carrier cloud on:
[Wikipedia]
[Google]
[Amazon]
In
RFC 5693: Application-Layer Traffic Optimization (ALTO) Problem Statement
/ref> * ''High level of security and governance'': Cloud application providers are subject to general and domain specific security, privacy, and governance requirements and regulations, such as the European Data Protection Directive and the U.S. Health Insurance Portability and Accountability Act. For added security, the wide area network of the carrier cloud can provide segregated encrypted or unencrypted network links that are not accessible from the general Internet. At the data center, the carrier cloud provides e.g. virtual private servers, management processes, logs and documentation to fulfill security and governance rules. * ''Location control'': Fundamentally, cloud users should not be concerned with the geographic location of their cloud resources. However, privacy and other regulations may mandate that certain types of data must not be sent outside a national jurisdiction or other geographical region. * ''Open APIs'': Carrier clouds provide
cloud computing
Cloud computing is the on-demand availability of computer system resources, especially data storage ( cloud storage) and computing power, without direct active management by the user. Large clouds often have functions distributed over mu ...
a carrier cloud is a class of cloud that integrates wide area network
A wide area network (WAN) is a telecommunications network that extends over a large geographic area. Wide area networks are often established with leased telecommunication circuits.
Businesses, as well as schools and government entities, u ...
s (WAN) and other attributes of communications service provider
A telephone company, also known as a telco, telephone service provider, or telecommunications operator, is a kind of communications service provider (CSP), more precisely a telecommunications service provider (TSP), that provides telecommunic ...
s’ carrier grade networks to enable the deployment of highly complex applications in the cloud. In contrast, classic cloud computing focuses on the data center, and does not address the network connecting data centers and cloud users. This may result in unpredictable response times and security issues when business critical data are transferred over the Internet
The Internet (or internet) is the global system of interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a '' network of networks'' that consists of private, p ...
.
History
The advent ofvirtualization
In computing, virtualization or virtualisation (sometimes abbreviated v12n, a numeronym) is the act of creating a virtual (rather than actual) version of something at the same abstraction level, including virtual computer hardware platforms, stor ...
technology and cost effective computing hardware as well as ubiquitous Internet connectivity enabled a first wave of cloud services starting in the first years of the 21st century.
But many businesses and other organizations hesitated to move more demanding applications from on-premises dedicated hardware into private or public clouds. As a response, communications service provider
A telephone company, also known as a telco, telephone service provider, or telecommunications operator, is a kind of communications service provider (CSP), more precisely a telecommunications service provider (TSP), that provides telecommunic ...
s started in the 2010/2011 time frame to develop carrier clouds that address perceived weaknesses in existing cloud services. Weaknesses cited vary but often include possible downtime, security issues, high cost of custom software and data transfer, inflexibility of some cloud apps, poor customer and nonfulfillment of service level agreement
A service-level agreement (SLA) is a commitment between a service provider and a customer. Particular aspects of the service – quality, availability, responsibilities – are agreed between the service provider and the service user.
...
s (SLAs).
Characteristics
To enable the deployment of time-sensitive and business critical applications in the cloud, the carrier cloud is designed to match or even exceed the characteristics of on-premises deployments. Therefore, the carrier cloud is characterized by some or all of the following items: * ''Configurable, elastic network performance'': Typical cloud computing solutions use the best effort public Internet to connect cloud users and data centers. This approach provides instant connectivity but does not offer control over network capacities, latencies, andjitter
In electronics and telecommunications, jitter is the deviation from true periodicity of a presumably periodic signal, often in relation to a reference clock signal. In clock recovery applications it is called timing jitter. Jitter is a signific ...
. Carrier clouds address these gaps with content delivery networks and/or dedicated virtual private network
A virtual private network (VPN) extends a private network across a public network and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network. The b ...
s (VPN) at OSI layers 1 (optical wavelengths
In physics, the wavelength is the spatial period of a periodic wave—the distance over which the wave's shape repeats.
It is the distance between consecutive corresponding points of the same phase on the wave, such as two adjacent crests, tr ...
), 2 (data link layer
The data link layer, or layer 2, is the second layer of the seven-layer OSI model of computer networking. This layer is the protocol layer that transfers data between nodes on a network segment across the physical layer. The data link layer p ...
), and 3 (network layer
In the seven-layer OSI model of computer networking, the network layer is layer 3. The network layer is responsible for packet forwarding including routing through intermediate routers.
Functions
The network layer provides the means of tran ...
). These VPNs can be configured to offer the desired performance parameters and exhibit the same type of elasticity for the network that regular clouds provide for servers and storage. To achieve the requested performance parameters, such as low latency
Latency, from a general point of view, is a time delay between the cause and the effect of some physical change in the system being observed. Lag, as it is known in gaming circles, refers to the latency between the input to a simulation and ...
, cloud applications can be (automatically) allocated to distributed data centers that are close enough to the cloud users.
* ''Automatic resource placement:'' For a cloud with multiple data centers, information about both the data center and the connecting network is relevant for a decision of where to place cloud images and storage volumes. For this decision, carrier clouds can obtain relevant information about the network, e.g., using the Application-Layer Traffic Optimization (ALTO) protocol./ref> * ''High level of security and governance'': Cloud application providers are subject to general and domain specific security, privacy, and governance requirements and regulations, such as the European Data Protection Directive and the U.S. Health Insurance Portability and Accountability Act. For added security, the wide area network of the carrier cloud can provide segregated encrypted or unencrypted network links that are not accessible from the general Internet. At the data center, the carrier cloud provides e.g. virtual private servers, management processes, logs and documentation to fulfill security and governance rules. * ''Location control'': Fundamentally, cloud users should not be concerned with the geographic location of their cloud resources. However, privacy and other regulations may mandate that certain types of data must not be sent outside a national jurisdiction or other geographical region. * ''Open APIs'': Carrier clouds provide
graphical user interface
The GUI ( "UI" by itself is still usually pronounced . or ), graphical user interface, is a form of user interface that allows users to interact with electronic devices through graphical icons and audio indicator such as primary notation, ins ...
s and Web application programming interfaces that allow cloud application providers to set up, manage, and monitor both, the data center and the WAN, of their cloud services.
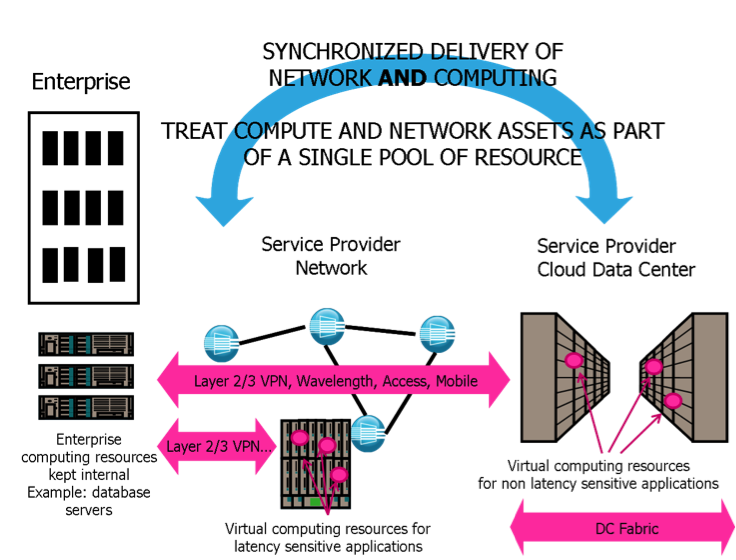
Architecture
Carrier clouds encompass data centers at different network tiers and wide area networks that connect multiple data centers to each other as well as to the cloud users. Links between data centers are used, for instance, for failover, overflow, backup, and geographic diversity. Carrier clouds can be set up as public, private, or hybrid clouds. The carrier cloud federates these cloud entities, using a single management system to orchestrate, manage, and monitor data center and network resources as a single system.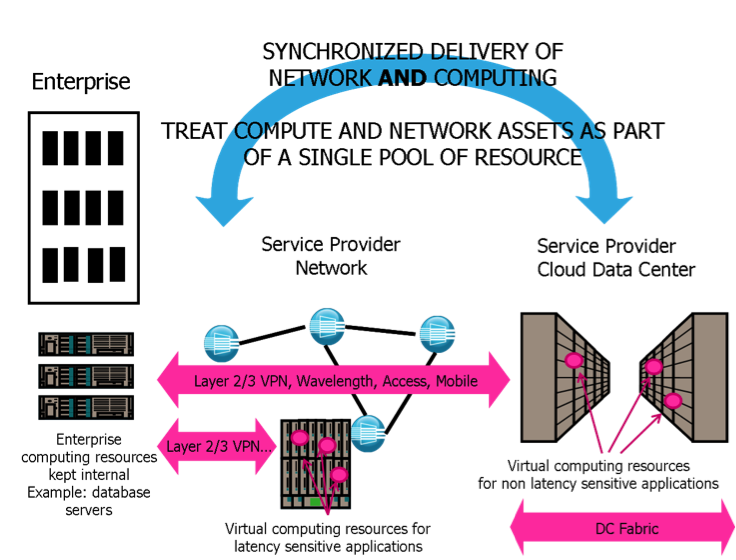
References
{{ReflistCategories
Cloud computing