Counterterrorism And The European Union on:
[Wikipedia]
[Google]
[Amazon]

 Counterterrorism (also spelled counter-terrorism), also known as anti-terrorism, incorporates the practices,
Counterterrorism (also spelled counter-terrorism), also known as anti-terrorism, incorporates the practices,
 Most counter-terrorism strategies involve an increase in standard police and domestic intelligence. The central activities are traditional: interception of communications and the tracing of persons. New technology has, however, expanded the range of military and law enforcement operations.
Domestic intelligence is often directed at specific groups, defined based on origin or religion, which is a source of political controversy.
Most counter-terrorism strategies involve an increase in standard police and domestic intelligence. The central activities are traditional: interception of communications and the tracing of persons. New technology has, however, expanded the range of military and law enforcement operations.
Domestic intelligence is often directed at specific groups, defined based on origin or religion, which is a source of political controversy.
 One of the primary difficulties of implementing effective counter-terrorist measures is the waning of civil liberties and individual privacy that such measures often entail, both for citizens of, and for those detained by states attempting to combat terror. At times, measures designed to tighten security have been seen as abuses of power or even violations of human rights.
Examples of these problems can include prolonged, incommunicado detention without judicial review or long periods of 'preventive detention'; risk of subjecting to torture during the transfer, return and extradition of people between or within countries; and the adoption of security measures that restrain the rights or freedoms of citizens and breach principles of non-discrimination. Examples include:
* In November 2003, Malaysia passed new counter-terrorism laws, widely criticized by local human rights groups for being vague and overbroad. Critics claim that the laws put the fundamental rights of free expression, association, and assembly at risk. Malaysia persisted in holding around 100 alleged militants without trial, including five Malaysian students detained for alleged terrorist activity while studying in Karachi, Pakistan.
* In November 2003, a Canadian-Syrian national, Maher Arar, publicly alleged that he had been tortured in a Syrian prison after being handed over to the Syrian authorities by the U.S.
* In December 2003, Colombia's congress approved legislation that would give the military the power to arrest, tap telephones, and carry out searches without warrants or any previous judicial order.
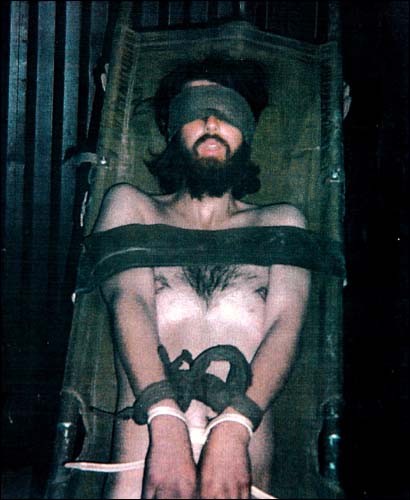
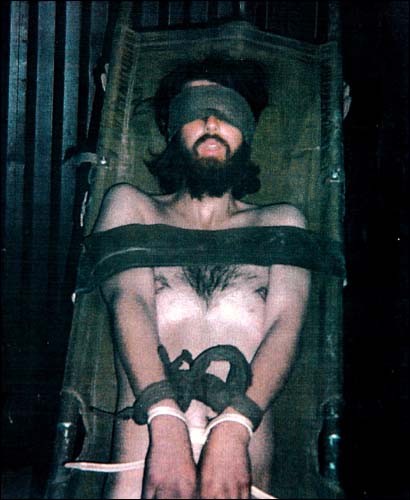
* Images of unpopular treatment of detainees in U.S. custody in Iraq and other locations have encouraged international scrutiny of U.S. operations in the war on terror.
* Hundreds of foreign nationals remain in prolonged indefinite detention without charge or trial in Guantánamo Bay, despite international and U.S. constitutional standards some groups believe outlaw such practices.
* Hundreds of people suspected of connections with the Taliban or
One of the primary difficulties of implementing effective counter-terrorist measures is the waning of civil liberties and individual privacy that such measures often entail, both for citizens of, and for those detained by states attempting to combat terror. At times, measures designed to tighten security have been seen as abuses of power or even violations of human rights.
Examples of these problems can include prolonged, incommunicado detention without judicial review or long periods of 'preventive detention'; risk of subjecting to torture during the transfer, return and extradition of people between or within countries; and the adoption of security measures that restrain the rights or freedoms of citizens and breach principles of non-discrimination. Examples include:
* In November 2003, Malaysia passed new counter-terrorism laws, widely criticized by local human rights groups for being vague and overbroad. Critics claim that the laws put the fundamental rights of free expression, association, and assembly at risk. Malaysia persisted in holding around 100 alleged militants without trial, including five Malaysian students detained for alleged terrorist activity while studying in Karachi, Pakistan.
* In November 2003, a Canadian-Syrian national, Maher Arar, publicly alleged that he had been tortured in a Syrian prison after being handed over to the Syrian authorities by the U.S.
* In December 2003, Colombia's congress approved legislation that would give the military the power to arrest, tap telephones, and carry out searches without warrants or any previous judicial order.
* Images of unpopular treatment of detainees in U.S. custody in Iraq and other locations have encouraged international scrutiny of U.S. operations in the war on terror.
* Hundreds of foreign nationals remain in prolonged indefinite detention without charge or trial in Guantánamo Bay, despite international and U.S. constitutional standards some groups believe outlaw such practices.
* Hundreds of people suspected of connections with the Taliban or
online
/ref>
 The human security paradigm outlines a non-military approach that aims to address the enduring underlying inequalities which fuel terrorist activity. Causal factors need to be delineated and measures implemented which allow equal access to resources and
The human security paradigm outlines a non-military approach that aims to address the enduring underlying inequalities which fuel terrorist activity. Causal factors need to be delineated and measures implemented which allow equal access to resources and
 As Israel is suffering from constant shelling of its cities, towns, and settlements by artillery rockets from the
As Israel is suffering from constant shelling of its cities, towns, and settlements by artillery rockets from the
 Many countries have dedicated counterterrorist units trained to handle terrorist threats. Besides various security agencies, there are police tactical units whose role is to directly engage terrorists and prevent terrorist attacks.
Such units perform both in preventive actions, hostage rescue, and responding to ongoing attacks. Countries of all sizes can have highly trained counterterrorist teams. Tactics, techniques, and procedures for manhunting are under constant development.
These units are specially trained in
Many countries have dedicated counterterrorist units trained to handle terrorist threats. Besides various security agencies, there are police tactical units whose role is to directly engage terrorists and prevent terrorist attacks.
Such units perform both in preventive actions, hostage rescue, and responding to ongoing attacks. Countries of all sizes can have highly trained counterterrorist teams. Tactics, techniques, and procedures for manhunting are under constant development.
These units are specially trained in
 Some counter-terrorist actions of the 20th and 21st centuries are listed below. See list of hostage crises for a more extended list, including hostage-takings that did not end violently.
Some counter-terrorist actions of the 20th and 21st centuries are listed below. See list of hostage crises for a more extended list, including hostage-takings that did not end violently.
 Pursuant to passage of the
Pursuant to passage of the

''A Fear Management Approach to Counter-Terrorism'' (International Centre for Counter-Terrorism – The Hague, 2012)
* J.M. Berger
''Making CVE Work: A Focused Approach Based on Process Disruption''
(International Centre for Counter-Terrorism – The Hague, May 2016 * Janos Besenyo
Low-cost attacks, unnoticeable plots?
Overview on the economical character of current terrorism, Strategic Impact (ROMANIA) (ISSN: 1841–5784) (eISSN: 1824–9904) 62/2017: (Issue No. 1) pp. 83–100. * Deflem, Mathieu. 2020
In The Handbook of Collective Violence: Current Developments and Understanding, eds. C.A. Ireland, et al. Abingdon, UK: Routledge. * Deflem, Mathieu, and Stephen Chicoine. 2019
In The Handbook of Social Control, edited by Mathieu Deflem. Hoboken, NJ: Wiley-Blackwell. * Deflem, Mathieu and Shannon McDonough. 2015
Society 52(1):70–79. * Gagliano Giuseppe, ''Agitazione sovversiva, guerra psicologica e terrorismo'' (2010) , Uniservice Books. * Ishmael Jones, ''The Human Factor: Inside the CIA's Dysfunctional Intelligence Culture'' (2008, revised 2010) , Encounter Books. * Ivan Arreguín-Toft, "Tunnel at the End of the Light: A Critique of U.S. Counter-terrorist Grand Strategy," ''Cambridge Review of International Affairs'', Vol. 15, No. 3 (2002), pp. 549–563. * Ivan Arreguín-Toft, "How to Lose a War on Terror: A Comparative Analysis of a Counterinsurgency Success and Failure," in Jan Ångström and Isabelle Duyvesteyn, Eds., ''Understanding Victory and Defeat in Contemporary War'' (London: Frank Cass, 2007). * James Mitchell, "Identifying Potential Terrorist Targets" a study in the use of convergence. G2 Whitepaper on terrorism, copyright 2006, G2. Counterterrorism Conference, June 2006, Washington D.C. *
''Boundaries of the Battlefield: A Critical Look at the Legal Paradigms and Rules in Countering Terrorism'' (International Centre for Counter-Terrorism – The Hague, 2013)
* Judy Kuriansky (Editor), "Terror in the Holy Land: Inside the Anguish of the Israeli-Palestinian Conflict" (2006, , Praeger Publishers). * Lynn Zusman (Editor),
The Law of Counterterrorism
(2012, , American Bar Association).* Marc Sageman, ''Understanding Terror Networks'' (Philadelphia, PA: University of Pennsylvania Press, 2004), . * Newton Lee, ''Counterterrorism and Cybersecurity: Total Information Awareness (Second Edition)'' (Switzerland: Springer International Publishing, 2015), . * Teemu Sinkkonen, ''Political Responses to Terrorism'' (Acta Universitatis Tamperensis, 2009), . * Vandana Asthana,
Cross-Border Terrorism in India: Counterterrorism Strategies and Challenges
" ''ACDIS Occasional Paper'' (June 2010), Program in Arms Control, Disarmament, and International Security (ACDIS), University of Illinois
U.S. Bureau of CounterterrorismUK Counter Terrorism Policing«Public order and safety» – International project on combating crime and terrorism
{{Authority control Law enforcement Security National security Public safety

 Counterterrorism (also spelled counter-terrorism), also known as anti-terrorism, incorporates the practices,
Counterterrorism (also spelled counter-terrorism), also known as anti-terrorism, incorporates the practices, military tactics
Military tactics encompasses the art of organizing and employing fighting forces on or near the battlefield. They involve the application of four battlefield functions which are closely related – kinetic or firepower, Mobility (military), mobil ...
, techniques, and strategies that governments, law enforcement, business
Business is the practice of making one's living or making money by producing or Trade, buying and selling Product (business), products (such as goods and Service (economics), services). It is also "any activity or enterprise entered into for pr ...
, and intelligence agencies use to combat or eliminate terrorism. Counterterrorism strategies are a government's motivation to use the instruments of national power to defeat terrorists, the organizations they maintain, and the networks they contain.
If definitions of terrorism are part of a broader insurgency, counterterrorism may employ counterinsurgency measures. The United States Armed Forces uses the term foreign internal defense for programs that support other countries' attempts to suppress insurgency, lawlessness, or subversion
Subversion () refers to a process by which the values and principles of a system in place are contradicted or reversed in an attempt to transform the established social order and its structures of power, authority, hierarchy, and social norms. Sub ...
, or to reduce the conditions under which threats to national security
National security, or national defence, is the security and defence of a sovereign state, including its citizens, economy, and institutions, which is regarded as a duty of government. Originally conceived as protection against military atta ...
may develop.
History
The first counter-terrorism body formed was the Special Irish Branch of theMetropolitan Police
The Metropolitan Police Service (MPS), formerly and still commonly known as the Metropolitan Police (and informally as the Met Police, the Met, Scotland Yard, or the Yard), is the territorial police force responsible for law enforcement and ...
, later renamed the Special Branch
Special Branch is a label customarily used to identify units responsible for matters of national security and Intelligence (information gathering), intelligence in Policing in the United Kingdom, British, Commonwealth of Nations, Commonwealth, ...
after it expanded its scope beyond its original focus on Fenian terrorism. Law enforcement agencies established similar units in the United Kingdom and elsewhere. The first tactical counterterrorist unit was GSG 9
, formerly (), is the police tactical unit of the German Federal Police ''(Bundespolizei (Germany), Bundespolizei)''. The state police (''Landespolizei'') maintain their own tactical units known as the ''Special Deployment Commando, Spezialein ...
of the German Federal Police, formed in response to the 1972 Munich massacre.
Counter-terrorism forces expanded with the perceived growing threat of terrorism in the late 20th century. After the September 11 attacks, Western governments made counter-terrorism efforts a priority, including more foreign cooperation, shifting tactics involving red teams, and preventive measures. Although sensational attacks in the developed world receive a great deal of media attention, most terrorism occurs in less developed countries. Government responses to terrorism, in some cases, can lead to substantial unintended consequences, such as in the above-mentioned Munich massacre.
Planning
Intelligence, surveillance, and reconnaissance
 Most counter-terrorism strategies involve an increase in standard police and domestic intelligence. The central activities are traditional: interception of communications and the tracing of persons. New technology has, however, expanded the range of military and law enforcement operations.
Domestic intelligence is often directed at specific groups, defined based on origin or religion, which is a source of political controversy.
Most counter-terrorism strategies involve an increase in standard police and domestic intelligence. The central activities are traditional: interception of communications and the tracing of persons. New technology has, however, expanded the range of military and law enforcement operations.
Domestic intelligence is often directed at specific groups, defined based on origin or religion, which is a source of political controversy. Mass surveillance
Mass surveillance is the intricate surveillance of an entire or a substantial fraction of a population in order to monitor that group of citizens. The surveillance is often carried out by local and federal governments or governmental organizati ...
of an entire population raises objections on civil liberties
Civil liberties are guarantees and freedoms that governments commit not to abridge, either by constitution, legislation, or judicial interpretation, without due process. Though the scope of the term differs between countries, civil liberties may ...
grounds. Domestic terrorists, especially lone wolves, are often harder to detect because of their citizenship or legal status and ability to stay under the radar.
To select the effective action when terrorism appears to be more of an isolated event, the appropriate government organizations need to understand the source, motivation, methods of preparation, and tactics of terrorist groups. Good intelligence is at the heart of such preparation, as well as a political and social understanding of any grievances that might be solved. Ideally, one gets information from inside the group, a very difficult challenge for human intelligence operations because operational terrorist cells are often small, with all members known to one another, perhaps even related.
Counterintelligence is a great challenge with the security of cell-based systems, since the ideal, but the nearly impossible, goal is to obtain a clandestine source within the cell. Financial tracking can play a role, as a communications intercept. However, both of these approaches need to be balanced against legitimate expectations of privacy.
Legal contexts
In response to the growing legislation. ; * The United Kingdom has had anti-terrorism legislation in place for more than thirty years. The Prevention of Violence Act 1939 was brought in response to an Irish Republican Army (IRA) campaign of violence under the S-Plan. This act had been allowed to expire in 1953. It was repealed in 1973 to be replaced by the Prevention of Terrorism Acts, a response to the Troubles in Northern Ireland. From 1974 to 1989, the temporary provisions of the act were renewed annually. * In 2000 the Acts were replaced with the more permanent Terrorism Act 2000, which contained many of their powers, and then the Prevention of Terrorism Act 2005. * The Anti-terrorism, Crime and Security Act 2001 was formally introduced into the Parliament on November 19, 2001, two months after theSeptember 11, 2001 attacks
The September 11 attacks, commonly known as 9/11, were four coordinated suicide terrorist attacks carried out by al-Qaeda against the United States on Tuesday, September 11, 2001. That morning, nineteen terrorists hijacked four commercial ...
in the United States. It received royal assent and went into force on December 13, 2001. On December 16, 2004, the Law Lords ruled that Part 4 was incompatible with the European Convention on Human Rights. However, under the terms of the Human Rights Act 1998
The Human Rights Act 1998 (c. 42) is an Act of Parliament of the United Kingdom which received royal assent on 9 November 1998, and came into force on 2 October 2000. Its aim was to incorporate into UK law the rights contained in the European Con ...
, it remained in force. The Prevention of Terrorism Act 2005 was drafted to answer the Law Lords ruling and the Terrorism Act 2006 creates new offenses related to terrorism, and amends existing ones. The act was drafted in the aftermath of the 7 July 2005 London bombings and, like its predecessors, some of its terms have proven to be highly controversial.
Since 1978 the UK's terrorism laws have been regularly reviewed by a security-cleared Independent Reviewer of Terrorism Legislation, whose often influential reports are submitted to Parliament and published in full.
;
* U.S. legal issues surrounding this issue include rulings on the domestic employment of deadly force by law enforcement agencies.
* Search and seizure is governed by the Fourth Amendment to the United States Constitution
The Fourth Amendment (Amendment IV) to the United States Constitution is part of the Bill of Rights. It prohibits unreasonable searches and seizures. In addition, it sets requirements for issuing warrants: warrants must be issued by a judge o ...
.
* The U.S. passed the USA PATRIOT Act after the September 11 attacks, as well as a range of other legislation and executive orders
''Executive Orders'' is a techno-thriller novel, written by Tom Clancy and released on July 1, 1996. It picks up immediately where the final events of ''Debt of Honor'' (1994) left off, and features now-U.S. President Jack Ryan as he tries to d ...
relating to national security.
* The Department of Homeland Security was established to consolidate domestic security agencies to coordinate anti-terrorism and national response to major natural disasters and accidents.
* The Posse Comitatus Act limits domestic employment of the United States Army and the United States Air Force, requiring Presidential approval before deploying the Army or the Air Force. Pentagon
In geometry, a pentagon (from the Greek πέντε ''pente'' meaning ''five'' and γωνία ''gonia'' meaning ''angle'') is any five-sided polygon or 5-gon. The sum of the internal angles in a simple pentagon is 540°.
A pentagon may be simpl ...
policy also applies this limitation to the United States Marine Corps and the United States Navy, because the Posse Comitatus Act does not cover naval services, even though they are federal military forces. The Department of Defense can be employed domestically on Presidential order, as was done during the Los Angeles riots of 1992
The 1992 Los Angeles riots, sometimes called the 1992 Los Angeles uprising and the Los Angeles Race Riots, were a series of riots and civil disturbances that occurred in Los Angeles County, California, in April and May 1992. Unrest began in S ...
, Hurricane Katrina
Hurricane Katrina was a destructive Category 5 Atlantic hurricane that caused over 1,800 fatalities and $125 billion in damage in late August 2005, especially in the city of New Orleans and the surrounding areas. It was at the time the cost ...
, and the Beltway Sniper incidents.
* External or international use of lethal force would require a Presidential finding.
* In February 2017, sources claimed that the Trump administration intends to rename and revamp the U.S. government program Countering Violent Extremism
Counterterrorism (also spelled counter-terrorism), also known as anti-terrorism, incorporates the practices, military tactics, techniques, and strategies that governments, law enforcement, business, and intelligence agencies use to combat or el ...
(CVE) to focus solely on Islamist extremism.
;
;
* Australia has passed several anti-terrorism acts. In 2004, a bill comprising three acts Anti-terrorism Act, 2004, (No 2) and (No 3) was passed. Then Attorney-General, Philip Ruddock, introduced the ''Anti-terrorism bill, 2004'' on March 31. He described it as ''"a bill to strengthen Australia's counter-terrorism laws in a number of respects – a task made more urgent following the recent tragic terrorist bombings in Spain."'' He said that Australia's counter-terrorism laws "require review and, where necessary, updating if we are to have a legal framework capable of safeguarding all Australians from the scourge of terrorism." The Australian Anti-Terrorism Act 2005
The ''Anti-Terrorism Act 2005'' (Cth) is an Act of the Parliament of Australia, which is intended to hamper the activities of any potential terrorists in the country. The counter-terrorism law was passed on 6 December 2005.
Background
Hi ...
supplemented the powers of the earlier acts. The Australian legislation allows police to detain suspects for up to two weeks without charge and to electronically track suspects for up to a year. The Australian Anti-Terrorism Act of 2005 included a "shoot-to-kill" clause. In a country with entrenched liberal democratic traditions, the measures are controversial and have been criticized by civil libertarians and Islam
Islam (; ar, ۘالِإسلَام, , ) is an Abrahamic religions, Abrahamic Monotheism#Islam, monotheistic religion centred primarily around the Quran, a religious text considered by Muslims to be the direct word of God in Islam, God (or ...
ic groups.
;
;
* Israel monitors a list of designated terrorist organizations and has laws forbidding membership in such organizations and funding or helping them.
* On December 14, 2006, the Israeli Supreme Court ruled targeted killings were a permitted form of self-defense.
* In 2016 the Israeli Knesset passed a comprehensive law against terrorism, forbidding any kind of terrorism and support of terrorism, and setting severe punishments for terrorists. The law also regulates legal efforts against terrorism.
Human rights
 One of the primary difficulties of implementing effective counter-terrorist measures is the waning of civil liberties and individual privacy that such measures often entail, both for citizens of, and for those detained by states attempting to combat terror. At times, measures designed to tighten security have been seen as abuses of power or even violations of human rights.
Examples of these problems can include prolonged, incommunicado detention without judicial review or long periods of 'preventive detention'; risk of subjecting to torture during the transfer, return and extradition of people between or within countries; and the adoption of security measures that restrain the rights or freedoms of citizens and breach principles of non-discrimination. Examples include:
* In November 2003, Malaysia passed new counter-terrorism laws, widely criticized by local human rights groups for being vague and overbroad. Critics claim that the laws put the fundamental rights of free expression, association, and assembly at risk. Malaysia persisted in holding around 100 alleged militants without trial, including five Malaysian students detained for alleged terrorist activity while studying in Karachi, Pakistan.
* In November 2003, a Canadian-Syrian national, Maher Arar, publicly alleged that he had been tortured in a Syrian prison after being handed over to the Syrian authorities by the U.S.
* In December 2003, Colombia's congress approved legislation that would give the military the power to arrest, tap telephones, and carry out searches without warrants or any previous judicial order.
* Images of unpopular treatment of detainees in U.S. custody in Iraq and other locations have encouraged international scrutiny of U.S. operations in the war on terror.
* Hundreds of foreign nationals remain in prolonged indefinite detention without charge or trial in Guantánamo Bay, despite international and U.S. constitutional standards some groups believe outlaw such practices.
* Hundreds of people suspected of connections with the Taliban or
One of the primary difficulties of implementing effective counter-terrorist measures is the waning of civil liberties and individual privacy that such measures often entail, both for citizens of, and for those detained by states attempting to combat terror. At times, measures designed to tighten security have been seen as abuses of power or even violations of human rights.
Examples of these problems can include prolonged, incommunicado detention without judicial review or long periods of 'preventive detention'; risk of subjecting to torture during the transfer, return and extradition of people between or within countries; and the adoption of security measures that restrain the rights or freedoms of citizens and breach principles of non-discrimination. Examples include:
* In November 2003, Malaysia passed new counter-terrorism laws, widely criticized by local human rights groups for being vague and overbroad. Critics claim that the laws put the fundamental rights of free expression, association, and assembly at risk. Malaysia persisted in holding around 100 alleged militants without trial, including five Malaysian students detained for alleged terrorist activity while studying in Karachi, Pakistan.
* In November 2003, a Canadian-Syrian national, Maher Arar, publicly alleged that he had been tortured in a Syrian prison after being handed over to the Syrian authorities by the U.S.
* In December 2003, Colombia's congress approved legislation that would give the military the power to arrest, tap telephones, and carry out searches without warrants or any previous judicial order.
* Images of unpopular treatment of detainees in U.S. custody in Iraq and other locations have encouraged international scrutiny of U.S. operations in the war on terror.
* Hundreds of foreign nationals remain in prolonged indefinite detention without charge or trial in Guantánamo Bay, despite international and U.S. constitutional standards some groups believe outlaw such practices.
* Hundreds of people suspected of connections with the Taliban or Al-Qaeda
Al-Qaeda (; , ) is an Islamic extremism, Islamic extremist organization composed of Salafist jihadists. Its members are mostly composed of Arab, Arabs, but also include other peoples. Al-Qaeda has mounted attacks on civilian and military ta ...
remain in long-term detention in Pakistan or in U.S.-controlled centers in Afghanistan.
* China has used the "war on terror" to justify its policies in the predominantly Muslim Xinjiang Uyghur Autonomous Region to stifle Uyghur identity.
* In Morocco, Saudi Arabia, Tunisia, Yemen, and other countries, scores of people have been arrested and arbitrarily detained in connection with suspected terrorist acts or links to opposition armed groups.
* Until 2005, eleven men remained in high security detention in the UK under the Anti-Terrorism, Crime and Security Act 2001.
* United Nations experts condemned the misuse of counter-terrorism powers by the Egyptian authorities following the arrest, detention, and designation of human rights activists Ramy Shaath and Zyad El-Elaimy as terrorists. The two activists were arrested in June 2019, and the first-ever renewal of remand detention for Shaath came for the 21st time in 19 months on 24 January 2021. Experts called it alarming, and demanded the urgent implementation of the Working Group's opinion and removal of the two's names from the “terrorism entities’ list.
Many argue that such violations of rights could exacerbate rather than counter the terrorist threat. Human rights activists argue for the crucial role of human rights protection as an intrinsic part to fight against terrorism. This suggests, as proponents of human security have long argued, that respecting human rights may indeed help us to incur security. Amnesty International
Amnesty International (also referred to as Amnesty or AI) is an international non-governmental organization focused on human rights, with its headquarters in the United Kingdom. The organization says it has more than ten million members and sup ...
included a section on confronting terrorism in the recommendations in the Madrid Agenda arising from the Madrid Summit on Democracy and Terrorism (Madrid March 8–11, 2005):
While international efforts to combat terrorism have focused on the need to enhance cooperation between states, proponents of human rights (as well as human security) have suggested that more effort needs to be given to the effective inclusion of human rights protection as a crucial element in that cooperation. They argue that international human rights obligations do not stop at borders, and a failure to respect human rights in one state may undermine its effectiveness in the global effort to cooperate to combat terrorism.Human Rights News (2004): "Human Rights and Counter-Terrorism", in the Briefing to the 60th Session of the UN Commission on Human Rightsonline
/ref>
Preemptive neutralization
Some countries see preemptive attacks as a legitimate strategy. This includes capturing, killing, or disabling suspected terrorists before they can mount an attack. Israel, the United Kingdom, the United States, and Russia have taken this approach, while Western European states generally do not. Another major method of preemptive neutralization is theinterrogation
Interrogation (also called questioning) is interviewing as commonly employed by law enforcement officers, military personnel, intelligence agencies, organized crime syndicates, and terrorist organizations with the goal of eliciting useful informa ...
of known or suspected terrorists to obtain information about specific plots, targets, the identity of other terrorists, whether or not the interrogation subjects himself is guilty of terrorist involvement. Sometimes more extreme methods are used to increase suggestibility, such as sleep deprivation
Sleep deprivation, also known as sleep insufficiency or sleeplessness, is the condition of not having adequate duration and/or quality of sleep to support decent alertness, performance, and health. It can be either chronic or acute and may vary ...
or drugs. Such methods may lead captives to offer false information in an attempt to stop the treatment, or due to the confusion caused by it. These methods are not tolerated by European powers. In 1978 the European Court of Human Rights ruled in the Ireland v. United Kingdom case that such methods amounted to a practice of inhuman and degrading treatment, and that such practices were in breach of the European Convention on Human Rights Article 3 (art. 3).
Non-military
 The human security paradigm outlines a non-military approach that aims to address the enduring underlying inequalities which fuel terrorist activity. Causal factors need to be delineated and measures implemented which allow equal access to resources and
The human security paradigm outlines a non-military approach that aims to address the enduring underlying inequalities which fuel terrorist activity. Causal factors need to be delineated and measures implemented which allow equal access to resources and sustainability
Specific definitions of sustainability are difficult to agree on and have varied in the literature and over time. The concept of sustainability can be used to guide decisions at the global, national, and individual levels (e.g. sustainable livi ...
for all people. Such activities empower citizens, providing "freedom from fear" and "freedom from want".
This can take many forms, including the provision of clean drinking water, education, vaccination programs, provision of food and shelter and protection from violence, military or otherwise. Successful human security campaigns have been characterized by the participation of a diverse group of actors, including governments, NGOs, and citizens.
Foreign internal defense programs provide outside expert assistance to a threatened government. FID can involve both non-military and military aspects of counter-terrorism.
A 2017 study found that "governance and civil society aid is effective in dampening domestic terrorism, but this effect is only present if the recipient country is not experiencing a civil conflict."
Military
Terrorism has often been used to justify military intervention in countries like Pakistan, where terrorists are said to be based. That was the primary stated justification for theU.S. invasion of Afghanistan
In late 2001, the United States and its close allies invaded Afghanistan and toppled the Taliban government. The invasion's aims were to dismantle al-Qaeda, which had executed the September 11 attacks, and to deny it a safe base of operation ...
. It was also a stated justification for the second Russian invasion of Chechnya
The Second Chechen War (russian: Втора́я чече́нская война́, ) took place in Chechnya and the border regions of the North Caucasus between the Russian Federation and the Chechen Republic of Ichkeria, from August 1999 t ...
.
Military intervention has not always been successful in stopping or preventing future terrorism, such as during the Malayan Emergency
The Malayan Emergency, also known as the Anti–British National Liberation War was a guerrilla war fought in British Malaya between communist pro-independence fighters of the Malayan National Liberation Army (MNLA) and the military forces o ...
, the Mau Mau uprising
The Mau Mau rebellion (1952–1960), also known as the Mau Mau uprising, Mau Mau revolt or Kenya Emergency, was a war in the British Kenya Colony (1920–1963) between the Kenya Land and Freedom Army (KLFA), also known as the ''Mau Mau'', an ...
, and most of the campaigns against the IRA during the Irish Civil War
The Irish Civil War ( ga, Cogadh Cathartha na hÉireann; 28 June 1922 – 24 May 1923) was a conflict that followed the Irish War of Independence and accompanied the establishment of the Irish Free State, an entity independent from the United ...
, the S-Plan, the Border Campaign (IRA) and the Troubles in Northern Ireland. Although military action can temporarily disrupt a terrorist group's operations temporarily, it sometimes does not end the threat completely.
Repression by the military in itself usually leads to short term victories, but tend to be unsuccessful in the long run (e.g., the French doctrine used in colonial Indochina and Algeria), particularly if it is not accompanied by other measures. However, new methods such as those taken in Iraq have yet to be seen as beneficial or ineffectual.
Preparation
Target-hardening
Whatever the target of terrorists, there are multiple ways of hardening the targets to prevent the terrorists from hitting their mark, or reducing the damage of attacks. One method is to place hostile vehicle mitigation to enforce protective standoff distance outside tall or politically sensitive buildings to preventcar bombings
A car bomb, bus bomb, lorry bomb, or truck bomb, also known as a vehicle-borne improvised explosive device (VBIED), is an improvised explosive device designed to be detonated in an automobile or other vehicles.
Car bombs can be roughly divide ...
. Another way to reduce the impact of attacks is to design buildings for rapid evacuation.
Aircraft cockpits are kept locked during flights and have reinforced doors, which only the pilots in the cabin are capable of opening. UK railway stations removed their garbage bins in response to the Provisional IRA threat, as convenient locations for depositing bombs. Scottish stations removed theirs after the 7 July 2005 London Bombings as a precautionary measure. The Massachusetts Bay Transportation Authority purchased bomb-resistant barriers after the September 11 attacks.
 As Israel is suffering from constant shelling of its cities, towns, and settlements by artillery rockets from the
As Israel is suffering from constant shelling of its cities, towns, and settlements by artillery rockets from the Gaza Strip
The Gaza Strip (;The New Oxford Dictionary of English (1998) – p.761 "Gaza Strip /'gɑːzə/ a strip of territory under the control of the Palestinian National Authority and Hamas, on the SE Mediterranean coast including the town of Gaza.. ...
(mainly by Hamas, but also by other Palestinian factions) and Lebanon (mainly by Hezbollah
Hezbollah (; ar, حزب الله ', , also transliterated Hizbullah or Hizballah, among others) is a Lebanese Shia Islamist political party and militant group, led by its Secretary-General Hassan Nasrallah since 1992. Hezbollah's parami ...
), Israel developed several defensive measures against artillery, rockets, and missiles. These include building a bomb shelter in every building and school, but also deploying active protection systems
An active protection system is a system designed to actively prevent certain anti-tank weapons from destroying a vehicle.
Countermeasures that either conceal the vehicle from, or disrupt the guidance of an incoming guided missile threat are design ...
such as the Arrow ABM, Iron Dome and David's Sling, which intercept the incoming threat in the air. Iron Dome has successfully intercepted hundreds of Qassam rockets and Grad rockets
The BM-21 "Grad" (russian: БМ-21 "Град", lit= hail) is a self-propelled 122 mm multiple rocket launcher designed in the Soviet Union. The system and the M-21OF rocket were first developed in the early 1960s, and saw their first comb ...
fired by Palestinians from the Gaza Strip.
A more sophisticated target-hardening approach must consider industrial and other critical industrial infrastructure that could be attacked. Terrorists do not need import chemical weapons if they can cause a major industrial accident such as the Bhopal disaster or the Halifax Explosion. Industrial chemicals in manufacturing, shipping, and storage thus require greater protection, and some efforts are in progress. To put this risk into perspective, the first major lethal chemical attack of World War I used 160 tons of chlorine; industrial shipments of chlorine, widely used in water purification and the chemical industry, travel in 90- or 55-ton tank cars.
To give one more example, the Northeast blackout of 2003 demonstrated the vulnerability of the North American electrical grid to natural disasters coupled with inadequate, possibly insecure, SCADA
Supervisory control and data acquisition (SCADA) is a control system architecture comprising computers, networked data communications and graphical user interfaces for high-level supervision of machines and processes. It also covers sensors and ...
(supervisory control and data acquisition) networks. Part of the vulnerability is due to deregulation, leading to much more interconnection in a grid designed for only occasional power-selling between utilities. A small number of terrorists, attacking critical power facilities when one or more engineers have infiltrated the power control centers, could wreak havoc.
Equipping likely targets with containers of pig lard has been used to discourage attacks by suicide bombers. The technique was apparently used on a limited scale by British authorities in the 1940s. The approach stems from the idea that Muslims perpetrating the attack would not want to be "soiled" by the lard in the moment before dying. The idea has been suggested more recently as a deterrent to suicide bombings in Israel. However, the actual effectiveness of this tactic is likely limited. A sympathetic Islamic scholar could issue a fatwa
A fatwā ( ; ar, فتوى; plural ''fatāwā'' ) is a legal ruling on a point of Islamic law (''sharia'') given by a qualified '' Faqih'' (Islamic jurist) in response to a question posed by a private individual, judge or government. A jurist i ...
proclaiming that a suicide bomber would not be polluted by the swine products.
Command and control
For a threatened or completed terrorist attack, an incident command system (ICS) may be invoked to control the various services that may need to be involved in the response. ICS has varied levels of escalation, such as might be required for multiple incidents in a given area (e.g.2005 London bombings
The 7 July 2005 London bombings, often referred to as 7/7, were a series of four coordinated suicide attacks carried out by Islamic terrorists in London that targeted commuters travelling on the city's public transport system during the mo ...
or the 2004 Madrid train bombings
The 2004 Madrid train bombings (also known in Spain as 11M) were a series of coordinated, nearly simultaneous bombings against the Cercanías Madrid, Cercanías commuter train system of Madrid, Spain, on the morning of 11 March 2004—three days ...
), or all the way to a national response plan invocation if national-level resources are needed. For example, a national response might be required for a nuclear, biological, radiological, or significant chemical attack.
Damage mitigation
Fire department
A fire department (American English) or fire brigade (Commonwealth English), also known as a fire authority, fire district, fire and rescue, or fire service in some areas, is an organization that provides fire prevention and fire suppression se ...
s, perhaps supplemented by public works agencies, utility providers, and heavy construction contractors, are most apt to deal with the physical consequences of an attack.
Local security
Again under an incident command model, local police can isolate the incident area, reducing confusion, and specialized police units can conduct tactical operations against terrorists, often using specialized counterterrorist tactical units. Bringing in such units will typically involve civil or military authority beyond the local level.Medical services
Emergency medical services are capable of triaging, treating, and transporting the more severely affected victims to hospitals, which typically have mass casualty and triage plans in place for terrorist attacks. Public health agencies, from local to the national level, may be designated to deal with identification, and sometimes mitigation, of possible biological attacks, and sometimes chemical or radiologic contamination.Tactical units
military tactics
Military tactics encompasses the art of organizing and employing fighting forces on or near the battlefield. They involve the application of four battlefield functions which are closely related – kinetic or firepower, Mobility (military), mobil ...
and are equipped for close-quarters combat, with emphasis on stealth and performing the mission with minimal casualties. The units include assault teams, sniper
A sniper is a military/paramilitary marksman who engages targets from positions of concealment or at distances exceeding the target's detection capabilities. Snipers generally have specialized training and are equipped with high-precision r ...
s, EOD experts, dog handlers, and intelligence officers. Most of these measures deal with terrorist attacks that affect an area or threaten to do so, or are lengthy situations such as shootouts and hostage takings that allow the counterterrorist units to assemble and respond; it is harder to deal with shorter incidents such as assassinations or reprisal attacks, due to the short warning time and the quick exfiltration of the assassins.
The majority of counterterrorism operations at the tactical level are conducted by state, federal, and national law enforcement or intelligence agencies. In some countries, the military may be called in as a last resort. For countries whose military is legally permitted to conduct domestic law enforcement operations, this is not an issue, and such counterterrorism operations are conducted by their military.
Counterterrorist operations
 Some counter-terrorist actions of the 20th and 21st centuries are listed below. See list of hostage crises for a more extended list, including hostage-takings that did not end violently.
Some counter-terrorist actions of the 20th and 21st centuries are listed below. See list of hostage crises for a more extended list, including hostage-takings that did not end violently.
Designing counterterrorist systems
The scope for anti-terrorism systems is very large in physical terms and in other dimensions, such as type and degree of terrorist threats, political and diplomatic ramifications, and legal concerns. Ideal counterterrorist systems use technology to enable persistent intelligence, surveillance and reconnaissance missions, and potential actions. Designing such a system-of-systems comprises a major technological project. A particular design problem for counterterrorist systems is the uncertainty of the future: the threat of terrorism may increase, decrease or remain the same, the type of terrorism and location are difficult to predict, and there are technological uncertainties. A potential solution is to incorporate engineering flexibility into system design, allowing for flexibility when new information arrives. Flexibility can be incorporated in the design of a counterterrorism system in the form of options that can be exercised in the future when new information is available.Law enforcement
While some countries with longstanding terrorism problems have law enforcement agencies primarily designed to prevent and respond to terror attacks, in other nations, counterterrorism is a relatively more recent objective of law enforcement agencies.Deflem, Mathieu. 2010. The Policing of Terrorism: Organizational and Global Perspectives. New York: Routledge. Though some civil libertarians and criminal justice scholars have criticized efforts of law enforcement agencies to combat terrorism as futile and expensive or as threats to civil liberties, other scholars have analyzed the most important dimensions of the policing of terrorism as an important dimension of counter-terrorism, especially in the post-9/11 era, and have discussed how police view terrorism as a matter of crime control. Such analyses highlight the civilian police role in counterterrorism next to the military model of a war on terror.American law enforcement
 Pursuant to passage of the
Pursuant to passage of the Homeland Security Act of 2002
The Homeland Security Act (HSA) of 2002, () was introduced in the aftermath of the September 11 attacks and subsequent mailings of anthrax spores. The HSA was cosponsored by 118 members of Congress. The act passed the U.S. Senate by a vote of ...
, federal, state, and local law enforcement agencies began to systemically reorganize. Two primary federal agencies, the Department of Justice (DOJ) and the Department of Homeland Security (DHS), house most of the federal agencies that are prepared to combat domestic and international terrorist attacks. These include the Border Patrol, the Secret Service, the Coast Guard and the FBI.
Following suit from federal changes pursuant to 9/11, however, most state and local law enforcement agencies began to include a commitment to "fighting terrorism" in their mission statements. Local agencies began to establish more patterned lines of communication with federal agencies. Some scholars have doubted the ability of local police to help in the war on terror and suggest their limited manpower is still best utilized by engaging community and targeting street crimes.
While counter-terror measures (most notably heightened airport security, immigrant profiling and border patrol) have been adapted during the last decade, to enhance counter-terror in law enforcement, there have been remarkable limitations to assessing the actual utility/effectiveness of law enforcement practices that are ostensibly preventative. Thus, while sweeping changes in counter-terrorism rhetoric redefined most American post 9/11 law enforcement agencies in theory, it is hard to assess how well such hyperbole has translated into practice.
In intelligence-led policing (ILP) efforts, the most quantitatively amenable starting point for measuring the effectiveness of any policing strategy (i.e.: Neighborhood Watch, Gun Abatement, Foot Patrols, etc.) is usually to assess total financial costs against clearance rates or arrest rates. Since terrorism is such a rare event phenomena, measuring arrests or clearance rates would be a non-generalizable and ineffective way to test enforcement policy effectiveness. Another methodological problem in assessing counter-terrorism efforts in law enforcement hinges on finding operational measures for key concepts in the study of homeland security. Both terrorism and homeland security are relatively new concepts for criminologists, and academicians have yet to agree on the matter of how to properly define these ideas in a way that is accessible.
Counter-terrorism agencies

Military
Within military operational approaches, counter-terrorism falls into the category ofirregular warfare
Irregular warfare (IW) is defined in United States joint doctrine as "a violent struggle among state and non-state actors for legitimacy and influence over the relevant populations." Concepts associated with irregular warfare are older than the te ...
.Kitzen M. (2020) Operations in Irregular Warfare. In: Sookermany A. (eds) Handbook of Military Sciences. p. 1-21. Springer, Cham Given the nature of operational counter-terrorism tasks national military organizations do not generally have dedicated units whose sole responsibility is the prosecution of these tasks. Instead the counter-terrorism function is an element of the role, allowing flexibility in their employment, with operations being undertaken in the domestic or international context.
In some cases the legal framework within which they operate prohibits military units conducting operations in the domestic arena; United States Department of Defense policy, based on the Posse Comitatus Act, forbids domestic counter-terrorism operations by the U.S. military. Units allocated some operational counter-terrorism tasks are frequently special forces
Special forces and special operations forces (SOF) are military units trained to conduct special operations. NATO has defined special operations as "military activities conducted by specially designated, organized, selected, trained and equip ...
or similar assets.
In cases where military organisations do operate in the domestic context some form of formal handover from the law enforcement community is regularly required, to ensure adherence to the legislative framework and limitations. such as the Iranian Embassy siege, the British police formally turned responsibility over to the Special Air Service
The Special Air Service (SAS) is a special forces unit of the British Army. It was founded as a regiment in 1941 by David Stirling and in 1950, it was reconstituted as a corps. The unit specialises in a number of roles including counter-terro ...
when the situation went beyond police capabilities.
See also
* Civilian casualty ratio * Counterinsurgency * Counter-IED efforts * Counterjihad * Deradicalization * Explosive detection * Extrajudicial execution * Extraordinary rendition * Fatwa on Terrorism * Global Initiative to Combat Nuclear Terrorism * Informant *International counter-terrorism operations of Russia Russian government has been involved in many counter-terrorism operations abroad, in cooperation with other nations.
Delhi security summit
The Delhi summit on security took place on February 14, 2007 with the foreign ministers of China, India ...
* Irregular warfare
Irregular warfare (IW) is defined in United States joint doctrine as "a violent struggle among state and non-state actors for legitimacy and influence over the relevant populations." Concepts associated with irregular warfare are older than the te ...
* Manhunt (law enforcement)
* Manhunt (military)
* Preventive State
* Security increase
* Sociology of terrorism
* Special Activities Division, Central Intelligence Agency
* Targeted killing
* Terrorism Research Center
* War amongst the people
References
Further reading
* Ariel Merari, "Terrorism as a Strategy in Insurgency," ''Terrorism and Political Violence'', Vol. 5, No. 4 (Winter 1993), pp. 213–251. * Edwin Bakker, Tinka Veldhuis''A Fear Management Approach to Counter-Terrorism'' (International Centre for Counter-Terrorism – The Hague, 2012)
* J.M. Berger
''Making CVE Work: A Focused Approach Based on Process Disruption''
(International Centre for Counter-Terrorism – The Hague, May 2016 * Janos Besenyo
Low-cost attacks, unnoticeable plots?
Overview on the economical character of current terrorism, Strategic Impact (ROMANIA) (ISSN: 1841–5784) (eISSN: 1824–9904) 62/2017: (Issue No. 1) pp. 83–100. * Deflem, Mathieu. 2020
In The Handbook of Collective Violence: Current Developments and Understanding, eds. C.A. Ireland, et al. Abingdon, UK: Routledge. * Deflem, Mathieu, and Stephen Chicoine. 2019
In The Handbook of Social Control, edited by Mathieu Deflem. Hoboken, NJ: Wiley-Blackwell. * Deflem, Mathieu and Shannon McDonough. 2015
Society 52(1):70–79. * Gagliano Giuseppe, ''Agitazione sovversiva, guerra psicologica e terrorismo'' (2010) , Uniservice Books. * Ishmael Jones, ''The Human Factor: Inside the CIA's Dysfunctional Intelligence Culture'' (2008, revised 2010) , Encounter Books. * Ivan Arreguín-Toft, "Tunnel at the End of the Light: A Critique of U.S. Counter-terrorist Grand Strategy," ''Cambridge Review of International Affairs'', Vol. 15, No. 3 (2002), pp. 549–563. * Ivan Arreguín-Toft, "How to Lose a War on Terror: A Comparative Analysis of a Counterinsurgency Success and Failure," in Jan Ångström and Isabelle Duyvesteyn, Eds., ''Understanding Victory and Defeat in Contemporary War'' (London: Frank Cass, 2007). * James Mitchell, "Identifying Potential Terrorist Targets" a study in the use of convergence. G2 Whitepaper on terrorism, copyright 2006, G2. Counterterrorism Conference, June 2006, Washington D.C. *
James F. Pastor
James F. Pastor is an expert in terrorism, security, public safety and police matters.
Dr. Pastor's educational and instructional experience included: Associate Professor of Public Safety at Calumet College of St. Joseph, an adjunct instructor ...
, "Terrorism and Public Safety Policing:Implications for the Obama Presidency" (2009, , Taylor & Francis).
* Jessica Dorsey, Christophe Paulussen''Boundaries of the Battlefield: A Critical Look at the Legal Paradigms and Rules in Countering Terrorism'' (International Centre for Counter-Terrorism – The Hague, 2013)
* Judy Kuriansky (Editor), "Terror in the Holy Land: Inside the Anguish of the Israeli-Palestinian Conflict" (2006, , Praeger Publishers). * Lynn Zusman (Editor),
The Law of Counterterrorism
(2012, , American Bar Association).* Marc Sageman, ''Understanding Terror Networks'' (Philadelphia, PA: University of Pennsylvania Press, 2004), . * Newton Lee, ''Counterterrorism and Cybersecurity: Total Information Awareness (Second Edition)'' (Switzerland: Springer International Publishing, 2015), . * Teemu Sinkkonen, ''Political Responses to Terrorism'' (Acta Universitatis Tamperensis, 2009), . * Vandana Asthana,
Cross-Border Terrorism in India: Counterterrorism Strategies and Challenges
" ''ACDIS Occasional Paper'' (June 2010), Program in Arms Control, Disarmament, and International Security (ACDIS), University of Illinois
External links
U.S. Bureau of Counterterrorism
{{Authority control Law enforcement Security National security Public safety