|
Information Security Management System
Information security management (ISM) defines and manages controls that an organization needs to implement to ensure that it is sensibly protecting the confidentiality, availability, and integrity of assets from threats and vulnerabilities. The core of ISM includes information risk management, a process that involves the assessment of the risks an organization must deal with in the management and protection of assets, as well as the dissemination of the risks to all appropriate stakeholders. This requires proper asset identification and valuation steps, including evaluating the value of confidentiality, integrity, availability, and replacement of assets. As part of information security management, an organization may implement an information security management system and other best practices found in the ISO/IEC 27001, ISO/IEC 27002, and ISO/IEC 27035 standards on information security. Risk management and mitigation Managing information security in essence means managing and mitiga ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Confidentiality
Confidentiality involves a set of rules or a promise usually executed through confidentiality agreements that limits the access or places restrictions on certain types of information. Legal confidentiality By law, lawyers are often required to keep confidential anything pertaining to the representation of a client. The duty of confidentiality is much broader than the attorney–client evidentiary privilege, which only covers ''communications'' between the attorney and the client. Both the privilege and the duty serve the purpose of encouraging clients to speak frankly about their cases. This way, lawyers can carry out their duty to provide clients with zealous representation. Otherwise, the opposing side may be able to surprise the lawyer in court with something he did not know about his client, which may weaken the client's position. Also, a distrustful client might hide a relevant fact he thinks is incriminating, but that a skilled lawyer could turn to the client's advanta ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Privacy
Information privacy is the relationship between the collection and dissemination of data, technology, the public expectation of privacy, contextual information norms, and the legal and political issues surrounding them. It is also known as data privacy or data protection. Data privacy is challenging since attempts to use data while protecting an individual's privacy preferences and personally identifiable information. The fields of computer security, data security, and information security all design and use software, hardware, and human resources to address this issue. Authorities Laws Authorities by country Information types Various types of personal information often come under privacy concerns. Cable television This describes the ability to control what information one reveals about oneself over cable television, and who can access that information. For example, third parties can track IP TV programs someone has watched at any given time. "The addition of any informati ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Management
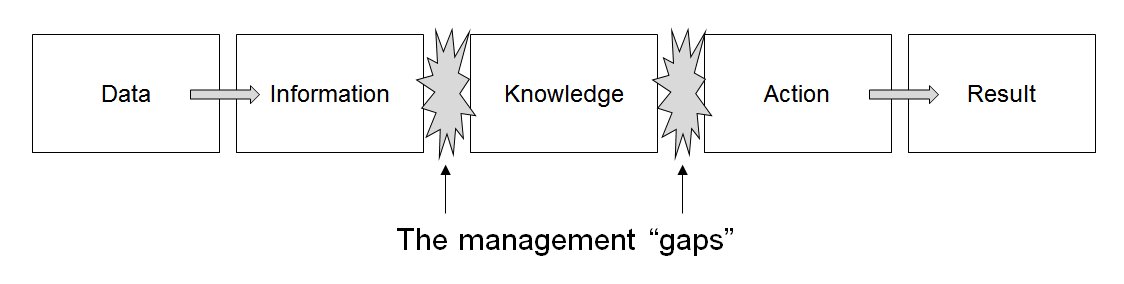
Information management (IM) concerns a cycle of organizational activity: the acquisition of information from one or more sources, the custodianship and the distribution of that information to those who need it, and its ultimate disposal through archiving or deletion. This cycle of information organisation involves a variety of stakeholders, including those who are responsible for assuring the quality, accessibility and utility of acquired information; those who are responsible for its safe storage and disposal; and those who need it for decision making. Stakeholders might have rights to originate, change, distribute or delete information according to organisational information management policies. Information management embraces all the generic concepts of management, including the planning, organizing, structuring, processing, controlling, evaluation and reporting of information activities, all of which is needed in order to meet the needs of those with organisational r ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Security Information Management
Security information management (SIM) is an information security industry term for the collection of data such as log files into a central repository for trend analysis. Overview SIM products generally are software agents running on the computer systems that are monitored. The recorded log information is then sent to a centralized server that acts as a "security console". The console typically displays reports, charts, and graphs of that information, often in real time. Some software agents can incorporate local filters to reduce and manipulate the data that they send to the server, although typically from a forensic point of view you would collect all audit and accounting logs to ensure you can recreate a security incident. The security console is monitored by an administrator who reviews the consolidated information and takes action in response to any alerts issued. The data that is sent to the server to be correlated and analyzed are normalized by the software agents into a co ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Chief Information Security Officer
A chief information security officer (CISO) is a senior-level executive within an organization responsible for establishing and maintaining the enterprise vision, strategy, and program to ensure information assets and technologies are adequately protected. The CISO directs staff in identifying, developing, implementing, and maintaining processes across the enterprise to reduce information and information technology (IT) risks. They respond to incidents, establish appropriate standards and controls, manage security technologies, and direct the establishment and implementation of policies and procedures. The CISO is also usually responsible for information-related compliance (e.g. supervises the implementation to achieve ISO/IEC 27001 certification for an entity or a part of it). The CISO is also responsible for protecting proprietary information and assets of the company, including the data of clients and consumers. CISO works with other executives to make sure the company is growing ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Certified Information Systems Security Professional
CISSP (Certified Information Systems Security Professional) is an independent information security certification granted by the International Information System Security Certification Consortium, also known as (ISC)². As of January, 2022 there are 152,632 (ISC)² members holding the CISSP certification worldwide. In June 2004, the CISSP designation was accredited under the ANSI ISO/IEC Standard 17024:2003.ANSI Accreditation Services - International Information Systems Security Certification Consortium, Inc. (ISC)2 . It is also formally approved by the |
The Open Group
The Open Group is a global consortium that seeks to "enable the achievement of business objectives" by developing "open, vendor-neutral technology standards and certifications." It has over 840 member organizations and provides a number of services, including strategy, management, innovation and research, standards, certification, and test development. It was established in 1996 when X/Open merged with the Open Software Foundation. The Open Group is the certifying body for the UNIX trademark, and publishes the Single UNIX Specification technical standard, which extends the POSIX standards. The Open Group also develops and manages the TOGAF® standard, which is an industry standard enterprise architecture framework. Members The over 840 members include a range of technology vendors and buyers as well as government agencies, including, for example, Capgemini, Fujitsu, HPE, Orbus Software, IBM, Huawei, Philips, the U.S. Department of Defense, and NASA. There is no obligation on ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
ISACA
ISACA is an international professional association focused on IT (information technology) governance. On its IRS filings, it is known as the Information Systems Audit and Control Association, although ISACA now goes by its acronym only. ISACA currently offers 8 certification program as well as other micro-certificates. History ISACA originated in United States in 1967, when a group of individuals working on auditing controls in computer systems started to become increasingly critical of the operations of their organizations. They identified a need for a centralized source of information and guidance in the field. In 1969, Stuart Tyrnauer, an employee of the (later)[...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Open Information Security Maturity Model
The Open Group Information Security Management Maturity Model (O-ISM3) is a maturity model for managing information security. It aims to ensure that security processes in any organization are implemented so as to operate at a level consistent with that organization’s business requirements. O-ISM3 defines a comprehensive but manageable number of information security processes sufficient for the needs of most organizations, with the relevant security control(s) being identified within each process as an essential subset of that process. O-ISM3 v2.0 2018 p6 History The original motivation behind O-ISM3 development was to narrow the gap between theory and practice for information security management systems, and the trigger was the idea of linking security management and maturity models. O-ISM3 strove to keep clear of a number of pitfalls with previous approaches.Siponen, Mikko (2002-08-24). Designing Secure Information Systems and Software: Critical evaluation of the existing approa ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
COBIT
COBIT (Control Objectives for Information and Related Technologies) is a framework created by ISACA for information technology (IT) management and IT governance. The framework is business focused and defines a set of generic processes for the management of IT, with each process defined together with process inputs and outputs, key process-activities, process objectives, performance measures and an elementary maturity model. Framework and components Business and IT goals are linked and measured to create responsibilities of business and IT teams. Five processes are identified: Evaluate, Direct and Monitor (EDM); Align, Plan and Organize (APO); Build, Acquire and Implement (BAI); Deliver, Service and Support (DSS); and Monitor, Evaluate and Assess (MEA).COBIT 2019 Framework: Introduction and Methodology from ISACA The COBIT framework ties in with COSO, ITIL, BiSL, ISO 27000, CMMI, TOGAF and PMBOK. The framework helps companies follow law, be more agile and earn more. Below ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
ITIL
The Information Technology Infrastructure Library (ITIL) is a set of detailed practices for IT activities such as IT service management (ITSM) and IT asset management (ITAM) that focus on aligning IT services with the needs of business. ITIL describes processes, procedures, tasks, and checklists which are neither organization-specific nor technology-specific, but can be applied by an organization toward strategy, delivering value, and maintaining a minimum level of competency. It allows the organization to establish a baseline from which it can plan, implement, and measure. It is used to demonstrate compliance and to measure improvement. There is no formal independent third party compliance assessment available for ITIL compliance in an organization. Certification in ITIL is only available to individuals. Since 2013, ITIL has been owned by AXELOS, a joint venture between Capita and the UK Cabinet Office. History Responding to growing dependence on IT, the UK Government's Ce ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
ISO/IEC 27000
ISO/IEC 27000 is part of a growing family of ISO/IEC standards - the ' ISO/IEC 27000 series'. ISO/IEC 27000 is an international standard titled: ''Information technology — Security techniques — Information security management systems — Overview and vocabulary''. The standard was developed by subcommittee 27 (SC27) of the first Joint Technical Committee (JTC1) of the International Organization for Standardization and the International Electrotechnical Commission. ISO/IEC 27000 provides: * An overview of, and introduction to, the entire ISO/IEC 27000 family of Information Security Management Systems (ISMS)-related standards. * A glossary or vocabulary of the specialist terms used throughout the ISO/IEC 27000 family, formally defined. ISO/IEC 27000 is available via the ITTF website. (gratis download). Overview and introduction The standard describes the purpose of an Information Security Management System (ISMS), a management system similar in concept to those recommend ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |