Identity Document Forgery on:
[Wikipedia]
[Google]
[Amazon]
 Identity document forgery is the process by which identity documents issued by governing bodies are copied and/or modified by persons not authorized to create such documents or engage in such modifications, for the purpose of deceiving those who would view the documents about the identity or status of the bearer. The term also encompasses the activity of acquiring identity documents from legitimate bodies by falsifying the required supporting documentation in order to create the desired identity.
Identity documents differ from other credentials in that they are intended to be usable by only the person holding the card. Unlike other credentials, they may be used to restrict the activities of the holder as well as to expand them.
Documents that have been forged in this way include
Identity document forgery is the process by which identity documents issued by governing bodies are copied and/or modified by persons not authorized to create such documents or engage in such modifications, for the purpose of deceiving those who would view the documents about the identity or status of the bearer. The term also encompasses the activity of acquiring identity documents from legitimate bodies by falsifying the required supporting documentation in order to create the desired identity.
Identity documents differ from other credentials in that they are intended to be usable by only the person holding the card. Unlike other credentials, they may be used to restrict the activities of the holder as well as to expand them.
Documents that have been forged in this way include
 A distinction needs to be made between the different uses of an identity document. In some cases, the fake ID may only have to pass a cursory inspection, such as flashing a plastic ID card for a security guard. At the other extreme, a document may have to resist scrutiny by a trained document examiner, who may be equipped with technical tools for verifying biometrics and reading hidden security features within the card. To make forgery more difficult, most modern IDs contain numerous security features that require specialised and expensive equipment to duplicate. School IDs are typically easier to fake, as they often do not have the same level of security measures as government-issued IDs.
Fake ID cards can be ordered on the internet and some examples of these include the UK national identification card and a provisional motorcycle licence. It is an offence under section 1 of the Forgery and Counterfeiting Act 1981. There are a number of different types of false documents such as using another person's ID, a genuine document which has been altered, a form of ID that doesn't exist and a copy of an ID which has been made.
Modern fake ID cards almost invariably carry a picture of the authorized user, a simple and effective form of biometric identification. However, forgery of basic photographic ID cards has become simple in recent years with the availability of low-cost high-resolution printers, scanners and photo-editing software. Basic fake ID cards are commonly made using an inkjet or laser printer to print a replica document which is then laminated to resemble a real ID card. Most designs are made using computer programs, re-creating scanned copies of a license.
More complex ID cards are now being created by printing on a material called Teslin or Artisyn, which are paper-like materials that are actually micro-porous plastic sheets. When butterfly pouches and holograms are applied, the card is then run through a heat laminator, creating a professional-looking ID card.
Numerous security printing techniques have been used to attempt to enhance the security of ID cards. For example, many modern documents include holograms, which are difficult to replicate without expensive equipment not generally available. Though accurate recreation of these holograms is extremely difficult, using a mixture of pigments and base can create a similar shiny multi-colored look that may pass cursory inspection. Another form of document security is UV-light visible ink.
In addition, some documents include a magnetic strip, which contains the similar information to that printed on the card. The data may thus be checked against other data on the card, such as printed information or a machine-readable barcode. Magnetic strips may also contain other secret identifying information. Although magnetic strips can also be faked, they provide another barrier to entry for the amateur forger. Other hidden security devices can also be added, including embedded secure cryptoprocessor chips which are designed to be very difficult to forge, and RFID tags — the two technologies may also be combined, in the case of contactless smart cards.
Another effective technique is the use of online verification of security information against a central database. In many cases, online verification can detect simple copying of a document by detecting attempted use in multiple places at the same time, or completely false IDs, as the information on the ID will be found to be invalid. A simple method of confirming that an ID is genuine is to print a serial number on it unique to the card and stored on a centralized database. If checked, it will quickly become clear that the ID is false; either the number on the ID is not registered for the holder, or no ID has the number at all. Online verification also has the advantage that it allows easy revocation of lost or stolen documents.
Using verifiable credentials is another effective method to detect ID forgery. The ID can include a verifiable credential, with a proof (such as a cryptographic signature by the legitimate issuer), that represents the information on the ID. The proof on the verifiable credential allows authentication of the ID. If the verifiable credential of a fake ID is checked, it will be evident that the ID is fake, because either the information on the ID and the verifiable credential do not match, the verifiable credential was not signed by the legitimate issuer, or the verifiable credential was issued by the legitimate issuer, but the information on it was modified without the legitimate issuer signing the modified verifiable credential.
Many modern credentials now contain some kind of barcode. For example, many U.S. driving licences include a 2-dimensional code in PDF417 format, which contains the same information as on the front of the license. Barcodes allow rapid checking of credentials for low-security applications, and may potentially contain extra information which can be used to verify other information on the card.
A distinction needs to be made between the different uses of an identity document. In some cases, the fake ID may only have to pass a cursory inspection, such as flashing a plastic ID card for a security guard. At the other extreme, a document may have to resist scrutiny by a trained document examiner, who may be equipped with technical tools for verifying biometrics and reading hidden security features within the card. To make forgery more difficult, most modern IDs contain numerous security features that require specialised and expensive equipment to duplicate. School IDs are typically easier to fake, as they often do not have the same level of security measures as government-issued IDs.
Fake ID cards can be ordered on the internet and some examples of these include the UK national identification card and a provisional motorcycle licence. It is an offence under section 1 of the Forgery and Counterfeiting Act 1981. There are a number of different types of false documents such as using another person's ID, a genuine document which has been altered, a form of ID that doesn't exist and a copy of an ID which has been made.
Modern fake ID cards almost invariably carry a picture of the authorized user, a simple and effective form of biometric identification. However, forgery of basic photographic ID cards has become simple in recent years with the availability of low-cost high-resolution printers, scanners and photo-editing software. Basic fake ID cards are commonly made using an inkjet or laser printer to print a replica document which is then laminated to resemble a real ID card. Most designs are made using computer programs, re-creating scanned copies of a license.
More complex ID cards are now being created by printing on a material called Teslin or Artisyn, which are paper-like materials that are actually micro-porous plastic sheets. When butterfly pouches and holograms are applied, the card is then run through a heat laminator, creating a professional-looking ID card.
Numerous security printing techniques have been used to attempt to enhance the security of ID cards. For example, many modern documents include holograms, which are difficult to replicate without expensive equipment not generally available. Though accurate recreation of these holograms is extremely difficult, using a mixture of pigments and base can create a similar shiny multi-colored look that may pass cursory inspection. Another form of document security is UV-light visible ink.
In addition, some documents include a magnetic strip, which contains the similar information to that printed on the card. The data may thus be checked against other data on the card, such as printed information or a machine-readable barcode. Magnetic strips may also contain other secret identifying information. Although magnetic strips can also be faked, they provide another barrier to entry for the amateur forger. Other hidden security devices can also be added, including embedded secure cryptoprocessor chips which are designed to be very difficult to forge, and RFID tags — the two technologies may also be combined, in the case of contactless smart cards.
Another effective technique is the use of online verification of security information against a central database. In many cases, online verification can detect simple copying of a document by detecting attempted use in multiple places at the same time, or completely false IDs, as the information on the ID will be found to be invalid. A simple method of confirming that an ID is genuine is to print a serial number on it unique to the card and stored on a centralized database. If checked, it will quickly become clear that the ID is false; either the number on the ID is not registered for the holder, or no ID has the number at all. Online verification also has the advantage that it allows easy revocation of lost or stolen documents.
Using verifiable credentials is another effective method to detect ID forgery. The ID can include a verifiable credential, with a proof (such as a cryptographic signature by the legitimate issuer), that represents the information on the ID. The proof on the verifiable credential allows authentication of the ID. If the verifiable credential of a fake ID is checked, it will be evident that the ID is fake, because either the information on the ID and the verifiable credential do not match, the verifiable credential was not signed by the legitimate issuer, or the verifiable credential was issued by the legitimate issuer, but the information on it was modified without the legitimate issuer signing the modified verifiable credential.
Many modern credentials now contain some kind of barcode. For example, many U.S. driving licences include a 2-dimensional code in PDF417 format, which contains the same information as on the front of the license. Barcodes allow rapid checking of credentials for low-security applications, and may potentially contain extra information which can be used to verify other information on the card.
 Identity document forgery is the process by which identity documents issued by governing bodies are copied and/or modified by persons not authorized to create such documents or engage in such modifications, for the purpose of deceiving those who would view the documents about the identity or status of the bearer. The term also encompasses the activity of acquiring identity documents from legitimate bodies by falsifying the required supporting documentation in order to create the desired identity.
Identity documents differ from other credentials in that they are intended to be usable by only the person holding the card. Unlike other credentials, they may be used to restrict the activities of the holder as well as to expand them.
Documents that have been forged in this way include
Identity document forgery is the process by which identity documents issued by governing bodies are copied and/or modified by persons not authorized to create such documents or engage in such modifications, for the purpose of deceiving those who would view the documents about the identity or status of the bearer. The term also encompasses the activity of acquiring identity documents from legitimate bodies by falsifying the required supporting documentation in order to create the desired identity.
Identity documents differ from other credentials in that they are intended to be usable by only the person holding the card. Unlike other credentials, they may be used to restrict the activities of the holder as well as to expand them.
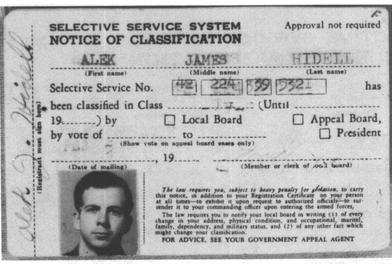
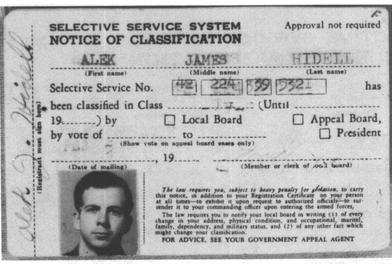
Documents that have been forged in this way include driver's license
A driver's license is a legal authorization, or the official document confirming such an authorization, for a specific individual to operate one or more types of motorized vehicles—such as motorcycles, cars, trucks, or buses—on a publi ...
s (historically forged or altered as an attempt to conceal the fact that persons desiring to purchase alcohol are under the legal drinking age); birth certificates and Social Security cards (likely used in identity theft schemes or to defraud the government); and passports (used to evade restrictions on entry into a particular country). At the beginning of 2010, there were 11 million stolen or lost passports listed in the global database of Interpol
The International Criminal Police Organization (ICPO; french: link=no, Organisation internationale de police criminelle), commonly known as Interpol ( , ), is an international organization that facilitates worldwide police cooperation and cr ...
.
Such falsified documents can be used for identity theft, age deception, illegal immigration, organized crime
Organized crime (or organised crime) is a category of transnational, national, or local groupings of highly centralized enterprises run by criminals to engage in illegal activity, most commonly for profit. While organized crime is generally tho ...
, and espionage
Espionage, spying, or intelligence gathering is the act of obtaining secret or confidential information ( intelligence) from non-disclosed sources or divulging of the same without the permission of the holder of the information for a tang ...
.
Use scenarios, forgery techniques and security countermeasures
 A distinction needs to be made between the different uses of an identity document. In some cases, the fake ID may only have to pass a cursory inspection, such as flashing a plastic ID card for a security guard. At the other extreme, a document may have to resist scrutiny by a trained document examiner, who may be equipped with technical tools for verifying biometrics and reading hidden security features within the card. To make forgery more difficult, most modern IDs contain numerous security features that require specialised and expensive equipment to duplicate. School IDs are typically easier to fake, as they often do not have the same level of security measures as government-issued IDs.
Fake ID cards can be ordered on the internet and some examples of these include the UK national identification card and a provisional motorcycle licence. It is an offence under section 1 of the Forgery and Counterfeiting Act 1981. There are a number of different types of false documents such as using another person's ID, a genuine document which has been altered, a form of ID that doesn't exist and a copy of an ID which has been made.
Modern fake ID cards almost invariably carry a picture of the authorized user, a simple and effective form of biometric identification. However, forgery of basic photographic ID cards has become simple in recent years with the availability of low-cost high-resolution printers, scanners and photo-editing software. Basic fake ID cards are commonly made using an inkjet or laser printer to print a replica document which is then laminated to resemble a real ID card. Most designs are made using computer programs, re-creating scanned copies of a license.
More complex ID cards are now being created by printing on a material called Teslin or Artisyn, which are paper-like materials that are actually micro-porous plastic sheets. When butterfly pouches and holograms are applied, the card is then run through a heat laminator, creating a professional-looking ID card.
Numerous security printing techniques have been used to attempt to enhance the security of ID cards. For example, many modern documents include holograms, which are difficult to replicate without expensive equipment not generally available. Though accurate recreation of these holograms is extremely difficult, using a mixture of pigments and base can create a similar shiny multi-colored look that may pass cursory inspection. Another form of document security is UV-light visible ink.
In addition, some documents include a magnetic strip, which contains the similar information to that printed on the card. The data may thus be checked against other data on the card, such as printed information or a machine-readable barcode. Magnetic strips may also contain other secret identifying information. Although magnetic strips can also be faked, they provide another barrier to entry for the amateur forger. Other hidden security devices can also be added, including embedded secure cryptoprocessor chips which are designed to be very difficult to forge, and RFID tags — the two technologies may also be combined, in the case of contactless smart cards.
Another effective technique is the use of online verification of security information against a central database. In many cases, online verification can detect simple copying of a document by detecting attempted use in multiple places at the same time, or completely false IDs, as the information on the ID will be found to be invalid. A simple method of confirming that an ID is genuine is to print a serial number on it unique to the card and stored on a centralized database. If checked, it will quickly become clear that the ID is false; either the number on the ID is not registered for the holder, or no ID has the number at all. Online verification also has the advantage that it allows easy revocation of lost or stolen documents.
Using verifiable credentials is another effective method to detect ID forgery. The ID can include a verifiable credential, with a proof (such as a cryptographic signature by the legitimate issuer), that represents the information on the ID. The proof on the verifiable credential allows authentication of the ID. If the verifiable credential of a fake ID is checked, it will be evident that the ID is fake, because either the information on the ID and the verifiable credential do not match, the verifiable credential was not signed by the legitimate issuer, or the verifiable credential was issued by the legitimate issuer, but the information on it was modified without the legitimate issuer signing the modified verifiable credential.
Many modern credentials now contain some kind of barcode. For example, many U.S. driving licences include a 2-dimensional code in PDF417 format, which contains the same information as on the front of the license. Barcodes allow rapid checking of credentials for low-security applications, and may potentially contain extra information which can be used to verify other information on the card.
A distinction needs to be made between the different uses of an identity document. In some cases, the fake ID may only have to pass a cursory inspection, such as flashing a plastic ID card for a security guard. At the other extreme, a document may have to resist scrutiny by a trained document examiner, who may be equipped with technical tools for verifying biometrics and reading hidden security features within the card. To make forgery more difficult, most modern IDs contain numerous security features that require specialised and expensive equipment to duplicate. School IDs are typically easier to fake, as they often do not have the same level of security measures as government-issued IDs.
Fake ID cards can be ordered on the internet and some examples of these include the UK national identification card and a provisional motorcycle licence. It is an offence under section 1 of the Forgery and Counterfeiting Act 1981. There are a number of different types of false documents such as using another person's ID, a genuine document which has been altered, a form of ID that doesn't exist and a copy of an ID which has been made.
Modern fake ID cards almost invariably carry a picture of the authorized user, a simple and effective form of biometric identification. However, forgery of basic photographic ID cards has become simple in recent years with the availability of low-cost high-resolution printers, scanners and photo-editing software. Basic fake ID cards are commonly made using an inkjet or laser printer to print a replica document which is then laminated to resemble a real ID card. Most designs are made using computer programs, re-creating scanned copies of a license.
More complex ID cards are now being created by printing on a material called Teslin or Artisyn, which are paper-like materials that are actually micro-porous plastic sheets. When butterfly pouches and holograms are applied, the card is then run through a heat laminator, creating a professional-looking ID card.
Numerous security printing techniques have been used to attempt to enhance the security of ID cards. For example, many modern documents include holograms, which are difficult to replicate without expensive equipment not generally available. Though accurate recreation of these holograms is extremely difficult, using a mixture of pigments and base can create a similar shiny multi-colored look that may pass cursory inspection. Another form of document security is UV-light visible ink.
In addition, some documents include a magnetic strip, which contains the similar information to that printed on the card. The data may thus be checked against other data on the card, such as printed information or a machine-readable barcode. Magnetic strips may also contain other secret identifying information. Although magnetic strips can also be faked, they provide another barrier to entry for the amateur forger. Other hidden security devices can also be added, including embedded secure cryptoprocessor chips which are designed to be very difficult to forge, and RFID tags — the two technologies may also be combined, in the case of contactless smart cards.
Another effective technique is the use of online verification of security information against a central database. In many cases, online verification can detect simple copying of a document by detecting attempted use in multiple places at the same time, or completely false IDs, as the information on the ID will be found to be invalid. A simple method of confirming that an ID is genuine is to print a serial number on it unique to the card and stored on a centralized database. If checked, it will quickly become clear that the ID is false; either the number on the ID is not registered for the holder, or no ID has the number at all. Online verification also has the advantage that it allows easy revocation of lost or stolen documents.
Using verifiable credentials is another effective method to detect ID forgery. The ID can include a verifiable credential, with a proof (such as a cryptographic signature by the legitimate issuer), that represents the information on the ID. The proof on the verifiable credential allows authentication of the ID. If the verifiable credential of a fake ID is checked, it will be evident that the ID is fake, because either the information on the ID and the verifiable credential do not match, the verifiable credential was not signed by the legitimate issuer, or the verifiable credential was issued by the legitimate issuer, but the information on it was modified without the legitimate issuer signing the modified verifiable credential.
Many modern credentials now contain some kind of barcode. For example, many U.S. driving licences include a 2-dimensional code in PDF417 format, which contains the same information as on the front of the license. Barcodes allow rapid checking of credentials for low-security applications, and may potentially contain extra information which can be used to verify other information on the card.
Systemic attacks
The combination of multiple high-security features, biometrics, and well-trained document inspectors with technical assistance can be very effective at preventing forged documents from being easily produced. Instead of acquiring the expensive specialized equipment needed to make fake documents, it may be more economical to produce a "genuine fake" — a legitimate document, but one which contains false information. One way of doing this is to present the document issuing authority with false credentials, which they will then endorse by issuing a new document. In this way, false identities and credentials can be "bootstrapped" over a period of time. Another simpler way of generating false credentials is to suborn one of the officials involved in the document-issuing process through bribery or intimidation. This may also be combined with the bootstrapping process mentioned above to mount complex attacks. Corruption in the document-issuing process is hard to counter, since as the value of a credential increases, the economic incentives for corruption also increase. This is particularly true in the case of fake ID cards that combine many functions in one document, and for documents which are issued in large numbers, thus requiring many thousands of people to have authorizing powers, thus creating a longer chain of people who can possibly be exploited. Detection of a "genuine fake" document is also a difficult process; as such a fake is a legitimate document, it will pass any tests for forgery. To detect such fakes, it is necessary to perform a background check on the individual in question to confirm the legitimacy of the document's information.See also
* ID card printer * Outline of forgeryReferences
{{Authority control Security engineering Document forgery