¤żÉ on:
[Wikipedia]
[Google]
[Amazon]

 Secrecy is the practice of hiding information from certain individuals or groups who do not have the "need to know", perhaps while sharing it with other individuals. That which is kept hidden is known as the secret.
Secrecy is often controversial, depending on the content or nature of the secret, the group or people keeping the secret, and the motivation for secrecy.
Secrecy is the practice of hiding information from certain individuals or groups who do not have the "need to know", perhaps while sharing it with other individuals. That which is kept hidden is known as the secret.
Secrecy is often controversial, depending on the content or nature of the secret, the group or people keeping the secret, and the motivation for secrecy.
 Secrecy by government entities is often decried as excessive or in promotion of poor operation; excessive revelation of information on individuals can conflict with virtues of
Secrecy by government entities is often decried as excessive or in promotion of poor operation; excessive revelation of information on individuals can conflict with virtues of 
 Secrecy can exist in a number of different ways: encoding or encryption (where mathematical and technical strategies are used to hide messages), true secrecy (where restrictions are put upon those who take part of the message, such as through government security classification) and
Secrecy can exist in a number of different ways: encoding or encryption (where mathematical and technical strategies are used to hide messages), true secrecy (where restrictions are put upon those who take part of the message, such as through government security classification) and
 Secrets are sometimes kept to provide the pleasure of surprise. This includes keeping secret about a
Secrets are sometimes kept to provide the pleasure of surprise. This includes keeping secret about a
security clearance
for access and other protection methods, such as keeping documents in a
competitive advantage
to meet legal requirements, or, in some cases, to conceal nefarious behavior. New products under development, unique manufacturing techniques, or simply lists of customers are types of information protected by trade secret laws. Research on corporate secrecy has studied the factors supporting secret organizations. In particular, scholars in economics and management have paid attention to the way firms participating in cartels work together to maintain secrecy and conceal their activities from antitrust authorities. The diversity of the participants (in terms of age and size of the firms) influences their ability to coordinate to avoid being detected. The patent system encourages inventors to publish information in exchange for a limited time monopoly on its use, though patent applications are initially secret. Secret society, Secret societies use secrecy as a way to attract members by creating a sense of importance. Shell corporation, Shell companies may be used to launder money from criminal activity, to finance terrorism, or to evade taxes. Registers of beneficial ownership aim at fighting corporate secrecy in that sense. Other laws ''require'' organizations to keep certain information secret, such as medical records (Health Insurance Portability and Accountability Act, HIPAA in the U.S.), or financial reports that are under preparation (to limit insider trading). Europe has particularly strict laws about database privacy. In many countries, neoliberal reforms of government have included expanding the outsourcing of government tasks and functions to private businesses with the aim of improving efficiency and effectiveness in government administration. However, among the criticisms of these reforms is the claim that the pervasive use of
Commercial-in-confidence
(or secrecy) clauses in contracts between government and private providers further limits public accountability of governments and prevents proper public scrutiny of the performance and probity of the private companies. Concerns have been raised that 'commercial-in-confidence' is open to abuse because it can be deliberately used to hide corporate or government maladministration and even corruption.
 Preservation of secrets is one of the goals of information security. Techniques used include physical security and cryptography. The latter depends on the secrecy o
Preservation of secrets is one of the goals of information security. Techniques used include physical security and cryptography. The latter depends on the secrecy o
cryptographic keys
Many believe that security technology can be more effective if it itself is not kept secret.
Information hiding
is a design principle in much software engineering. It is considered easier to verify software reliability if one can be sure that different parts of the program can only access (and therefore depend on) a known limited amount of information.
 Military secrecy is the concealing of information about martial affairs that is purposely not made available to the general public and hence to any enemy, in order to gain an advantage or to not reveal a weakness, to avoid embarrassment, or to help in propaganda efforts. Most military secrets are tactical in nature, such as the strengths and weaknesses of weapon systems, military tactics, tactics, training methods, plans, and the number and location of specific weapons. Some secrets involve information in broader areas, such as secure communications, cryptography, intelligence operations, and cooperation with third parties.
Military secrecy is the concealing of information about martial affairs that is purposely not made available to the general public and hence to any enemy, in order to gain an advantage or to not reveal a weakness, to avoid embarrassment, or to help in propaganda efforts. Most military secrets are tactical in nature, such as the strengths and weaknesses of weapon systems, military tactics, tactics, training methods, plans, and the number and location of specific weapons. Some secrets involve information in broader areas, such as secure communications, cryptography, intelligence operations, and cooperation with third parties.
Preview.
An Open Source Collection of Readings on Secrecy
Secrecy News
from the Federation of American Scientists {{Authority control Secrecy, Classified information

 Secrecy is the practice of hiding information from certain individuals or groups who do not have the "need to know", perhaps while sharing it with other individuals. That which is kept hidden is known as the secret.
Secrecy is often controversial, depending on the content or nature of the secret, the group or people keeping the secret, and the motivation for secrecy.
Secrecy is the practice of hiding information from certain individuals or groups who do not have the "need to know", perhaps while sharing it with other individuals. That which is kept hidden is known as the secret.
Secrecy is often controversial, depending on the content or nature of the secret, the group or people keeping the secret, and the motivation for secrecy.
 Secrecy by government entities is often decried as excessive or in promotion of poor operation; excessive revelation of information on individuals can conflict with virtues of
Secrecy by government entities is often decried as excessive or in promotion of poor operation; excessive revelation of information on individuals can conflict with virtues of privacy
Privacy (, ) is the ability of an individual or group to seclude themselves or information about themselves, and thereby express themselves selectively.
The domain of privacy partially overlaps with security, which can include the concepts of a ...
and confidentiality. It is often contrasted with social transparency.

 Secrecy can exist in a number of different ways: encoding or encryption (where mathematical and technical strategies are used to hide messages), true secrecy (where restrictions are put upon those who take part of the message, such as through government security classification) and
Secrecy can exist in a number of different ways: encoding or encryption (where mathematical and technical strategies are used to hide messages), true secrecy (where restrictions are put upon those who take part of the message, such as through government security classification) and obfuscation
Obfuscation is the obscuring of the intended meaning of communication by making the message difficult to understand, usually with confusing and ambiguous language. The obfuscation might be either unintentional or intentional (although intent u ...
, where secrets are hidden in plain sight behind complex idiosyncratic language ( jargon) or steganography.
Another classification proposed by Claude Shannon in 1948 reads there are three systems of secrecy within communication:
# concealment systems, including such methods as invisible ink, concealing a message in an innocent text, or in a fake covering cryptogram, or other methods in which the existence of the message is concealed from the enemy
# privacy systems, for example, voice inversion, in which special equipment is required to recover the message
# "true" secrecy systems where the meaning of the message is concealed by the cypher, code, etc., although its existence is not hidden, and the enemy is assumed to have any special equipment necessary to intercept and record the transmitted signal
Sociology
Animals conceal the location of theirden
Den may refer to:
* Den (room), a small room in a house
* Maternity den, a lair where an animal gives birth
Media and entertainment
* ''Den'' (album), 2012, by Kreidler
* Den (''Battle Angel Alita''), a character in the ''Battle Angel Alita' ...
or nest from predators
Predation is a biological interaction where one organism, the predator, kills and eats another organism, its prey. It is one of a family of common feeding behaviours that includes parasitism and micropredation (which usually do not kill the ...
. Squirrels bury nuts, hiding them, and they try to remember their locations later.
Humans attempt to consciously conceal aspects of themselves from others due to shame, or from fear of violence, rejection, harassment, loss of acceptance
Acceptance in human psychology is a person's assent to the reality of a situation, recognizing a process or condition (often a negative or uncomfortable situation) without attempting to change it or protest it. The concept is close in meaning to ...
, or loss of employment
Employment is a relationship between two parties regulating the provision of paid labour services. Usually based on a contract, one party, the employer, which might be a corporation, a not-for-profit organization, a co-operative, or any othe ...
. Humans may also attempt to conceal aspects of their own self which they are not capable of incorporating psychologically into their conscious being. Families sometimes maintain " family secrets", obliging family members never to discuss disagreeable issues concerning the family with outsiders or sometimes even within the family. Many "family secrets" are maintained by using a mutually agreed-upon construct (an official family story) when speaking with outside members. Agreement to maintain the secret is often coerced through "shaming" and reference to family honor. The information may even be something as trivial as a recipe
A recipe is a set of instructions that describes how to prepare or make something, especially a dish of prepared food. A sub-recipe or subrecipe is a recipe for an ingredient that will be called for in the instructions for the main recipe.
His ...
.
 Secrets are sometimes kept to provide the pleasure of surprise. This includes keeping secret about a
Secrets are sometimes kept to provide the pleasure of surprise. This includes keeping secret about a surprise party
A party is a gathering of people who have been invited by a host for the purposes of socializing, conversation, recreation, or as part of a festival or other commemoration or celebration of a special occasion. A party will often feature ...
, not telling spoiler
Spoiler is a security vulnerability on modern computer central processing units that use speculative execution. It exploits side-effects of speculative execution to improve the efficiency of Rowhammer and other related memory and cache attacks. Ac ...
s of a story, and avoiding exposure of a magic trick.
Keeping one's strategy
Strategy (from Greek ŽāŽäŽü╬▒Žä╬Ę╬│╬»╬▒ ''strat─ōgia'', "art of troop leader; office of general, command, generalship") is a general plan to achieve one or more long-term or overall goals under conditions of uncertainty. In the sense of the "art ...
secret is important in many aspects of game theory
Game theory is the study of mathematical models of strategic interactions among rational agents. Myerson, Roger B. (1991). ''Game Theory: Analysis of Conflict,'' Harvard University Press, p.&nbs1 Chapter-preview links, ppviiŌĆōxi It has appli ...
.
In anthropology secret sharing is one way for people to establish traditional relations with other people. A commonly used narrative that describes this kind of behavior is Joseph Conrad
Joseph Conrad (born J├│zef Teodor Konrad Korzeniowski, ; 3 December 1857 ŌĆō 3 August 1924) was a Poles in the United Kingdom#19th century, Polish-British novelist and short story writer. He is regarded as one of the greatest writers in t ...
's short story "The Secret Sharer
"The Secret Sharer" is a short story by Polish-British author Joseph Conrad, originally written in 1909 and first published in two parts in the August and September 1910 editions of '' Harper's Magazine''. It was later included in the short st ...
".
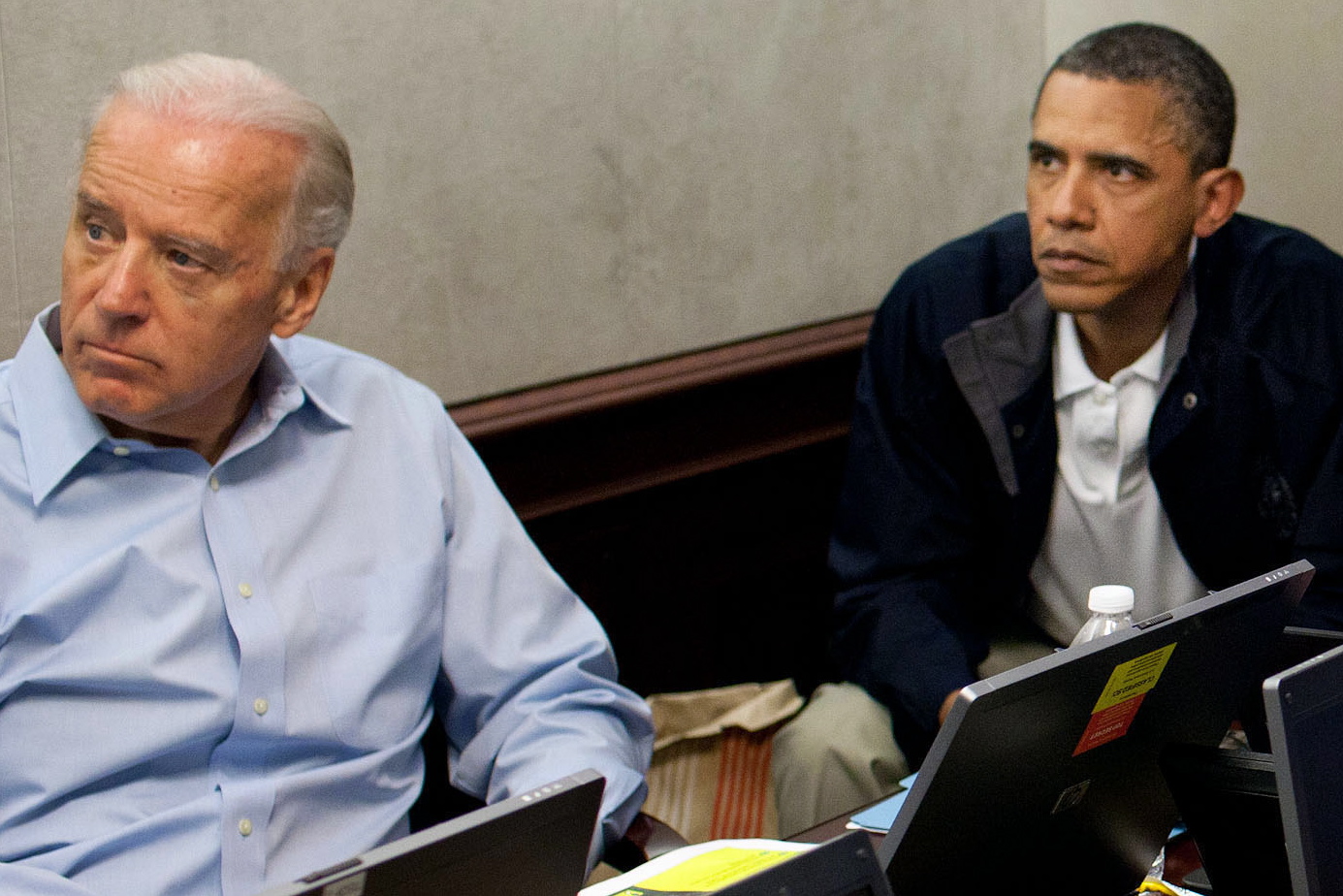
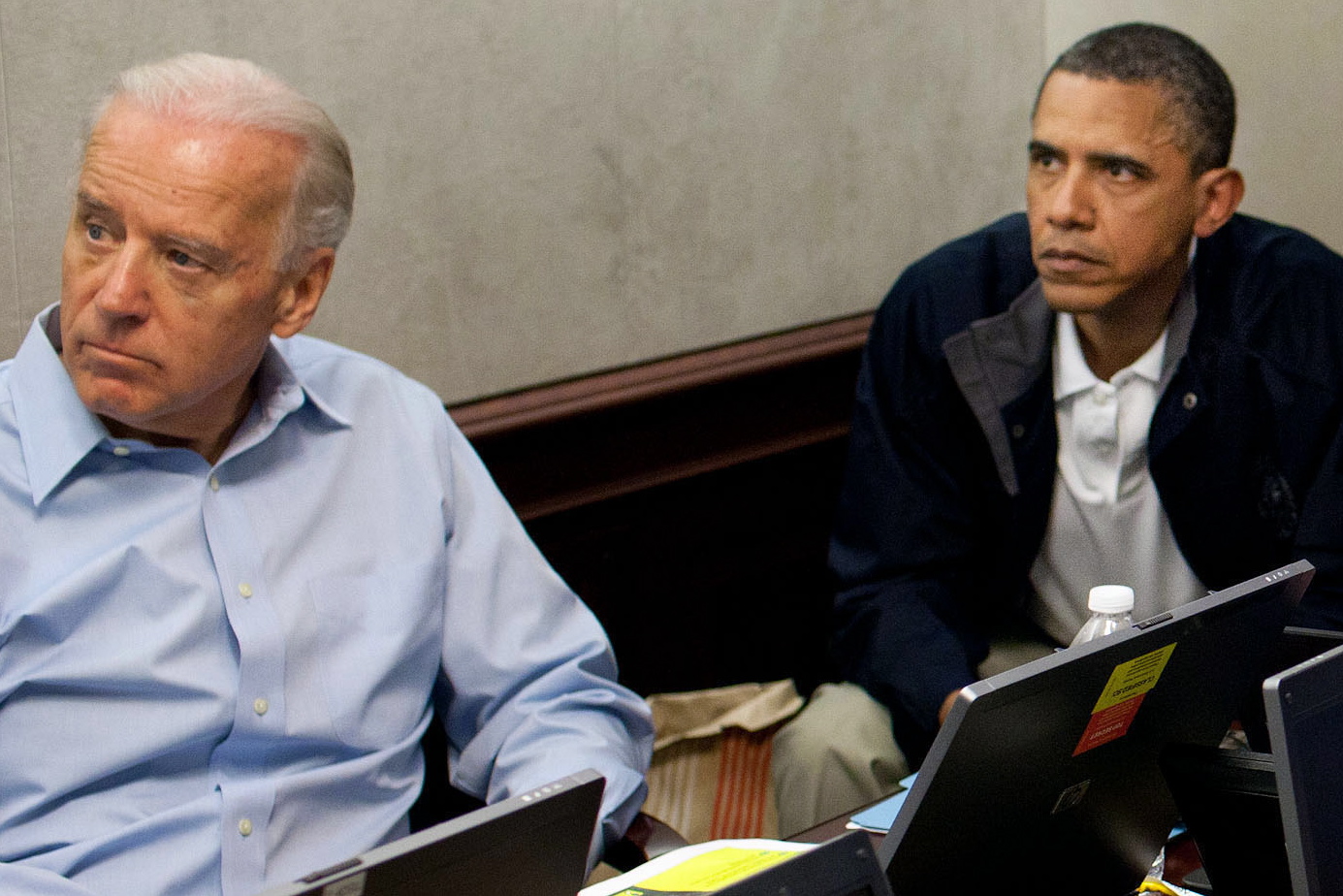
Government
Governments often attempt to conceal information from other governments and the public. These state secrets can include weapon designs, military plans,diplomatic
Diplomatics (in American English, and in most anglophone countries), or diplomatic (in British English), is a scholarly discipline centred on the critical analysis of documents: especially, historical documents. It focuses on the conventions, p ...
negotiation tactics, and secrets obtained illicitly from others (" intelligence"). Most nations have some form of Official Secrets Act
An Official Secrets Act (OSA) is legislation that provides for the protection of state secrets and official information, mainly related to national security but in unrevised form (based on the UK Official Secrets Act 1911) can include all infor ...
(the Espionage Act in the U.S.) and classify material according to the level of protection needed (hence the term " classified information"). An individual needs security clearance
for access and other protection methods, such as keeping documents in a
safe
A safe (also called a strongbox or coffer) is a secure lockable box used for securing valuable objects against theft or fire. A safe is usually a hollow cuboid or cylinder, with one face being removable or hinged to form a door. The body and ...
, are stipulated.
Few people dispute the desirability of keeping Critical Nuclear Weapon Design Information secret, but many believe government secrecy to be excessive and too often employed for political purposes. Many countries have laws that attempt to limit government secrecy, such as the U.S. Freedom of Information Act (United States), Freedom of Information Act and sunshine laws. Government officials sometimes political leak, leak information they are supposed to keep secret. (''For a recent (2005) example, see Plame affair.'')
Secrecy in elections is a growing issue, particularly secrecy of vote counts on computerized vote counting machines. While voting, citizens are acting in a unique sovereign or "owner" capacity (instead of being a subject of the laws, as is true outside of elections) in selecting their government servants. It is argued that secrecy is impermissible as against the public in the area of elections where the government gets all of its power and taxing authority. In any event, permissible secrecy varies significantly with the context involved.
Corporations
Organizations, ranging from multi-national for profit corporations to nonprofit charities, keep secrets focompetitive advantage
to meet legal requirements, or, in some cases, to conceal nefarious behavior. New products under development, unique manufacturing techniques, or simply lists of customers are types of information protected by trade secret laws. Research on corporate secrecy has studied the factors supporting secret organizations. In particular, scholars in economics and management have paid attention to the way firms participating in cartels work together to maintain secrecy and conceal their activities from antitrust authorities. The diversity of the participants (in terms of age and size of the firms) influences their ability to coordinate to avoid being detected. The patent system encourages inventors to publish information in exchange for a limited time monopoly on its use, though patent applications are initially secret. Secret society, Secret societies use secrecy as a way to attract members by creating a sense of importance. Shell corporation, Shell companies may be used to launder money from criminal activity, to finance terrorism, or to evade taxes. Registers of beneficial ownership aim at fighting corporate secrecy in that sense. Other laws ''require'' organizations to keep certain information secret, such as medical records (Health Insurance Portability and Accountability Act, HIPAA in the U.S.), or financial reports that are under preparation (to limit insider trading). Europe has particularly strict laws about database privacy. In many countries, neoliberal reforms of government have included expanding the outsourcing of government tasks and functions to private businesses with the aim of improving efficiency and effectiveness in government administration. However, among the criticisms of these reforms is the claim that the pervasive use of
Commercial-in-confidence
(or secrecy) clauses in contracts between government and private providers further limits public accountability of governments and prevents proper public scrutiny of the performance and probity of the private companies. Concerns have been raised that 'commercial-in-confidence' is open to abuse because it can be deliberately used to hide corporate or government maladministration and even corruption.
Computing
 Preservation of secrets is one of the goals of information security. Techniques used include physical security and cryptography. The latter depends on the secrecy o
Preservation of secrets is one of the goals of information security. Techniques used include physical security and cryptography. The latter depends on the secrecy ocryptographic keys
Many believe that security technology can be more effective if it itself is not kept secret.
Information hiding
is a design principle in much software engineering. It is considered easier to verify software reliability if one can be sure that different parts of the program can only access (and therefore depend on) a known limited amount of information.
Military
 Military secrecy is the concealing of information about martial affairs that is purposely not made available to the general public and hence to any enemy, in order to gain an advantage or to not reveal a weakness, to avoid embarrassment, or to help in propaganda efforts. Most military secrets are tactical in nature, such as the strengths and weaknesses of weapon systems, military tactics, tactics, training methods, plans, and the number and location of specific weapons. Some secrets involve information in broader areas, such as secure communications, cryptography, intelligence operations, and cooperation with third parties.
Military secrecy is the concealing of information about martial affairs that is purposely not made available to the general public and hence to any enemy, in order to gain an advantage or to not reveal a weakness, to avoid embarrassment, or to help in propaganda efforts. Most military secrets are tactical in nature, such as the strengths and weaknesses of weapon systems, military tactics, tactics, training methods, plans, and the number and location of specific weapons. Some secrets involve information in broader areas, such as secure communications, cryptography, intelligence operations, and cooperation with third parties.
Views
Excessive secrecy is often citedLightfoot, Geoffrey, and Tomasz Piotr Wisniewski. "Information asymmetry and power in a surveillance society." Information and Organization 24.4 (2014): 214-235. as a source of much human conflict. One may have to lie in order to hold a secret, which might lead to psychology, psychological repercussions. The alternative, declining to answer when asked something, may suggest the answer and may therefore not always be suitable for keeping a secret. Also, the other may insist that one answer the question. Nearly 2500 years ago, Sophocles wrote, "Do nothing secretly; for Time sees and hears all things, and discloses all." Gautama Siddhartha, the Buddha, once said "Three things cannot long stay hidden: the sun, the moon and the truth".See also
* Ambiguity * Banking secrecy * Classified information * Concealment device * Confidentiality * Conspiracy theory * Covert operation * Cover-up * Deception * Don't ask, don't tell * Espionage * Freedom of information legislation * Media transparency * Need to know * Open secret * Secrecy (sociology) * Secret passage * Secret sharing * Self-concealment * Somebody Else's Problem * Smuggling * State Secrets Privilege * ''Sub rosa'' * WikiLeaksReferences
* * * * * * * * * * * * * * ::Also available as:Preview.
Further reading
*External links
An Open Source Collection of Readings on Secrecy
Secrecy News
from the Federation of American Scientists {{Authority control Secrecy, Classified information