Identity replacement technology is any technology that is used to cover up all or parts of a person's identity, either in real life or
virtually
In mathematics, especially in the area of abstract algebra that studies infinite groups, the adverb virtually is used to modify a property so that it need only hold for a subgroup of finite index. Given a property P, the group ''G'' is said to b ...
. This can include face
mask
A mask is an object normally worn on the face, typically for protection, disguise, performance, or entertainment and often they have been employed for rituals and rights. Masks have been used since antiquity for both ceremonial and practic ...
s, face authentication technology, and
deepfake
Deepfakes (a portmanteau of "deep learning" and "fake") are synthetic media in which a person in an existing image or video is replaced with someone else's likeness. While the act of creating fake content is not new, deepfakes leverage powerful ...
s on the Internet that spread fake
editing
Editing is the process of selecting and preparing written, photographic, visual, audible, or cinematic material used by a person or an entity to convey a message or information. The editing process can involve correction, condensation, orga ...
of videos and images.
Face replacement and identity masking are used by either criminals or law-abiding citizens. Identity replacement tech, when operated on by criminals, leads to
heists or robbery activities. Law-abiding citizens utilize identity replacement technology to prevent government or various entities from tracking private information such as locations, social connections, and daily behaviors.
Online
identity theft
Identity theft occurs when someone uses another person's personal identifying information, like their name, identifying number, or credit card number, without their permission, to commit fraud or other crimes. The term ''identity theft'' was co ...
, information stealing, and deepfakes are all methods used by hackers to replace or alter the identity of a victim. Along with these hacking methods are some solutions: face liveness detection,
obfuscation
Obfuscation is the obscuring of the intended meaning of communication by making the message difficult to understand, usually with confusing and ambiguous language. The obfuscation might be either unintentional or intentional (although intent u ...
of crucial information, and location privacy obfuscation. More advanced obfuscation technology can cover up the location of a person through privacy protection. The main method to achieve these kinds of obfuscation is by replacing personal information such as the location of a person with anonymous identities and operators or
trackers.
There is also research being done on the effectiveness and use of
biometric
Biometrics are body measurements and calculations related to human characteristics. Biometric authentication (or realistic authentication) is used in computer science as a form of identification and access control. It is also used to identify in ...
identity authentication such as fingerprints and faces to replace personal identity authentication such as one's
SSN.
For biotechnology identity replacement, gene sequencing and identity adjustments are common areas of research. With cutting-edge technology, it is possible to change the identity of a person or the identity of an offspring.
With the advancement of science comes the ethical issues of
cloning
Cloning is the process of producing individual organisms with identical or virtually identical DNA, either by natural or artificial means. In nature, some organisms produce clones through asexual reproduction. In the field of biotechnology, cl ...
, identity change, and societal and organizational transformations.
Features replacement
Features replacement technology is any technology that changes, alters, hides, or misrepresent a person's features. This can include feature replacements such as fingerprint replacement, face replacement,
pupil
The pupil is a black hole located in the center of the iris of the eye that allows light to strike the retina.Cassin, B. and Solomon, S. (1990) ''Dictionary of Eye Terminology''. Gainesville, Florida: Triad Publishing Company. It appears black ...
authentication replacement, etc. The technology involved in features replacement ranges from masking to creating 3D videos and images.
Criminal uses

A variety of technologies attempt to fool facial recognition software by the use of
anti-facial recognition masks.
3D masks that replace body features, usually faces, can be made from materials such as plastic, cotton, leather, etc. These identity masks can range from realistic imitations of a person to unrealistic characters that hide the identity of an individual. Criminals and hackers tend to use a spectrum of masks depending on their intended objectives of the crime and other environmental factors. Usually, if a crime involves more planning and execution, criminals and hackers put more effort into creating their 3d masks.
There are many intended purposes for feature replacements.
Cyber criminals
A cybercrime is a crime that involves a computer or a computer network.Moore, R. (2005) "Cyber crime: Investigating High-Technology Computer Crime," Cleveland, Mississippi: Anderson Publishing. The computer may have been used in committing the ...
or real-life criminals use masks or 3D generated images of a mask to hide from security systems or pass through security checks. They usually do this finding the identity of a victim who has access to certain security systems. Then, criminals wear masks in public to conduct fraud and passes through security systems as the victim of the identity theft.
This usage of masks and
3D printed
3D printing or additive manufacturing is the construction of a three-dimensional object from a CAD model or a digital 3D model. It can be done in a variety of processes in which material is deposited, joined or solidified under computer co ...
items to cover certain body features while conducting crime is illegal under laws like
anti-mask law
Anti-mask or anti-masking laws are legislative or penal initiatives prohibiting the concealment of one's face in public. Anti-mask laws vary widely between jurisdictions in their intent, scope, and penalties.
North America
United States
There a ...
s.
Other reasons for features replacement
Another use of face replacement technology is to hide one's identity from third-party trackers, monitors, and government officials.
Although uncommonly used by individuals, this method of hiding one's identity (either online or in-person) is mainly used for hiding from government tracking, for entertainment purposes, and for religious purposes. People may decide to wear a mask in-doors to prevent government tracking, for example.
Deepfakes, spoofing, and anti-spoofing
Deepfakes and synthetic media
Deepfake usages
Deepfakes, a type of identity replacement technology, are pictures or video edits that replace the identity of a person in the picture or the video. This digital forgery is used to manipulate informations, defame people, and blackmail individuals. Through editing techniques such as face replacement and
pixel
In digital imaging, a pixel (abbreviated px), pel, or picture element is the smallest addressable element in a raster image, or the smallest point in an all points addressable display device.
In most digital display devices, pixels are the smal ...
or coloration implant, deepfakes can resemble the real image closely.
Deepfakes are classified into four types of identity manipulations: face synthesis, identity swap, attribute manipulation, and expression swap.
Some more specific examples include face swapping,
lip sync
Lip sync or lip synch (pronounced , the same as the word ''sink'', short for lip synchronization) is a technical term for matching a speaking or singing person's lip movements with sung or spoken vocals.
Audio for lip syncing is generated thr ...
ing, motion transfer, and audio generation.
Although a more common usage of synthetic media or deepfakes is political disinformation, a less known phenomenon is financial fraud committed by
cybercriminals who use deepfakes to steal financial data and profit from doing so. Hackers and criminals use deepfakes to penetrate social media accounts, security systems of banks, and individual financial information of wealthy individuals.
Two scenarios that are used by hackers and manipulators include
narrowcast
Narrowcasting is the dissemination of information (usually via Internet, radio, newspaper, or television) to a narrow audience, rather than to the broader public at-large. Related to niche marketing or target marketing, narrowcasting involves aim ...
and
broadcast
Broadcasting is the distribution of audio or video content to a dispersed audience via any electronic mass communications medium, but typically one using the electromagnetic spectrum ( radio waves), in a one-to-many model. Broadcasting began ...
. Some deepfake techniques include deepfake
voice phishing
Voice phishing, or vishing, is the use of telephony (often Voice over IP telephony) to conduct phishing attacks.
Landline telephone services have traditionally been trustworthy; terminated in physical locations known to the telephone company, and ...
, fabricated private marks, and synthetic social media profiles that contain profiles of fake identities. According to research,
deepfake prevention requires collaboration from key stakeholder such as internal firm employees, industry-wide experts, and multi-stakeholder groups.
Technology used to deter deepfakes
Some possible methods of deterring deepfakes include early detection of face mismatches, individual feature analysis of the face, identity confirmation of images or videos, and techniques that utilize multi-feature analysis that pinpoint face liveness, etc.
There is further research being done on deepfakes techniques such as face morphing and face de-identification. However, deepfake prevention techniques tend to be worse at identifying more advanced deepfakes, identification methods sometimes fail to recognize unseen conditions not related to facial analysis, and databases and technology must be up-to-date based on evolving deepfake techniques.
Deepfakes can be used as weapons to spread
misinformation
Misinformation is incorrect or misleading information. It differs from disinformation, which is ''deliberately'' deceptive. Rumors are information not attributed to any particular source, and so are unreliable and often unverified, but can turn ou ...
and threaten democratic systems through identity replacement strategies. Some deepfakes, due to low cost and ease of usage, can be used to replace identities and spread misinformation across nations and the international landscape effectively.
Hackers can use
bot
Bot may refer to:
Sciences
Computing and technology
* Chatbot, a computer program that converses in natural language
* Internet bot, a software application that runs automated tasks (scripts) over the Internet
**a Spambot, an internet bot des ...
s or deepfakes that spread propaganda and disinformation to adversaries, and these attempts could challenge democratic processes internationally. The public will be distrustful due to the potential use of deepfakes by politicians or outside countries.
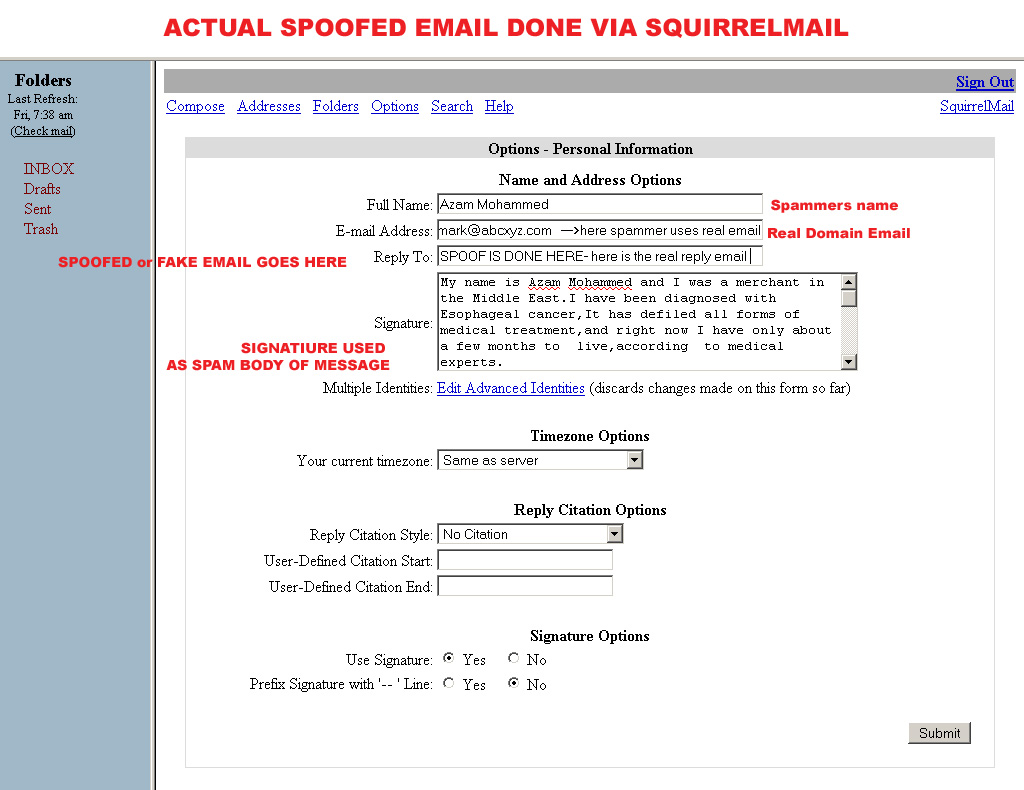
Spoofing and anti-spoofing

Spoofing
Spoofing, a concept related to deepfake, is a method of hacking and identity manipulation by impersonating as a known source trusted by a spoof target or system of security. Spoofing attacks can be easily launched due to common uses of face recognition systems in
mobile device
A mobile device (or handheld computer) is a computer small enough to hold and operate in the hand. Mobile devices typically have a flat LCD or OLED screen, a touchscreen interface, and digital or physical buttons. They may also have a physical ...
unlocking.
One way the hackers get into the system is by using a synthetic-forged biometric that fools sensors and grants a different identity to the hacker who passes through as the real identity.
Spoofing can also involve fake physical artifacts such as fake printouts of masks and fingers that hackers use to manipulate biometric authentication technology.
Due to spoofing attempts on a mass scale, there are global political, ethical, and economical threats that goes beyond a country's borders. Mass crimes involving cybersecurity
breach
Breach, Breached, or The Breach may refer to:
Places
* Breach, Kent, United Kingdom
* Breach, West Sussex, United Kingdom
* ''The Breach'', Great South Bay in the State of New York
People
* Breach (DJ), an Electronic/House music act
* Miroslava ...
es, political hacking, and personal identity thieving can cause damage to the international landscape.
Anti-spoofing techniques
Payment information,
personal information
Personal data, also known as personal information or personally identifiable information (PII), is any information related to an identifiable person.
The abbreviation PII is widely accepted in the United States, but the phrase it abbreviates ha ...
, and biometric information are all potential exploitation sources performed on by hackers.
There are both feature level and sensor level anti-spoofing techniques. The goal of anti-spoofing is to deter illegitimate users from accessing to important and personal information. 4 main groups of anti-spoofing techniques are widely used by cybersecurity experts: motion analysis, texture analysis, image quality analysis, and hardware based analysis that integrates software components.
Another anti-spoofing technique is using color texture to analyze the joint color-texture density of facial features in images and videos.
By comparing across databases using replay videos of spoof attacks, many of these methods are able to detect
liveness Properties of an execution of a computer program —particularly for concurrent and distributed systems— have long been formulated by giving ''safety properties'' ("bad things don't happen") and ''liveness properties'' ("good things do happen").
...
of faces and facial symmetry under a controlled environment.
Anti-spoofing and deepfake identification are prone to errors and attacks. For example, one model of attentional adversarial network to generate fake images that match the original pictures in terms of features, face strength, and
semantic
Semantics (from grc, σημαντικός ''sēmantikós'', "significant") is the study of reference, meaning, or truth. The term can be used to refer to subfields of several distinct disciplines, including philosophy, linguistics and comput ...
information.
One drawback of such an adversarial network model is it analyzes only one attack target; However, research is being done on using various models to target multiple attacks.
Some other shortcomings of anti-spoofing techniques include failure to detect spoofing across databases, failure to apply to real life scenarios, and performance issues related to the limits of the technologies involved.
Identity change and biotech enhancement
Biotech enhancement
Gene sequencing and gene therapy are cutting-edge technology used by biotech researchers to discover ways of altering the identities or genes of offsprings and humans. With gene alternating and features enhancement, one can change the structural identities of offsprings. Another related concept is cloning, a more futuristic concept about replicating human beings.
On a broader level, identity change leads to
social transformation
In sociology, social transformation is a somewhat ambiguous term that has two broad definitions.
One definition of social transformation is the process by which an individual ''alters'' the socially ascribed social status of their parents into a ...
.
Identity change and organization transformations occur sometimes at the same time. For example, there is profound socio-political change related to collective and individual identity change in Ireland. Identity change is also associated with economical, political, and social factors related to the changing environment. Individuals maintain the right to make personal choices, but these choices are often affected by one's surroundings and one's immediate environment.
Enhancement and alteration of the human body and identity is thus connected to broader social transformations. If society changes and evolves, then individuals may choose to evolve with it. Generational factors are also considered by researchers as biotech evolves and advances.
Ethical concerns of biotech enhancement
Fundamentally, some current objections to enhancement biotech include questions about authenticity of biotech enhancement and fundamental attributes and values of being human. Some key concerns include safety, ethical distributions, and identity traits violations.
Current biotech research is seeking to expand upon what human identity means, the connection between gene alteration and human enhancement, generational offspring alterations. More research is needed in this realm of biotechnology research for scientists to determine the viability and ethical issues revolving around advanced
biotechnology
Biotechnology is the integration of natural sciences and engineering sciences in order to achieve the application of organisms, cells, parts thereof and molecular analogues for products and services. The term ''biotechnology'' was first used b ...
.
Face authentication and biometric identification
Biometric identifications, including face authentication technology, is used by firms, governments, and various other organizations for security checks and personal identification.
This procedure and technology is especially important to protect private materials and information of a firm or government. Due to evolving security technology, Biometric authentication methods are replacing physical copies of IDs, numbers like
SSN, and personal information written on paper.
3D sensor analysis to test face authenticity
3D cameras and depth analysis can be used to detect spoofing and fraudulent data.
Biometric identifications with a wide range of depth and flexility can aid the detection of spoofing attempts by hackers and identity thieves. Liveness assurance and authentication of faces can help prevent face identity manipulation and forgery in that liveness detection of the face can use color, depth, angle of facial features, and other factors to distinguish between fake and real faces. Due to the ease of making a 3D mask and creating deepfakes online, fake identities is increasingly common in the tech industry. Some common methods used to achieve face authentication results include: SVM classifiers,
image quality Image quality can refer to the level of accuracy with which different imaging systems capture, process, store, compress, transmit and display the signals that form an image. Another definition refers to image quality as "the weighted combination of ...
assessment, pupil tracking and color texture analysis.
Biometric identification
Biometrics are body measurements and calculations related to human characteristics. Biometric authentication (or realistic authentication) is used in computer science as a form of identification and access control. It is also used to identify in ...
technology with a higher flexibility leads to better detection of spoofing attacks.
3D face reconstruction and face alignment can aid the use of biometric identification systems when authenticating identities of individuals. An end-to-end method called Position Map Regression Network is used to reconstruct 3D facial features from the 3D space such as from an image of a person. Some key metrics in measuring the effectiveness of alignment and reconstruction include face reconstruction speed, runtime of alignments and accuracy of facial alignment compared to original image.
Through restructuring 3D facial structures using density to align faces, position maps can convert a 3D face into a 2D image based on a UV plain analysis. 3D shapes are acquired by 3D sensors and specific features within the face shape are acquired by the sensors to retrieve information.
Convolutional neural networks are trained to extract facial and semantic information from the 3D image to the 2D image with a process called regression.
Overall, this position-map method of facial reconstruction and alignment can be used in cybersecurity authentication, biometric verification, and identity matching.
Fingerprint biometric identification

Fingerprint
A fingerprint is an impression left by the friction ridges of a human finger. The recovery of partial fingerprints from a crime scene is an important method of forensic science. Moisture and grease on a finger result in fingerprints on surfac ...
ing is also a biometric identification method researched on by cybersecurity firms and governments. Fingerprint verification can be used to counter identity theft or potential fraud just like face authentication technologies. One study uses a minutiae-extraction algorithm to develop an identity-authentication system based on how it extracts data and verifiable information from the fingerprint scan.
This model is based on alignment, where it matches inputs to stored template to verify the identity of someone faster and more accurately. The goal of all biometric authentication methods, including fingerprint identification, is to have accurate and speedy responses in authenticating data. Systems and alignment technologies are constantly updated to achieve better results. Some drawbacks of fingerprint identification are large distortions in poor image quality, straight line
deformations, vague transformations that affects authentication quality, and missing minutiae for some parts of an image.
However, multiple biometric authentication tools could be used, such as face and fingerprint, in order to obtain better and more accurate performances.

Applications of 3D sensors and biometrics
The components of 3d sensors such as key electronic parts and sensor systems are increasingly made smaller and better by emphasizing compactness of sensors, effectiveness of detecting shapes, portability, strength of imaging, etc.
3D imaging and optical sensor can be expensive, but the cost can be decreased when manufacturers and suppliers make individual sensor components cheaper and more flexible to fit a variety of sensors and cameras. Virtual
renders and prototyping tools are integrated into 3D sensor and camera systems to aid with facial reconstruction, identity search, and shape designs. 3D sensors can be made to form sensor systems where the entire system is more effective at capture an image compared to single sensors or cameras.
There are applications for 3D sensors such as in manufacturing, optical uses, and robotic applications. Key industries that could utilize 3d cameras include
robotics
Robotics is an interdisciplinary branch of computer science and engineering. Robotics involves design, construction, operation, and use of robots. The goal of robotics is to design machines that can help and assist humans. Robotics integrat ...
, law enforcements, automatic authentication systems, and product development.
Identity theft
Identity theft is the concept when a thief steals the identity of a victim and portrays oneself as the victim's identity. Identity theft has many implications both on a small and large scale. Individual identity theft can be limited to a single person when the identity thief takes on the identity of that victim.
The reason for identity theft might include pleasure of entertainment, malicious hacking, settling revenge, or for political purposes of sabotage. Mass scale identity theft can involve political sabotage, financial and economical heists and crimes, and social changes for the worse.
Identity theft and consumer payment
Identity theft and identity replacement has shaped and affected
consumer spending
Consumer spending is the total money spent on final goods and services by individuals and households.
There are two components of consumer spending: induced consumption (which is affected by the level of income) and autonomous consumption (which ...
over the past years in the financial world. One method used to analyze identity theft is to map identity theft incidents to determine geographical locations, environmental factors, and purposes of identity theft. Payment instruments used by different types of payment systems can affect how identity theft is used to obtain financial information and commit financial fraud.
Identity theft has an implication for consumer payment behaviors and adoptions. Although customers have different payment methods, geographical areas with more identity theft occurrences tend to have an increased use of payment methods such as money orders, travelers’ check,
prepaid cards
A stored-value card (SVC) is a payment card with a monetary value stored on the card itself, not in an external account maintained by a financial institution. This means no network access is required by the payment collection terminals as funds ...
, and credit card payments.
Electronic payments are widely used by consumers given society's evolving landscape of payment technology. However, these payment systems, including transactions of checks, cards, and cash, require periodic updates to keep up with evolving ways of identity theft.
Given our current economy of transactions involving
customer data
Customer data or consumer data refers to all personal, Behaviorism, behavioural, and demographic data that is collected by marketing companies and departments from their customer base.
To some extent, data collection from customers intrudes into c ...
, more opportunities are created for fraudulent transactions since more consumers are shopping online and conducting financial transactions online.
A thief could hack data related to common financial derivatives and items such as product payments,
loan
In finance, a loan is the lending of money by one or more individuals, organizations, or other entities to other individuals, organizations, etc. The recipient (i.e., the borrower) incurs a debt and is usually liable to pay interest on that d ...
s, mortgages, stocks,
options trading, etc.
One way identity theft can happen is when the thief tries to obtain a service or product but pays it with someone else's financial data or account information. This fraudulent transaction will attribute the cost of the transaction to the identity thief victim. The victim's identity could be used multiple times by different thieves using similar or different identity theft methods. Some solutions to such problems include
consumer protection
Consumer protection is the practice of safeguarding buyers of goods and services, and the public, against unfair practices in the marketplace. Consumer protection measures are often established by law. Such laws are intended to prevent business ...
s,
credit freeze
A credit freeze (also known as a security freeze) allows an individual to control how a consumer reporting agency (also known as a credit bureau: Equifax, Experian, TransUnion, and Innovis) is able to sell personal financial identity data. The cre ...
s if fraud occurs, credit verification, and penalties and enforcements.
Identity theft in politics
Identity theft can also involve political manipulations and hacking on a large scale that is detrimental to the political wellbeing of international politics.
Identity thieves can use identity replacement methods such as biometric replacement, face masks, deepfakes, and personal information stealing to conduct political sabotages. For example, an identity thief could conduct
voter fraud
Electoral fraud, sometimes referred to as election manipulation, voter fraud or vote rigging, involves illegal interference with the process of an election, either by increasing the vote share of a favored candidate, depressing the vote share of ...
by imposing as one or more individuals who cast ballots. The thief could also hack the social media account of a politician and post scandals or defamation about that politician.
Obfuscation and identity privacy protection
Definition of obfuscation
Obfuscation
Obfuscation is the obscuring of the intended meaning of communication by making the message difficult to understand, usually with confusing and ambiguous language. The obfuscation might be either unintentional or intentional (although intent u ...
has a technical meaning of code protection and making coding patterns, structures, and lines anonymous to everyone but the code programmer. This way, the programmer deters incoming hacks and shell-injection attacks methods. Another use of obfuscation is protecting a person's identity online, such as protection of privacy, location, and behaviors.

Methods of obfuscation
Obfuscation operators can be used to determine distribution areas, privacy protections, and location preferences. Probabilistic fundamentals such as the
joint distribution function
Given two random variables that are defined on the same probability space, the joint probability distribution is the corresponding probability distribution on all possible pairs of outputs. The joint distribution can just as well be considere ...
are used to test out obfuscation operators and how operators can be used to protect location privacy of individuals without sacrificing certain app features and efficiencies.
Thus, obfuscation can be used to make location and related information anonymous and useless to potential hackers who are trying to breach the privacy of individuals. Adversary models can be used to form combinations of operators to test the viability of obfuscation operators based on adversary awareness, utility functions, and robustness of operator families.
Another obfuscation
privacy protection
Privacy engineering is an emerging field of engineering which aims to provide methodologies, tools, and techniques to ensure systems provide acceptable levels of privacy.
In the US, an acceptable level of privacy is defined in terms of compliance ...
method protects images online and through social media.
The targeted-identity-protection-iterative method(TIP-IM) is used for this type of image-privacy protection. The method is to feed various adversarial models into TIP-IM and look at the performance of adversarial networks. By simulating an identity-protection system, the method identifies an adversarial network that interacts with privacy protection results.
Thus, the TIP-IM can prevent hackers' unauthorized access to images, accounts, and systems that have sensitive information. There is also a trade-off between effectiveness and naturalness of the protected face and identity images: naturalness of faces decreases as image protection becomes more effective.
Obfuscation Categories
Obfuscation can be divided into three categories: construction, empirical, and construction and empirical combination. Mapping obfuscation techniques involves analysis in data, layout, control, and preventive structures of applications.
By diversifying systems and obfuscation of data through system analysis, data scientists and security experts can make it harder for hackers to breach a system's security and privacy settings. Virtualization systems are used by cybersecurity experts to test the effects of various obfuscation techniques on potential cyber attacks. Different cyber attacks on private information require different diversification and obfuscation methods. Thus, a combination of multiple obfuscation methods such as code blocking, location
privacy protection
Privacy engineering is an emerging field of engineering which aims to provide methodologies, tools, and techniques to ensure systems provide acceptable levels of privacy.
In the US, an acceptable level of privacy is defined in terms of compliance ...
, identity replacements can be used. Some further studies in the field of obfuscation include analysis on diversification methods and performing tests on different virtual environments such as
cloud
In meteorology, a cloud is an aerosol consisting of a visible mass of miniature liquid droplets, frozen crystals, or other particles suspended in the atmosphere of a planetary body or similar space. Water or various other chemicals may co ...
and trusted computing.
Olympus: an example of obfuscation technology
One study formed a system of obfuscation operators called Olympus, a system of managing data and protecting privacy of individuals on applications.
Olympus's goal is to maintain existing data structures and functionality of the applications while also protecting the privacy of personal information uploaded onto the testing applications. These data usually come from sensors and are uploaded onto the application where it's analyzed. Through obfuscation operators and certain combinations of them, an individual's private data can be protected while also being analyzed. Information categories like SSN, birth dates, home locations, age, gender, race, and income that are sensitive to
data-stealing and identity thieving are protected. Olympus is an attempt to apply privacy protection to real world applications. By forming adversarial networks between utility requirements and privacy through weighing the tradeoffs between them, data's usability is kept.
See also
*
Obfuscation
Obfuscation is the obscuring of the intended meaning of communication by making the message difficult to understand, usually with confusing and ambiguous language. The obfuscation might be either unintentional or intentional (although intent u ...
*
3D sensor systems
*
Spoofing and anti-spoofing
*Face
authentication
Authentication (from ''authentikos'', "real, genuine", from αὐθέντης ''authentes'', "author") is the act of proving an assertion, such as the identity of a computer system user. In contrast with identification, the act of indicati ...
References
{{Reflist
Personal identification
Ethically disputed practices
 A variety of technologies attempt to fool facial recognition software by the use of anti-facial recognition masks. 3D masks that replace body features, usually faces, can be made from materials such as plastic, cotton, leather, etc. These identity masks can range from realistic imitations of a person to unrealistic characters that hide the identity of an individual. Criminals and hackers tend to use a spectrum of masks depending on their intended objectives of the crime and other environmental factors. Usually, if a crime involves more planning and execution, criminals and hackers put more effort into creating their 3d masks.
There are many intended purposes for feature replacements.
A variety of technologies attempt to fool facial recognition software by the use of anti-facial recognition masks. 3D masks that replace body features, usually faces, can be made from materials such as plastic, cotton, leather, etc. These identity masks can range from realistic imitations of a person to unrealistic characters that hide the identity of an individual. Criminals and hackers tend to use a spectrum of masks depending on their intended objectives of the crime and other environmental factors. Usually, if a crime involves more planning and execution, criminals and hackers put more effort into creating their 3d masks.
There are many intended purposes for feature replacements. 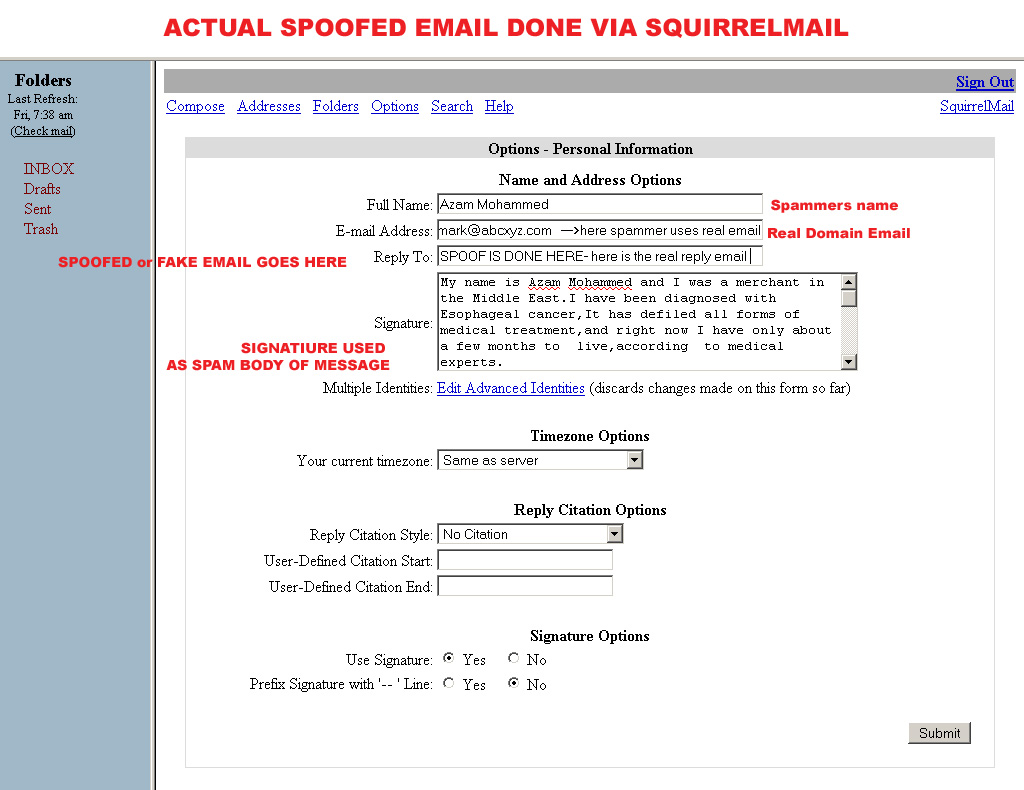 Anti-spoofing and deepfake identification are prone to errors and attacks. For example, one model of attentional adversarial network to generate fake images that match the original pictures in terms of features, face strength, and
Anti-spoofing and deepfake identification are prone to errors and attacks. For example, one model of attentional adversarial network to generate fake images that match the original pictures in terms of features, face strength, and 

