Cheating in online games on:
[Wikipedia]
[Google]
[Amazon]
 Cheating in online games is the subversion of the rules or mechanics of online video games to gain an unfair advantage over other players, generally with the use of third-party software. What constitutes cheating is dependent on the game in question, its rules, and consensus opinion as to whether a particular activity is considered to be cheating.
Cheating is present in most
Cheating in online games is the subversion of the rules or mechanics of online video games to gain an unfair advantage over other players, generally with the use of third-party software. What constitutes cheating is dependent on the game in question, its rules, and consensus opinion as to whether a particular activity is considered to be cheating.
Cheating is present in most
Aspects of Networking in Multiplayer Computer Games
by J.Smed ''et al.'', The Electronic Library, volume 20, number 2, pages 87–97, 2002.
Fair Online Gaming
Information on Intel's anti-cheat research initiative and technology. {{DEFAULTSORT:Cheating In Online Games Cheating in video games, Esports techniques Video game controversies Online games
 Cheating in online games is the subversion of the rules or mechanics of online video games to gain an unfair advantage over other players, generally with the use of third-party software. What constitutes cheating is dependent on the game in question, its rules, and consensus opinion as to whether a particular activity is considered to be cheating.
Cheating is present in most
Cheating in online games is the subversion of the rules or mechanics of online video games to gain an unfair advantage over other players, generally with the use of third-party software. What constitutes cheating is dependent on the game in question, its rules, and consensus opinion as to whether a particular activity is considered to be cheating.
Cheating is present in most multiplayer
A multiplayer video game is a video game in which more than one person can play in the same game environment at the same time, either locally on the same computing system ( couch co-op), on different computing systems via a local area network, or ...
online games, but it is difficult to measure. Various methods of cheating in online games can take the form of software assistance, such as scripts and bots, and various forms of unsporting play taking advantage of exploits within the game. The Internet and darknets can provide players with the methodology necessary to cheat in online games, with software often available for purchase.
As methods of cheating have advanced, video game publishers have similarly increased methods of anti-cheating, but are still limited in their effectiveness. Punishments for cheaters also have various forms, with legal measures also being taken against those who create or use cheats. While some countries include laws that prohibit and punish cheating, video game companies have a history of citing copyright infringement in lawsuits against cheaters.
Bots and software assistance
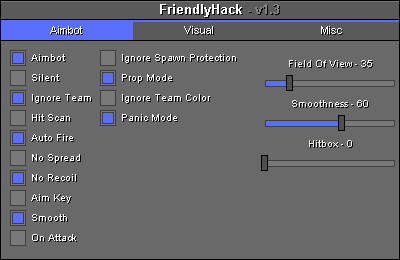
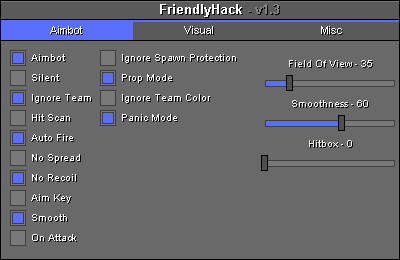
Aimbots and triggerbots
An aimbot or autoaim is a type ofcomputer game bot
In video games, a bot is a type of artificial intelligence (AI)–based expert system software that plays a video game in the place of a human. Bots are used in a variety of video game genres for a variety of tasks: a bot written for a first- ...
most commonly used in first-person shooter
First-person shooter (FPS) is a sub-genre of shooter video games centered on gun and other weapon-based combat in a first-person perspective, with the player experiencing the action through the eyes of the protagonist and controlling the p ...
games to provide varying levels of automated target acquisition
Target acquisition is the detection and identification of the location of a target in sufficient detail to permit the effective employment of lethal and non-lethal means. The term is used for a broad area of applications.
A "target" here is an e ...
and calibration
In measurement technology and metrology, calibration is the comparison of measurement values delivered by a device under test with those of a calibration standard of known accuracy. Such a standard could be another measurement device of kno ...
to the player. They are sometimes used along with a triggerbot, which automatically shoots when an opponent appears within the field-of-view or aiming reticule of the player.
Aimbotting relies on each player's client computer receiving information about all other players, whether they are visible from the player's position or not. Targeting is a matter of determining the location of any opponent relative to the player's location and pointing the player's weapon at the target. This targeting works regardless of whether the opponent is behind walls or too far away to be seen directly.
Some servers allow inactive players to spectate, watching the game from the viewpoints of the active players. Recording of gameplay actions is also often possible. If someone was using a targeting aimbot, the bot would be obvious to the spectator as unnatural exact position tracking. Some aimbots and triggerbots attempt to hide from spectators the fact they are being used through a number of methods, such as delaying firing to hide the fact it shoots the instant an opponent is in the cheater's crosshair. Some triggerbot programs can be easily toggled on and off using the mouse or keyboard.
Cheat suites may incorporate these in addition to other features, including adjustments to extrasensory perception, move speed, ammo count, and player radar. Neophytes may colloquially define these suites as aimbot programs.
Artificial lag/lag switch
In the peer-to-peer gaming model, lagging is what happens when the stream of data between one or more players gets slowed or interrupted, causing movement to stutter and making opponents appear to behave erratically. By using a lag switch, a player is able to disrupt uploads from the client to the server, while their own client queues up the actions performed. The goal is to gain advantage over another player without reciprocation; opponents slow down or stop moving, allowing the lag switch user to easily outmaneuver them. From the opponent's perspective, the player using the device may appear to be teleporting, invisible or invincible, while the opponents suffer delayed animations and fast-forwarded game play, delivered in bursts. Some gaming communities refer to this method as "tapping" which refers to the users "tapping" on and off their internet connection to create the lag. The term "lag switch" encompasses many methods of disrupting the network communication between a client and its server. One method is by attaching a physical device, called a hardware lag switch, to a standard Ethernet cable. By flipping the switch on and off, the physical connection between the client and the server is disrupted. The designers ofvideo game console
A video game console is an electronic device that outputs a video signal or image to display a video game that can be played with a game controller. These may be home consoles, which are generally placed in a permanent location connected to ...
hardware have started to introduce built-in protection against lag switches in the form of voltage detectors, which detect a change in voltage when the switch is flipped. Some manufacturers have taken counter measures to bypass or trick this detector. This can also be achieved by simply unplugging the Ethernet cord going to the client, causing a disruption in the player's internet connection. Other methods, called a software or wireless lag switch, involve using a computer program. In this method, the cheater runs an application on a computer connected to the same network as the client. The application hogs the network bandwidth, disrupting the communication between the client and its server. However, one cannot do this for an unlimited amount of time. At some point, if no traffic is being received, most game clients and/or game servers will decide that the connection has been lost and will remove the player from the game. In some P2P games, it can result in all players lagging or being disconnected from the game.
Simpler methods are firewall or router rules that apply bandwidth shaping and network latency, a cheat is able to adjust limits on both bandwidth and latency to stay relevant to a P2P network yet have considerable advantage over other players.
Look-ahead
Look-ahead cheating is a method of cheating within a peer-to-peer multiplayer gaming architecture where the cheating client gains an unfair advantage by delaying their actions to see what other players do before announcing its own action. A client can cheat using this method by acting as if it is suffering from high latency; the outgoing packet is forged by attaching a time-stamp that is prior to the actual moment the packet is sent, thereby fooling other clients into thinking that the action was sent at the correct time, but was delayed in arrival. A partial solution is thelockstep protocol
The lockstep protocol is a ''partial'' solution to the look-ahead cheating problem in peer-to-peer architecture multiplayer games, in which a cheating client delays their own actions to await the messages of other players. A client can do so b ...
.
World-hacking
World-hacking is a method or third-party program that enables a user to exploit bugs and to view more of a level than intended by thedeveloper
Developer may refer to:
Computers
* Software developer, a person or organization who develop programs/applications
* Video game developer, a person or business involved in video game development, the process of designing and creating games
* Web d ...
.
A common aspect of real-time strategy
Real-time strategy (RTS) is a subgenre of strategy video games that do not progress incrementally in turns, but allow all players to play simultaneously, in "real time". By contrast, in turn-based strategy (TBS) games, players take turns to p ...
games is the player's partial limitation or complete inability to see beyond the visibility range of individual game objects that are under their ownership (typically units and structures); this concept is controlled by a mechanism known as the fog of war
The fog of war (german: links=no, Nebel des Krieges) is the uncertainty in situational awareness experienced by participants in military operations. The term seeks to capture the uncertainty regarding one's own capability, adversary capability, ...
. World-hacking usually enables the user to bypass this mechanism, either by removing it entirely and/or by rendering objects through the fog that would not normally be visible. In multiplayer modes, this allows for a distinct advantage against the other players who are subject to the intended settings. The advantage gained can be substantial, especially for the average real-time strategy games that rely on the rock paper scissors
Rock paper scissors (also known by other orderings of the three items, with "rock" sometimes being called "stone," or as Rochambeau, roshambo, or ro-sham-bo) is a hand game originating in China, usually played between two people, in which each p ...
dynamic to balance
Balance or balancing may refer to:
Common meanings
* Balance (ability) in biomechanics
* Balance (accounting)
* Balance or weighing scale
* Balance as in equality or equilibrium
Arts and entertainment Film
* ''Balance'' (1983 film), a Bulgaria ...
out individual objects' varying strengths and weaknesses.
World-hacking may also allow a player to see through solid or opaque objects and/or manipulate or remove textures, to know in advance when an opponent is about to come into targeting range from an occluded area. This can be done by making wall textures transparent, or modifying the game maps to insert polygonal holes into otherwise solid walls. This variation is commonly known as a "wallhack" since it basically allows to the player to see enemies through walls.
World-hacking relies on the fact that an FPS server usually sends raw positional information for all players in the game, and leaves it up to the client's 3D renderer to hide opponents behind walls, in plant foliage, or in dark shadows. If the game map rendering could be turned off completely, all players could be seen moving around in what appears to be empty space. Complete map hiding offers no advantage to a cheater as they would be unable to navigate the invisible map pathways and obstacles. However, if only certain surfaces are made transparent or removed, this leaves just enough of an outline of the world to allow the cheater still to navigate it easily.
Asus released wireframe display drivers in 2001 that enabled players to use wallhacks, announcing the settings as "special weapons" that users could employ in multiplayer games. In a poll by the Online Gamers Association
In computer technology and telecommunications, online indicates a state of connectivity and offline indicates a disconnected state. In modern terminology, this usually refers to an Internet connection, but (especially when expressed "on line" or ...
, 90% of its members were against the release of the drivers.
Unsporting play
Boosting / Win trading
Players will set up multiple accounts to play against each other. Usually, the primary account will be allowed to win through a deliberate lack of resistance from the secondary account(s) due to those accounts being unplayed or those players agreeing to lose. Some players will reverse roles between games, giving each account an equal win–loss record.Disconnecting
In games where wins and losses are recorded on a player's account, a player may disconnect when he or she is about to lose in order to prevent that loss from being recorded. This is usually done by activating known in-game glitches or through third-party sources via "IP booting" (a feature of firewall software). Some players do this if they feel their opponent is being unfair. Some games implement a disconnection penalty, usually by recording the disconnect as a loss, a deduction of experience, or even Elo points. Certain games also have a 'disconnect delay' period before the player can disconnect that can last 10–30 seconds. This prevents a player from instantly disconnecting if they are about to die or lose. In some games, if a player disconnects they can receive a warning or even get locked out of online play for a short period.Rapid Fire Modifications (Macros)
In many games, weapons can be fired in burst fire or single shot fire modes. Modifying a controller or keyboard/mouse to gain the advantage of having a faster firing weapon than the standard player can be considered a method of cheating. These modifications can create an imbalance within the game. In addition to modifying a console or its controller, it is possible to achieve a similar effect on the PC by binding the firing button to the scroll wheel of a mouse, or by using a macro setting that will simulate rapid key presses automatically. However, most games limit the rate at which weapons can be fired, regardless of how fast a player presses the button, in order to limit this form of cheating.Exploits
Exploiting is the application of an unintended feature or bug that gives the player an advantage not intended by the game design. Exploiting is generally considered cheating by the gaming community at large due to the unfair advantage usually gained by the exploiter. Most software developers of online games prohibit exploiting in their terms of service and often issue sanctions against players found to be exploiting. There is some contention by exploiters that exploiting should not be considered cheating as it is merely taking advantage of actions allowed by the software. Some players view exploiting as a skill because certain exploits take a significant amount of time to find, or dexterity and timing to use.Farming
The term farming may refer to the practice of garnering achievements or virtual property for the purpose of real-money-trading. With rare exception, this has no direct effect on the gaming experience of other players; instead, it is a violation of most EULAs and could devalue the virtual property being farmed.Twinking
Twinking is the act of transferring gear intended for higher level characters to lower level characters that would be incapable of obtaining the gear on their own. Twinked characters have a huge advantage over untwinked characters, as well as the rest of the game world. This is usually used by players who wish to create a new character, either to help them level more rapidly or to gain an unfair advantage in PvP (''i.e.'' player versus player, a type of multiplayer interactive conflict). Most MMORPGs tolerate it, provided that the twinked character is not used in PvP combat against non-twinked characters. Often limits on twinking are placed into the game, usually through strict level or stat requirements to equip the item. Circumventing these level requirements would then be further cheating.Ghosting
Most games allow other participants to observe the game as it is played from a variety of perspectives; depending on the game, perspectives allow an observer a map overview or attach a "camera" to the movement of a specific player. In doing so, the observer can communicate with an accomplice using a secondary communication methodology (in-gameprivate message
In computing, a private message, personal message, or direct message (abbreviated as PM or DM) refers to a private communication sent or received by a user of a private communication channel on any given platform. Unlike public posts, PMs are only ...
, third party communication, or even off-line) to inform friendly players of traps or the position of opponents. An observer can be an active player, using a separate computer, connection and account.
Some systems prevent inactive players from observing the game if they are on the same IP address
An Internet Protocol address (IP address) is a numerical label such as that is connected to a computer network that uses the Internet Protocol for communication.. Updated by . An IP address serves two main functions: network interface ident ...
as an active player, on the grounds that they are probably in close physical proximity; when all players from a single IP address are no longer active participants, they are all allowed to observe. However, this restriction can be easily evaded if there are multiple IP addresses available at one location (a common feature of broadband subscriptions), or if the observer installs remote desktop software
In computing, the term remote desktop refers to a software- or operating system feature that allows a personal computer's desktop environment to be run remotely off of one system (usually a PC, but the concept applies equally to a server or a ...
on their computer, thus enabling their computer screen to be viewed by select other players in real time.
Additionally, this may be used against players livestreaming to platforms like Twitch
Twitch may refer to:
Biology
* Muscle contraction
** Convulsion, rapid and repeated muscle contraction and relaxation
** Fasciculation, a small, local, involuntary muscle contraction
** Myoclonic twitch, a jerk usually caused by sudden muscle co ...
to observe the player and their team's position and stats. This is often referred to as stream sniping.
Stacking
Stacking involves altering game settings or team lineups to give one or more teams an unfair advantage over others. One example includes arranging a team composed of skilled or professional players against a team with members of lesser skill. Less ethical rigging involves weighting the game by providing a player or team with an advantage by outfitting them with better (or more familiar) weapons or equipment, or creating a play field that caters to a certain player, team or playing style. Many games prevent this by preventing players from joining a team with more players than the opposing side, forcing newcomers to balance the teams.Scripting
Scripting is the use of a program or game feature to automate certain actions or behaviors. The use of scripts may or may not be considered cheating, depending on the behavior involved, and whether said behaviour is replicable without the use of such script. A script may give the user unusually fast firing rate, unobtainable otherwise, or may perform seemingly trivial tasks such as reloading. Some scripts can also tamper with other players' systems by spoofing commands.Implementation of cheats
In theclient–server model
The client–server model is a distributed application structure that partitions tasks or workloads between the providers of a resource or service, called servers, and service requesters, called clients. Often clients and servers communicate ove ...
, the server is responsible for information security and enforcing game rules. (See " Anti-cheating methods and limitations" below for drawbacks.) In the peer-to-peer
Peer-to-peer (P2P) computing or networking is a distributed application architecture that partitions tasks or workloads between peers. Peers are equally privileged, equipotent participants in the network. They are said to form a peer-to-peer ...
gaming model, clients run equal code but are still subject to most of the same type of cheats found in the client–server multiplayer model; however, the peer-to-peer multiplayer model has been deprecated in favor of the client–server model with the wider adoption of high-speed networks.
"Never trust the client" is a maxim among game developers (as well as other developers) that summarizes the model of client–server game design. It means that no information sent from a client should be accepted by a server if it breaks the game rules or the basic mechanics of the game, and that no information should be sent to a client unless it is "need-to-know." For example, a server with no rule enforcement or data integrity checking will synchronize all of the clients with all of the information about all of the other clients. The server will be very fast, but any wallhack program will reveal where all the players in the game are, what team they are on, and what state they're in — health, weapon, ammo etc. At the same time, altered and erroneous data from a client will allow a player to break the game rules, manipulate the server, and even manipulate other clients.
Game code modification
Many cheats are implemented by modifying game software, despite EULAs which forbid modification. While game software distributed in binary-only versions makes it harder to modify code, reverse engineering is possible. Also game data files can be edited separately from the main program and thereby circumvent protections implemented in software.System software modification
Rather than modifying the game code (which the game itself or a 3rd-party protection system may detect), some cheats modify underlying system components. An example of this is graphics driver modifications that ignore depth checking and draw all objects on the screen—a primitive wallhack. System or driver modification is harder to detect, as there are a large number of system drivers that differ from user to user.Packet interception and manipulation
The security of game software can be circumvented by intercepting and/or manipulating data (divided into " packets") in real-time while in transit from the client to the server or vice versa (i.e. aman-in-the-middle attack
In cryptography and computer security, a man-in-the-middle, monster-in-the-middle, machine-in-the-middle, monkey-in-the-middle, meddler-in-the-middle, manipulator-in-the-middle (MITM), person-in-the-middle (PITM) or adversary-in-the-middle (AiTM) ...
). Interception can be passive or result in active manipulation; either method can be performed on the client machine itself or via an external communication proxy; some aimbot
Cheating in online games is the subversion of the rules or mechanics of online video games to gain an unfair advantage over other players, generally with the use of third-party software. What constitutes cheating is dependent on the game in ...
s incorporate this method.
Anti-cheating methods and limitations
There are many facets of cheating in online games which make the creation of a system to stop cheating very difficult; however, game developers and third-party software developers have created or are developing technologies that attempt to prevent cheating. Such countermeasures are commonly used in video games, with notable anti-cheat software beingBattlEye
BattlEye is a Proprietary software, proprietary anti-cheat software system which protects games and their players from hacking, cheating, and other forms of exploits while playing an online game. It was initially released as a third-party anti-che ...
, GameGuard, PunkBuster
PunkBuster is a computer program that is designed to detect software used for cheating in online games. It does this by scanning the memory contents of the local machine. A computer identified as using cheats may be banned from connecting to pro ...
, Valve Anti-Cheat
Valve Anti-Cheat (VAC) is an anti-cheat software product developed by Valve as a component of the Steam platform, first released with ''Counter-Strike'' in 2002.
When the software detects a cheat on a player's system, it will ban them in the f ...
(specifically used on games on the Steam platform), and EasyAntiCheat.
Exploits of bugs are usually resolved/removed via a patch to the game; however, not all companies force the patches/updates on users, leaving the actual resolution to individual users.
Authoritative and mirrored server design
Generally, the better the server is at enforcing the rules, the less of a problem cheating will be in the game. In this approach all client functionality either runs purely on the game server or alternatively the game server mirrors the client gameplay and continuously validates the game state. In many mobile games, it is a common practice to run the client game sessions synchronously on the server, using exactly the same user input. The client session is reset when the game sessions become unsynced, thereby preventing cheating. Server-side game code makes a trade-off between calculating and sending results for display on a just-in-time basis or trusting the client to calculate and display the results in appropriate sequence as a player progresses. It can do this by sending the parts of the world state needed for immediate display, which can result in client ''lag'' under bandwidth constraints, or sending the player the entire world state, which results in faster display for the player under the same bandwidth constraints, but exposes that data to interception or manipulation—a trade-off between security and efficiency. When game servers were restricted by limited available resources such as storage, memory, internal bandwidth, and computational capacity due to the technologies available and the cost of the hardware, coupled with internet connections that were slow, it was believed to be necessary to compromise on security for optimization to minimize the impact on the end-user. Today however, with the increased speed and power of multi-core computers, lower-priced hardware, and the increased availability of broadband internet, this has become less of an issue.Software obfuscation
Additionally to storing data in non-standard formats, some games also utilize runtime protection through software protectors. The key target is to keep attackers from directly inspecting or modifying compiled software. Protectors utilize any of three methods to protect software. Encryption solutions will encrypt the code instructions and typically use a multi–layered defense mechanism against any reversing or tampering attempts that target the decryption code directly. Most protection systems in this category encrypt the code and then decrypt it at the application's startup or during runtime. This is the moment at which an attacker will breakpoint, reverse, and inject custom code. Runtime decryption may also add significant processing overhead and lower the game's framerate. Alternatively, some solutions focus on obfuscating the code by inserting jump statements and seemingly random instruction paths. The final and strongest alternative is virtualization. In this approach the encrypted code runs on a virtual CPU that can be markedly different from generic x86 and x64 CPUs as the command set can be unique for each protected file. The shared weakness of protectors and virtualizers is that they impact performance, either by requiring decryption or by introducing unnecessary CPU instructions. To reduce the overhead code virtualizers are often only used to secure the critical parts of the code base, such as those interfacing with the gamestate and rendering.Player supervision
Spectator functionality can allow server administrators to monitor individual players and thereby determine whether or not a cheat is in place. One risk of the spectator mode is that in competitive matches the spectator could abuse the mode for spying on specific players and communicating player positions and tactics to the opposing team. Some games get around this limitation by not allowing spectator mode at all, or by delaying the video feed. Some games have systemized player supervision by allowing the community to review reports of disruptive behavior, determine whether those reports are valid, and apply temporary bans if appropriate. Reports can include data such as screenshots, videos, and chatlogs.Anomaly detection
Anomalies in player behavior can be detected by statistically analyzing game events sent by the client to the server. The benefit is that this anti–cheat method is non–intrusive to the player's privacy and guaranteed to work on all end–user system configurations. The restriction of this method is that it cannot always be clear whether or not a player is cheating. Highly skilled players can for example develop such a map sense that they may end up being flagged for the use of a wallhack and/or aimbot. On the other hand, players may also cheat in a way that is under the detection thresholds and remain uncaught. To reduce the amount of false positives, statistical detection systems are often combined with a supervision system that either is community driven or managed by a professional administrator team. In such implementations unusual player behavior can trigger a client-side component to create and upload reports for review.Pattern detection
Pattern detection systems scan the player's hard drives and system memory for known cheat code or programs. Compared to statistical detection the key advantage is that also the subtle cheaters are detected. Other than this, a pure pattern detection approach generally has few advantages. Experience has shown that keeping detection-based systems up to date is relatively slow and labor-intensive as one needs to constantly track down cheats and update detection patterns. End–users may also be concerned with privacy issues, such as has been the case with VAC (Valve Anti-Cheat) accessing browsing history.Sandboxing
Sandboxing a software process can protect against potentially malicious actions such as code injection and memory modifications that would otherwise tamper with the game. One of the key benefits of sandboxing is that it can effectively prevent the underlying cheat mechanisms from working, and thereby can avoid the need for banning game community members as cheats simply don't work. Additionally, strong prevention mechanisms can stop many game hackers from targeting the game because of elevated skill requirements. Compared to pattern detection systems, sandboxing is generally not privacy invasive, as the approach requires no data to be uploaded to foreign back-end systems.System incompatibility
Anti-cheat software commonly use low-level system interfaces not intended by the OS vendor for public use. As a result, they are a common source of incompatibilities with newer versions ofoperating system
An operating system (OS) is system software that manages computer hardware, software resources, and provides common services for computer programs.
Time-sharing operating systems schedule tasks for efficient use of the system and may also i ...
s and security measures as well as alternative OS API implementations such as Wine
Wine is an alcoholic drink typically made from fermented grapes. Yeast consumes the sugar in the grapes and converts it to ethanol and carbon dioxide, releasing heat in the process. Different varieties of grapes and strains of yeasts are m ...
. For example, Windows enables Hypervisor-protected Code Integrity (HVCI) by default in every market except Chinese and Korean installations due to anti-cheat compatibility issues.
Penalties for cheating
Game publishers can implement a wide array of consequences for cheating players.Banning players
Some game publishers may decide to try to permanently ban players who are persistent in cheating and ruining the game community. Such bans are typically placed based on hardware ID or IP address. Consequently, cheaters may develop ways of getting around these bans, by either playing through proxy or VPN servers, or spoofing or changing their hardware configuration. Some companies and leagues ban suspected cheaters by blacklisting specific installation or serial keys, or user accounts, meaning that the player is effectively prevented from playing the game online. Certain games are known to identify cheaters and " shadow ban" them by placing them in matchmaking with other cheaters only, so as not to let the cheaters know that they have been identified. While game publishers are known to ban players employing cheats, the actual number of players banned is usually not revealed. Exceptions to this includeBlizzard Entertainment
Blizzard Entertainment, Inc. is an American video game developer and publisher based in Irvine, California. A subsidiary of Activision Blizzard, the company was founded on February 8, 1991, under the name Silicon & Synapse, Inc. by three gradu ...
, Nexon
Nexon Co., Ltd. is a global video game publisher, listed in Japan, that specializes in online Virtual World games for PCs, consoles and mobile. Nexon is one of the world’s ten largest interactive game companies based on market capitalization a ...
, and CipSoft
CipSoft GmbH is a German video game developer based in Regensburg. Founded in 2001, it is the developer of ''Tibia''. As of January 2023, the company employs 95 people.
History
CipSoft was founded on 8 June 2001 by Guido Lübke, Stephan Payer ...
, known for banning cheaters in batches, and publicising the number of banned accounts, presumably in order to discourage others from cheating.
Suspension
In some cases a ban may not be permanent and will expire after a certain period of time. Suspensions are commonly used as a punitive measure for abuse of game glitches, harassing players, or benefiting from hacks. Temporary bans may also be utilized in case a violation cannot be fully proven, as is common with anti-cheating methods based on supervision or statistical detection.In-game kick
In general kicking is perceived as a mild punishment, serving as a warning for the player in question. Some anti-cheat systems may decide to kick players out of a game server when the system integrity cannot be enforced nor be determined with certainty. Other anti-cheat methods may also utilize kicks as an instant punishment for presumably unfair game play behavior. Some games may also provide the community with the option of voting for particular players to be kicked. Such a system provides the power to self-regulate and effectively get rid of abusive players without depending on supervision or other anti-cheat methods. Even though vote kicking brings many benefits, it may also serve as a tool for trolling orgriefing
A griefer or bad-faith player is a player in a multiplayer video game who deliberately irritates and harasses other players within the game ( trolling), by using aspects of the game in unintended ways such as destroying something another player ...
by allowing for legitimate players to be removed out of the game through the voting process.
Demotion
When a violation is the result of farming or stat-padding, it may be too severe of a punishment to suspend or ban players. Some games, therefore, implement a system of demotion in which the offender is moved to a lower rank (demoting), the opposite of a promotion.Progress-removal
In several games where points are used, if a player is caught cheating they will get their score reset to the base value that is applied when a new player joins the server.Legal measures
In recent years, countries including South Korea and China have criminalized the sale or use of cheats in video games. In South Korea, cheaters could be punished with up to 5 years in jail or fines exceeding $40,000. The presence of cheaters in online games may push away the legitimate playerbase and reduce overall profits in the industry, leading to game developers working with legislative bodies or enforcement agencies. Historically, some game companies have also taken legal measures against individuals that have created and sold cheating tools in video games as a means to curb their use. Anti-cheat experts have argued that it is particularly important to take legal steps against entities who profit from making and selling cheats. In April 2013, coder DrUnKeN ChEeTaH was sued byNexon America
Nexon Co., Ltd. is a global video game publisher, listed in Japan, that specializes in online Virtual World games for PCs, consoles and mobile. Nexon is one of the world’s ten largest interactive game companies based on market capitalization a ...
for operating GameAnarchy, a popular subscription based cheat provider for ''Combat Arms
Combat arms (or fighting arms in non-American parlance) are troops within national armed forces who participate in direct tactical ground combat. In general, they are units that carry or employ weapons, such as infantry, cavalry, and artillery ...
'', and lost, Nexon being awarded $1.4M in damages. In January 2017, Riot Games successfully sued the LeagueSharp service, which offered a subscription-based hacking service for Riot's ''League of Legends
''League of Legends'' (''LoL''), commonly referred to as ''League'', is a 2009 multiplayer online battle arena video game developed and published by Riot Games. Inspired by '' Defense of the Ancients'', a custom map for ''Warcraft III'', ...
'', with a $10 million award to be paid to Riot. Blizzard Entertainment
Blizzard Entertainment, Inc. is an American video game developer and publisher based in Irvine, California. A subsidiary of Activision Blizzard, the company was founded on February 8, 1991, under the name Silicon & Synapse, Inc. by three gradu ...
sued Bossland GMBH for distributing software hacks for several of its games, and was awarded $8.5 million in damages. Epic Games, producers of the battle royale game ''Fortnite
''Fortnite'' is an online video game developed by Epic Games and released in 2017. It is available in three distinct game mode versions that otherwise share the same general gameplay and game engine: ''Fortnite Battle Royale'', a free-to- ...
'' have sued two cheaters partnered with AddictedCheats, who offer cheating services for a variety of online games.
Often, game company lawsuits against cheaters or cheat providers cite copyright infringement
Copyright infringement (at times referred to as piracy) is the use of works protected by copyright without permission for a usage where such permission is required, thereby infringing certain exclusive rights granted to the copyright holder, s ...
as the reason for the lawsuit. While some argue against the merit of this claim, grounds for copyright infringement include damaging the company's intellectual property, affecting the experience of other users, and circumventing the Digital Millennium Copyright Act, Digital Millennium Copyright Act (DMCA), which could be applied to video games.
See also
* Cheating in video games * Cheating in esports * Gaming etiquette * Warden (software)References
Further reading
* ''Exploiting Online Games'', Hoglund, Greg, 2008, Pearson Education, * ''Cheating: Gaining Advantage in Videogames'', Consalvo, Mia, 2007, MIT Press,External links
Aspects of Networking in Multiplayer Computer Games
by J.Smed ''et al.'', The Electronic Library, volume 20, number 2, pages 87–97, 2002.
Fair Online Gaming
Information on Intel's anti-cheat research initiative and technology. {{DEFAULTSORT:Cheating In Online Games Cheating in video games, Esports techniques Video game controversies Online games