end-user (computer science) on:
[Wikipedia]
[Google]
[Amazon]
In product development, an end user (sometimes end-user) is a person who ultimately uses or is intended to ultimately use a product. The end user stands in contrast to users who support or maintain the product, such as
 The aim of end user
The aim of end user
sysop
A sysop (, an abbreviation of system operator) is an administrator of a multi-user computer system, such as a bulletin board system (BBS) or an online service virtual community.Jansen, E. & James, V. (2002). NetLingo: the Internet dictionary. Ne ...
s, system administrator
An IT administrator, system administrator, sysadmin, or admin is a person who is responsible for the upkeep, configuration, and reliable operation of computer systems, especially multi-user computers, such as Server (computing), servers. The ...
s, database administrators, information technology
Information technology (IT) is a set of related fields within information and communications technology (ICT), that encompass computer systems, software, programming languages, data processing, data and information processing, and storage. Inf ...
(IT) experts, software professionals, and computer technicians. End users typically do not possess the technical understanding or skill of the product designers, a fact easily overlooked and forgotten by designers: leading to features creating low customer satisfaction. In information technology, end users are not customer
In sales, commerce, and economics, a customer (sometimes known as a Client (business), client, buyer, or purchaser) is the recipient of a Good (economics), good, service (economics), service, product (business), product, or an Intellectual prop ...
s in the usual sense—they are typically employees of the customer. For example, if a large retail
Retail is the sale of goods and services to consumers, in contrast to wholesaling, which is the sale to business or institutional customers. A retailer purchases goods in large quantities from manufacturers, directly or through a wholes ...
corporation buys a software package for its employees to use, even though the large retail corporation was the ''customer'' that purchased the software, the end users are the employees of the company, who will use the software at work.
Context
End users are one of the three major factors contributing to the complexity of managing information systems. The end user's position has changed from a position in the 1950s (where end users did not interact with themainframe
A mainframe computer, informally called a mainframe or big iron, is a computer used primarily by large organizations for critical applications like bulk data processing for tasks such as censuses, industry and consumer statistics, enterpris ...
; computer experts programmed and ran the mainframe) to one in the 2010s where the end user collaborates with and advises the management information system
A management information system (MIS) is an information system used for decision-making, and for the coordination, control, analysis, and visualization of information in an organization. The study of the management information systems involves peo ...
and Information Technology department about his or her needs regarding the system or product. This raises new questions, such as: Who manages each resource?, What is the role of the MIS Department? and What is the optimal relationship between the end-user and the MIS Department?
Empowerment
The concept of end-user first surfaced in the late 1980s and has since then raised many debates. One challenge was the goal to give both the user more freedom, by adding advanced features and functions (for more advanced users) and adding more constraints (to prevent a neophyte user from accidentally erasing an entire company's database). This phenomenon appeared as a consequence ofconsumerization
Consumerization is the reorientation of product and service designs to focus on (and marketing, market to) the end user as an individual consumer, in contrast with an earlier era of only organization-oriented offerings (designed solely for busine ...
of computer products and software. In the 1960s and 1970s, computer users were generally programming experts and computer scientist
A computer scientist is a scientist who specializes in the academic study of computer science.
Computer scientists typically work on the theoretical side of computation. Although computer scientists can also focus their work and research on ...
s. However, in the 1980s, and especially in the mid-to-late 1990s and the early 2000s, everyday, regular people began using computer devices and software for personal and work use. IT specialists needed to cope with this trend in various ways. In the 2010s, users now want to have more control over the systems they operate, to solve their own problems, and be able to customize the systems to suit their needs. The apparent drawbacks were the risk of corruption of the systems and data the users had control of, due to their lack of knowledge on how to properly operate the computer/software at an advanced level.
For companies to appeal to the user, it took primary care to accommodate and think of end-users in their new products, software launches, and updates. A partnership needed to be formed between the programmer-developers and the everyday end users so both parties could maximize the use of the products effectively. A major example of the public's effects on end user's requirements were the public libraries. They have been affected by new technologies in many ways, ranging from the digitalization of their card catalog, the shift to e-book
An ebook (short for electronic book), also spelled as e-book or eBook, is a book publication made available in electronic form, consisting of text, images, or both, readable on the flat-panel display of computers or other electronic devices. Al ...
s, e-journal
An academic journal (or scholarly journal or scientific journal) is a periodical publication in which scholarship relating to a particular academic discipline is published. They serve as permanent and transparent forums for the dissemination, scr ...
s, and offering online services. Libraries have had to undergo many changes in order to cope, including training existing librarians in Web 2.0
Web 2.0 (also known as participative (or participatory) web and social web) refers to websites that emphasize user-generated content, ease of use, participatory culture, and interoperability (i.e., compatibility with other products, systems, a ...
and database
In computing, a database is an organized collection of data or a type of data store based on the use of a database management system (DBMS), the software that interacts with end users, applications, and the database itself to capture and a ...
skills, to hiring IT and software experts.
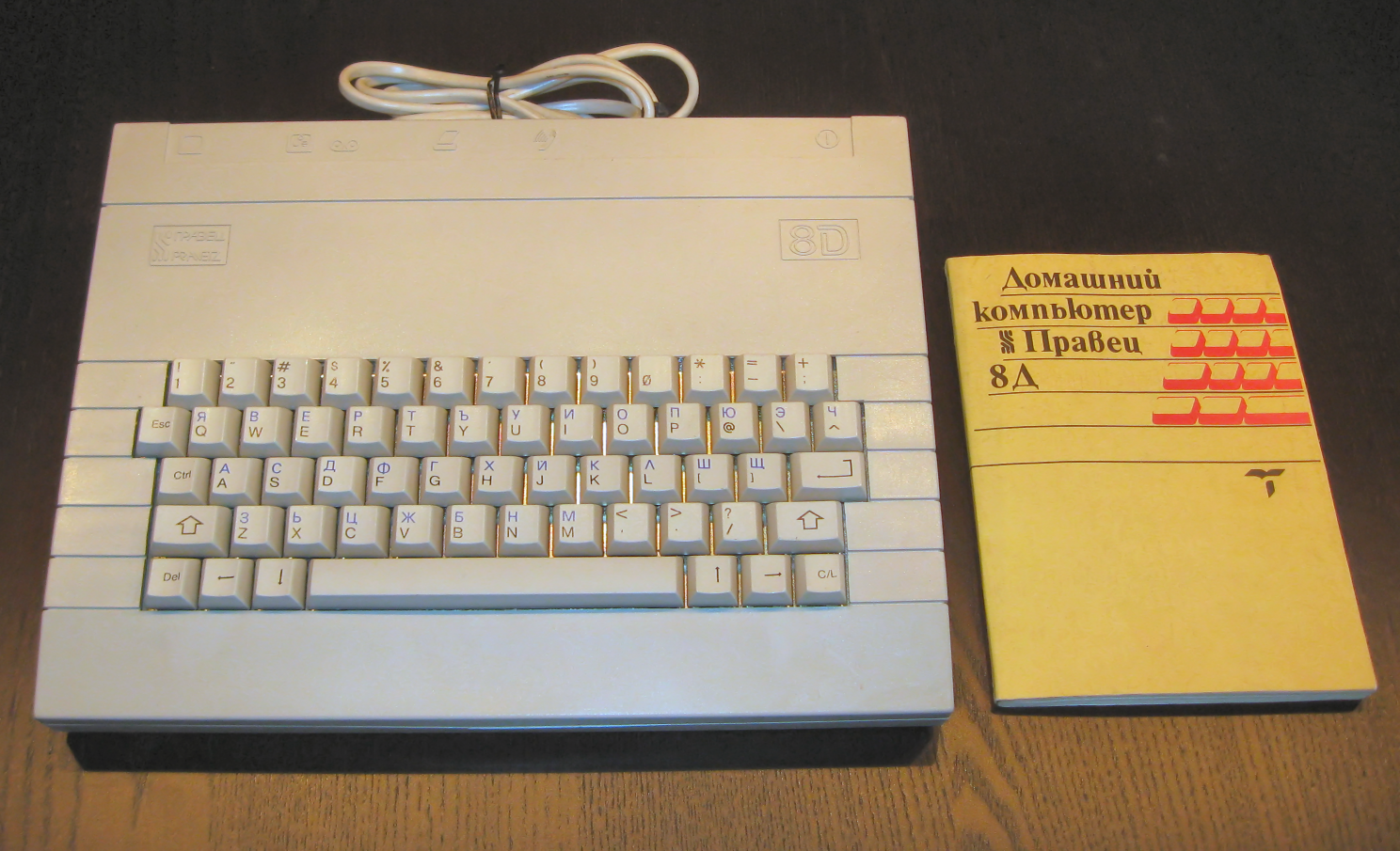
End user documentation
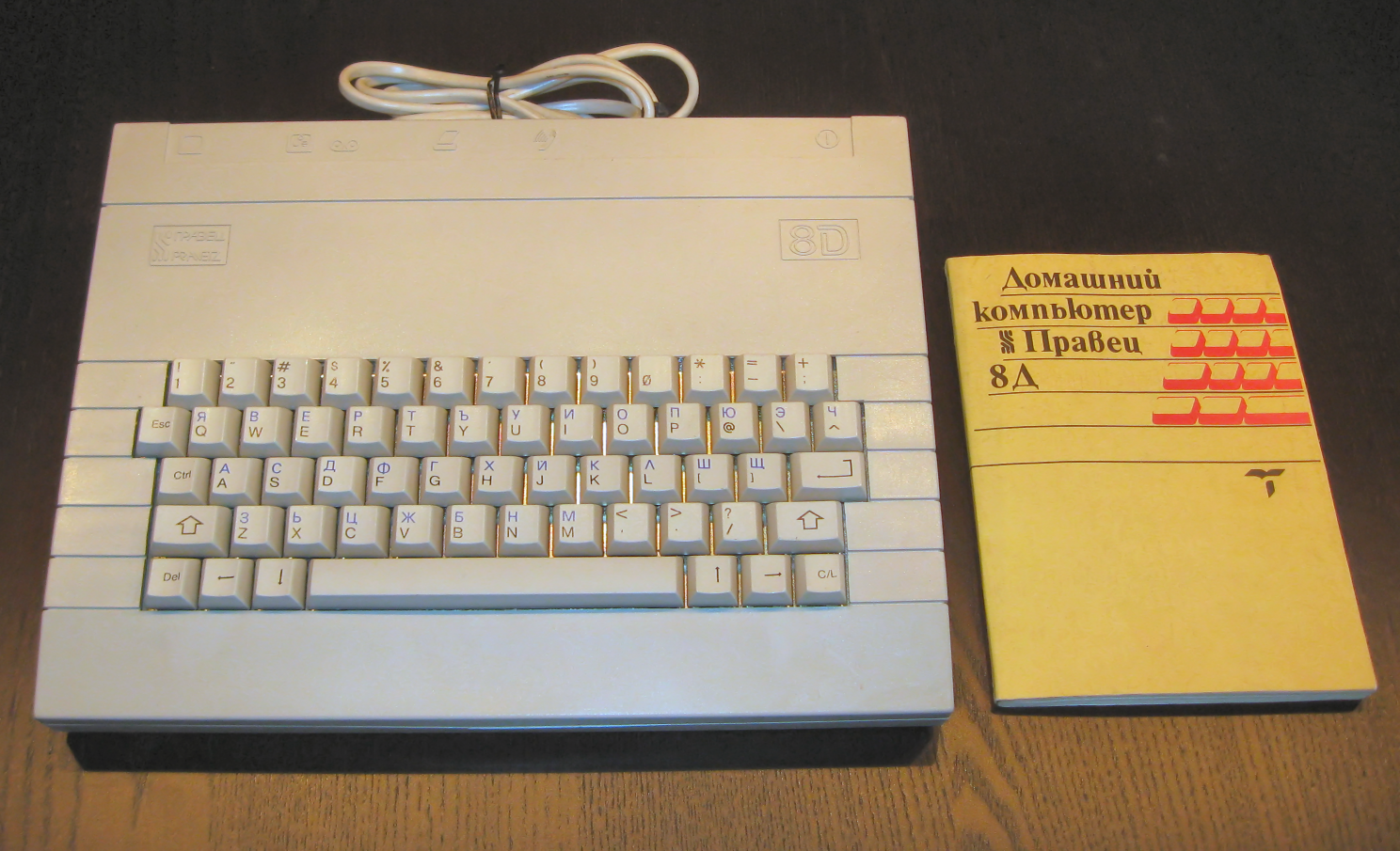 The aim of end user
The aim of end user documentation
Documentation is any communicable material that is used to describe, explain or instruct regarding some attributes of an object, system or procedure, such as its parts, assembly, installation, maintenance, and use. As a form of knowledge managem ...
(e.g., manuals and guidebooks for products) is to help the user understand certain aspects of the systems and to provide all the answers in one place. A lot of documentation is available for users to help them understand and properly use a certain product or service. Due to the fact that the information available is usually very vast, inconsistent or ambiguous (e.g., a user manual with hundreds of pages, including guidance on using advanced features), many users suffer from an information overload. Therefore, they become unable to take the right course of action. This needs to be kept in mind when developing products and services and the necessary documentation for them.
Well-written documentation is needed for a user to reference. Some key aspects of such a documentation are:
* Specific titles and subtitles for subsections to aid the reader in finding sections
* Use of videos, annotated screenshot
A screenshot (also known as screen capture or screen grab) is an analog or digital image that shows the contents of a computer display. A screenshot is created by a (film) camera shooting the screen or the operating system
An operating sys ...
s, text and links to help the reader understand how to use the device or program
* Structured provision of information, which goes from the most basic instructions, written in plain language, without specialist jargon
Jargon, or technical language, is the specialized terminology associated with a particular field or area of activity. Jargon is normally employed in a particular Context (language use), communicative context and may not be well understood outside ...
or acronym
An acronym is a type of abbreviation consisting of a phrase whose only pronounced elements are the initial letters or initial sounds of words inside that phrase. Acronyms are often spelled with the initial Letter (alphabet), letter of each wor ...
s, progressing to the information that intermediate or advanced users will need (these sections can include jargon and acronyms, but each new term should be defined or spelled out upon its first use)
* Easy to search the help guide, find information and access information
* Clear end results are described to the reader (e.g., "When the program is installed properly, an icon will appear in the left-hand corner of your screen and the LED
A light-emitting diode (LED) is a semiconductor device that emits light when current flows through it. Electrons in the semiconductor recombine with electron holes, releasing energy in the form of photons. The color of the light (corresp ...
will turn on...")
* Detailed, numbered steps, to enable users with a range of proficiency levels (from novice to advanced) to go step-by-step to install, use and troubleshoot
Troubleshooting is a form of problem solving, often applied to repair failed products or processes on a machine or a system. It is a logical, systematic search for the source of a problem in order to solve it, and make the product or process ope ...
the product or service
* Unique Uniform Resource Locator
A uniform resource locator (URL), colloquially known as an address on the World Wide Web, Web, is a reference to a web resource, resource that specifies its location on a computer network and a mechanism for retrieving it. A URL is a specific t ...
(URLs) so that the user can go to the product website to find additional help and resources.
At times users do not refer to the documentation available to them due to various reasons, ranging from finding the manual too large or due to not understanding the jargon and acronyms it contains. In other cases, the users may find that the manual makes too many assumptions about a user having pre-existing knowledge of computers and software, and thus the directions may skip over these initial steps (from the users' point of view). Thus, frustrated user may report false problems because of their inability to understand the software or computer hardware. This in turn causes the company to focus on perceived problems instead of focusing on the actual problems of the software.
Security
In the 2010s, there is a lot of emphasis on user's security and privacy. With the increasing role that computers are playing in people's lives, people are carryinglaptop
A laptop computer or notebook computer, also known as a laptop or notebook, is a small, portable personal computer (PC). Laptops typically have a Clamshell design, clamshell form factor (design), form factor with a flat-panel computer scree ...
s and smartphone
A smartphone is a mobile phone with advanced computing capabilities. It typically has a touchscreen interface, allowing users to access a wide range of applications and services, such as web browsing, email, and social media, as well as multi ...
s with them and using them for scheduling appointments, making online purchases using credit cards and searching for information. These activities can potentially be observed by companies, governments or individuals, which can lead to breaches of privacy, identity theft
Identity theft, identity piracy or identity infringement occurs when someone uses another's personal identifying information, like their name, identifying number, or credit card number, without their permission, to commit fraud or other crimes. ...
, by, blackmailing and other serious concerns. As well, many businesses, ranging from small business
Small businesses are types of corporations, partnerships, or sole proprietorships which have a small number of employees and/or less annual revenue than a regular-sized business or corporation. Businesses are defined as "small" in terms of being ...
startups
A startup or start-up is a company or project undertaken by an Entrepreneurship, entrepreneur to seek, develop, and validate a scalable business model. While entrepreneurship includes all new businesses including self-employment and businesses tha ...
to huge corporations are using computers and software to design, manufacture, market and sell their products and services, and businesses also use computers and software in their back office
A back office in most corporations is where work that supports '' front office'' work is done. The front office is the "face" of the company and is all the resources of the company that are used to make sales and interact with customers and clien ...
processes (e.g., human resources
Human resources (HR) is the set of people who make up the workforce of an organization, business sector, industry, or economy. A narrower concept is human capital, the knowledge and skills which the individuals command. Similar terms include ' ...
, payroll
A payroll is a list of employment, employees of a company who are entitled to receive compensation as well as other work benefits, as well as the amounts that each should obtain. Along with the amounts that each employee should receive for time ...
, etc.). As such, it is important for people and organizations to know that the information and data they are storing, using, or sending over computer networks, or storing on computer systems, is secure.
However, developers of software and hardware are faced with many challenges in developing a system that can be both user friendly
''User Friendly'' was a webcomic written by J. D. Frazer, also known by his pen name Illiad. Starting in 1997, the strip was one of the earliest webcomics to make its creator a living. The comic is set in a fictional internet service provider a ...
, accessible 24/7 on almost any device, and be truly secure. Security leaks happen, even to individuals and organizations that have security measures in place to protect their data and information (e.g., firewalls, encryption
In Cryptography law, cryptography, encryption (more specifically, Code, encoding) is the process of transforming information in a way that, ideally, only authorized parties can decode. This process converts the original representation of the inf ...
, strong password
Password strength is a measure of the effectiveness of a password against guessing or brute-force attacks. In its usual form, it estimates how many trials an attacker who does not have direct access to the password would need, on average, to gues ...
s). The complexities of creating such a secure system come from the fact that the behaviour of humans is not always rational or predictable. Even in a very-well secured computer system, a malicious individual can telephone a worker and pretend to be a private investigator
A private investigator (often abbreviated to PI; also known as a private detective, an inquiry agent or informally a wikt:private eye, private eye) is a person who can be hired by individuals or groups to undertake investigatory law services. ...
working for the software company, and ask for the individual's password, a dishonest process called phishing
Phishing is a form of social engineering and a scam where attackers deceive people into revealing sensitive information or installing malware such as viruses, worms, adware, or ransomware. Phishing attacks have become increasingly sophisticate ...
. As well, even with a well-secured system, if a worker decides to put the company's electronic files on a USB drive to take them home to work on them over the weekend (against many companies' policies), and then loses this USB drive, the company's data may be compromised. Therefore, developers need to make systems that are intuitive to the user in order to have information security
Information security is the practice of protecting information by mitigating information risks. It is part of information risk management. It typically involves preventing or reducing the probability of unauthorized or inappropriate access to data ...
and system security.
Another key step to end user security is informing the people and employees about the security threats and what they can do to avoid them or protect themselves and the organization. Clearly underlining the capabilities and risks makes users more aware and informed whilst they are using the products.
Some situations that could put the user at risk are:
* Auto-logon as administrator options
* Auto-fill options, in which a computer or program remembers a user's personal information and HTTP cookie
HTTP cookie (also called web cookie, Internet cookie, browser cookie, or simply cookie) is a small block of data (computing), data created by a web server while a user (computing), user is browsing a website and placed on the user's computer o ...
s
* Opening junk emails of suspicious emails and/or opening/running attachments or computer files contained in these
* Email being monitored by third parties, especially when using Wi-Fi connections
* Unsecure Wi-Fi
Wi-Fi () is a family of wireless network protocols based on the IEEE 802.11 family of standards, which are commonly used for Wireless LAN, local area networking of devices and Internet access, allowing nearby digital devices to exchange data by ...
or use of a public Wi-Fi network at a coffee shop or hotel
* Weak password
A password, sometimes called a passcode, is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of password-protected services t ...
s (using a person's own name, own birthdate, name or birthdate of children, or easy-to-guess passwords such as "1234")
* Malicious programs such as viruses
Even if the security measures in place are strong, the choices the user makes and his/her behavior have a major impact on how secure their information really is. Therefore, an informed user is one who can protect and achieve the best security out of the system they use. Because of the importance of end-user security and the impact it can have on organizations the UK government set out a guidance for the public sector, to help civil servant
The civil service is a collective term for a sector of government composed mainly of career civil service personnel hired rather than elected, whose institutional tenure typically survives transitions of political leadership. A civil service offic ...
s learn how to be more security aware when using government networks and computers. While this is targeted to a certain sector, this type of educational effort can be informative to any type of user. This helps developers meet security norms and end users be aware of the risks involved.
Reimers and Andersson have conducted a number of studies on end-user security habits and found that the same type of repeated education/training in security best practices can have a marked effect on the perception of compliance with good end-user network security habits, especially concerning malware and ransomware.
Law
Inend-user license agreement
An end-user license agreement or EULA () is a legal contract between a software supplier and a customer or end-user.
The practice of selling licenses to rather than copies of software predates the recognition of software copyright, which has ...
s, the end user is distinguished from the value-added reseller who installs the software or the organization that purchases and manages the software.
Certain American defense-related products and information require export approval from the United States Government under the International Traffic in Arms Regulations and Export Administration Regulations
The Export Administration Regulations (EAR) are a set of United States export guidelines and prohibitions. They are administered by the Bureau of Industry and Security, which regulates the export restrictions of sensitive goods. The EAR apply ...
. In order to obtain a license to export, the exporter must specify both the end user and the end use for undertaking an end-user certificate.
In the UK, there exist documents that accompany licenses for products named in the end user undertaking statements.
See also
* End-user computing * End-user development * Voice of the customer *User guide
A user guide, also commonly known as a user manual, is intended to assist users in using a particular product, service or application. It is usually written by a technician, product developer, or a company's customer service staff.
Most user gu ...
Notes
References
External links
*{{Citation , last1=Ward , first1=Sandra N. , title=Teaching University Student End-Users about Online Searching , date=2019-12-06 , url=http://dx.doi.org/10.4324/9780429346101-3 , work=Serving End-Users in Sci-Tech Libraries , pages=17–32 , access-date=2023-12-23 , publisher=Routledge , isbn=978-0-429-34610-1 , last2=Osegueda , first2=Laura M., doi=10.4324/9780429346101-3 , url-access=subscription Computing terminology Export and import control Consumer