensional analogue of a point (zero dimensions), a line (one dimension) and three-dimensional space. Planes can arise as ...
images, or tiles
Tiles are usually thin, square or rectangular coverings manufactured from hard-wearing material such as ceramic, Rock (geology), stone, metal, baked clay, or even glass. They are generally fixed in place in an array to cover roofs, floors, wa ...
, collectively known as "tiles mode". Graphic interfaces of this kind have been successfully implemented on the Amiga
Amiga is a family of personal computers introduced by Commodore International, Commodore in 1985. The original model is one of a number of mid-1980s computers with 16- or 32-bit processors, 256 KB or more of RAM, mouse-based GUIs, and sign ...
, the X Window System
The X Window System (X11, or simply X) is a windowing system for bitmap displays, common on Unix-like operating systems.
X provides the basic framework for a GUI environment: drawing and moving windows on the display device and interacting wi ...
, the Microsoft Windows
Windows is a group of several proprietary graphical operating system families developed and marketed by Microsoft. Each family caters to a certain sector of the computing industry. For example, Windows NT for consumers, Windows Server for ...
GUI, the Qt toolkit
Qt (pronounced "cute") is cross-platform software for creating graphical user interfaces as well as cross-platform applications that run on various software and hardware platforms such as Linux, Windows, macOS, Android or embedded systems wi ...
, and the GNOME
A gnome is a mythological creature and diminutive spirit in Renaissance magic and alchemy, first introduced by Paracelsus in the 16th century and later adopted by more recent authors including those of modern fantasy literature. Its characte ...
libraries.
Enhanced graphical options also exist, such as the isometric perspective
Isometric video game graphics are graphics employed in video games and pixel art that use a parallel projection, but which angle the viewpoint to reveal facets of the environment that would otherwise not be visible from a top-down perspective ...
of ''Falcon's Eye
''Falcon's Eye'' is a version of the roguelike video game ''NetHack'' which introduces isometric graphics and mouse control. ''Falcon's Eye'' has been praised for improving ''NetHacks visuals and audio to an almost commercial level and has ...
'' and ''Vulture's Eye'', or the three-dimensional
Three-dimensional space (also: 3D space, 3-space or, rarely, tri-dimensional space) is a geometric setting in which three values (called '' parameters'') are required to determine the position of an element (i.e., point). This is the inform ...
rendering that noegnud offers. ''Vulture's Eye'' is a fork
In cutlery or kitchenware, a fork (from la, furca 'pitchfork') is a utensil, now usually made of metal, whose long handle terminates in a head that branches into several narrow and often slightly curved tine (structural), tines with which one ...
of the now defunct Falcon's Eye project. ''Vulture's Eye'' adds additional graphics, sounds, bug fixes and performance enhancements and is under active development in an open collaborative environment.
OPENSTEP
OpenStep is a defunct object-oriented application programming interface (API) specification for a legacy object-oriented operating system, with the basic goal of offering a NeXTSTEP-like environment on non-NeXTSTEP operating systems. OpenStep wa ...
/NeXTSTEP
NeXTSTEP is a discontinued object-oriented, multitasking operating system based on the Mach kernel and the UNIX-derived BSD. It was developed by NeXT Computer in the late 1980s and early 1990s and was initially used for its range of propri ...
History and development
''NetHack'' is a software derivative of ''Hack'', which itself was inspired by ''Rogue''. ''Hack'' was created by students Jay Fenlason, Kenny Woodland, Mike Thome, and Jonathan Payne atLincoln-Sudbury Regional High School
Lincoln-Sudbury Regional High School (LSRHS or L-S) is a public regional high school in Sudbury, Massachusetts, with a 99% graduation-rate. The school was founded in 1954, and the building was replaced prior to the 2004–2005 academic year, wit ...
as part of a computer class, after seeing and playing ''Rogue'' at the University of California Berkeley computer labs.Craddock 2015, Chapter 5: "When the Inmates Run the Asylum - Hack-ing at Lincoln-Sudbury High School" The group had tried to get the source code of ''Rogue'' from Glenn Wichman Glenn R. Wichman (born in 1960 in Bay City, Michigan) is a software developer and one of the original authors of the computer game '' Rogue'', along with Michael Toy, Ken Arnold and Jon Lane. Wichman has also contributed to many other commercial so ...
and Michael Toy to build upon, but Wichman and Toy had refused, forcing the students to build the dungeon-creation routines on their own. As such, the game was named ''Hack'' in part for the hack-and-slash gameplay and that the code to generate the dungeons was considered a programming hack. After their classes ended, the students' work on the program also ended, though they had a working game. Fenlason provided the source code
In computing, source code, or simply code, is any collection of code, with or without comments, written using a human-readable programming language, usually as plain text. The source code of a program is specially designed to facilitate the ...
to a local USENIX conference, and eventually it was uploaded to USENET
Usenet () is a worldwide distributed discussion system available on computers. It was developed from the general-purpose Unix-to-Unix Copy (UUCP) dial-up network architecture. Tom Truscott and Jim Ellis conceived the idea in 1979, and it wa ...
newsgroups. The code drew the attention of many players who started working to modify and improve the game as well as port it to other computer systems. ''Hack'' did not have any formal maintainer and while one person was generally recognized to hold the main code to the current version of ''Hack'', many software forks emerged from the unorganized development of the game.
Eventually, Mike Stephenson took on the role as maintainer of the ''Hack'' source code. At this point, he decided to create a new fork of the game, bringing in novel ideas from Izchak Miller, a philosophy professor at University of Pennsylvania
The University of Pennsylvania (also known as Penn or UPenn) is a Private university, private research university in Philadelphia. It is the fourth-oldest institution of higher education in the United States and is ranked among the highest- ...
, and Janet Walz, another computer hacker. They called themselves the DevTeam and renamed their branch ''NetHack'' since their collaboration work was done over the Internet.Craddock 2015, Chapter 6: "It Takes a Village: Raising NetHack" They expanded the bestiary and other objects in the game, and drew from other sources outside of the high fantasy setting, such as from ''Discworld
''Discworld'' is a comic fantasy"Humorous Fantasy" in David Pringle, ed., ''The Ultimate Encyclopedia of Fantasy'' (pp.31-33). London, Carlton,2006. book series written by the English author Terry Pratchett, set on the Discworld, a flat ...
'' with the introduction of the tourist character class. Knowing of the multiple forks of ''Hack'' that existed, the DevTeam established a principle that while the game was open source and anyone could create a fork as a new project, only a few select members in the DevTeam could make modifications to the main source repository of the game, so that players could be assured that the DevTeam's release was the legitimate version of ''NetHack''.
Release history
The DevTeam's first release of ''NetHack'' was on 28 July 1987. The core DevTeam had expanded with the release of ''NetHack'' 3.0 in July 1989. By that point, they had established a tight-lipped culture, revealing little, if anything, between releases. Owing to the ever-increasing depth and complexity found in each release, the development team enjoys a near-mythical status among fans. This perceived omniscience is captured in the initialism TDTTOE, "The DevTeam Thinks of Everything", in that many of the possibleemergent gameplay
Emergent gameplay refers to complex situations in video games, board games, or table top role-playing games that emerge from the interaction of relatively simple game mechanics.
Designers have attempted to encourage emergent play by providing too ...
elements that could occur due to the behavior of the complex game systems had already been programmed in by the DevTeam. Since version 3.0, the DevTeam has typically kept to minor bug fix updates, represented by a change in the third version number (e.g. v3.0.1 over v3.0.0), and only releases major updates (v3.1.0 over v3.0.0) when significant new features are added to the game, including support for new platforms. Many of those from the community that helped with the ports to other systems were subsequently invited to be part of the DevTeam as the team's needs grew, with Stephenson remaining the key member currently.
Updates to the game were generally regular from around 1987 through 2003, with the DevTeam releasing v3.4.3 in December 2003. Subsequent updates from the DevTeam included new tilesets and compatibility with variants of Mac OS, but no major updates to the game had been made. In the absence of new releases from the developers, several community-made updates to the code and variants developed by fans emerged.
On 7 December 2015, version 3.6.0 was released, the first major release in over a decade. While the patch did not add major new gameplay features, the update was designed to prepare the game for expansion in the future, with the DevTeam's patch notes stating "This release consists of a series of foundational changes in the team, underlying infrastructure and changes to the approach to game development". Stephenson said that despite the number of roguelike titles that had emerged since the v3.4.3 release, they saw that ''NetHack'' was still being talked about online in part due to its high degree of portability, and decided to continue its development. According to DevTeam member Paul Winner, they looked to evaluate what community features had been introduced in the prior decade to improve the game while maintaining the necessary balance. The update came shortly after the death of Terry Pratchett
Sir Terence David John Pratchett (28 April 1948 – 12 March 2015) was an English humourist, satirist, and author of fantasy novels, especially comical works. He is best known for his '' Discworld'' series of 41 novels.
Pratchett's first no ...
, whose ''Discworld'' had been influential on the game, and the new update included a tribute to him. With the v3.6.0 release, ''NetHack'' remains "one of the oldest games still being developed".
A public read-only mirror of ''NetHack'' git
Git () is a distributed version control system: tracking changes in any set of files, usually used for coordinating work among programmers collaboratively developing source code during software development. Its goals include speed, data in ...
repository was made available on 10 February 2016. Since v3.6.0, the DevTeam has continued to push updates to the title, with the latest being v3.6.6 on 8 March 2020. Version 3.7.0 is currently in development.
, the official source release supports the following systems: Windows
Windows is a group of several proprietary graphical operating system families developed and marketed by Microsoft. Each family caters to a certain sector of the computing industry. For example, Windows NT for consumers, Windows Server for se ...
, Linux
Linux ( or ) is a family of open-source Unix-like operating systems based on the Linux kernel, an operating system kernel first released on September 17, 1991, by Linus Torvalds. Linux is typically packaged as a Linux distribution, whi ...
, macOS
macOS (; previously OS X and originally Mac OS X) is a Unix operating system developed and marketed by Apple Inc. since 2001. It is the primary operating system for Apple's Mac computers. Within the market of desktop and la ...
, Windows CE
Windows Embedded Compact, formerly Windows Embedded CE, Windows Powered and Windows CE, is an operating system subfamily developed by Microsoft as part of its Windows Embedded family of products.
Unlike Windows Embedded Standard, which is base ...
, OS/2
OS/2 (Operating System/2) is a series of computer operating systems, initially created by Microsoft and IBM under the leadership of IBM software designer Ed Iacobucci. As a result of a feud between the two companies over how to position OS/2 r ...
, Unix
Unix (; trademarked as UNIX) is a family of multitasking, multiuser computer operating systems that derive from the original AT&T Unix, whose development started in 1969 at the Bell Labs research center by Ken Thompson, Dennis Ritchie, ...
( BSD, System V
Unix System V (pronounced: "System Five") is one of the first commercial versions of the Unix operating system. It was originally developed by AT&T and first released in 1983. Four major versions of System V were released, numbered 1, 2, 3, an ...
, Solaris, HP-UX
HP-UX (from "Hewlett Packard Unix") is Hewlett Packard Enterprise's proprietary implementation of the Unix operating system, based on Unix System V (initially System III) and first released in 1984. Current versions support HPE Integrity Se ...
), BeOS
BeOS is an operating system for personal computers first developed by Be Inc. in 1990. It was first written to run on BeBox hardware.
BeOS was positioned as a multimedia platform that could be used by a substantial population of desktop users an ...
, and VMS.
Licensing, ports, and derivative ports
''NetHack'' is released under the NetHack General Public License, which was written in 1989 by Mike Stephenson, patterned after theGNU bison
GNU Bison, commonly known as Bison, is a parser generator that is part of the GNU Project. Bison reads a specification in the BNF notation (a context-free language), warns about any parsing ambiguities, and generates a parser that reads sequen ...
license (which was written by Richard Stallman
Richard Matthew Stallman (; born March 16, 1953), also known by his initials, rms, is an American free software movement activist and programmer. He campaigns for software to be distributed in such a manner that its users have the freedom to ...
in 1988). Like the Bison license, and Stallman's later GNU General Public License
The GNU General Public License (GNU GPL or simply GPL) is a series of widely used free software licenses that guarantee end users the four freedoms to run, study, share, and modify the software. The license was the first copyleft for general ...
, the ''NetHack'' license was written to allow the free sharing and modification of the source code
In computing, source code, or simply code, is any collection of code, with or without comments, written using a human-readable programming language, usually as plain text. The source code of a program is specially designed to facilitate the ...
under its protection. At the same time, the license explicitly states that the source code is not covered by any warranty
In contract law, a warranty is a promise which is not a condition of the contract or an innominate term: (1) it is a term "not going to the root of the contract",Hogg M. (2011). ''Promises and Contract Law: Comparative Perspectives''p. 48 Cambri ...
, thus protecting the original authors from litigation
-
A lawsuit is a proceeding by a party or parties against another in the civil court of law. The archaic term "suit in law" is found in only a small number of laws still in effect today. The term "lawsuit" is used in reference to a civil act ...
. The NetHack General Public License is a copyleft
Copyleft is the legal technique of granting certain freedoms over copies of copyrighted works with the requirement that the same rights be preserved in derivative works. In this sense, ''freedoms'' refers to the use of the work for any purpose ...
software license
A software license is a legal instrument (usually by way of contract law, with or without printed material) governing the use or redistribution of software. Under United States copyright law, all software is copyright protected, in both sourc ...
certified as an open source license
An open-source license is a type of license for computer software and other products that allows the source code, blueprint or design to be used, modified and/or shared under defined terms and conditions. This allows end users and commercial comp ...
by the Open Source Initiative
The Open Source Initiative (OSI) is the steward of the Open Source Definition, the set of rules that define open source software. It is a California public-benefit nonprofit corporation, with 501(c)(3) tax-exempt status.
The organization wa ...
.
The NetHack General Public License allows anyone to port
A port is a maritime facility comprising one or more wharves or loading areas, where ships load and discharge cargo and passengers. Although usually situated on a sea coast or estuary, ports can also be found far inland, such as H ...
the game to a platform not supported by the official DevTeam, provided that they use the same license. Over the years this licensing has led to a large number of ports and internationalized versions in German, Japanese, and Spanish. The license also allows for software forks as long as they are distributed under the same license, except that the creator of a derivative work is allowed to offer warranty protection on the new work. The derivative work is required to indicate the modifications made and the dates of changes. In addition, the source code of the derivative work must be made available, free of charge except for nominal distribution fees. This has also allowed source code forks of ''NetHack'' including ''Slash'EM
''Slash'EM'' (''Super Lotsa Added Stuff Hack – Extended Magic'') is a variant of the roguelike game ''NetHack'' that offers extra features, monsters, and items. Several of its novel features, such as the Monk class, "conducts" (voluntary ch ...
'', ''UnNetHack'', and ''dNethack''.
Online support
Bugs, humorous messages, stories, experiences, and ideas for the next version are discussed on theUsenet
Usenet () is a worldwide distributed discussion system available on computers. It was developed from the general-purpose Unix-to-Unix Copy (UUCP) dial-up network architecture. Tom Truscott and Jim Ellis conceived the idea in 1979, and it wa ...
newsgroup
A Usenet newsgroup is a repository usually within the Usenet system, for messages posted from users in different locations using the Internet. They are discussion groups and are not devoted to publishing news. Newsgroups are technically disti ...
rec.games.roguelike.nethack.
A public server at nethack.alt.org, commonly known as "NAO", gives players access to NetHack through a Telnet
Telnet is an application protocol used on the Internet or local area network to provide a bidirectional interactive text-oriented communication facility using a virtual terminal connection. User data is interspersed in-band with Telnet control i ...
or SSH interface. A browser-based client is also available on the same site. Ebonhack connects to NAO with a graphical tiles-based interface.
During the whole month of November, the annual /dev/null NetHack Tournament took place every year from 1999 to 2016. The November NetHack Tournament, initially conceived as a one-time tribute to devnull, has taken place each year since 2018. The Junethack Cross-Variant Summer Tournament has taken place annually since 2011.
NetHack Learning Environment
TheFacebook
Facebook is an online social media and social networking service owned by American company Meta Platforms. Founded in 2004 by Mark Zuckerberg with fellow Harvard College students and roommates Eduardo Saverin, Andrew McCollum, Dust ...
artificial intelligence
Artificial intelligence (AI) is intelligence—perceiving, synthesizing, and inferring information—demonstrated by machines, as opposed to intelligence displayed by animals and humans. Example tasks in which this is done include speech ...
(AI) research team, along with researchers at the University of Oxford
, mottoeng = The Lord is my light
, established =
, endowment = £6.1 billion (including colleges) (2019)
, budget = £2.145 billion (2019–20)
, chancellor ...
, New York University
New York University (NYU) is a private research university in New York City. Chartered in 1831 by the New York State Legislature, NYU was founded by a group of New Yorkers led by then- Secretary of the Treasury Albert Gallatin.
In 1832, th ...
, the Imperial College London
Imperial College London (legally Imperial College of Science, Technology and Medicine) is a public research university in London, United Kingdom. Its history began with Prince Albert, consort of Queen Victoria, who developed his vision for a cu ...
, and University College London
, mottoeng = Let all come who by merit deserve the most reward
, established =
, type = Public research university
, endowment = £143 million (2020)
, budget = ...
, developed an open-source platform called the NetHack Learning Environment, designed to teach AI agents to play ''NetHack''. The base environment is able to maneuver the agent and fight its way through dungeons, but the team seeks community help to build an AI on the complexities of ''NetHack'' interconnected systems, using implicit knowledge that comes from player-made resources, thus giving a means for programmers to hook into the environment with additional resources. Facebook's research led the company to pose ''NetHack'' as a grand challenge in AI in June 2021, in part due to the game's permadeath and inability to experiment with the environment without creating a reaction. The competition at the 2021 Conference on Neural Information Processing Systems
The Conference and Workshop on Neural Information Processing Systems (abbreviated as NeurIPS and formerly NIPS) is a machine learning and computational neuroscience conference held every December. The conference is currently a double-track meet ...
involved agents of various designs attempting to ascend. None of the agents managed this; the results were ranked by median in-game score, with the highest-ranked agent (Team AutoAscend) using a symbolic (non-machine-learning) design.
Legacy
''Nethack'' will be part of the video game exhibit "Never Alone", in theMuseum of Modern Art
The Museum of Modern Art (MoMA) is an art museum located in Midtown Manhattan, New York City, on 53rd Street between Fifth and Sixth Avenues.
It plays a major role in developing and collecting modern art, and is often identified as one of t ...
's collection, set to run from September 2022 to mid-2023.
See also
*List of open-source video games
This is a list of notable open-source video games. Open-source video games are assembled from and are themselves open-source software, including public domain games with public domain source code. This list also includes games in which the engine ...
* List of roguelikes
This is a selected list of roguelike video games. Roguelike games are those that incorporate elements of role-playing games with procedural generation, following the formula of the genre's namesake, '' Rogue''. Due to the large number of variat ...
References
*Citations
External links
* *A Guide to the Mazes of Menace (Guidebook for ''NetHack'')
*
*
The NetHack Wiki
NAO website
/dev/null NetHack Tournament
* *
''NetHack''
at SourceForge.net
Hall of Fame – ''NetHack''
at
GameSpy
GameSpy was an American provider of online multiplayer and matchmaking middleware for video games founded in 1996 by Mark Surfas. After the release of a multiplayer server browser for the game, QSpy, Surfas licensed the software under the Ga ...
{{DEFAULTSORT:Nethack
1987 video games
Acorn Archimedes games
Amiga games
Android (operating system) games
Atari ST games
Cross-platform software
Fantasy video games
Free and open-source Android software
Games with concealed rules
GP2X games
Linux games
Classic Mac OS games
Open-source video games
MacOS games
Roguelike video games
Role-playing video games
Video games with textual graphics
Windows games
Video games using procedural generation