email account on:
[Wikipedia]
[Google]
[Amazon]
 Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic (
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic (
 # The MUA formats the message in email format and uses the submission protocol, a profile of the
# The MUA formats the message in email format and uses the submission protocol, a profile of the
permanent
an
field names, including also fields defined for MIME, netnews, and HTTP, and referencing relevant RFCs. Common header fields for email include: * ''To'': The email address(es), and optionally name(s) of the message's recipient(s). Indicates primary recipients (multiple allowed), for secondary recipients see Cc: and Bcc: below. * ''Subject'': A brief summary of the topic of the message. Certain abbreviations are commonly used in the subject, including "RE:" and "FW:". * ''Cc'':
 Messages are exchanged between hosts using the
Messages are exchanged between hosts using the
Is Email a Curse or a Boon?
" September 22, 2010. Retrieved October 11, 2010. It has some key benefits to business and other organizations, including: ; Facilitating logistics : Much of the business world relies on communications between people who are not physically in the same building, area, or even country; setting up and attending an in-person meeting,
ITvibe.com
and was threatening the usefulness of email as a practical tool. The US
, May 12, 2016, securelist.com In September 2017, for example, the proportion of spam to legitimate email rose to 59.56%. The percentage of spam email in 2021 is estimated to be 85%.
"Gmail blows up e-mail marketing..."
, Ron Amadeo, Dec 13 2013, Ars Technica
Inbox Detox and The Habit of Email Excellence
", Acanthus Publishing * Lawrence Hughes, ''Internet e-mail Protocols, Standards and Implementation'', Artech House Publishers, . * Kevin Johnson, ''Internet Email Protocols: A Developer's Guide'', Addison-Wesley Professional, . * Pete Loshin, ''Essential Email Standards: RFCs and Protocols Made Practical'', John Wiley & Sons, . * * Sara Radicati, ''Electronic Mail: An Introduction to the X.400 Message Handling Standards'', Mcgraw-Hill, . * John Rhoton, ''Programmer's Guide to Internet Mail: SMTP, POP, IMAP, and LDAP'', Elsevier, . * John Rhoton, ''X.400 and SMTP: Battle of the E-mail Protocols'', Elsevier, . * David Wood, ''Programming Internet Mail'', O'Reilly, .
The History of Email
is Dave Crocker's attempt at capturing the sequence of 'significant' occurrences in the evolution of email; a collaborative effort that also cites this page.
is a personal memoir by the implementer of an early email system
A Look at the Origins of Network Email
is a short, yet vivid recap of the key historical facts
Business E-Mail Compromise - An Emerging Global Threat
Explained from first principles
a 2021 article attempting to summarize more than 100 RFCs {{DEFAULTSORT:Email Internet terminology
 Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic (
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic (digital
Digital usually refers to something using discrete digits, often binary digits.
Technology and computing Hardware
*Digital electronics, electronic circuits which operate using digital signals
**Digital camera, which captures and stores digital i ...
) version of, or counterpart to, mail
The mail or post is a system for physically transporting postcards, letters, and parcels. A postal service can be private or public, though many governments place restrictions on private systems. Since the mid-19th century, national postal sys ...
, at a time when "mail" meant only physical mail (hence '' e- + mail''). Email later became a ubiquitous (very widely used) communication medium, to the point that in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries.
''Email'' is the medium, and each message sent therewith is also called an ''email.'' The term is a mass noun
In linguistics, a mass noun, uncountable noun, non-count noun, uncount noun, or just uncountable, is a noun with the syntactic property that any quantity of it is treated as an undifferentiated unit, rather than as something with discrete elemen ...
.
Email operates across computer networks, primarily the Internet
The Internet (or internet) is the global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a '' network of networks'' that consists of private, pub ...
, and also local area network
A local area network (LAN) is a computer network that interconnects computers within a limited area such as a residence, school, laboratory, university campus or office building. By contrast, a wide area network (WAN) not only covers a larger ...
s. Today's email systems are based on a store-and-forward
Store and forward is a telecommunications technique in which information is sent to an intermediate station where it is kept and sent at a later time to the final destination or to another intermediate station. The intermediate station, or node in ...
model. Email servers accept, forward, deliver, and store messages. Neither the users nor their computers are required to be online simultaneously; they need to connect, typically to a mail server
Within the Internet email system, a message transfer agent (MTA), or mail transfer agent, or mail relay is software that transfers electronic mail messages from one computer to another using SMTP. The terms mail server, mail exchanger, and MX host ...
or a webmail
Webmail (or web-based email) is an email service that can be accessed using a standard web browser. It contrasts with email service accessible through a specialised email client software. Examples of webmail providers are 1&1 Ionos, AOL Mail, G ...
interface to send or receive messages or download it.
Originally an ASCII
ASCII ( ), abbreviated from American Standard Code for Information Interchange, is a character encoding standard for electronic communication. ASCII codes represent text in computers, telecommunications equipment, and other devices. Because of ...
text-only communications medium, Internet email was extended by Multipurpose Internet Mail Extensions
Multipurpose Internet Mail Extensions (MIME) is an Internet standard that extends the format of email messages to support text in character sets other than ASCII, as well as attachments of audio, video, images, and application programs. Message ...
(MIME) to carry text in other character sets and multimedia content attachments. International email International email arises from the combined provision of ''internationalized domain names'' (IDN) and ''email address internationalization'' (EAI).Started with: The result is email that contains international characters (characters which do not e ...
, with internationalized email addresses using UTF-8
UTF-8 is a variable-length character encoding used for electronic communication. Defined by the Unicode Standard, the name is derived from ''Unicode'' (or ''Universal Coded Character Set'') ''Transformation Format 8-bit''.
UTF-8 is capable of e ...
, is standardized but not widely adopted.
Terminology
The term ''electronic mail'' has been in use with its modern meaning since 1975, and variations of the shorter ''E-mail'' have been in use since 1979: * ''email'' is now the common form, and recommended bystyle guide
A style guide or manual of style is a set of standards for the writing, formatting, and design of documents. It is often called a style sheet, although that term also has multiple other meanings. The standards can be applied either for gener ...
s. It is the form required by IETF
The Internet Engineering Task Force (IETF) is a standards organization for the Internet and is responsible for the technical standards that make up the Internet protocol suite (TCP/IP). It has no formal membership roster or requirements and a ...
Requests for Comments
A Request for Comments (RFC) is a publication in a series from the principal technical development and standards-setting bodies for the Internet, most prominently the Internet Engineering Task Force (IETF). An RFC is authored by individuals or g ...
(RFC) and working groups. This spelling also appears in most dictionaries.Random House Unabridged Dictionary, 2006The American Heritage Dictionary of the English Language, Fourth EditionPrinceton University WordNet 3.0The American Heritage Science Dictionary, 2002
* ''e-mail'' is the form favored in edited published American English and British English writing as reflected in the Corpus of Contemporary American English
The Corpus of Contemporary American English (COCA) is a one-billion-word corpus of contemporary American English. It was created by Mark Davies, retired professor of corpus linguistics at Brigham Young University (BYU).
Content
The Corpus of Co ...
data, but is falling out of favor in some style guides.
* ''E-mail'' is sometimes used. The original usage in June 1979 occurred in the journal ''Electronics
The field of electronics is a branch of physics and electrical engineering that deals with the emission, behaviour and effects of electrons using electronic devices. Electronics uses active devices to control electron flow by amplification a ...
'' in reference to the United States Postal Service
The United States Postal Service (USPS), also known as the Post Office, U.S. Mail, or Postal Service, is an independent agency of the executive branch of the United States federal government responsible for providing postal service in the U. ...
initiative called E-COM
E-COM, short for Electronic Computer Originated Mail, was a hybrid mail process used from 1982 to 1985 by the U.S. Postal Service (USPS) to print electronically originated mail, and deliver it in envelopes to customers within two days of transmiss ...
, which was developed in the late 1970s and operated in the early 1980s.
* ''Email'' is also used.
* ''EMAIL'' was used by CompuServe
CompuServe (CompuServe Information Service, also known by its initialism CIS) was an American online service provider, the first major commercial one in the world – described in 1994 as "the oldest of the Big Three information services (the oth ...
starting in April 1981, which popularized the term.
* ''EMail'' is a traditional form used in RFCs for the "Author's Address".
The service is often simply referred to as ''mail'', and a single piece of electronic mail is called a ''message''. The conventions for fields within emails — the “To,” “From,” “CC,” “BCC” etc. — began with RFC-680 in 1975.
An Internet email consists of an ''envelope'' and ''content''; the content consists of a ''header'' and a ''body''.
History
Computer-based messaging between users of the same system became possible after the advent oftime-sharing
In computing, time-sharing is the sharing of a computing resource among many users at the same time by means of multiprogramming and multi-tasking.DEC Timesharing (1965), by Peter Clark, The DEC Professional, Volume 1, Number 1
Its emergence a ...
in the early 1960s, with a notable implementation by MIT
The Massachusetts Institute of Technology (MIT) is a private land-grant research university in Cambridge, Massachusetts. Established in 1861, MIT has played a key role in the development of modern technology and science, and is one of the m ...
's CTSS project in 1965. Most developers of early mainframe
A mainframe computer, informally called a mainframe or big iron, is a computer used primarily by large organizations for critical applications like bulk data processing for tasks such as censuses, industry and consumer statistics, enterprise ...
s and minicomputer
A minicomputer, or colloquially mini, is a class of smaller general purpose computers that developed in the mid-1960s and sold at a much lower price than mainframe and mid-size computers from IBM and its direct competitors. In a 1970 survey, ...
s developed similar, but generally incompatible, mail applications. In 1971 the first ARPANET
The Advanced Research Projects Agency Network (ARPANET) was the first wide-area packet-switched network with distributed control and one of the first networks to implement the TCP/IP protocol suite. Both technologies became the technical foun ...
network mail was sent, introducing the now-familiar address syntax with the '@' symbol designating the user's system address. Over a series of RFCs, conventions were refined for sending mail messages over the File Transfer Protocol
The File Transfer Protocol (FTP) is a standard communication protocol used for the transfer of computer files from a server to a client on a computer network. FTP is built on a client–server model architecture using separate control and data ...
.
Proprietary electronic mail systems soon began to emerge. IBM, CompuServe
CompuServe (CompuServe Information Service, also known by its initialism CIS) was an American online service provider, the first major commercial one in the world – described in 1994 as "the oldest of the Big Three information services (the oth ...
and Xerox
Xerox Holdings Corporation (; also known simply as Xerox) is an American corporation that sells print and digital document products and services in more than 160 countries. Xerox is headquartered in Norwalk, Connecticut (having moved from Stamf ...
used in-house mail systems in the 1970s; CompuServe sold a commercial intraoffice mail product from 1978 and IBM and Xerox from 1981.; ; ; ; DEC's ALL-IN-1
ALL-IN-1 was an office automation product developed and sold by Digital Equipment Corporation in the 1980s. It was one of the first purchasable off the shelf electronic mail products. It was later known as ''Office Server V3.2 for OpenVMS Alpha a ...
and Hewlett-Packard's HPMAIL (later HP DeskManager) were released in 1982; development work on the former began in the late 1970s and the latter became the world’s largest selling email system.
The Simple Mail Transfer Protocol
The Simple Mail Transfer Protocol (SMTP) is an Internet standard communication protocol for electronic mail transmission. Mail servers and other message transfer agents use SMTP to send and receive mail messages. User-level email clients typical ...
(SMTP) protocol was implemented on the ARPANET in 1983. LAN email systems emerged in the mid 1980s. For a time in the late 1980s and early 1990s, it seemed likely that either a proprietary commercial system or the X.400
X.400 is a suite of ITU-T Recommendations that defines the ITU-T Message Handling System (MHS).
At one time, the designers of X.400 were expecting it to be the predominant form of email, but this role has been taken by the SMTP-based Internet e-m ...
email system, part of the Government Open Systems Interconnection Profile The Government Open Systems Interconnection Profile (GOSIP) was a specification that profiled open networking products for procurement by governments in the late 1980s and early 1990s.
Timeline
* 1988 - GOSIP: Government Open Systems Interconnectio ...
(GOSIP), would predominate. However, once the final restrictions on carrying commercial traffic over the Internet ended in 1995, a combination of factors made the current Internet suite of SMTP, POP3
In computing, the Post Office Protocol (POP) is an application-layer Internet standard protocol used by e-mail clients to retrieve e-mail from a mail server. POP version 3 (POP3) is the version in common use, and along with IMAP the most common ...
and IMAP
In computing, the Internet Message Access Protocol (IMAP) is an Internet standard protocol used by email clients to retrieve email messages from a mail server over a TCP/IP connection. IMAP is defined by .
IMAP was designed with the goal of pe ...
email protocols the standard (see Protocol Wars
A long-running debate in computer science known as the Protocol Wars occurred from the 1970s to the 1990s when engineers, organizations and nations became polarized over the issue of which communication protocol would result in the best and most r ...
).
Operation
The following is a typical sequence of events that takes place when sender Alice transmits a message using amail user agent
The mail or post is a system for physically transporting postcards, letters, and parcels. A postal service can be private or public, though many governments place restrictions on private systems. Since the mid-19th century, national postal syst ...
(MUA) addressed to the email address
An email address identifies an email box to which messages are delivered. While early messaging systems used a variety of formats for addressing, today, email addresses follow a set of specific rules originally standardized by the Internet Engineer ...
of the recipient.
Simple Mail Transfer Protocol
The Simple Mail Transfer Protocol (SMTP) is an Internet standard communication protocol for electronic mail transmission. Mail servers and other message transfer agents use SMTP to send and receive mail messages. User-level email clients typical ...
(SMTP), to send the message content to the local mail submission agent
A message submission agent (MSA), or mail submission agent, is a computer program or software agent that receives electronic mail messages from a mail user agent (MUA) and cooperates with a mail transfer agent (MTA) for delivery of the mail. It us ...
(MSA), in this case ''smtp.a.org''.
# The MSA determines the destination address provided in the SMTP protocol (not from the message header) — in this case, ''[email protected]'' — which is a fully qualified domain address (FQDA). The part before the @ sign is the ''local part'' of the address, often the username
A user is a person who utilizes a computer or network service.
A user often has a user account and is identified to the system by a username (or user name). Other terms for username include login name, screenname (or screen name), accoun ...
of the recipient, and the part after the @ sign is a domain name
A domain name is a string that identifies a realm of administrative autonomy, authority or control within the Internet. Domain names are often used to identify services provided through the Internet, such as websites, email services and more. As ...
. The MSA resolves a domain name to determine the fully qualified domain name
A fully qualified domain name (FQDN), sometimes also referred to as an ''absolute domain name'', is a domain name that specifies its exact location in the tree hierarchy of the Domain Name System (DNS). It specifies all domain levels, including th ...
of the mail server
Within the Internet email system, a message transfer agent (MTA), or mail transfer agent, or mail relay is software that transfers electronic mail messages from one computer to another using SMTP. The terms mail server, mail exchanger, and MX host ...
in the Domain Name System
The Domain Name System (DNS) is a hierarchical and distributed naming system for computers, services, and other resources in the Internet or other Internet Protocol (IP) networks. It associates various information with domain names assigned to ...
(DNS).
# The DNS server
A name server refers to the server component of the Domain Name System (DNS), one of the two principal namespaces of the Internet. The most important function of DNS servers is the translation (resolution) of human-memorable domain names (exampl ...
for the domain ''b.org'' (''ns.b.org'') responds with any MX record
A mail exchanger record (MX record) specifies the mail server responsible for accepting email messages on behalf of a domain name. It is a resource record in the Domain Name System (DNS). It is possible to configure several MX records, typically p ...
s listing the mail exchange servers for that domain, in this case ''mx.b.org'', a message transfer agent
Within the Internet email system, a message transfer agent (MTA), or mail transfer agent, or mail relay is software that transfers electronic mail messages from one computer to another using SMTP. The terms mail server, mail exchanger, and MX host ...
(MTA) server run by the recipient's ISP.
# smtp.a.org sends the message to mx.b.org using SMTP. This server may need to forward the message to other MTAs before the message reaches the final message delivery agent A message delivery agent (MDA), or mail delivery agent, is a computer software component that is responsible for the delivery of e-mail messages to a local recipient's mailbox., ''Internet Mail Architecture'', D. Crocker (July 2009) It is also call ...
(MDA).
# The MDA delivers it to the mailbox of user ''bob''.
# Bob's MUA picks up the message using either the Post Office Protocol
In computing, the Post Office Protocol (POP) is an application-layer Internet standard protocol used by e-mail clients to retrieve e-mail from a mail server. POP version 3 (POP3) is the version in common use, and along with IMAP the most common ...
(POP3) or the Internet Message Access Protocol
In computing, the Internet Message Access Protocol (IMAP) is an Internet standard protocol used by email clients to retrieve email messages from a mail server over a TCP/IP connection. IMAP is defined by .
IMAP was designed with the goal of p ...
(IMAP).
In addition to this example, alternatives and complications exist in the email system:
* Alice or Bob may use a client connected to a corporate email system, such as IBM Lotus Notes
HCL Notes (formerly IBM Notes and Lotus Notes; see Branding below) and HCL Domino (formerly IBM Domino and Lotus Domino) are the client and server, respectively, of a collaborative client-server software platform formerly sold by IBM, now by HC ...
or Microsoft
Microsoft Corporation is an American multinational technology corporation producing computer software, consumer electronics, personal computers, and related services headquartered at the Microsoft Redmond campus located in Redmond, Washingt ...
Exchange
Exchange may refer to:
Physics
*Gas exchange is the movement of oxygen and carbon dioxide molecules from a region of higher concentration to a region of lower concentration. Places United States
* Exchange, Indiana, an unincorporated community
* ...
. These systems often have their own internal email format and their clients typically communicate with the email server using a vendor-specific, proprietary protocol. The server sends or receives email via the Internet through the product's Internet mail gateway which also does any necessary reformatting. If Alice and Bob work for the same company, the entire transaction may happen completely within a single corporate email system.
* Alice may not have an MUA on her computer but instead may connect to a webmail
Webmail (or web-based email) is an email service that can be accessed using a standard web browser. It contrasts with email service accessible through a specialised email client software. Examples of webmail providers are 1&1 Ionos, AOL Mail, G ...
service.
* Alice's computer may run its own MTA, so avoiding the transfer at step 1.
* Bob may pick up his email in many ways, for example logging into mx.b.org and reading it directly, or by using a webmail service.
* Domains usually have several mail exchange servers so that they can continue to accept mail even if the primary is not available.
Many MTAs used to accept messages for any recipient on the Internet and do their best to deliver them. Such MTAs are called ''open mail relay
An open mail relay is a Simple Mail Transfer Protocol (SMTP) server configured in such a way that it allows anyone on the Internet to send e-mail through it, not just mail destined to or originating from known users. This used to be the default con ...
s''. This was very important in the early days of the Internet when network connections were unreliable. However, this mechanism proved to be exploitable by originators of unsolicited bulk email
Email spam, also referred to as junk email, spam mail, or simply spam, is unsolicited messages sent in bulk by email (spamming).
The name comes from a Monty Python sketch in which the name of the canned pork product Spam is ubiquitous, unavoida ...
and as a consequence open mail relays have become rare, and many MTAs do not accept messages from open mail relays.
Message format
The basic Internet message format used for email is defined by , with encoding of non-ASCII data and multimedia content attachments defined in RFC 2045 through RFC 2049, collectively called ''Multipurpose Internet Mail Extensions
Multipurpose Internet Mail Extensions (MIME) is an Internet standard that extends the format of email messages to support text in character sets other than ASCII, as well as attachments of audio, video, images, and application programs. Message ...
'' or ''MIME''. The extensions in International email International email arises from the combined provision of ''internationalized domain names'' (IDN) and ''email address internationalization'' (EAI).Started with: The result is email that contains international characters (characters which do not e ...
apply only to email. RFC 5322 replaced the earlier RFC 2822 in 2008, then RFC 2822 in 2001 replaced RFC 822 – the standard for Internet email for decades. Published in 1982, RFC 822 was based on the earlier RFC 733 for the ARPANET.
Internet email messages consist of two sections, "header" and "body". These are known as "content". The header is structured into fields
Fields may refer to:
Music
*Fields (band), an indie rock band formed in 2006
*Fields (progressive rock band), a progressive rock band formed in 1971
* ''Fields'' (album), an LP by Swedish-based indie rock band Junip (2010)
* "Fields", a song by ...
such as From, To, CC, Subject, Date, and other information about the email. In the process of transporting email messages between systems, SMTP communicates delivery parameters and information using message header fields. The body contains the message, as unstructured text, sometimes containing a signature block
A signature block (often abbreviated as signature, sig block, sig file, .sig, dot sig, siggy, or just sig) is a personalized block of text automatically appended at the bottom of an email message, Usenet article, or forum post.
Email and Usenet
...
at the end. The header is separated from the body by a blank line.
Message header
RFC 5322 specifies thesyntax
In linguistics, syntax () is the study of how words and morphemes combine to form larger units such as phrases and sentences. Central concerns of syntax include word order, grammatical relations, hierarchical sentence structure (constituency ...
of the email header. Each email message has a header (the "header section" of the message, according to the specification), comprising a number of fields
Fields may refer to:
Music
*Fields (band), an indie rock band formed in 2006
*Fields (progressive rock band), a progressive rock band formed in 1971
* ''Fields'' (album), an LP by Swedish-based indie rock band Junip (2010)
* "Fields", a song by ...
("header fields"). Each field has a name ("field name" or "header field name"), followed by the separator character ":", and a value ("field body" or "header field body").
Each field name begins in the first character of a new line in the header section, and begins with a non-whitespace
White space or whitespace may refer to:
Technology
* Whitespace characters, characters in computing that represent horizontal or vertical space
* White spaces (radio), allocated but locally unused radio frequencies
* TV White Space Database, a mec ...
printable character. It ends with the separator character ":". The separator is followed by the field value (the "field body"). The value can continue onto subsequent lines if those lines have space or tab as their first character. Field names and, without SMTPUTF8
The Simple Mail Transfer Protocol (SMTP) is an Internet standard communication protocol for electronic mail transmission. Mail servers and other message transfer agents use SMTP to send and receive mail messages. User-level email clients typical ...
, field bodies are restricted to 7-bit ASCII characters. Some non-ASCII values may be represented using MIME encoded words.
Header fields
Email header fields can be multi-line, with each line recommended to be no more than 78 characters, although the limit is 998 characters. Header fields defined by RFC 5322 contain onlyUS-ASCII
ASCII ( ), abbreviated from American Standard Code for Information Interchange, is a character encoding standard for electronic communication. ASCII codes represent text in computers, telecommunications equipment, and other devices. Because of ...
characters; for encoding characters in other sets, a syntax specified in RFC 2047 may be used. In some examples, the IETF EAI working group defines some standards track extensions, replacing previous experimental extensions so UTF-8
UTF-8 is a variable-length character encoding used for electronic communication. Defined by the Unicode Standard, the name is derived from ''Unicode'' (or ''Universal Coded Character Set'') ''Transformation Format 8-bit''.
UTF-8 is capable of e ...
encoded Unicode
Unicode, formally The Unicode Standard,The formal version reference is is an information technology standard for the consistent encoding, representation, and handling of text expressed in most of the world's writing systems. The standard, whic ...
characters may be used within the header. In particular, this allows email addresses to use non-ASCII characters. Such addresses are supported by Google and Microsoft products, and promoted by some government agents.
The message header must include at least the following fields:
* ''From'': The email address, and, optionally, the name of the author(s). Some email clients are changeable through account settings.
* ''Date'': The local time and date the message was written. Like the ''From:'' field, many email clients fill this in automatically before sending. The recipient's client may display the time in the format and time zone local to them.
RFC 3864 describes registration procedures for message header fields at the IANA
The Internet Assigned Numbers Authority (IANA) is a standards organization that oversees global IP address allocation, autonomous system number allocation, root zone management in the Domain Name System (DNS), media types, and other Interne ...
; it provides fopermanent
an
field names, including also fields defined for MIME, netnews, and HTTP, and referencing relevant RFCs. Common header fields for email include: * ''To'': The email address(es), and optionally name(s) of the message's recipient(s). Indicates primary recipients (multiple allowed), for secondary recipients see Cc: and Bcc: below. * ''Subject'': A brief summary of the topic of the message. Certain abbreviations are commonly used in the subject, including "RE:" and "FW:". * ''Cc'':
Carbon copy
Before the development of photographic copiers, a carbon copy was the under-copy of a typed or written document placed over carbon paper and the under-copy sheet itself (not to be confused with the carbon print family of photographic reproduc ...
; Many email clients mark email in one's inbox differently depending on whether they are in the To: or Cc: list.
* ''Bcc'': Blind carbon copy
Blind carbon copy (abbreviated Bcc) allows the sender of a message to conceal the person entered in the Bcc field from the other recipients. This concept originally applied to paper correspondence and now also applies to email.
In some circumsta ...
; addresses are usually only specified during SMTP delivery, and not usually listed in the message header.
* Content-Type: Information about how the message is to be displayed, usually a MIME
Multipurpose Internet Mail Extensions (MIME) is an Internet standard that extends the format of email messages to support text in character sets other than ASCII, as well as attachments of audio, video, images, and application programs. Message ...
type.
* ''Precedence'': commonly with values "bulk", "junk", or "list"; used to indicate automated "vacation" or "out of office" responses should not be returned for this mail, e.g. to prevent vacation notices from sent to all other subscribers of a mailing list. Sendmail
Sendmail is a general purpose internetwork email routing facility that supports many kinds of mail-transfer and delivery methods, including the Simple Mail Transfer Protocol (SMTP) used for email transport over the Internet.
A descendant of the ...
uses this field to affect prioritization of queued email, with "Precedence: special-delivery" messages delivered sooner. With modern high-bandwidth networks, delivery priority is less of an issue than it was. Microsoft Exchange respects a fine-grained automatic response suppression mechanism, the ''X-Auto-Response-Suppress'' field.
* '' Message-ID'': Also an automatic-generated field to prevent multiple deliveries and for reference in In-Reply-To: (see below).
* ''In-Reply-To'': Message-ID of the message this is a reply to. Used to link related messages together. This field only applies to reply messages.
* ''References'': Message-ID of the message this is a reply to, and the message-id of the message the previous reply was a reply to, etc.
* ': Address should be used to reply to the message.
* ''Sender'': Address of the sender acting on behalf of the author listed in the From: field (secretary, list manager, etc.).
* ''Archived-At'': A direct link to the archived form of an individual email message.
The ''To:'' field may be unrelated to the addresses to which the message is delivered. The delivery list is supplied separately to the transport protocol, SMTP
The Simple Mail Transfer Protocol (SMTP) is an Internet standard communication protocol for electronic mail transmission. Mail servers and other message transfer agents use SMTP to send and receive mail messages. User-level email clients typica ...
, which may be extracted from the header content. The "To:" field is similar to the addressing at the top of a conventional letter delivered according to the address on the outer envelope. In the same way, the "From:" field may not be the sender. Some mail servers apply email authentication Email authentication, or validation, is a collection of techniques aimed at providing verifiable information about the origin of email messages by validating the domain ownership of any message transfer agents (MTA) who participated in transferring ...
systems to messages relayed. Data pertaining to the server's activity is also part of the header, as defined below.
SMTP defines the ''trace information'' of a message saved in the header using the following two fields:
* ''Received'': after an SMTP server accepts a message, it inserts this trace record at the top of the header (last to first).
* ''Return-Path'': after the delivery SMTP server makes the ''final delivery'' of a message, it inserts this field at the top of the header.
Other fields added on top of the header by the receiving server may be called ''trace fields''.
* ''Authentication-Results'': after a server verifies authentication, it can save the results in this field for consumption by downstream agents.
* ''Received-SPF'': stores results of SPF checks in more detail than Authentication-Results.
* ''DKIM-Signature'': stores results of DomainKeys Identified Mail
DomainKeys Identified Mail (DKIM) is an email authentication method designed to detect forged sender addresses in email ( email spoofing), a technique often used in phishing and email spam.
DKIM allows the receiver to check that an email claime ...
(DKIM) decryption to verify the message was not changed after it was sent.
* ''Auto-Submitted'': is used to mark automatic-generated messages.
* ''VBR-Info'': claims VBR whitelisting
Message body
Content encoding
Internet email was designed for 7-bit ASCII. Most email software is8-bit clean
''8-bit clean'' is an attribute of computer systems, communication channels, and other devices and software, that handle 8-bit character encodings correctly. Such encoding include the ISO 8859 series and the UTF-8 encoding of Unicode.
History
...
, but must assume it will communicate with 7-bit servers and mail readers. The MIME
Multipurpose Internet Mail Extensions (MIME) is an Internet standard that extends the format of email messages to support text in character sets other than ASCII, as well as attachments of audio, video, images, and application programs. Message ...
standard introduced character set specifiers and two content transfer encodings to enable transmission of non-ASCII data: quoted printable
Quoted-Printable, or QP encoding, is a binary-to-text encoding system using printable ASCII characters (alphanumeric and the equals sign =) to transmit 8-bit data over a 7-bit data path or, generally, over a medium which is not 8-bit clean. Hist ...
for mostly 7-bit content with a few characters outside that range and base64
In computer programming, Base64 is a group of binary-to-text encoding schemes that represent binary data (more specifically, a sequence of 8-bit bytes) in sequences of 24 bits that can be represented by four 6-bit Base64 digits.
Common to all bi ...
for arbitrary binary data. The 8BITMIME
The Simple Mail Transfer Protocol (SMTP) is an Internet standard communication protocol for electronic mail transmission. Mail servers and other message transfer agents use SMTP to send and receive mail messages. User-level email clients typical ...
and BINARY
Binary may refer to:
Science and technology Mathematics
* Binary number, a representation of numbers using only two digits (0 and 1)
* Binary function, a function that takes two arguments
* Binary operation, a mathematical operation that ta ...
extensions were introduced to allow transmission of mail without the need for these encodings, but many mail transport agent
Within the Internet email system, a message transfer agent (MTA), or mail transfer agent, or mail relay is software that transfers electronic mail messages from one computer to another using SMTP. The terms mail server, mail exchanger, and MX host ...
s may not support them. In some countries, e-mail software violates by sending rawNot using Internationalized Email or MIME non-ASCII text and several encoding schemes co-exist; as a result, by default, the message in a non-Latin alphabet language appears in non-readable form (the only exception is a coincidence if the sender and receiver use the same encoding scheme). Therefore, for international character set
Character encoding is the process of assigning numbers to graphical characters, especially the written characters of human language, allowing them to be stored, transmitted, and transformed using digital computers. The numerical values that ...
s, Unicode
Unicode, formally The Unicode Standard,The formal version reference is is an information technology standard for the consistent encoding, representation, and handling of text expressed in most of the world's writing systems. The standard, whic ...
is growing in popularity.
Plain text and HTML
Most modern graphicemail client
An email client, email reader or, more formally, message user agent (MUA) or mail user agent is a computer program used to access and manage a user's email.
A web application which provides message management, composition, and reception functio ...
s allow the use of either plain text
In computing, plain text is a loose term for data (e.g. file contents) that represent only characters of readable material but not its graphical representation nor other objects ( floating-point numbers, images, etc.). It may also include a lim ...
or HTML
The HyperText Markup Language or HTML is the standard markup language for documents designed to be displayed in a web browser. It can be assisted by technologies such as Cascading Style Sheets (CSS) and scripting languages such as JavaScript ...
for the message body at the option of the user. HTML email
HTML email is the use of a subset of HTML to provide formatting and semantic markup capabilities in email that are not available with plain text: Text can be linked without displaying a URL, or breaking long URLs into multiple pieces. Text is wra ...
messages often include an automatic-generated plain text copy for compatibility.
Advantages of HTML include the ability to include in-line links and images, set apart previous messages in block quotes, wrap naturally on any display, use emphasis such as underline
An underscore, ; also called an underline, low line, or low dash; is a line drawn under a segment of text. In proofreading, underscoring is a convention that says "set this text in italic type", traditionally used on manuscript or typescript as ...
s and italics
In typography, italic type is a cursive font based on a stylised form of calligraphic handwriting. Owing to the influence from calligraphy, italics normally slant slightly to the right. Italics are a way to emphasise key points in a printed tex ...
, and change font
In metal typesetting, a font is a particular size, weight and style of a typeface. Each font is a matched set of type, with a piece (a "sort") for each glyph. A typeface consists of a range of such fonts that shared an overall design.
In mod ...
styles. Disadvantages include the increased size of the email, privacy concerns about web bug
A web beaconAlso called web bug, tracking bug, tag, web tag, page tag, tracking pixel, pixel tag, 1×1 GIF, or clear GIF. is a technique used on web pages and email to unobtrusively (usually invisibly) allow checking that a user has accessed s ...
s, abuse of HTML email as a vector for phishing
Phishing is a type of social engineering where an attacker sends a fraudulent (e.g., spoofed, fake, or otherwise deceptive) message designed to trick a person into revealing sensitive information to the attacker or to deploy malicious softwar ...
attacks and the spread of malicious software
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, depr ...
.
Some e-mail clients interpret the body as HTML even in the absence of a Content-Type: html header field; this may cause various problems.
Some web-based mailing list
A mailing list is a collection of names and addresses used by an individual or an organization to send material to multiple recipients. The term is often extended to include the people subscribed to such a list, so the group of subscribers is re ...
s recommend all posts be made in plain text, with 72 or 80 characters per line
In typography and computing, characters per line (CPL) or terminal width refers to the maximal number of monospaced characters that may appear on a single line. It is similar to line length in typesetting.
History
The limit of the line length ...
for all the above reasons, and because they have a significant number of readers using text-based email clients such as Mutt.
Various informal conventions evolved for marking up plain text in email and usenet
Usenet () is a worldwide distributed discussion system available on computers. It was developed from the general-purpose UUCP, Unix-to-Unix Copy (UUCP) dial-up network architecture. Tom Truscott and Jim Ellis (computing), Jim Ellis conceived th ...
posts, which later led to the development of formal languages like setext
Setext (Structure Enhanced Text) is a lightweight markup language used to format plain text documents such as e-newsletters, Usenet postings, and e-mails. In contrast to some other markup languages (such as HTML), the markup is easily readable wi ...
''(c. 1992)'' and many others
Many may refer to:
* grammatically plural in number
*an English quantifier used with count nouns indicating a large but indefinite number of; at any rate, more than a few
;Place names
* Many, Moselle, a commune of the Moselle department in Fran ...
, the most popular of them being markdown
Markdown is a lightweight markup language for creating formatted text using a plain-text editor. John Gruber and Aaron Swartz created Markdown in 2004 as a markup language that is appealing to human readers in its source code form. Markdown is ...
.
Some Microsoft
Microsoft Corporation is an American multinational technology corporation producing computer software, consumer electronics, personal computers, and related services headquartered at the Microsoft Redmond campus located in Redmond, Washingt ...
email clients may allow rich formatting using their proprietary Rich Text Format
)
As an example, the following RTF code
would be rendered as follows:
This is some bold text.
Character encoding
A standard RTF file can only consist of 7-bit ASCII characters, but can use escape sequences to encode other characters. Th ...
(RTF), but this should be avoided unless the recipient is guaranteed to have a compatible email client.
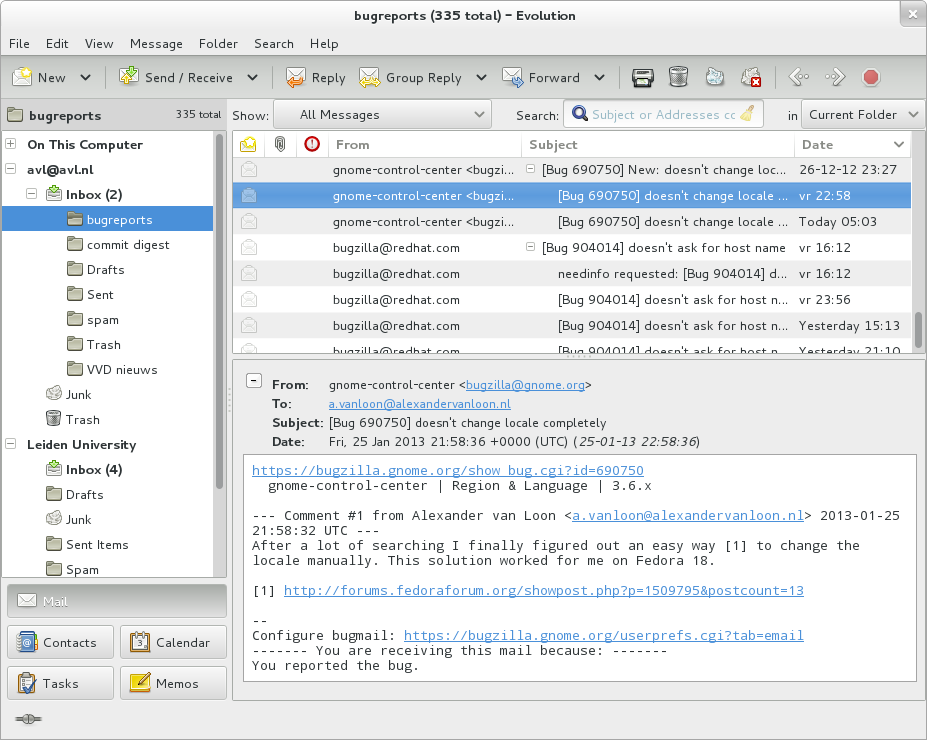
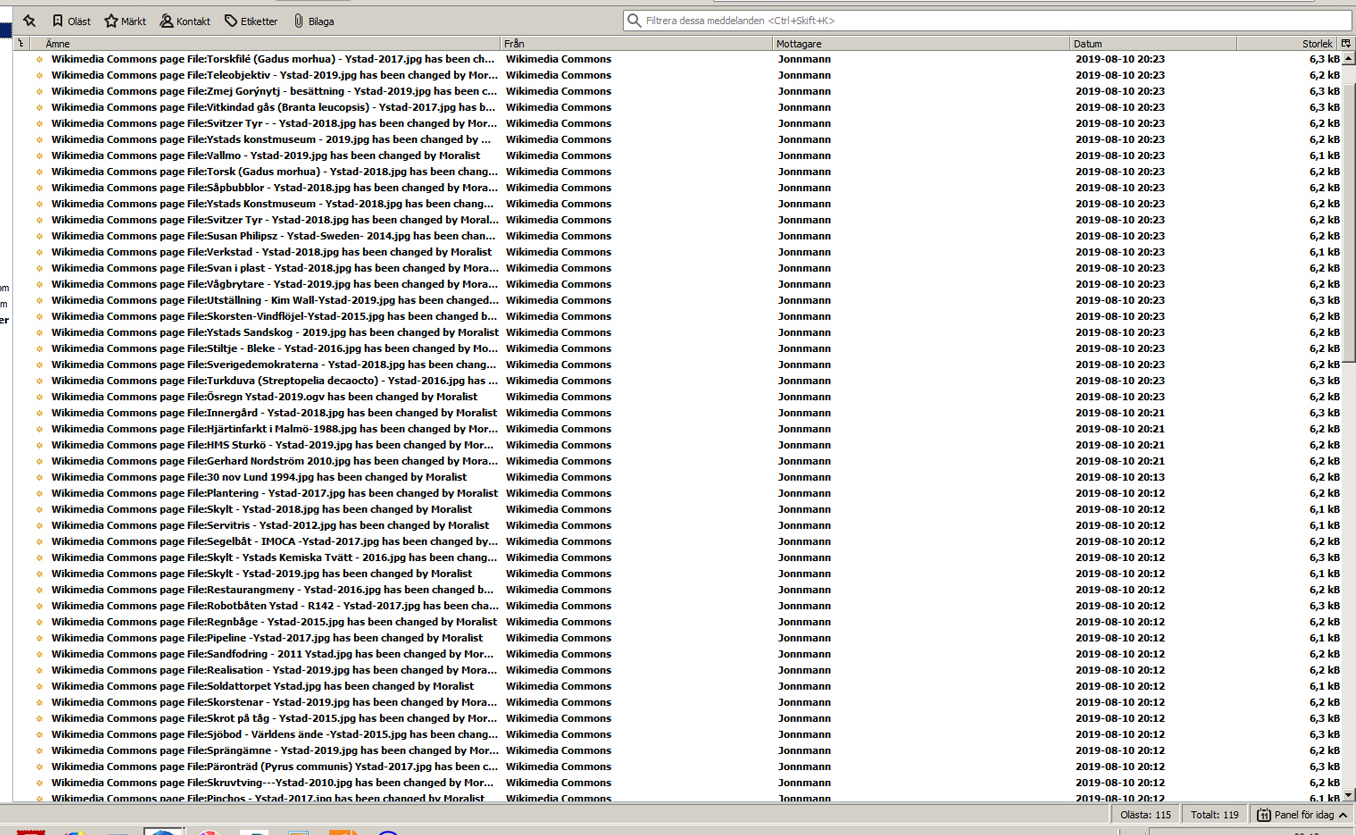
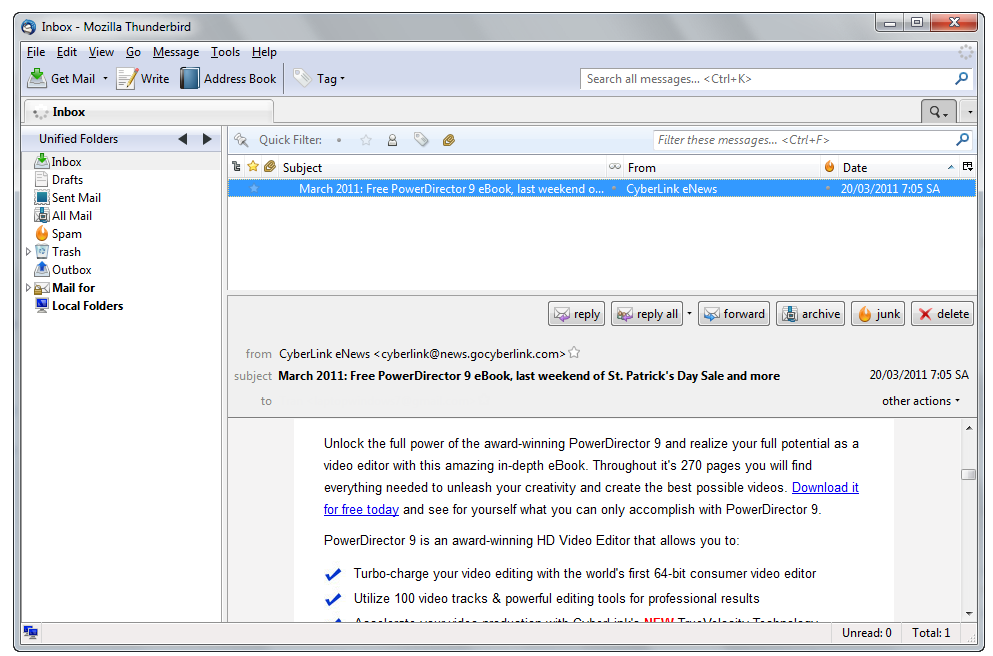
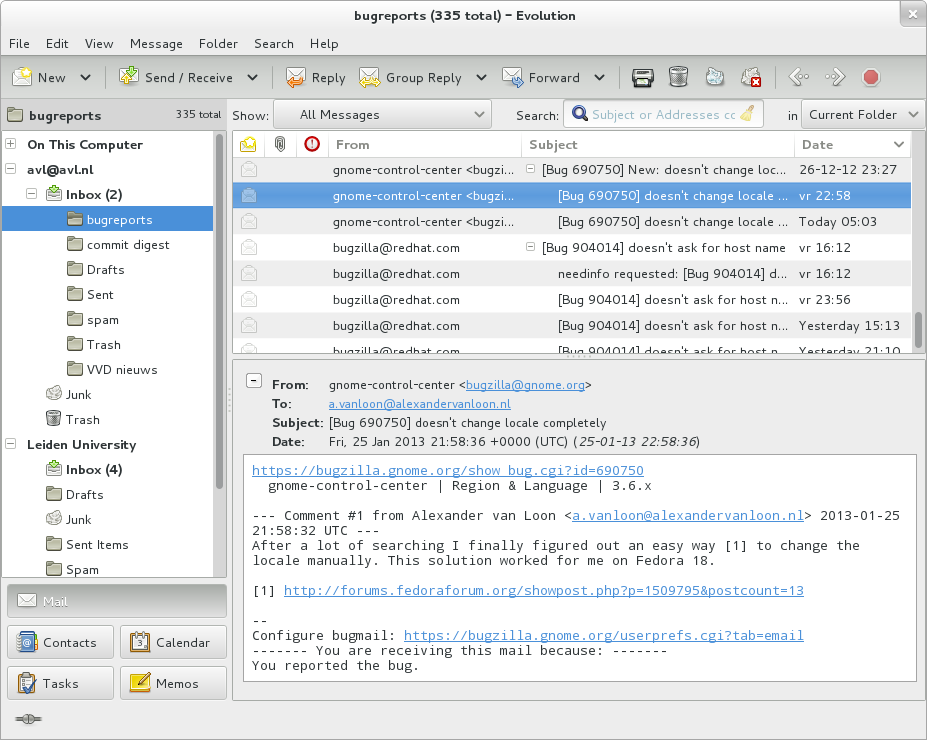
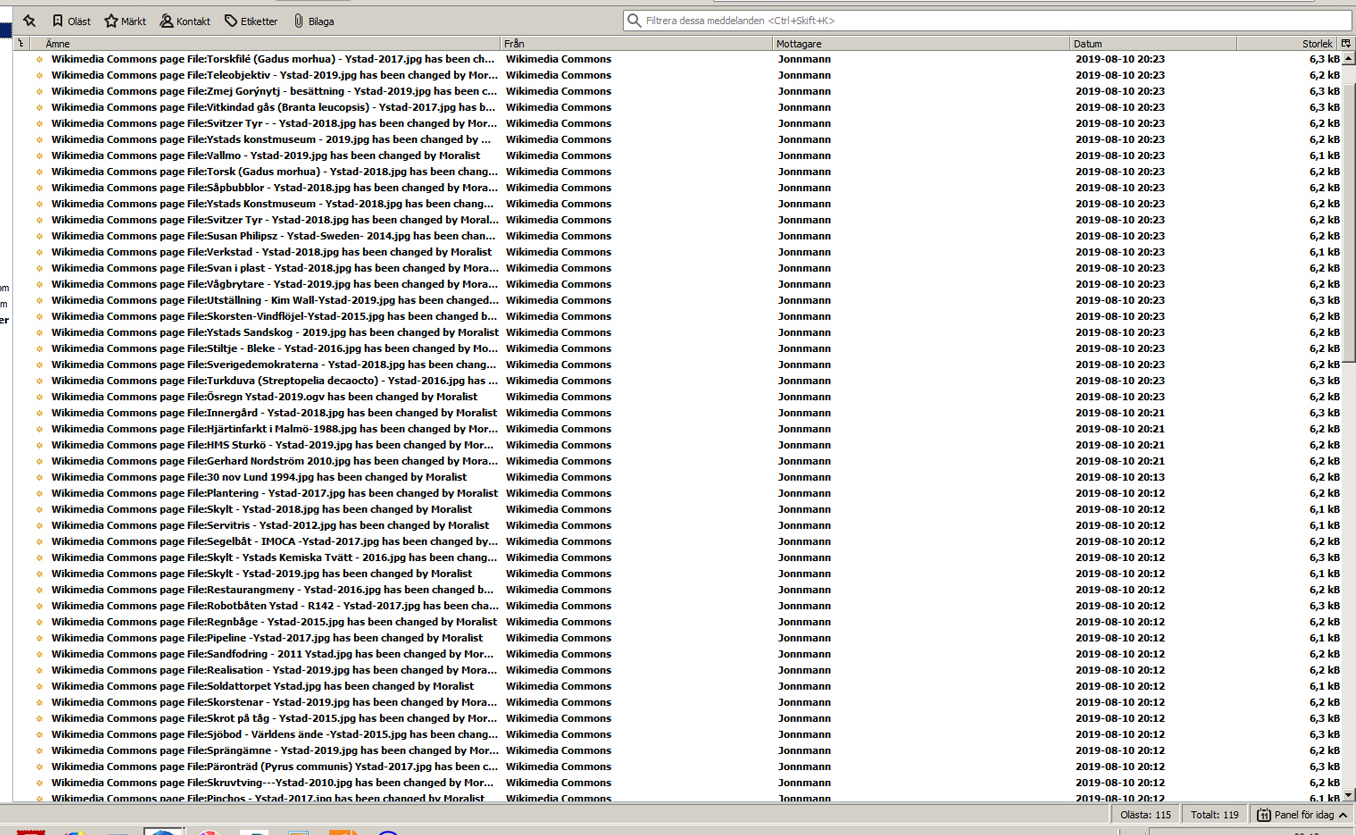
Servers and client applications
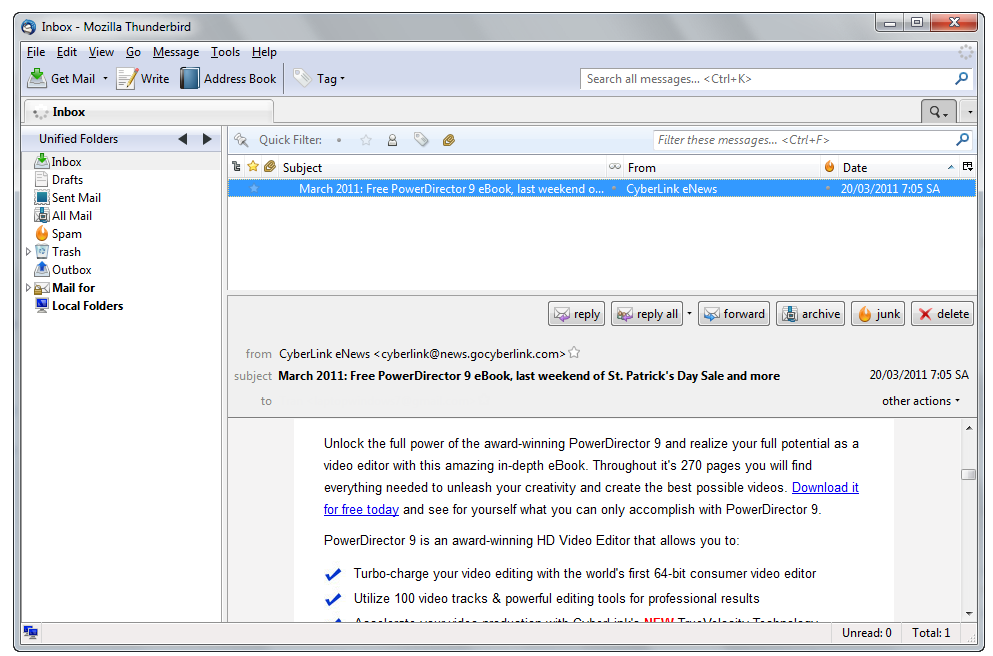 Messages are exchanged between hosts using the
Messages are exchanged between hosts using the Simple Mail Transfer Protocol
The Simple Mail Transfer Protocol (SMTP) is an Internet standard communication protocol for electronic mail transmission. Mail servers and other message transfer agents use SMTP to send and receive mail messages. User-level email clients typical ...
with software programs called mail transfer agent
The mail or post is a system for physically transporting postcards, letters, and parcels. A postal service can be private or public, though many governments place restrictions on private systems. Since the mid-19th century, national postal syst ...
s (MTAs); and delivered to a mail store by programs called mail delivery agent A message delivery agent (MDA), or mail delivery agent, is a computer software component that is responsible for the delivery of e-mail messages to a local recipient's mailbox., ''Internet Mail Architecture'', D. Crocker (July 2009) It is also call ...
s (MDAs, also sometimes called local delivery agents, LDAs). Accepting a message obliges an MTA to deliver it, and when a message cannot be delivered, that MTA must send a bounce message back to the sender, indicating the problem.
Users can retrieve their messages from servers using standard protocols such as POP or IMAP
In computing, the Internet Message Access Protocol (IMAP) is an Internet standard protocol used by email clients to retrieve email messages from a mail server over a TCP/IP connection. IMAP is defined by .
IMAP was designed with the goal of pe ...
, or, as is more likely in a large corporate
A corporation is an organization—usually a group of people or a company—authorized by the state to act as a single entity (a legal entity recognized by private and public law "born out of statute"; a legal person in legal context) and re ...
environment, with a proprietary protocol specific to Novell Groupwise
GroupWise is a messaging and collaboration platform from Micro Focus that supports email, calendaring, personal information management, instant messaging, and document management. The GroupWise platform consists of desktop client software, whi ...
, Lotus Notes
HCL Notes (formerly IBM Notes and Lotus Notes; see Branding below) and HCL Domino (formerly IBM Domino and Lotus Domino) are the client and server, respectively, of a collaborative client-server software platform formerly sold by IBM, now by HC ...
or Microsoft Exchange Server
Microsoft Exchange Server is a mail server and calendaring server developed by Microsoft. It runs exclusively on Windows Server operating systems.
The first version was called Exchange Server 4.0, to position it as the successor to the related ...
s. Programs used by users for retrieving, reading, and managing email are called mail user agent
The mail or post is a system for physically transporting postcards, letters, and parcels. A postal service can be private or public, though many governments place restrictions on private systems. Since the mid-19th century, national postal syst ...
s (MUAs).
When opening an email, it is marked as "read", which typically visibly distinguishes it from "unread" messages on clients' user interfaces. Email clients may allow hiding read emails from the inbox so the user can focus on the unread.
Mail can be stored on the client
Client(s) or The Client may refer to:
* Client (business)
* Client (computing), hardware or software that accesses a remote service on another computer
* Customer or client, a recipient of goods or services in return for monetary or other valuable ...
, on the server
Server may refer to:
Computing
* Server (computing), a computer program or a device that provides functionality for other programs or devices, called clients
Role
* Waiting staff, those who work at a restaurant or a bar attending customers and s ...
side, or in both places. Standard formats for mailboxes include Maildir
The Maildir e-mail format is a common way of storing email messages in which each message is stored in a separate file with a unique name, and each mail folder is a file system directory. The local file system handles file locking as messages are ...
and mbox
Mbox is a generic term for a family of related file formats used for holding collections of email messages. It was first implemented in Fifth Edition Unix.
All messages in an mbox mailbox are concatenated and stored as plain text in a single f ...
. Several prominent email clients use their own proprietary format and require conversion software to transfer email between them. Server-side storage is often in a proprietary format but since access is through a standard protocol such as IMAP
In computing, the Internet Message Access Protocol (IMAP) is an Internet standard protocol used by email clients to retrieve email messages from a mail server over a TCP/IP connection. IMAP is defined by .
IMAP was designed with the goal of pe ...
, moving email from one server to another can be done with any MUA supporting the protocol.
Many current email users do not run MTA, MDA or MUA programs themselves, but use a web-based email platform, such as Gmail
Gmail is a free email service provided by Google. As of 2019, it had 1.5 billion active users worldwide. A user typically accesses Gmail in a web browser or the official mobile app. Google also supports the use of email clients via the POP an ...
or Yahoo! Mail
Yahoo! Mail is an email service launched on October 8, 1997, by the American company Yahoo, Inc. The service is free for personal use, with an optional monthly fee for additional features. Business email was previously available with the Yahoo ...
, that performs the same tasks. Such webmail
Webmail (or web-based email) is an email service that can be accessed using a standard web browser. It contrasts with email service accessible through a specialised email client software. Examples of webmail providers are 1&1 Ionos, AOL Mail, G ...
interfaces allow users to access their mail with any standard web browser
A web browser is application software for accessing websites. When a user requests a web page from a particular website, the browser retrieves its files from a web server and then displays the page on the user's screen. Browsers are used on ...
, from any computer, rather than relying on a local email client.
Filename extensions
Upon reception of email messages, email client applications save messages in operating system files in the file system. Some clients save individual messages as separate files, while others use various database formats, often proprietary, for collective storage. A historical standard of storage is the ''mbox
Mbox is a generic term for a family of related file formats used for holding collections of email messages. It was first implemented in Fifth Edition Unix.
All messages in an mbox mailbox are concatenated and stored as plain text in a single f ...
'' format. The specific format used is often indicated by special filename extension
A filename extension, file name extension or file extension is a suffix to the name of a computer file (e.g., .txt, .docx, .md). The extension indicates a characteristic of the file contents or its intended use. A filename extension is typically d ...
s:
;eml
:Used by many email clients including Novell GroupWise
GroupWise is a messaging and collaboration platform from Micro Focus that supports email, calendaring, personal information management, instant messaging, and document management. The GroupWise platform consists of desktop client software, whi ...
, Microsoft Outlook Express, Lotus notes
HCL Notes (formerly IBM Notes and Lotus Notes; see Branding below) and HCL Domino (formerly IBM Domino and Lotus Domino) are the client and server, respectively, of a collaborative client-server software platform formerly sold by IBM, now by HC ...
, Windows Mail
Mail (formerly Windows Mail) is an email client developed by Microsoft and included in Windows Vista and later versions of Windows. The main function of Mail is sending and receiving email. It is available as the successor to Outlook Express, wh ...
, Mozilla Thunderbird
Mozilla Thunderbird is a free and open-source cross-platform email client, personal information manager, news client, RSS and chat client developed by the Mozilla Foundation and operated by subsidiary MZLA Technologies Corporation. The proje ...
, and Postbox. The files contain the email contents as plain text
In computing, plain text is a loose term for data (e.g. file contents) that represent only characters of readable material but not its graphical representation nor other objects ( floating-point numbers, images, etc.). It may also include a lim ...
in MIME
Multipurpose Internet Mail Extensions (MIME) is an Internet standard that extends the format of email messages to support text in character sets other than ASCII, as well as attachments of audio, video, images, and application programs. Message ...
format, containing the email header and body, including attachments in one or more of several formats.
;emlx
:Used by Apple Mail
Apple Mail (officially known as Mail) is an email client included by Apple Inc. with its operating systems macOS, iOS, iPadOS and watchOS. Apple Mail grew out of NeXTMail, which was originally developed by NeXT as part of its NeXTSTEP operatin ...
.
;msg
:Used by Microsoft Office Outlook and OfficeLogic Groupware.
;mbx
:Used by Opera Mail
Opera Mail (formerly known as M2) is the email and news client developed by Opera Software. It was an integrated component within the Opera web browser from version 2 through 12. With the release of Opera 15 in 2013, Opera Mail became a separate p ...
, KMail
Kontact is a personal information manager and groupware software suite developed by KDE. It supports calendars, contacts, notes, to-do lists, news, and email. It offers a number of inter-changeable graphical UIs (KMail, KAddressBook, Akregator, ...
, and Apple Mail
Apple Mail (officially known as Mail) is an email client included by Apple Inc. with its operating systems macOS, iOS, iPadOS and watchOS. Apple Mail grew out of NeXTMail, which was originally developed by NeXT as part of its NeXTSTEP operatin ...
based on the mbox
Mbox is a generic term for a family of related file formats used for holding collections of email messages. It was first implemented in Fifth Edition Unix.
All messages in an mbox mailbox are concatenated and stored as plain text in a single f ...
format.
Some applications (like Apple Mail
Apple Mail (officially known as Mail) is an email client included by Apple Inc. with its operating systems macOS, iOS, iPadOS and watchOS. Apple Mail grew out of NeXTMail, which was originally developed by NeXT as part of its NeXTSTEP operatin ...
) leave attachments encoded in messages for searching while also saving separate copies of the attachments. Others separate attachments from messages and save them in a specific directory.
URI scheme mailto
TheURI scheme
A Uniform Resource Identifier (URI) is a unique sequence of characters that identifies a logical or physical resource used by web technologies. URIs may be used to identify anything, including real-world objects, such as people and places, conc ...
, as registered with the IANA
The Internet Assigned Numbers Authority (IANA) is a standards organization that oversees global IP address allocation, autonomous system number allocation, root zone management in the Domain Name System (DNS), media types, and other Interne ...
, defines the mailto: scheme for SMTP email addresses. Though its use is not strictly defined, URLs of this form are intended to be used to open the new message window of the user's mail client when the URL is activated, with the address as defined by the URL in the ''To:'' field. Many clients also support query string parameters for the other email fields, such as its subject line or carbon copy recipients.
Types
Web-based email
Many email providers have a web-based email client. This allows users to log into the email account by using any compatibleweb browser
A web browser is application software for accessing websites. When a user requests a web page from a particular website, the browser retrieves its files from a web server and then displays the page on the user's screen. Browsers are used on ...
to send and receive their email. Mail is typically not downloaded to the web client, so can't be read without a current Internet connection.
POP3 email servers
ThePost Office Protocol
In computing, the Post Office Protocol (POP) is an application-layer Internet standard protocol used by e-mail clients to retrieve e-mail from a mail server. POP version 3 (POP3) is the version in common use, and along with IMAP the most common ...
3 (POP3) is a mail access protocol used by a client application to read messages from the mail server. Received messages are often deleted from the server
Server may refer to:
Computing
* Server (computing), a computer program or a device that provides functionality for other programs or devices, called clients
Role
* Waiting staff, those who work at a restaurant or a bar attending customers and s ...
. POP supports simple download-and-delete requirements for access to remote mailboxes (termed maildrop in the POP RFC's). POP3 allows you to download email messages on your local computer and read them even when you are offline.
IMAP email servers
TheInternet Message Access Protocol
In computing, the Internet Message Access Protocol (IMAP) is an Internet standard protocol used by email clients to retrieve email messages from a mail server over a TCP/IP connection. IMAP is defined by .
IMAP was designed with the goal of p ...
(IMAP) provides features to manage a mailbox from multiple devices. Small portable devices like smartphone
A smartphone is a portable computer device that combines mobile telephone and computing functions into one unit. They are distinguished from feature phones by their stronger hardware capabilities and extensive mobile operating systems, which ...
s are increasingly used to check email while traveling and to make brief replies, larger devices with better keyboard access being used to reply at greater length. IMAP shows the headers of messages, the sender and the subject and the device needs to request to download specific messages. Usually, the mail is left in folders in the mail server.
MAPI email servers
Messaging Application Programming Interface
Messaging Application Programming Interface (MAPI) is an API for Microsoft Windows which allows programs to become email-aware. While MAPI is designed to be independent of the protocol, it is usually used to communicate with Microsoft Exchange Ser ...
(MAPI) is used by Microsoft Outlook to communicate to Microsoft Exchange Server
Microsoft Exchange Server is a mail server and calendaring server developed by Microsoft. It runs exclusively on Windows Server operating systems.
The first version was called Exchange Server 4.0, to position it as the successor to the related ...
- and to a range of other email server products such as Axigen Mail Server, Kerio Connect
Kerio Technologies, Inc. is a former technology company specializing in collaboration software and unified threat management for small and medium organizations. Founded in 2001, Kerio is headquartered in San Jose, California. In January 2017, GFI ...
, Scalix
Scalix is an e-mail and groupware server that runs on Linux, licensed under the Scalix Public License (SPL).
The software provides e-mail, group calendaring and other collaborative software, which are standard in groupware. It can be also be ac ...
, Zimbra
Zimbra Collaboration, formerly known as the Zimbra Collaboration Suite (ZCS) before 2019, is a collaborative software suite that includes an email server and a web client.
Zimbra was initially developed by LiquidSys, which changed their nam ...
, HP OpenMail HP OpenMail, also known simply as OpenMail, was an enterprise email messaging and collaboration product from Hewlett-Packard.
It was known for its ability to interconnect several other APIs and protocols, including MAPI, cc:Mail, SMTP and MIME, an ...
, IBM Lotus Notes
HCL Notes (formerly IBM Notes and Lotus Notes; see Branding below) and HCL Domino (formerly IBM Domino and Lotus Domino) are the client and server, respectively, of a collaborative client-server software platform formerly sold by IBM, now by HC ...
, Zarafa, and Bynari
Bynari is a defunct company based in Dallas, developing server and email software, mainly known for its Insight Family, similar to Microsoft Exchange Server with Outlook.
Development of the products is a joint effort with various OEM partners.
In ...
where vendors have added MAPI support to allow their products to be accessed directly via Outlook.
Uses
Business and organizational use
Email has been widely accepted by businesses, governments and non-governmental organizations in the developed world, and it is one of the key parts of an 'e-revolution' in workplace communication (with the other key plank being widespread adoption of highspeedInternet
The Internet (or internet) is the global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a '' network of networks'' that consists of private, pub ...
). A sponsored 2010 study on workplace communication found 83% of U.S. knowledge workers felt email was critical to their success and productivity at work.By Om Malik, GigaOm.Is Email a Curse or a Boon?
" September 22, 2010. Retrieved October 11, 2010. It has some key benefits to business and other organizations, including: ; Facilitating logistics : Much of the business world relies on communications between people who are not physically in the same building, area, or even country; setting up and attending an in-person meeting,
telephone call
A telephone call is a connection over a telephone network between the called party and the calling party.
First telephone call
The first telephone call was made on March 10, 1876, by Alexander Graham Bell. Bell demonstrated his ability to "ta ...
, or conference call
A conference call is a telephone call in which someone talks to several people at the same time. The conference call may be designed to allow the called party to participate during the call or set up so that the called party merely listens into ...
can be inconvenient, time-consuming, and costly. Email provides a method of exchanging information between two or more people with no set-up costs and that is generally far less expensive than a physical meeting or phone call.
; Helping with synchronization
: With real time communication by meetings or phone calls, participants must work on the same schedule, and each participant must spend the same amount of time in the meeting or call. Email allows asynchrony: each participant may control their schedule independently. Batch processing of incoming emails can improve workflow compared to interrupting calls.
; Reducing cost
: Sending an email is much less expensive than sending postal mail, or long distance telephone call
In telecommunications, a long-distance call (U.S.) or trunk call (also known as a toll call in the U.K. ) is a telephone call made to a location outside a defined local calling area. Long-distance calls are typically charged a higher billing rat ...
s, telex
The telex network is a station-to-station switched network of teleprinters similar to a telephone network, using telegraph-grade connecting circuits for two-way text-based messages. Telex was a major method of sending written messages electroni ...
or telegrams
Telegraphy is the long-distance transmission of messages where the sender uses symbolic codes, known to the recipient, rather than a physical exchange of an object bearing the message. Thus flag semaphore is a method of telegraphy, whereas p ...
.
; Increasing speed
: Much faster than most of the alternatives.
; Creating a "written" record
: Unlike a telephone or in-person conversation, email by its nature creates a detailed written record of the communication, the identity of the sender(s) and recipient(s) and the date and time the message was sent. In the event of a contract or legal dispute, saved emails can be used to prove that an individual was advised of certain issues, as each email has the date and time recorded on it.
; Possibility of auto-processing and improved distribution
: As well pre-processing of customer's orders and/or addressing the person in charge can be realized by automated procedures.
Email marketing
Email marketing
Email marketing is the act of sending a commercial message, typically to a group of people, using email. In its broadest sense, every email sent to a potential or current customer could be considered email marketing. It involves using email to s ...
via "opt-in
Opt-in email is a term used when someone is not initially added to an emailing list and is instead given the option to join the emailing list. Typically, this is some sort of mailing list, newsletter, or advertising. Opt-out emails do not ask ...
" is often successfully used to send special sales offerings and new product information. Depending on the recipient's culture, email sent without permission—such as an "opt-in"—is likely to be viewed as unwelcome "email spam
Email spam, also referred to as junk email, spam mail, or simply spam, is unsolicited messages sent in bulk by email (spamming).
The name comes from a Monty Python sketch in which the name of the canned pork product Spam is ubiquitous, unavoida ...
".
Personal use
Personal computer
Many users access their personal emails from friends and family members using apersonal computer
A personal computer (PC) is a multi-purpose microcomputer whose size, capabilities, and price make it feasible for individual use. Personal computers are intended to be operated directly by an end user, rather than by a computer expert or techn ...
in their house or apartment.
Mobile
Email has become used onsmartphone
A smartphone is a portable computer device that combines mobile telephone and computing functions into one unit. They are distinguished from feature phones by their stronger hardware capabilities and extensive mobile operating systems, which ...
s and on all types of computers. Mobile "apps" for email increase accessibility to the medium for users who are out of their homes. While in the earliest years of email, users could only access email on desktop computers, in the 2010s, it is possible for users to check their email when they are away from home, whether they are across town or across the world. Alerts can also be sent to the smartphone or other devices to notify them immediately of new messages. This has given email the ability to be used for more frequent communication between users and allowed them to check their email and write messages throughout the day. , there were approximately 1.4 billion email users worldwide and 50 billion non-spam emails that were sent daily.
Individuals often check emails on smartphones for both personal and work-related messages. It was found that US adults check their email more than they browse the web or check their Facebook
Facebook is an online social media and social networking service owned by American company Meta Platforms. Founded in 2004 by Mark Zuckerberg with fellow Harvard College students and roommates Eduardo Saverin, Andrew McCollum, Dustin Mosk ...
accounts, making email the most popular activity for users to do on their smartphones. 78% of the respondents in the study revealed that they check their email on their phone. It was also found that 30% of consumers use only their smartphone to check their email, and 91% were likely to check their email at least once per day on their smartphone. However, the percentage of consumers using email on a smartphone ranges and differs dramatically across different countries. For example, in comparison to 75% of those consumers in the US who used it, only 17% in India did.
Declining use among young people
, the number of Americans visiting email web sites had fallen 6 percent after peaking in November 2009. For persons 12 to 17, the number was down 18 percent. Young people preferredinstant messaging
Instant messaging (IM) technology is a type of online chat allowing real-time text transmission over the Internet or another computer network. Messages are typically transmitted between two or more parties, when each user inputs text and trigg ...
, texting
Text messaging, or texting, is the act of composing and sending electronic messages, typically consisting of alphabetic and numeric characters, between two or more users of mobile devices, desktops/laptops, or another type of compatible compute ...
and social media
Social media are interactive media technologies that facilitate the creation and sharing of information, ideas, interests, and other forms of expression through virtual communities and networks. While challenges to the definition of ''social me ...
. Technology writer Matt Richtel said in ''The New York Times
''The New York Times'' (''the Times'', ''NYT'', or the Gray Lady) is a daily newspaper based in New York City with a worldwide readership reported in 2020 to comprise a declining 840,000 paid print subscribers, and a growing 6 million paid ...
'' that email was like the VCR
A videocassette recorder (VCR) or video recorder is an electromechanical device that records analog audio and analog video from broadcast television or other source on a removable, magnetic tape videocassette, and can play back the recordin ...
, vinyl record
A phonograph record (also known as a gramophone record, especially in British English), or simply a record, is an analog sound storage medium in the form of a flat disc with an inscribed, modulated spiral groove. The groove usually starts near ...
s and film cameras
A movie camera (also known as a film camera and cine-camera) is a type of photographic camera that rapidly takes a sequence of photographs, either on an image sensor or onto film stock, in order to produce a moving image to project onto a movie s ...
—no longer cool and something older people do.
A 2015 survey of Android users showed that persons 13 to 24 used messaging apps 3.5 times as much as those over 45, and were far less likely to use email.
Issues
Attachment size limitation
Email messages may have one or more attachments, which are additional files that are appended to the email. Typical attachments includeMicrosoft Word
Microsoft Word is a word processor, word processing software developed by Microsoft. It was first released on October 25, 1983, under the name ''Multi-Tool Word'' for Xenix systems. Subsequent versions were later written for several other pla ...
documents, PDF
Portable Document Format (PDF), standardized as ISO 32000, is a file format developed by Adobe in 1992 to present documents, including text formatting and images, in a manner independent of application software, hardware, and operating systems ...
documents, and scanned images of paper documents. In principle, there is no technical restriction on the size or number of attachments. However, in practice, email clients, server
Server may refer to:
Computing
* Server (computing), a computer program or a device that provides functionality for other programs or devices, called clients
Role
* Waiting staff, those who work at a restaurant or a bar attending customers and s ...
s, and Internet service providers implement various limitations on the size of files, or complete email – typically to 25MB or less. Furthermore, due to technical reasons, attachment sizes as seen by these transport systems can differ from what the user sees, which can be confusing to senders when trying to assess whether they can safely send a file by email. Where larger files need to be shared, various file hosting service
A file-hosting service, cloud-storage service, online file-storage provider, or cyberlocker is an internet hosting service specifically designed to host user files. It allows users to upload files that could be accessed over the internet afte ...
s are available and commonly used.
Information overload
The ubiquity of email for knowledge workers and "white collar" employees has led to concerns that recipients face an "information overload
Information overload (also known as infobesity, infoxication, information anxiety, and information explosion) is the difficulty in understanding an issue and effectively making decisions when one has too much information (TMI) about that issue, ...
" in dealing with increasing volumes of email. With the growth in mobile devices, by default employees may also receive work-related emails outside of their working day. This can lead to increased stress and decreased satisfaction with work. Some observers even argue it could have a significant negative economic effect, as efforts to read the many emails could reduce productivity
Productivity is the efficiency of production of goods or services expressed by some measure. Measurements of productivity are often expressed as a ratio of an aggregate output to a single input or an aggregate input used in a production proces ...
.
Spam
Email "spam" is unsolicited bulk email. The low cost of sending such email meant that, by 2003, up to 30% of total email traffic was spam,Rich Kawanagh. The top ten email spam list of 2005. ITVibe news, 2006, January 02ITvibe.com
and was threatening the usefulness of email as a practical tool. The US
CAN-SPAM Act of 2003
The Controlling the Assault of Non-Solicited Pornography And Marketing (CAN-SPAM) Act of 2003 is a law passed in 2003 establishing the United States' first national standards for the sending of commercial e-mail. The law requires the Federal Trad ...
and similar laws elsewhere had some impact, and a number of effective anti-spam techniques
Various anti-spam techniques are used to prevent email spam (unsolicited bulk email).
No technique is a complete solution to the spam problem, and each has trade-offs between incorrectly rejecting legitimate email (false positives) as opposed to ...
now largely mitigate the impact of spam by filtering or rejecting it for most users, but the volume sent is still very high—and increasingly consists not of advertisements for products, but malicious content or links."Spam and phishing in Q1 2016", May 12, 2016, securelist.com In September 2017, for example, the proportion of spam to legitimate email rose to 59.56%. The percentage of spam email in 2021 is estimated to be 85%.
Malware
A range of malicious email types exist. These range from various types of email scams, including "social engineering" scams such asadvance-fee scam
An advance-fee scam is a form of fraud and is one of the most common types of confidence tricks. The scam typically involves promising the victim a significant share of a large sum of money, in return for a small up-front payment, which the frauds ...
"Nigerian letters", to phishing
Phishing is a type of social engineering where an attacker sends a fraudulent (e.g., spoofed, fake, or otherwise deceptive) message designed to trick a person into revealing sensitive information to the attacker or to deploy malicious softwar ...
, email bomb
On Internet usage, an email bomb is a form of net abuse that sends large volumes of email to an address to overflow the mailbox, overwhelm the server where the email address is hosted in a denial-of-service attack (DoS attack) or as a smoke scre ...
ardment and email worms.
Email spoofing
Email spoofing
Email spoofing is the creation of email messages with a forged sender address. The term applies to email purporting to be from an address which is not actually the sender's; mail sent in reply to that address may bounce or be delivered to an unre ...
occurs when the email message header is designed to make the message appear to come from a known or trusted source. Email spam
Email spam, also referred to as junk email, spam mail, or simply spam, is unsolicited messages sent in bulk by email (spamming).
The name comes from a Monty Python sketch in which the name of the canned pork product Spam is ubiquitous, unavoida ...
and phishing
Phishing is a type of social engineering where an attacker sends a fraudulent (e.g., spoofed, fake, or otherwise deceptive) message designed to trick a person into revealing sensitive information to the attacker or to deploy malicious softwar ...
methods typically use spoofing to mislead the recipient about the true message origin. Email spoofing may be done as a prank, or as part of a criminal effort to defraud an individual or organization. An example of a potentially fraudulent email spoofing is if an individual creates an email that appears to be an invoice from a major company, and then sends it to one or more recipients. In some cases, these fraudulent emails incorporate the logo of the purported organization and even the email address may appear legitimate.
Email bombing
Email bomb
On Internet usage, an email bomb is a form of net abuse that sends large volumes of email to an address to overflow the mailbox, overwhelm the server where the email address is hosted in a denial-of-service attack (DoS attack) or as a smoke scre ...
ing is the intentional sending of large volumes of messages to a target address. The overloading of the target email address can render it unusable and can even cause the mail server to crash.
Privacy concerns
Today it can be important to distinguish between the Internet and internal email systems. Internet email may travel and be stored on networks and computers without the sender's or the recipient's control. During the transit time it is possible that third parties read or even modify the content. Internal mail systems, in which the information never leaves the organizational network, may be more secure, althoughinformation technology
Information technology (IT) is the use of computers to create, process, store, retrieve, and exchange all kinds of data . and information. IT forms part of information and communications technology (ICT). An information technology system (I ...
personnel and others whose function may involve monitoring or managing may be accessing the email of other employees.
Email privacy, without some security precautions, can be compromised because:
* email messages are generally not encrypted.
* email messages have to go through intermediate computers before reaching their destination, meaning it is relatively easy for others to intercept and read messages.
* many Internet Service Providers (ISP) store copies of email messages on their mail servers before they are delivered. The backups of these can remain for up to several months on their server, despite deletion from the mailbox.
* the "Received:"-fields and other information in the email can often identify the sender, preventing anonymous communication.
* web bug
A web beaconAlso called web bug, tracking bug, tag, web tag, page tag, tracking pixel, pixel tag, 1×1 GIF, or clear GIF. is a technique used on web pages and email to unobtrusively (usually invisibly) allow checking that a user has accessed s ...
s invisibly embedded in HTML content can alert the sender of any email whenever an email is rendered as HTML (some e-mail clients do this when the user reads, or re-reads the e-mail) and from which IP address. It can also reveal whether an email was read on a smartphone or a PC, or Apple Mac device via the user agent string
In computing, a user agent is any software, acting on behalf of a user, which "retrieves, renders and facilitates end-user interaction with Web content". A user agent is therefore a special kind of software agent.
Some prominent examples of u ...
.
There are cryptography
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adve ...
applications that can serve as a remedy to one or more of the above. For example, Virtual Private Network
A virtual private network (VPN) extends a private network across a public network and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network. The be ...
s or the Tor network can be used to encrypt traffic from the user machine to a safer network while GPG, PGP, SMEmail, or S/MIME S/MIME (Secure/Multipurpose Internet Mail Extensions) is a standard for public key encryption and signing of MIME data. S/MIME is on an IETF standards track and defined in a number of documents, most importantly . It was originally developed by ...
can be used for end-to-end message encryption, and SMTP STARTTLS or SMTP over Transport Layer Security
Transport Layer Security (TLS) is a cryptographic protocol designed to provide communications security over a computer network. The protocol is widely used in applications such as email, instant messaging, and voice over IP, but its use in secu ...
/Secure Sockets Layer can be used to encrypt communications for a single mail hop between the SMTP client and the SMTP server.
Additionally, many mail user agent
The mail or post is a system for physically transporting postcards, letters, and parcels. A postal service can be private or public, though many governments place restrictions on private systems. Since the mid-19th century, national postal syst ...
s do not protect logins and passwords, making them easy to intercept by an attacker. Encrypted authentication schemes such as SASL prevent this. Finally, the attached files share many of the same hazards as those found in peer-to-peer filesharing. Attached files may contain trojans
Trojan or Trojans may refer to:
* Of or from the ancient city of Troy
* Trojan language, the language of the historical Trojans
Arts and entertainment Music
* ''Les Troyens'' ('The Trojans'), an opera by Berlioz, premiered part 1863, part 189 ...
or viruses
A virus is a submicroscopic infectious agent that replicates only inside the living cells of an organism. Viruses infect all life forms, from animals and plants to microorganisms, including bacteria and archaea.
Since Dmitri Ivanovsky's ...
.
Legal contracts
It is possible for an exchange of emails to form a binding contract, so users must be careful about what they send through email correspondence. A signature block on an email may be interpreted as satisfying a signature requirement for a contract.Flaming
Flaming occurs when a person sends a message (or many messages) with angry or antagonistic content. The term is derived from the use of the word ''incendiary'' to describe particularly heated email discussions. The ease and impersonality of email communications mean that thesocial norms
Social norms are shared standards of acceptable behavior by groups. Social norms can both be informal understandings that govern the behavior of members of a society, as well as be codified into rules and laws. Social normative influences or soc ...
that encourage civility in person or via telephone do not exist and civility may be forgotten.
Email bankruptcy
Also known as "email fatigue", email bankruptcy is when a user ignores a large number of email messages after falling behind in reading and answering them. The reason for falling behind is often due to information overload and a general sense there is so much information that it is not possible to read it all. As a solution, people occasionally send a "boilerplate" message explaining that their email inbox is full, and that they are in the process of clearing out all the messages.Harvard University
Harvard University is a private Ivy League research university in Cambridge, Massachusetts. Founded in 1636 as Harvard College and named for its first benefactor, the Puritan clergyman John Harvard, it is the oldest institution of higher le ...
law professor Lawrence Lessig
Lester Lawrence Lessig III (born June 3, 1961) is an American academic, attorney, and political activist. He is the Roy L. Furman Professor of Law at Harvard Law School and the former director of the Edmond J. Safra Center for Ethics at Harvar ...
is credited with coining this term, but he may only have popularized it.
Internationalization
Originally Internet email was completely ASCII text-based. MIME now allows body content text and some header content text in international character sets, but other headers and email addresses using UTF-8, while standardized have yet to be widely adopted.Tracking of sent mail
The original SMTP mail service provides limited mechanisms for tracking a transmitted message, and none for verifying that it has been delivered or read. It requires that each mail server must either deliver it onward or return a failure notice (bounce message), but both software bugs and system failures can cause messages to be lost. To remedy this, theIETF
The Internet Engineering Task Force (IETF) is a standards organization for the Internet and is responsible for the technical standards that make up the Internet protocol suite (TCP/IP). It has no formal membership roster or requirements and a ...
introduced Delivery Status Notifications (delivery receipts) and Message Disposition Notifications (return receipts); however, these are not universally deployed in production.
Many ISPs now deliberately disable non-delivery reports (NDRs) and delivery receipts due to the activities of spammers:
* Delivery Reports can be used to verify whether an address exists and if so, this indicates to a spammer that it is available to be spammed.
* If the spammer uses a forged sender email address (email spoofing
Email spoofing is the creation of email messages with a forged sender address. The term applies to email purporting to be from an address which is not actually the sender's; mail sent in reply to that address may bounce or be delivered to an unre ...
), then the innocent email address that was used can be flooded with NDRs from the many invalid email addresses the spammer may have attempted to mail. These NDRs then constitute spam from the ISP to the innocent user.
In the absence of standard methods, a range of system based around the use of web bug
A web beaconAlso called web bug, tracking bug, tag, web tag, page tag, tracking pixel, pixel tag, 1×1 GIF, or clear GIF. is a technique used on web pages and email to unobtrusively (usually invisibly) allow checking that a user has accessed s ...
s have been developed. However, these are often seen as underhand or raising privacy concerns, and only work with email clients that support rendering of HTML. Many mail clients now default to not showing "web content". Webmail
Webmail (or web-based email) is an email service that can be accessed using a standard web browser. It contrasts with email service accessible through a specialised email client software. Examples of webmail providers are 1&1 Ionos, AOL Mail, G ...
providers can also disrupt web bugs by pre-caching images., Ron Amadeo, Dec 13 2013, Ars Technica
See also
*Anonymous remailer
An anonymous remailer is a server that receives messages with embedded instructions on where to send them next, and that forwards them without revealing where they originally came from. There are cypherpunk anonymous remailers, mixmaster anonym ...
* Anti-spam techniques
Various anti-spam techniques are used to prevent email spam (unsolicited bulk email).
No technique is a complete solution to the spam problem, and each has trade-offs between incorrectly rejecting legitimate email (false positives) as opposed to ...
* biff
* Bounce message
* Comparison of email clients
* Dark Mail Alliance
* Disposable email address
* E-card
E-card is an electronic postcard or greeting card, with the primary difference being that it is created using digital media instead of paper or other traditional materials. E-cards are made available many different ways, usually on various Intern ...
* Electronic mailing list
A mailing list is a collection of names and addresses used by an individual or an organization to send material to multiple recipients. The term is often extended to include the people subscribed to such a list, so the group of subscribers is re ...
* Email art
* Email authentication Email authentication, or validation, is a collection of techniques aimed at providing verifiable information about the origin of email messages by validating the domain ownership of any message transfer agents (MTA) who participated in transferring ...
* Email digest
An email digest is an email that is automatically generated by an electronic mailing list and which combines all exchanged emails during a time period (e.g. day, week, month, etc.) or when a volume limit is reached (e.g. every 10 or 100 messages) i ...
* Email encryption Email encryption is encryption of email messages to protect the content from being read by entities other than the intended recipients. Email encryption may also include authentication.
Email is prone to the disclosure of information. Most emails a ...
* Email hosting service
* Email storm
An email storm (also called a reply all storm or sometimes reply allpocalypse) is a sudden spike of "reply all" messages on an email distribution list, usually caused by a controversial or misdirected message. Such storms can start when even ...
* Email tracking
Email tracking is a method for monitoring whether the email messages is read by the intended recipient. Most tracking technologies use some form of digitally time-stamped record to reveal the exact time and date that an email was received or open ...
* HTML email
HTML email is the use of a subset of HTML to provide formatting and semantic markup capabilities in email that are not available with plain text: Text can be linked without displaying a URL, or breaking long URLs into multiple pieces. Text is wra ...
* Information overload
Information overload (also known as infobesity, infoxication, information anxiety, and information explosion) is the difficulty in understanding an issue and effectively making decisions when one has too much information (TMI) about that issue, ...
* Internet fax
Internet fax, e-fax, or online fax is the use of the internet and internet protocols to send a fax (facsimile), rather than using a standard telephone connection and a fax machine. A distinguishing feature of Internet fax, compared to other Intern ...
* Internet mail standard Internet e-mail functions through the use of Internet Standards. Although many more standards actually apply to e-mail, virtually all mail servers and e-mail clients support at least the following basic set.
* SMTP (or ) specifies the protocol by w ...
s
* List of email subject abbreviations
This is a list of commonly and uncommonly used abbreviations that are used in the subject of an English-language email header.
Standard prefixes
These prefixes are usually automatically inserted by the email client.
* RE: or "Re:" followed ...
* MCI Mail MCI Mail was one of the first ever commercial email services in the United States and one of the largest telecommunication services in the world. Operated by MCI Communications Corp. from 1983 to 2003, MCI Mail offered its customers a low cost and ...
* Netiquette
Etiquette in technology, colloquially referred to as netiquette is a term used to refer to the unofficial code of policies that encourage good behavior on the Internet which is used to regulate respect and polite behavior on social media platforms ...
* Posting style
When a message is replied to in e-mail, Internet forums, or Usenet, the original can often be included, or "quoted", in a variety of different posting styles.
The main options are interleaved posting (also called inline replying, in which the di ...
* Privacy-enhanced Electronic Mail
Privacy-Enhanced Mail (PEM) is a de facto file format for storing and sending cryptographic keys, certificates, and other data, based on a set of 1993 IETF standards defining "privacy-enhanced mail." While the original standards were never broa ...
* Push email
Push email is an email system that provides an always-on capability, in which new email is actively transferred ( pushed) as it arrives by the mail delivery agent (MDA) (commonly called mail server) to the mail user agent (MUA), also called the ema ...
* RSS
RSS ( RDF Site Summary or Really Simple Syndication) is a web feed that allows users and applications to access updates to websites in a standardized, computer-readable format. Subscribing to RSS feeds can allow a user to keep track of many d ...
* Telegraphy
Telegraphy is the long-distance transmission of messages where the sender uses symbolic codes, known to the recipient, rather than a physical exchange of an object bearing the message. Thus flag semaphore is a method of telegraphy, whereas p ...
* Unicode and email Many email clients now offer some support for Unicode. Some clients will automatically choose between a legacy encoding and Unicode depending on the mail's content, either automatically or when the user requests it.
Technical requirements for sendi ...
* Usenet quoting
When Usenet and e-mail users respond to a message, they often want to include some context for the discussion. This is often accomplished by quoting a portion of the original message using Usenet conventions. In essence the convention is to communi ...
* Webmail
Webmail (or web-based email) is an email service that can be accessed using a standard web browser. It contrasts with email service accessible through a specialised email client software. Examples of webmail providers are 1&1 Ionos, AOL Mail, G ...
, Comparison of webmail providers
* X-Originating-IP The X-Originating-IP (not to be confused with X-Forwarded-For) email header field is a de facto standard for identifying the originating IP address of a client connecting to a mail service's HTTP frontend. When clients connect directly to a mail ...
* X.400
X.400 is a suite of ITU-T Recommendations that defines the ITU-T Message Handling System (MHS).
At one time, the designers of X.400 were expecting it to be the predominant form of email, but this role has been taken by the SMTP-based Internet e-m ...
* Yerkish
Yerkish is an artificial language developed for use by non-human primates. It employs a keyboard whose keys contain ''lexigrams'', symbols corresponding to objects or ideas.
Lexigrams were notably used by the Georgia State University Language Res ...
Notes
References
Further reading
* Cemil Betanov, ''Introduction to X.400'', Artech House, . * Marsha Egan,Inbox Detox and The Habit of Email Excellence
", Acanthus Publishing * Lawrence Hughes, ''Internet e-mail Protocols, Standards and Implementation'', Artech House Publishers, . * Kevin Johnson, ''Internet Email Protocols: A Developer's Guide'', Addison-Wesley Professional, . * Pete Loshin, ''Essential Email Standards: RFCs and Protocols Made Practical'', John Wiley & Sons, . * * Sara Radicati, ''Electronic Mail: An Introduction to the X.400 Message Handling Standards'', Mcgraw-Hill, . * John Rhoton, ''Programmer's Guide to Internet Mail: SMTP, POP, IMAP, and LDAP'', Elsevier, . * John Rhoton, ''X.400 and SMTP: Battle of the E-mail Protocols'', Elsevier, . * David Wood, ''Programming Internet Mail'', O'Reilly, .
External links
The History of Email
is Dave Crocker's attempt at capturing the sequence of 'significant' occurrences in the evolution of email; a collaborative effort that also cites this page.
is a personal memoir by the implementer of an early email system
A Look at the Origins of Network Email
is a short, yet vivid recap of the key historical facts
Business E-Mail Compromise - An Emerging Global Threat
FBI
The Federal Bureau of Investigation (FBI) is the domestic intelligence and security service of the United States and its principal federal law enforcement agency. Operating under the jurisdiction of the United States Department of Justice, t ...
Explained from first principles
a 2021 article attempting to summarize more than 100 RFCs {{DEFAULTSORT:Email Internet terminology
Mail
The mail or post is a system for physically transporting postcards, letters, and parcels. A postal service can be private or public, though many governments place restrictions on private systems. Since the mid-19th century, national postal sys ...
History of the Internet
Computer-related introductions in 1971