Bombe (other) on:
[Wikipedia]
[Google]
[Amazon]
 The bombe () was an
The bombe () was an

 The Enigma is an
The Enigma is an 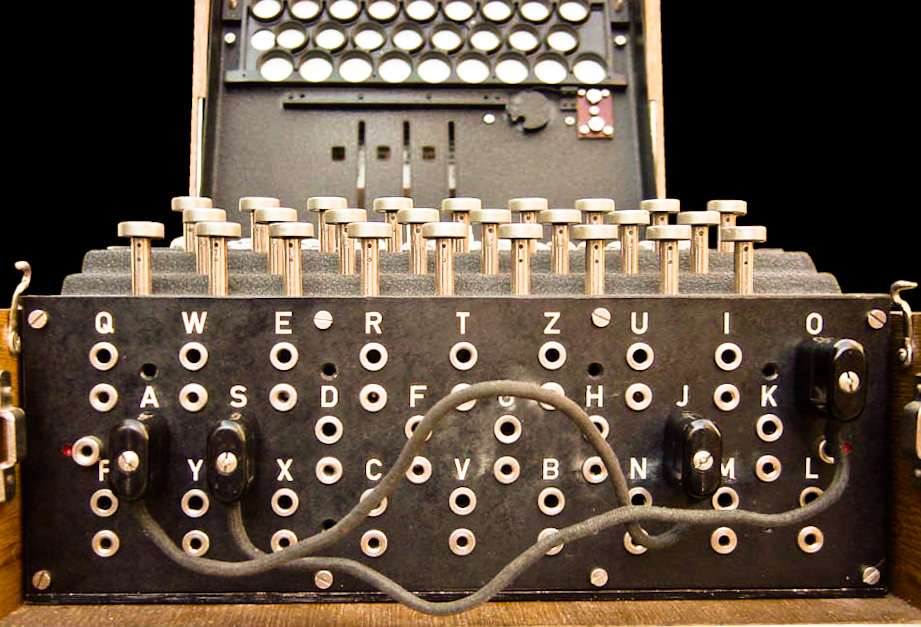 Although 105,456 is a large number, it does not guarantee security. A brute-force attack is possible: one could imagine using 100 code clerks who each tried to decode a message using 1000 distinct rotor settings. The Poles developed card catalogs so they could easily find rotor positions; Britain built "
Although 105,456 is a large number, it does not guarantee security. A brute-force attack is possible: one could imagine using 100 code clerks who each tried to decode a message using 1000 distinct rotor settings. The Poles developed card catalogs so they could easily find rotor positions; Britain built "

 The following settings of the Enigma machine must be discovered to decipher German military Enigma messages. Once these are known, all the messages for that network for that day (or pair of days in the case of the German navy) could be decrypted.
Internal settings (that required the lid of the Enigma machine to be opened)
* The selection of rotors in use in the Enigma's scrambler, and their positions on the spindle (''Walzenlage'' or "wheel order"). Possible wheel orders numbered 60 (three rotors from a choice of five) for army and air force networks and 336 (three rotors from a choice of eight) for the naval networks.
* The positions of the alphabet rings' turnover notch in relation to the core of each rotor in use (''Ringstellung'' or "ring settings"). There are 26 possible ring settings for each rotor.
External settings (that could be changed without opening the Enigma machine)
* The plugboard connections (''Steckerverbindungen'' or "stecker values"). The ten leads could be arranged in different combinations (approximately 151 trillion).
* The scrambler rotor positions at the start of enciphering the message key (the ''Grundstellung'' or "indicator-setting") — up to May 1940; or thereafter the initial positions of each rotor at the start of enciphering the message (the "message key") from which the indicator-setting could be derived. There are possible three-letter keys.
The bombe identified possible initial positions of the rotor cores and the ''stecker partner'' of a specified letter for a set of wheel orders. Manual techniques were then used to complete the decryption process. In the words of
The following settings of the Enigma machine must be discovered to decipher German military Enigma messages. Once these are known, all the messages for that network for that day (or pair of days in the case of the German navy) could be decrypted.
Internal settings (that required the lid of the Enigma machine to be opened)
* The selection of rotors in use in the Enigma's scrambler, and their positions on the spindle (''Walzenlage'' or "wheel order"). Possible wheel orders numbered 60 (three rotors from a choice of five) for army and air force networks and 336 (three rotors from a choice of eight) for the naval networks.
* The positions of the alphabet rings' turnover notch in relation to the core of each rotor in use (''Ringstellung'' or "ring settings"). There are 26 possible ring settings for each rotor.
External settings (that could be changed without opening the Enigma machine)
* The plugboard connections (''Steckerverbindungen'' or "stecker values"). The ten leads could be arranged in different combinations (approximately 151 trillion).
* The scrambler rotor positions at the start of enciphering the message key (the ''Grundstellung'' or "indicator-setting") — up to May 1940; or thereafter the initial positions of each rotor at the start of enciphering the message (the "message key") from which the indicator-setting could be derived. There are possible three-letter keys.
The bombe identified possible initial positions of the rotor cores and the ''stecker partner'' of a specified letter for a set of wheel orders. Manual techniques were then used to complete the decryption process. In the words of

 The bombe was an electro-mechanical device that replicated the action of several Enigma machines wired together. A standard German Enigma employed, at any one time, a set of three rotors, each of which could be set in any of 26 positions. The standard British bombe contained 36 Enigma equivalents, each with three drums wired to produce the same scrambling effect as the Enigma rotors. A bombe could run two or three jobs simultaneously.
Each job would have a '
The bombe was an electro-mechanical device that replicated the action of several Enigma machines wired together. A standard German Enigma employed, at any one time, a set of three rotors, each of which could be set in any of 26 positions. The standard British bombe contained 36 Enigma equivalents, each with three drums wired to produce the same scrambling effect as the Enigma rotors. A bombe could run two or three jobs simultaneously.
Each job would have a '
 A bombe run involved a cryptanalyst first obtaining a '' crib'' — a section of
A bombe run involved a cryptanalyst first obtaining a '' crib'' — a section of
 The German military Enigma included a plugboard (''Steckerbrett'' in German) which swapped letters (indicated here by ) before and after the main scrambler's change (indicated by ). The plugboard connections were known to the cryptanalysts as Stecker values. If there had been no plugboard, it would have been relatively straightforward to test a rotor setting; a Typex machine modified to replicate Enigma could be set up and the crib letter encrypted on it, and compared with the ciphertext, . If they matched, the next letter would be tried, checking that encrypted to and so on for the entire length of the crib. If at any point the letters failed to match, the initial rotor setting would be rejected; most incorrect settings would be ruled out after testing just two letters. This test could be readily mechanised and applied to all settings of the rotors.
However, with the plugboard, it was much harder to perform trial encryptions because it was unknown what the crib and ciphertext letters were transformed to by the plugboard. For example, in the first position, and were unknown because the plugboard settings were unknown.
Turing's solution to working out the stecker values (plugboard connections) was to note that, even though the values for, say, or , were unknown, the crib still provided known relationships amongst these values; that is, the values after the plugboard transformation. Using these relationships, a cryptanalyst could reason from one to another and, potentially, derive a logical contradiction, in which case the rotor setting under consideration could be ruled out.
A worked example of such reasoning might go as follows: a cryptanalyst might suppose that . Looking at position 10 of the crib:ciphertext comparison, we observe that encrypts to , or, expressed as a formula:
: =
Due to the function being its own inverse, we can apply it to both sides of the equation and obtain the following:
:
This gives us a relationship between and . If = , and for the rotor setting under consideration = (say), we can deduce that
: = =
While the crib does not allow us to determine what the values after the plugboard are, it does provide a constraint between them. In this case, it shows how is completely determined if is known.
Likewise, we can also observe that encrypts to at position 8. Using , we can deduce the steckered value for as well using a similar argument, to get, say,
: = =
Similarly, in position 6, encrypts to . As the Enigma machine is self-reciprocal, this means that at the same position would also encrypt to . Knowing this, we can apply the argument once more to deduce a value for , which might be:
: =
And again, the same sort of reasoning applies at position 7 to get:
: =
However, in this case, we have derived a
The German military Enigma included a plugboard (''Steckerbrett'' in German) which swapped letters (indicated here by ) before and after the main scrambler's change (indicated by ). The plugboard connections were known to the cryptanalysts as Stecker values. If there had been no plugboard, it would have been relatively straightforward to test a rotor setting; a Typex machine modified to replicate Enigma could be set up and the crib letter encrypted on it, and compared with the ciphertext, . If they matched, the next letter would be tried, checking that encrypted to and so on for the entire length of the crib. If at any point the letters failed to match, the initial rotor setting would be rejected; most incorrect settings would be ruled out after testing just two letters. This test could be readily mechanised and applied to all settings of the rotors.
However, with the plugboard, it was much harder to perform trial encryptions because it was unknown what the crib and ciphertext letters were transformed to by the plugboard. For example, in the first position, and were unknown because the plugboard settings were unknown.
Turing's solution to working out the stecker values (plugboard connections) was to note that, even though the values for, say, or , were unknown, the crib still provided known relationships amongst these values; that is, the values after the plugboard transformation. Using these relationships, a cryptanalyst could reason from one to another and, potentially, derive a logical contradiction, in which case the rotor setting under consideration could be ruled out.
A worked example of such reasoning might go as follows: a cryptanalyst might suppose that . Looking at position 10 of the crib:ciphertext comparison, we observe that encrypts to , or, expressed as a formula:
: =
Due to the function being its own inverse, we can apply it to both sides of the equation and obtain the following:
:
This gives us a relationship between and . If = , and for the rotor setting under consideration = (say), we can deduce that
: = =
While the crib does not allow us to determine what the values after the plugboard are, it does provide a constraint between them. In this case, it shows how is completely determined if is known.
Likewise, we can also observe that encrypts to at position 8. Using , we can deduce the steckered value for as well using a similar argument, to get, say,
: = =
Similarly, in position 6, encrypts to . As the Enigma machine is self-reciprocal, this means that at the same position would also encrypt to . Knowing this, we can apply the argument once more to deduce a value for , which might be:
: =
And again, the same sort of reasoning applies at position 7 to get:
: =
However, in this case, we have derived a
 A £100,000 budget for the construction of Turing's machine was acquired and the contract to build the bombes was awarded to the
A £100,000 budget for the construction of Turing's machine was acquired and the contract to build the bombes was awarded to the
 Commander
Commander
Virtual Bombe - Online 3D simulation of a Turing-Welchman Bombe
Turing Bombe and US Navy Bombe simulator
A bombe simulator (in Javascript)
Museum of Learning - Bombe: The Challenge Of The Four Rotor Enigma Machine
by N. Shaylor, 17 April 1997. Includes a simulator (a
Dayton Codebreakers
— documentary on the US Navy's Bombe; information on Desch, personnel of the US Naval Computing Machine Laboratory.
A simulator for both Turing and US Navy Bombes
Breaking German Navy Ciphers - The U534 Enigma M4 messages: Cracked with a Turing Bombe software
at Crypto Museum. 1930s computers Computer-related introductions in 1939 Cryptanalytic devices Electro-mechanical computers Early British computers English inventions World War II military equipment of the United Kingdom Bletchley Park Alan Turing NCR Corporation
 The bombe () was an
The bombe () was an electro-mechanical
In engineering, electromechanics combines processes and procedures drawn from electrical engineering and mechanical engineering. Electromechanics focuses on the interaction of electrical and mechanical systems as a whole and how the two systems ...
device used by British cryptologist
This is a list of cryptographers. Cryptography is the practice and study of techniques for secure communication in the presence of third parties called adversaries.
Pre twentieth century
* Al-Khalil ibn Ahmad al-Farahidi: wrote a (now lost) book ...
s to help decipher German Enigma-machine-encrypted secret messages during World War II
World War II or the Second World War, often abbreviated as WWII or WW2, was a world war that lasted from 1939 to 1945. It involved the vast majority of the world's countries—including all of the great powers—forming two opposin ...
. The US Navy
The United States Navy (USN) is the maritime service branch of the United States Armed Forces and one of the eight uniformed services of the United States. It is the largest and most powerful navy in the world, with the estimated tonnage of ...
and US Army
The United States Army (USA) is the land service branch of the United States Armed Forces. It is one of the eight U.S. uniformed services, and is designated as the Army of the United States in the U.S. Constitution.Article II, section 2, cla ...
later produced their own machines to the same functional specification, albeit engineered differently both from each other and from Polish and British bombes.
The British bombe was developed from a device known as the " bomba" ( pl, bomba kryptologiczna), which had been designed in Poland at the Biuro Szyfrów
The Cipher Bureau, in Polish: ''Biuro Szyfrów'' (), was the interwar Polish General Staff's Second Department's unit charged with SIGINT and both cryptography (the ''use'' of ciphers and codes) and cryptanalysis (the ''study'' of ciphers and ...
(Cipher Bureau) by cryptologist Marian Rejewski
Marian Adam Rejewski (; 16 August 1905 – 13 February 1980) was a Polish mathematician and cryptologist who in late 1932 reconstructed the sight-unseen German military Enigma cipher machine, aided by limited documents obtained by French mili ...
, who had been breaking German Enigma
Enigma may refer to:
*Riddle, someone or something that is mysterious or puzzling
Biology
*ENIGMA, a class of gene in the LIM domain
Computing and technology
*Enigma (company), a New York-based data-technology startup
* Enigma machine, a family o ...
messages for the previous seven years, using it and earlier machines. The initial design of the British bombe was produced in 1939 at the UK Government Code and Cypher School
Government Communications Headquarters, commonly known as GCHQ, is an intelligence and security organisation responsible for providing signals intelligence (SIGINT) and information assurance (IA) to the government and armed forces of the Unit ...
(GC&CS) at Bletchley Park
Bletchley Park is an English country house and estate in Bletchley, Milton Keynes ( Buckinghamshire) that became the principal centre of Allied code-breaking during the Second World War. The mansion was constructed during the years following ...
by Alan Turing
Alan Mathison Turing (; 23 June 1912 – 7 June 1954) was an English mathematician, computer scientist, logician, cryptanalyst, philosopher, and theoretical biologist. Turing was highly influential in the development of theoretical com ...
, with an important refinement devised in 1940 by Gordon Welchman
William Gordon Welchman (15 June 1906 – 8 October 1985) was a British mathematician. During World War II, he worked at Britain's secret codebreaking centre, "Station X" at Bletchley Park, where he was one of the most important contributors. A ...
. The engineering design and construction was the work of Harold Keen
Harold Hall "Doc" Keen (1894–1973) was a British engineer who produced the engineering design, and oversaw the construction of, the British bombe, a codebreaking machine used in World War II to read German messages sent using the Enigma machi ...
of the British Tabulating Machine Company
__NOTOC__
The British Tabulating Machine Company (BTM) was a firm which manufactured and sold Hollerith unit record equipment and other data-processing equipment. During World War II, BTM constructed some 200 "bombes", machines used at Bletchley P ...
. The first bombe, code-named ''Victory'', was installed in March 1940 while the second version, ''Agnus Dei'' or ''Agnes'', incorporating Welchman's new design, was working by August 1940.
The bombe was designed to discover some of the daily settings of the Enigma machines on the various German military networks
Network, networking and networked may refer to:
Science and technology
* Network theory, the study of graphs as a representation of relations between discrete objects
* Network science, an academic field that studies complex networks
Mathematics
...
: specifically, the set of rotors in use and their positions in the machine; the rotor core start positions for the message—the message key
Key or The Key may refer to:
Common meanings
* Key (cryptography), a piece of information that controls the operation of a cryptography algorithm
* Key (lock), device used to control access to places or facilities restricted by a lock
* Key (map ...
—and one of the wirings of the plugboard
A plugboard or control panel (the term used depends on the application area) is an array of jacks or sockets (often called hubs) into which patch cords can be inserted to complete an electrical circuit. Control panels are sometimes used to di ...
.
The Enigma machine

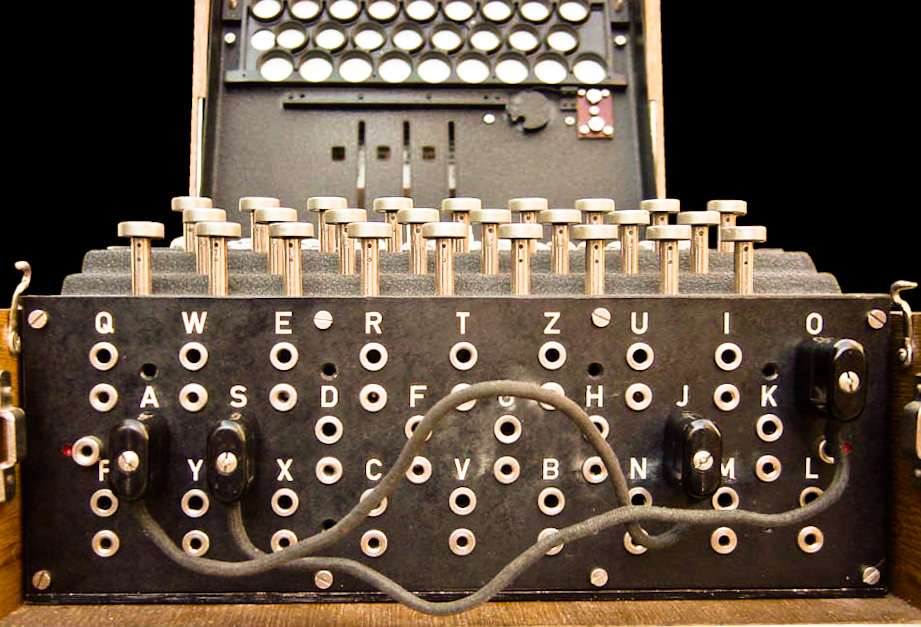
 The Enigma is an
The Enigma is an electro-mechanical
In engineering, electromechanics combines processes and procedures drawn from electrical engineering and mechanical engineering. Electromechanics focuses on the interaction of electrical and mechanical systems as a whole and how the two systems ...
rotor machine
In cryptography, a rotor machine is an electro-mechanical stream cipher device used for encrypting and decrypting messages. Rotor machines were the cryptographic state-of-the-art for much of the 20th century; they were in widespread use in the 19 ...
used for the encryption
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can decip ...
and decryption of secret messages. It was developed in Germany in the 1920s. The repeated changes of the electrical pathway from the keyboard to the lampboard implement a polyalphabetic substitution
A polyalphabetic cipher substitution, using multiple substitution alphabets. The Vigenère cipher is probably the best-known example of a polyalphabetic cipher, though it is a simplified special case. The Enigma machine is more complex but is sti ...
cipher, which turns plaintext
In cryptography, plaintext usually means unencrypted information pending input into cryptographic algorithms, usually encryption algorithms. This usually refers to data that is transmitted or stored unencrypted.
Overview
With the advent of comp ...
into ciphertext
In cryptography, ciphertext or cyphertext is the result of encryption performed on plaintext using an algorithm, called a cipher. Ciphertext is also known as encrypted or encoded information because it contains a form of the original plaintext ...
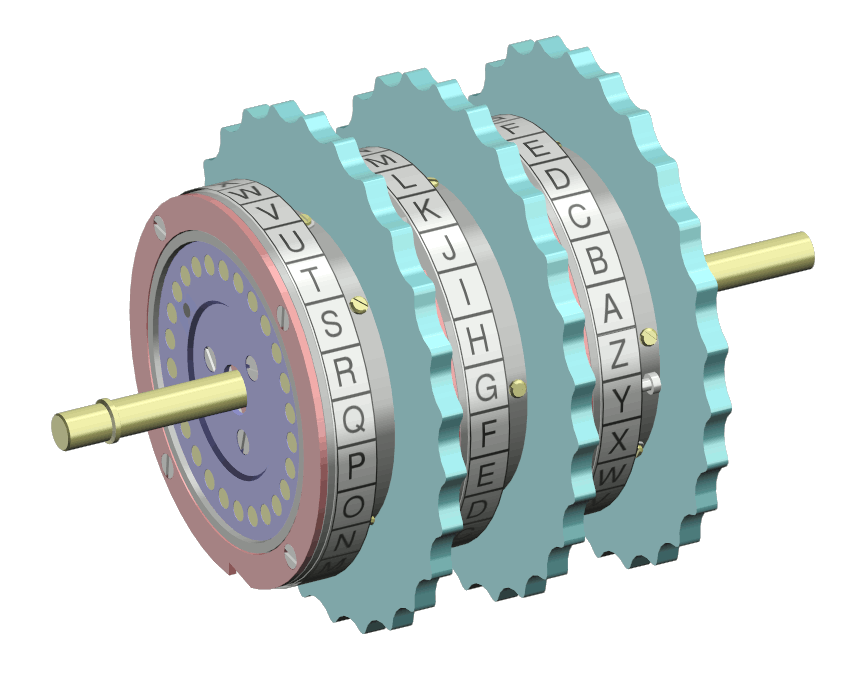
and back again. The Enigma's scrambler contains rotors with 26 electrical contacts on each side, whose wiring diverts the current to a different position on the two sides. When a key is pressed on the keyboard, an electric current flows through an entry drum at the right-hand end of the scrambler, then through the set of rotors to a reflecting drum (or reflector) which turns it back through the rotors and entry drum, and out to illuminate one of the lamps on the lampboard.
At each key depression, the right-hand or "fast" rotor advances one position, which causes the encipherment to change. In addition, once per rotation, the right-hand rotor causes the middle rotor to advance; the middle rotor similarly causes the left-hand (or "slow") rotor to advance. Each rotor's position is indicated by a letter of the alphabet showing through a window. The Enigma operator rotates the wheels by hand to set the start position for enciphering or deciphering a message. The three-letter sequence indicating the start position of the rotors is the "message key". There are 263 17,576 different message keys and different positions of the set of three rotors. By opening the lid of the machine and releasing a compression bar, the set of three rotors on their spindle can be removed from the machine and their sequence (called the "wheel order" at Bletchley Park) altered. Multiplying 17,576 by the six possible wheel orders gives 105,456 different ways that the scrambler can be set up.
 Although 105,456 is a large number, it does not guarantee security. A brute-force attack is possible: one could imagine using 100 code clerks who each tried to decode a message using 1000 distinct rotor settings. The Poles developed card catalogs so they could easily find rotor positions; Britain built "
Although 105,456 is a large number, it does not guarantee security. A brute-force attack is possible: one could imagine using 100 code clerks who each tried to decode a message using 1000 distinct rotor settings. The Poles developed card catalogs so they could easily find rotor positions; Britain built "''EINS''" (the German word for one) catalogs. Less intensive methods were also possible. If all message traffic for a day used the same rotor starting position, then frequency analysis for each position could recover the polyalphabetic substitutions. If different rotor starting positions were used, then overlapping portions of a message could be found using the index of coincidence
In cryptography, coincidence counting is the technique (invented by William F. Friedman) of putting two texts side-by-side and counting the number of times that identical letters appear in the same position in both texts. This count, either as a r ...
. Many major powers (including the Germans) could break Enigma traffic if they knew the rotor wiring. The German military knew the Enigma was weak.
In 1930, the German army introduced an additional security feature, a plugboard (''Steckerbrett'' in German; each plug is a ''Stecker'', and the British cryptologists also used the word) that further scrambled the letters, both before and after they passed through the rotor-reflector system. The Enigma encryption is a self-inverse function, meaning that it substitutes letters reciprocally: if A is transformed into R, then R is transformed into A. The plugboard transformation maintained the self-inverse quality, but the plugboard wiring, unlike the rotor positions, does not change during the encryption. This regularity was exploited by Welchman's "diagonal board" enhancement to the bombe, which vastly increased its efficiency. With six plug leads in use (leaving 14 letters "unsteckered"), there were 100,391,791,500 possible ways of setting up the plugboard.
An important feature of the machine from a cryptanalyst's point of view, and indeed Enigma's Achilles' heel
An Achilles' heel (or Achilles heel) is a weakness in spite of overall strength, which can lead to downfall. While the mythological origin refers to a physical vulnerability, idiomatic references to other attributes or qualities that can lead to ...
, was that the reflector in the scrambler prevented a letter from being enciphered as itself. Any putative solution that gave, for any location, the same letter in the proposed plaintext and the ciphertext could therefore be eliminated.
In the lead-up to World War II
World War II or the Second World War, often abbreviated as WWII or WW2, was a world war that lasted from 1939 to 1945. It involved the vast majority of the world's countries—including all of the great powers—forming two opposin ...
, the Germans made successive improvements to their military Enigma machines. By January 1939, additional rotors had been introduced so that three rotors were chosen from a set of five (hence there were now 60 possible wheel orders) for the army and air force Enigmas, and three out of eight (making 336 possible wheel orders) for the navy machines. In addition, ten leads were used on the plugboard, leaving only six letters unsteckered. This meant that the air force and army Enigmas could be set up in 1.5×1019 ways. In 1941 the German navy introduced a version of Enigma with a rotatable reflector (the M4 or Four-rotor Enigma) for communicating with its U-boat
U-boats were naval submarines operated by Germany, particularly in the First and Second World Wars. Although at times they were efficient fleet weapons against enemy naval warships, they were most effectively used in an economic warfare role ...
s. This could be set up in 1.8×1020 different ways.
Four-rotor Enigma
By late 1941 a change in German Navy fortunes in theBattle of the Atlantic
The Battle of the Atlantic, the longest continuous military campaign in World War II, ran from 1939 to the defeat of Nazi Germany in 1945, covering a major part of the naval history of World War II. At its core was the Allied naval blockade ...
, combined with intelligence reports, convinced Admiral Karl Dönitz
Karl Dönitz (sometimes spelled Doenitz; ; 16 September 1891 24 December 1980) was a German admiral who briefly succeeded Adolf Hitler as head of state in May 1945, holding the position until the dissolution of the Flensburg Government follo ...
that the Allies were able to read the German Navy's coded communications, and a fourth rotor with unknown wiring was added to German Navy Enigmas used for U-boat communications, producing the ''Triton'' system, known at Bletchley Park as ''Shark''. This was coupled with a thinner reflector design to make room for the extra rotor. The Triton was designed in such a way that it remained compatible with three-rotor machines when necessary: one of the extra 'fourth' rotors, the 'beta', was designed so that when it was paired with the thin 'B' reflector, and the rotor and ring were set to 'A', the pair acted as a 'B' reflector coupled with three rotors. Fortunately for the Allies, in December 1941, before the machine went into official service, a submarine accidentally sent a message with the fourth rotor in the wrong position, and then retransmitted the message with the rotor in the correct position to emulate the three-rotor machine. In February 1942 the change in the number of rotors used became official, and the Allies' ability to read German submarines' messages ceased until a snatch from a captured U-boat revealed not only the four-rotor machine's ability to emulate a three-rotor machine, but also that the fourth rotor did not move during a message. This along with the aforementioned retransmission eventually allowed the code breakers to figure out the wiring of both the 'beta' and 'gamma' fourth rotors.
The first half of 1942 was the "Second Happy Time
The "Second Happy Time" (; officially Operation Paukenschlag ("Operation Drumbeat"), and also known among German submarine commanders as the "American Shooting Season") was a phase in the Battle of the Atlantic during which Axis submarines att ...
" for the German U-boats, with renewed success in attacking Allied shipping, as the US had just entered war unprepared for the onslaught, lacking in anti-submarine warfare (ASW) aircraft, ships, personnel, doctrine and organization. Also, the security of the new Enigma and the Germans' ability to read Allied convoy messages sent in Naval Cipher No. 3 contributed to their success. Between January and March 1942, German submarines sank 216 ships off the US east coast. In May 1942 the US began using the convoy system and requiring a blackout of coastal cities so that ships would not be silhouetted against their lights, but this yielded only slightly improved security for Allied shipping. The Allies' failure to change their cipher for three months, together with the fact that Allied messages never contained any raw Enigma decrypts (or even mentioned that they were decrypting messages), helped convince the Germans that their messages were secure. Conversely, the Allies learned that the Germans had broken the naval cipher almost immediately from Enigma decrypts, but lost many ships due to the delay in changing the cipher.
The principle of the bombe

 The following settings of the Enigma machine must be discovered to decipher German military Enigma messages. Once these are known, all the messages for that network for that day (or pair of days in the case of the German navy) could be decrypted.
Internal settings (that required the lid of the Enigma machine to be opened)
* The selection of rotors in use in the Enigma's scrambler, and their positions on the spindle (''Walzenlage'' or "wheel order"). Possible wheel orders numbered 60 (three rotors from a choice of five) for army and air force networks and 336 (three rotors from a choice of eight) for the naval networks.
* The positions of the alphabet rings' turnover notch in relation to the core of each rotor in use (''Ringstellung'' or "ring settings"). There are 26 possible ring settings for each rotor.
External settings (that could be changed without opening the Enigma machine)
* The plugboard connections (''Steckerverbindungen'' or "stecker values"). The ten leads could be arranged in different combinations (approximately 151 trillion).
* The scrambler rotor positions at the start of enciphering the message key (the ''Grundstellung'' or "indicator-setting") — up to May 1940; or thereafter the initial positions of each rotor at the start of enciphering the message (the "message key") from which the indicator-setting could be derived. There are possible three-letter keys.
The bombe identified possible initial positions of the rotor cores and the ''stecker partner'' of a specified letter for a set of wheel orders. Manual techniques were then used to complete the decryption process. In the words of
The following settings of the Enigma machine must be discovered to decipher German military Enigma messages. Once these are known, all the messages for that network for that day (or pair of days in the case of the German navy) could be decrypted.
Internal settings (that required the lid of the Enigma machine to be opened)
* The selection of rotors in use in the Enigma's scrambler, and their positions on the spindle (''Walzenlage'' or "wheel order"). Possible wheel orders numbered 60 (three rotors from a choice of five) for army and air force networks and 336 (three rotors from a choice of eight) for the naval networks.
* The positions of the alphabet rings' turnover notch in relation to the core of each rotor in use (''Ringstellung'' or "ring settings"). There are 26 possible ring settings for each rotor.
External settings (that could be changed without opening the Enigma machine)
* The plugboard connections (''Steckerverbindungen'' or "stecker values"). The ten leads could be arranged in different combinations (approximately 151 trillion).
* The scrambler rotor positions at the start of enciphering the message key (the ''Grundstellung'' or "indicator-setting") — up to May 1940; or thereafter the initial positions of each rotor at the start of enciphering the message (the "message key") from which the indicator-setting could be derived. There are possible three-letter keys.
The bombe identified possible initial positions of the rotor cores and the ''stecker partner'' of a specified letter for a set of wheel orders. Manual techniques were then used to complete the decryption process. In the words of Gordon Welchman
William Gordon Welchman (15 June 1906 – 8 October 1985) was a British mathematician. During World War II, he worked at Britain's secret codebreaking centre, "Station X" at Bletchley Park, where he was one of the most important contributors. A ...
, "... the task of the bombe was simply to reduce the assumptions of wheel order and scrambler positions that required 'further analysis' to a manageable number".
Structure

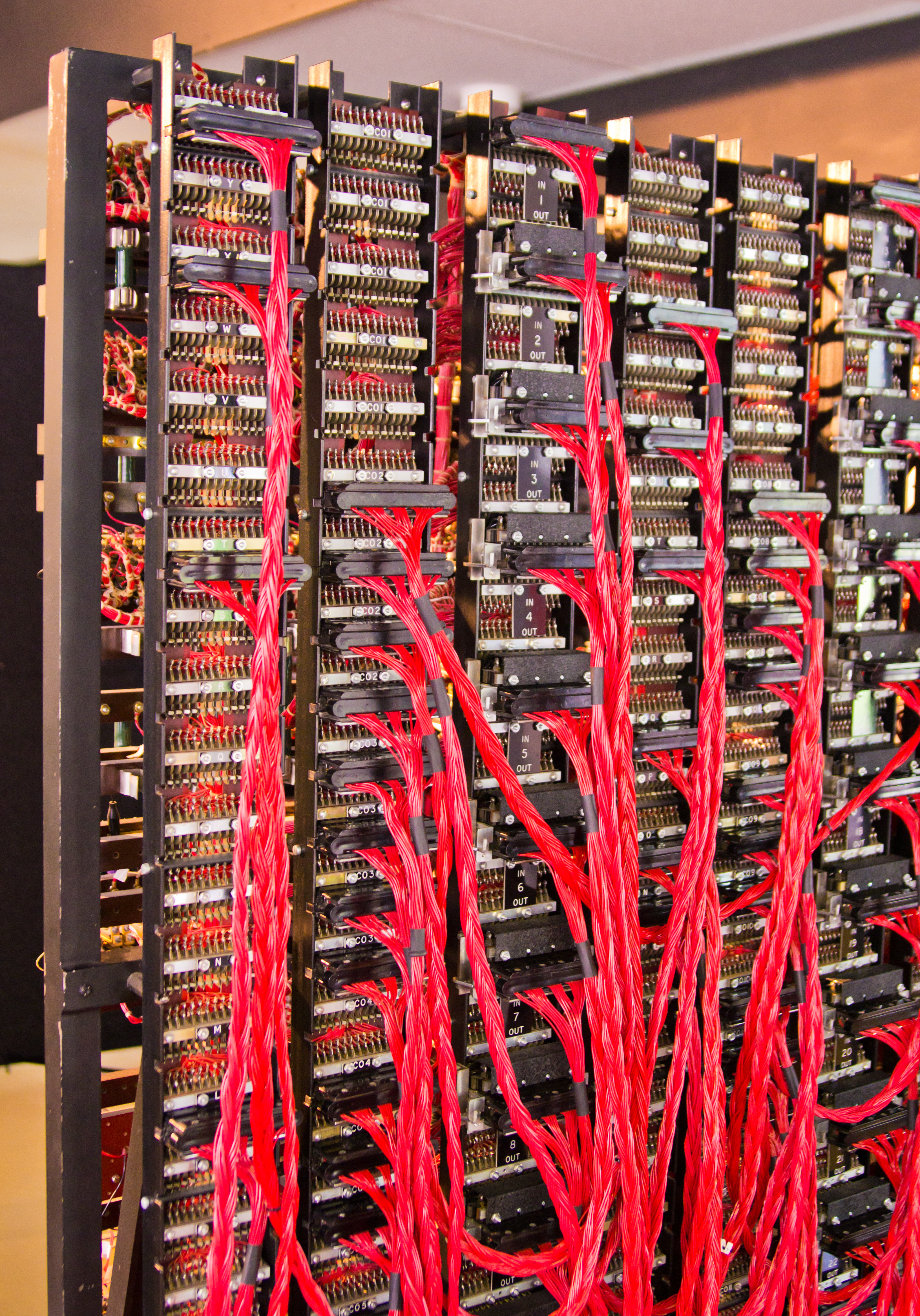
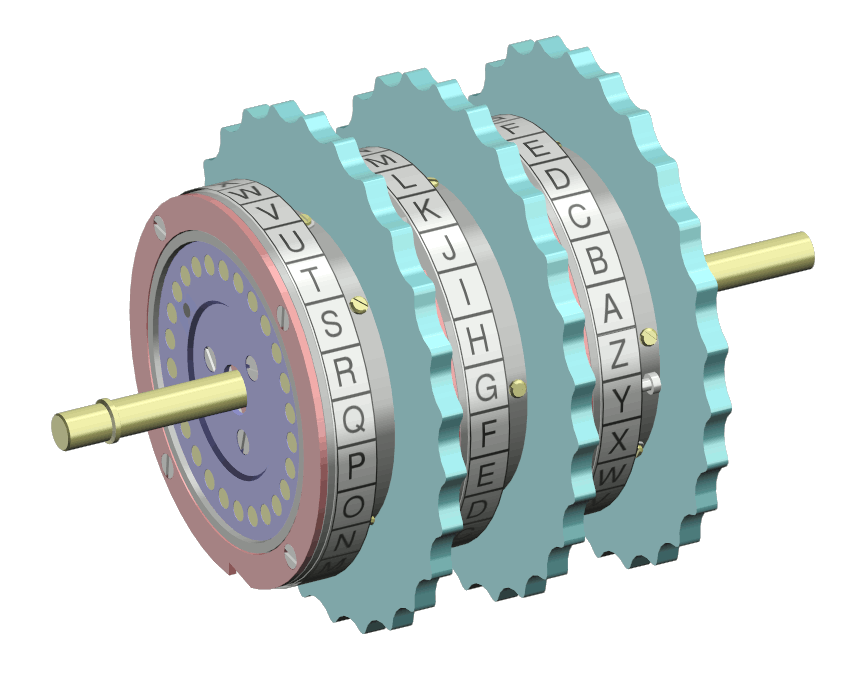
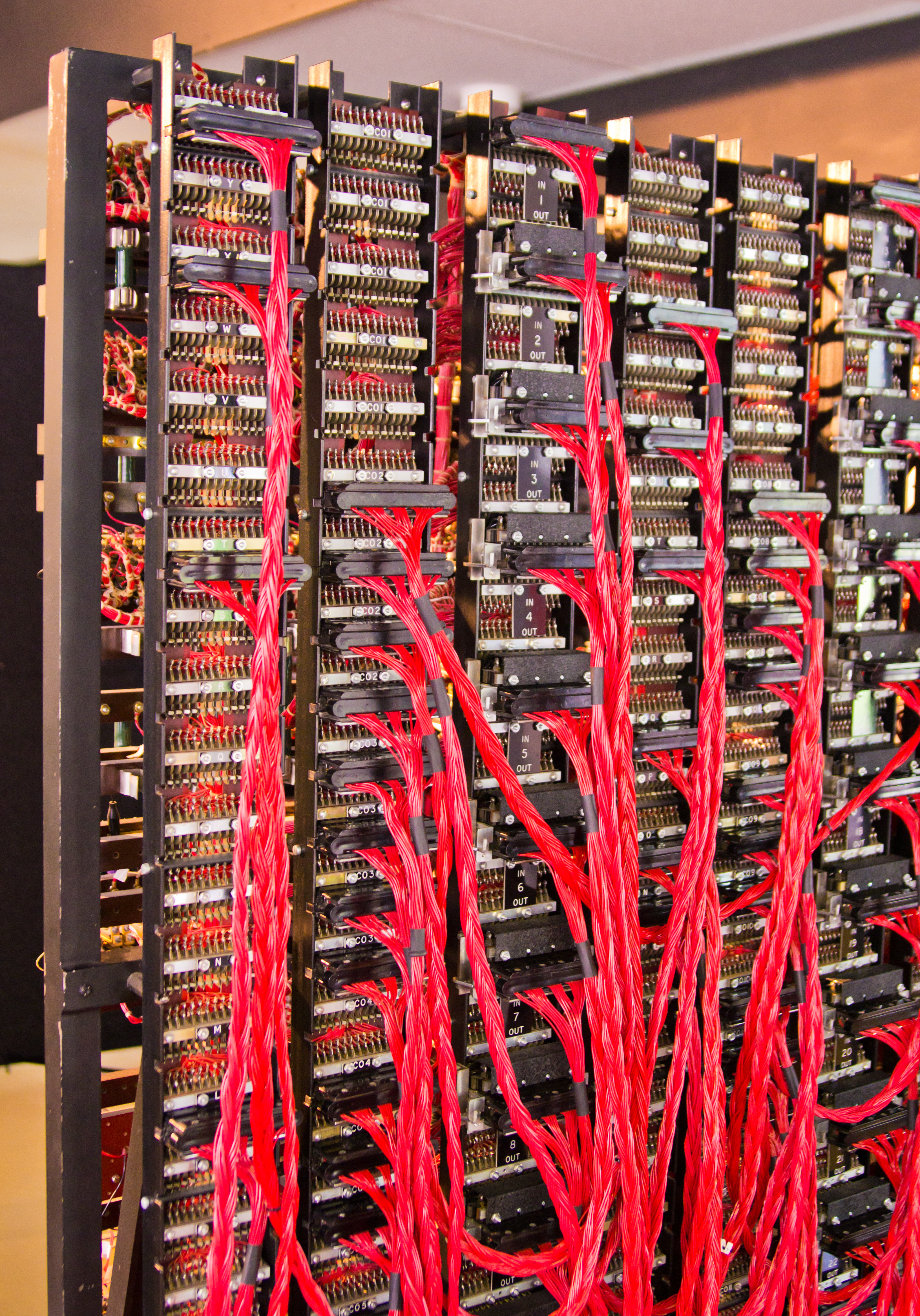
 The bombe was an electro-mechanical device that replicated the action of several Enigma machines wired together. A standard German Enigma employed, at any one time, a set of three rotors, each of which could be set in any of 26 positions. The standard British bombe contained 36 Enigma equivalents, each with three drums wired to produce the same scrambling effect as the Enigma rotors. A bombe could run two or three jobs simultaneously.
Each job would have a '
The bombe was an electro-mechanical device that replicated the action of several Enigma machines wired together. A standard German Enigma employed, at any one time, a set of three rotors, each of which could be set in any of 26 positions. The standard British bombe contained 36 Enigma equivalents, each with three drums wired to produce the same scrambling effect as the Enigma rotors. A bombe could run two or three jobs simultaneously.
Each job would have a 'menu
In a restaurant, the menu is a list of food and beverages offered to customers and the prices. A menu may be à la carte – which presents a list of options from which customers choose – or table d'hôte, in which case a pre-established seque ...
' that had to be run against a number of different wheel orders. If the menu contained 12 or fewer letters, three different wheel orders could be run on one bombe; if more than 12 letters, only two.
In order to simulate Enigma rotors, each rotor drum of the bombe had two complete sets of contacts, one for input towards the reflector and the other for output from the reflector, so that the reflected signal could pass back through a separate set of contacts. Each drum had 104 wire brushes, which made contact with the plate onto which they were loaded. The brushes and the corresponding set of contacts on the plate were arranged in four concentric circles of 26. The outer pair of circles (input and output) were equivalent to the current in an Enigma passing in one direction through the scrambler, and the inner pair equivalent to the current flowing in the opposite direction.
The interconnections within the drums between the two sets of input and output contacts were both identical to those of the relevant Enigma rotor. There was permanent wiring between the inner two sets of contacts of the three input/output plates. From there, the circuit continued to a plugboard located on the left-hand end panel, which was wired to imitate an Enigma reflector and then back through the outer pair of contacts. At each end of the "double-ended Enigma", there were sockets on the back of the machine, into which 26-way cables could be plugged.
The bombe drums were arranged with the top one of the three simulating the left-hand rotor of the Enigma scrambler, the middle one the middle rotor, and the bottom one the right-hand rotor. The top drums were all driven in synchrony by an electric motor. For each full rotation of the top drums, the middle drums were incremented by one position, and likewise for the middle and bottom drums, giving the total of 26 × 26 × 26 = positions of the 3-rotor Enigma scrambler.
The drums were colour-coded according to which Enigma rotor they emulated: I red; II maroon; III green; IV yellow; V brown; VI cobalt (blue); VII jet (black); VIII silver.
At each position of the rotors, an electric current would or would not flow in each of the 26 wires, and this would be tested in the bombe's comparator unit. For a large number of positions, the test would lead to a logical contradiction, ruling out that setting. If the test did not lead to a contradiction, the machine would stop.
The operator would then find the point at which the test passed, record the candidate solution by reading the positions of the indicator drums and the indicator unit on the Bombe's right-hand end panel. The operator then restarted the run. The candidate solutions, ''stops'' as they were called, were processed further to eliminate as many false stops as possible. Typically, there were many false bombe stops before the correct one was found.
The candidate solutions for the set of wheel orders were subject to extensive further cryptanalytical work. This progressively eliminated the false stops, built up the set of plugboard connections and established the positions of the rotor alphabet rings. Eventually, the result would be tested on a Typex machine that had been modified to replicate an Enigma, to see whether that decryption
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can decip ...
produced German language
German ( ) is a West Germanic languages, West Germanic language mainly spoken in Central Europe. It is the most widely spoken and Official language, official or co-official language in Germany, Austria, Switzerland, Liechtenstein, and the Ita ...
.
Bombe menu
plaintext
In cryptography, plaintext usually means unencrypted information pending input into cryptographic algorithms, usually encryption algorithms. This usually refers to data that is transmitted or stored unencrypted.
Overview
With the advent of comp ...
that was thought to correspond to the ciphertext
In cryptography, ciphertext or cyphertext is the result of encryption performed on plaintext using an algorithm, called a cipher. Ciphertext is also known as encrypted or encoded information because it contains a form of the original plaintext ...
. Finding cribs was not at all straightforward; it required considerable familiarity with German military jargon and the communication habits of the operators. However, the codebreakers were aided by the fact that the Enigma would never encrypt a letter to itself. This helped in testing a possible crib against the ciphertext, as it could rule out a number of cribs and positions, where the same letter occurred in the same position in both the plaintext and the ciphertext. This was termed a ''crash'' at Bletchley Park.
Once a suitable crib had been decided upon, the cryptanalyst would produce a ''menu'' for wiring up the bombe to test the crib against the ciphertext. The following is a simplified explanation of the process of constructing a menu. Suppose that the crib is ATTACKATDAWN to be tested against a certain stretch of ciphertext, say, WSNPNLKLSTCS. The letters of the crib and the ciphertext were compared to establish pairings between the ciphertext and the crib plaintext. These were then graphed as in the diagram. It should be borne in mind that the relationships are reciprocal so that A in the plaintext associated with W in the ciphertext is the same as W in the plaintext associated with A in the ciphertext. At position 1 of the plaintext-ciphertext comparison, the letter A is associated with W, but A is also associated with P at position 4, K at position 7 and T at position 10. Building up these relationships into such a diagram provided the menu from which the bombe connections and drum start positions would be set up.
In the illustration, there are three sequences of letters which form loops (or ''cycles'' or ''closures''), ATLK, TNS and TAWCN. The more loops in the menu, the more candidate rotor settings the bombe could reject, and hence the fewer false stops.
Alan Turing conducted a very substantial analysis (without any electronic aids) to estimate how many bombe stops would be expected according to the number of letters in the menu and the number of loops. Some of his results are given in the following table. Recent bombe simulations have shown similar results.
Stecker values
contradiction
In traditional logic, a contradiction occurs when a proposition conflicts either with itself or established fact. It is often used as a tool to detect disingenuous beliefs and bias. Illustrating a general tendency in applied logic, Aristotle's ...
, since, by hypothesis, we assumed that = at the outset. This means that the initial assumption must have been incorrect, and so that (for this rotor setting) ≠ (this type of argument is termed ''reductio ad absurdum
In logic, (Latin for "reduction to absurdity"), also known as (Latin for "argument to absurdity") or ''apagogical arguments'', is the form of argument that attempts to establish a claim by showing that the opposite scenario would lead to absu ...
'' or "proof by contradiction").
The cryptanalyst hypothesised one plugboard interconnection for the bombe to test. The other stecker values and the ring settings were worked out by hand methods.
Automated deduction
To automate these logical deductions, the bombe took the form of an electrical circuit. Current flowed around the circuit near-instantaneously, and represented all the possible logical deductions which could be made at that position. To form this circuit, the bombe used several sets of Enigma rotor stacks wired up together according to the instructions given on a menu, derived from a crib. Because each Enigma machine had 26 inputs and outputs, the replica Enigma stacks are connected to each other using 26-way cables. In addition, each Enigma stack rotor setting is offset a number of places as determined by its position in the crib; for example, an Enigma stack corresponding to the fifth letter in the crib would be four places further on than that corresponding to the first letter.In practice
Practical bombes used several stacks of rotors spinning together to test multiple hypotheses about possible setups of the Enigma machine, such as the order of the rotors in the stack. While Turing's bombe worked in theory, it required impractically long cribs to rule out sufficiently large numbers of settings.Gordon Welchman
William Gordon Welchman (15 June 1906 – 8 October 1985) was a British mathematician. During World War II, he worked at Britain's secret codebreaking centre, "Station X" at Bletchley Park, where he was one of the most important contributors. A ...
came up with a way of using the symmetry of the Enigma stecker to increase the power of the bombe. His suggestion was an attachment called the ''diagonal board'' that further improved the bombe's effectiveness.
The British Bombe
The Polish cryptologic '' bomba'' (Polish: ''bomba kryptologiczna''; plural ''bomby'') had been useful only as long as three conditions were met. First, the form of the indicator had to include the repetition of the message key; second, the number of rotors available had to be limited to three, giving six different "wheel orders" (the three rotors and their order within the machine); and third, the number of plug-board leads had to remain relatively small so that the majority of letters were ''unsteckered''. Six machines were built, one for each possible rotor order. The ''bomby'' were delivered in November 1938, but barely a month later the Germans introduced two additional rotors for loading into the Enigma scrambler, increasing the number of wheel orders by a factor of ten. Building another 54 ''bomby'' was beyond the Poles' resources. Also, on 1 January 1939, the number of plug-board leads was increased to ten. The Poles therefore had to return to manual methods, theZygalski sheets
The method of Zygalski sheets was a cryptologic technique used by the Polish Cipher Bureau before and during World War II, and during the war also by British cryptologists at Bletchley Park, to decrypt messages enciphered on German Enigma machin ...
.
Alan Turing
Alan Mathison Turing (; 23 June 1912 – 7 June 1954) was an English mathematician, computer scientist, logician, cryptanalyst, philosopher, and theoretical biologist. Turing was highly influential in the development of theoretical com ...
designed the British bombe on a more general principle, the assumption of the presence of text, called a ''crib'', that cryptanalysts could predict was likely to be present at a defined point in the message. This technique is termed a ''known plaintext attack
The known-plaintext attack (KPA) is an attack model for cryptanalysis where the attacker has access to both the plaintext (called a crib), and its encrypted version (ciphertext). These can be used to reveal further secret information such as secre ...
'' and had been used to a limited extent by the Poles, e.g., the Germans' use of "ANX" — "AN", German for "To", followed by "X" as a spacer.
 A £100,000 budget for the construction of Turing's machine was acquired and the contract to build the bombes was awarded to the
A £100,000 budget for the construction of Turing's machine was acquired and the contract to build the bombes was awarded to the British Tabulating Machine Company
__NOTOC__
The British Tabulating Machine Company (BTM) was a firm which manufactured and sold Hollerith unit record equipment and other data-processing equipment. During World War II, BTM constructed some 200 "bombes", machines used at Bletchley P ...
(BTM) at Letchworth
Letchworth Garden City, commonly known as Letchworth, is a town in the North Hertfordshire district of Hertfordshire, England. It is noted for being the first garden city. The population at the time of the 2011 census was 33,249.
Letchworth ...
. BTM placed the project under the direction of Harold 'Doc' Keen. Each machine was about wide, tall, deep and weighed about a ton. On the front of each bombe were 108 places where drums could be mounted. The drums were in three groups of 12 triplets. Each triplet, arranged vertically, corresponded to the three rotors of an Enigma scrambler. The bombe drums' input and output contacts went to cable connectors, allowing the bombe to be wired up according to the menu. The 'fast' drum rotated at a speed of 50.4 rpm
Revolutions per minute (abbreviated rpm, RPM, rev/min, r/min, or with the notation min−1) is a unit of rotational speed or rotational frequency for rotating machines.
Standards
ISO 80000-3:2019 defines a unit of rotation as the dimensionl ...
in the first models and 120 rpm in later ones, when the time to set up and run through all 17,576 possible positions for one rotor order was about 20 minutes.
The first bombe was named "Victory". It was installed in "Hut 1" at Bletchley Park on 18 March 1940. It was based on Turing's original design and so lacked a diagonal board. On 26 April 1940, captured a German trawler (''Schiff 26'', the ''Polares'') flying a Dutch flag; included in the capture were some Enigma keys for 23 to 26 April. Bletchley retrospectively attacked some messages sent during this period using the captured material and an ingenious Bombe menu where the Enigma fast rotors were all in the same position. In May and June 1940, Bletchley succeeded in breaking six days of naval traffic, 22–27 April 1940. Those messages were the first breaks of ''Kriegsmarine
The (, ) was the navy of Germany from 1935 to 1945. It superseded the Imperial German Navy of the German Empire (1871–1918) and the inter-war (1919–1935) of the Weimar Republic. The was one of three official branches, along with the a ...
'' messages of the war, " t though this success expanded Naval Section's knowledge of the Kriegsmarines's signals organization, it neither affected naval operations nor made further naval Enigma solutions possible." The second bombe, named "''Agnus dei''", later shortened to "Agnes", or "Aggie", was equipped with Welchman's diagonal board, and was installed on 8 August 1940; "Victory" was later returned to Letchworth to have a diagonal board fitted. The bombes were later moved from "Hut 1" to "Hut 11". The bombe was referred to by Group Captain Winterbotham as a "Bronze Goddess" because of its colour. The devices were more prosaically described by operators as being "like great big metal bookcases".
During 1940, 178 messages were broken on the two machines, nearly all successfully. Because of the danger of bombes at Bletchley Park being lost if there were to be a bombing raid, bombe outstations were established, at Adstock
''For the municipality in Quebec, see Adstock, Quebec''
Adstock is a village and civil parish about northwest of Winslow and southeast of Buckingham in the Aylesbury Vale district of Buckinghamshire. The 2001 Census recorded a parish populati ...
, Gayhurst
Gayhurst is a village and civil parish in the unitary authority area of the City of Milton Keynes, Buckinghamshire, England. It is about two and a half miles NNW of Newport Pagnell.
The village name is an Old English language word meaning ...
and Wavendon
Wavendon is a village and civil parish in the south east of the Milton Keynes urban area, in Buckinghamshire, England.
History and geography
The village name is an Old English language word, and means 'Wafa's hill'. In the '' Anglo-Saxon Chron ...
, all in Buckinghamshire
Buckinghamshire (), abbreviated Bucks, is a ceremonial county in South East England that borders Greater London to the south-east, Berkshire to the south, Oxfordshire to the west, Northamptonshire to the north, Bedfordshire to the north-ea ...
. In June–August 1941 there were 4 to 6 bombes at Bletchley Park, and when Wavendon was completed, Bletchley, Adstock and Wavenden had a total of 24 to 30 bombes. When Gayhurst became operational there were a total of 40 to 46 bombes, and it was expected that the total would increase to about 70 bombes run by some 700 Wrens (Women's Royal Naval Service). But in 1942 with the introduction of the naval four-rotor Enigma, "far more than seventy bombes" would be needed. New outstations were established at Stanmore
Stanmore is part of the London Borough of Harrow in London. It is centred northwest of Charing Cross, lies on the outskirts of the London urban area and includes Stanmore Hill, one of the highest points of London, at high. The district, which ...
and Eastcote
Eastcote is a suburban area in the London Borough of Hillingdon, in northwest London.
In the Middle Ages, Eastcote was one of the three areas that made up the parish of Ruislip, under the name of Ascot. The name came from its position to the e ...
, and the Wavendon and Adstock bombes were moved to them, though the Gayhurst site was retained. The few bombes left at Bletchley Park were used for demonstration and training purposes only.
Production of bombes by BTM at Letchworth in wartime conditions was nowhere near as rapid as the Americans later achieved at NCR in Dayton, Ohio.
Sergeant Jones was given the overall responsibility for Bombe maintenance by Edward Travis
Sir Edward Wilfred Harry Travis (24 September 1888 – 23 April 1956) was a British cryptography, cryptographer and intelligence officer, becoming the operational head of Bletchley Park during World War II, and later the head of GCHQ.
Career
...
. Later Squadron Leader and not to be confused with Eric Jones Eric Jones may refer to:
*Sir Eric Malcolm Jones (1907–1986), British intelligence officer
* Eric Jones (economic historian) (born 1936), British-Australian economist and historian
* Eric Jones (footballer, born 1915) (1915–1985), English foot ...
, he was one of the original bombe maintenance engineers, and experienced in BTM techniques. Welchman said that later in the war when other people tried to maintain them, they realised how lucky they were to have him. About 15 million delicate wire brushes on the drums had to make reliable contact with the terminals on the template. There were 104 brushes per drum, 720 drums per bombe, and ultimately around 200 bombes.
After World War II, some fifty bombes were retained at RAF Eastcote
RAF Eastcote, also known over time as RAF Lime Grove, HMS ''Pembroke V'' and Outstation Eastcote, was a UK Ministry of Defence site in Eastcote, Middlesex.
The British government first used the site during the Second World War, constructing a ...
, while the rest were destroyed. The surviving bombes were put to work, possibly on Eastern bloc
The Eastern Bloc, also known as the Communist Bloc and the Soviet Bloc, was the group of socialist states of Central and Eastern Europe, East Asia, Southeast Asia, Africa, and Latin America under the influence of the Soviet Union that existed du ...
ciphers. Smith cites the official history of the bombe as saying that "some of these machines were to be stored away but others were required to run new jobs and sixteen machines were kept comparatively busy on menus." and "It is interesting to note that most of the jobs came up and the operating, checking and other times maintained were faster than the best times during the war periods."
Response to the four-rotor Enigma
A program was initiated by Bletchley Park to design much faster bombes that could decrypt the four-rotor system in a reasonable time. There were two streams of development. One, code-named Cobra, with an electronic sensing unit, was produced by Charles Wynn-Williams of theTelecommunications Research Establishment
The Telecommunications Research Establishment (TRE) was the main United Kingdom research and development organization for radio navigation, radar, infra-red detection for heat seeking missiles, and related work for the Royal Air Force (RAF) d ...
(TRE) at Malvern and Tommy Flowers
Thomas Harold Flowers MBE (22 December 1905 – 28 October 1998) was an English engineer with the British General Post Office. During World War II, Flowers designed and built Colossus, the world's first programmable electronic computer, to help ...
of the General Post Office
The General Post Office (GPO) was the state postal system and telecommunications carrier of the United Kingdom until 1969. Before the Acts of Union 1707, it was the postal system of the Kingdom of England, established by Charles II in 1660. ...
(GPO). The other, code-named Mammoth, was designed by Harold Keen
Harold Hall "Doc" Keen (1894–1973) was a British engineer who produced the engineering design, and oversaw the construction of, the British bombe, a codebreaking machine used in World War II to read German messages sent using the Enigma machi ...
at BTM, Letchworth. Initial delivery was scheduled for August or September 1942. The dual development projects created considerable tension between the two teams, both of which cast doubts on the viability of the opposing team's machine. After considerable internal rivalry and dispute, Gordon Welchman
William Gordon Welchman (15 June 1906 – 8 October 1985) was a British mathematician. During World War II, he worked at Britain's secret codebreaking centre, "Station X" at Bletchley Park, where he was one of the most important contributors. A ...
(by then, Bletchley Park's Assistant Director for mechanisation) was forced to step in to resolve the situation. Ultimately, Cobra proved unreliable and Mammoth went into full-scale production.
Unlike the situation at Bletchley Park, the United States armed services did not share a combined cryptanalytical service. Indeed, there was considerable rivalry between the US Army's facility, the Signals Intelligence Service (SIS), and that of the US Navy
The United States Navy (USN) is the maritime service branch of the United States Armed Forces and one of the eight uniformed services of the United States. It is the largest and most powerful navy in the world, with the estimated tonnage of ...
known as OP-20-G
OP-20-G or "Office of Chief Of Naval Operations (OPNAV), 20th Division of the Office of Naval Communications, G Section / Communications Security", was the U.S. Navy's signals intelligence and cryptanalysis group during World War II. Its mission ...
. Before the US joined the war, there was collaboration with Britain, albeit with a considerable amount of caution on Britain's side because of the extreme importance of Germany and her allies not learning that its codes were being broken. Despite some worthwhile collaboration amongst the cryptanalysts, their superiors took some time to achieve a trusting relationship in which both British and American bombes were used to mutual benefit.
In February 1941, Captain Abe Sinkov and Lieutenant Leo Rosen of the US Army, and US Naval Lieutenants Robert Weeks and Prescott Currier, arrived at Bletchley Park bringing, amongst other things, a replica of the 'Purple' cipher machine for the Bletchley Park's Japanese section in Hut 7
Hut 7 was a wartime section of the Government Code and Cypher School (GC&CS) at Bletchley Park tasked with the solution of Japanese naval codes such as JN4, JN11, JN40, and JN-25. The hut was headed by Hugh Foss who reported to Frank Birch, the h ...
. The four returned to America after ten weeks, with a naval radio direction finding
Direction finding (DF), or radio direction finding (RDF), isin accordance with International Telecommunication Union (ITU)defined as radio location that uses the reception of radio waves to determine the direction in which a radio station ...
unit and many documents including a 'paper Enigma'.
Currier later wrote:
The main response to the Four-rotor Enigma was the US Navy bombe, which was manufactured in much less constrained facilities than were available in wartime Britain.
US Navy Bombe
ColonelJohn Tiltman
Brigadier John Hessell Tiltman, (25 May 1894 – 10 August 1982) was a British Army officer who worked in intelligence, often at or with the Government Code and Cypher School (GC&CS) starting in the 1920s. His intelligence work was largely conn ...
, who later became Deputy Director at Bletchley Park, visited the US Navy cryptanalysis office (OP-20-G
OP-20-G or "Office of Chief Of Naval Operations (OPNAV), 20th Division of the Office of Naval Communications, G Section / Communications Security", was the U.S. Navy's signals intelligence and cryptanalysis group during World War II. Its mission ...
) in April 1942 and recognised America's vital interest in deciphering U-boat traffic. The urgent need, doubts about the British engineering workload and slow progress, prompted the US to start investigating designs for a Navy bombe, based on the full blueprint
A blueprint is a reproduction of a technical drawing or engineering drawing using a contact print process on light-sensitive sheets. Introduced by Sir John Herschel in 1842, the process allowed rapid and accurate production of an unlimited number ...
s and wiring diagrams received by US Naval Lieutenants Robert Ely and Joseph Eachus at Bletchley Park in July 1942. Funding for a full, $2 million, navy development effort was requested on 3 September 1942 and approved the following day.
 Commander
Commander Edward Travis
Sir Edward Wilfred Harry Travis (24 September 1888 – 23 April 1956) was a British cryptography, cryptographer and intelligence officer, becoming the operational head of Bletchley Park during World War II, and later the head of GCHQ.
Career
...
, Deputy Director and Frank Birch
Francis Lyall "Frank" Birch, (5 December 1889 – 14 February 1956) was a British cryptographer and actor. He was educated at Eton College and King's College, Cambridge.
During World War I, he served as a lieutenant commander with the R ...
, Head of the German Naval Section travelled from Bletchley Park to Washington in September 1942. With Carl Frederick Holden
Carl Frederick Holden (May 25, 1895May 18, 1953) was a decorated officer in the United States Navy who reached the rank of Vice Admiral. A veteran of both World Wars, he became an expert in Naval communications, graduating with Master's degree ...
, US Director of Naval Communications they established, on 2 October 1942, a UK:US accord which may have "a stronger claim than BRUSA to being the forerunner of the UKUSA Agreement
The United Kingdom – United States of America Agreement (UKUSA, ) is a multilateral agreement for cooperation in signals intelligence between Australia, Canada, New Zealand, the United Kingdom, and the United States. The alliance of intellig ...
," being the first agreement "to establish the special Sigint
Signals intelligence (SIGINT) is intelligence-gathering by interception of ''signals'', whether communications between people (communications intelligence—abbreviated to COMINT) or from electronic signals not directly used in communication ( ...
relationship between the two countries," and "it set the pattern for UKUSA, in that the United States was very much the senior partner in the alliance." It established a relationship of "full collaboration" between Bletchley Park and OP-20-G.
An all electronic solution to the problem of a fast bombe was considered, but rejected for pragmatic reasons, and a contract was let with the National Cash Register Corporation
NCR Voyix Corporation, previously known as NCR Corporation and National Cash Register, is an American software, consulting and technology company providing several professional services and electronic products. It manufactured self-service ki ...
(NCR) in Dayton, Ohio
Dayton () is the sixth-largest city in the U.S. state of Ohio and the county seat of Montgomery County. A small part of the city extends into Greene County. The 2020 U.S. census estimate put the city population at 137,644, while Greater Day ...
. This established the United States Naval Computing Machine Laboratory
The United States Naval Computing Machine Laboratory (NCML) was a highly secret design and manufacturing site for code-breaking machinery located in Building 26 of the National Cash Register (NCR) company in Dayton, Ohio and operated by the Uni ...
. Engineering development was led by NCR's Joseph Desch
Joseph Raymond Desch (23 May 1907 – August 3, 1987) was an American electrical engineer and inventor. During World War II, he was Research Director of the project to design and manufacture the US Navy version of the bombe, a cryptanalytic mac ...
.
Alan Turing
Alan Mathison Turing (; 23 June 1912 – 7 June 1954) was an English mathematician, computer scientist, logician, cryptanalyst, philosopher, and theoretical biologist. Turing was highly influential in the development of theoretical com ...
, who had written a memorandum to OP-20-G (probably in 1941), was seconded to the British Joint Staff Mission in Washington in December 1942, because of his exceptionally wide knowledge about the bombes and the methods of their use. He was asked to look at the bombes that were being built by NCR and at the security of certain speech cipher equipment under development at Bell Labs. He visited OP-20-G, and went to NCR in Dayton on 21 December. He was able to show that it was not necessary to build 336 Bombes, one for each possible rotor order, by utilising techniques such as Banburismus
Banburismus was a cryptanalytic process developed by Alan Turing at Bletchley Park in Britain during the Second World War. It was used by Bletchley Park's Hut 8 to help break German ''Kriegsmarine'' (naval) messages enciphered on Enigma machine ...
. The initial order was scaled down to 96 machines.
The US Navy bombes used drums for the Enigma rotors in much the same way as the British bombes. They had eight Enigma-equivalents on the front and eight on the back. The fast drum rotated at 1,725 rpm
Revolutions per minute (abbreviated rpm, RPM, rev/min, r/min, or with the notation min−1) is a unit of rotational speed or rotational frequency for rotating machines.
Standards
ISO 80000-3:2019 defines a unit of rotation as the dimensionl ...
, 34 times the speed of the early British bombes. 'Stops' were detected electronically using thermionic valves
A vacuum tube, electron tube, valve (British usage), or tube (North America), is a device that controls electric current flow in a high vacuum between electrodes to which an electric potential difference has been applied.
The type known as a ...
(vacuum tubes)—mostly thyratron
A thyratron is a type of gas-filled tube used as a high-power electrical switch and controlled rectifier. Thyratrons can handle much greater currents than similar hard-vacuum tubes. Electron multiplication occurs when the gas becomes ionized, pro ...
s—for the high-speed circuits. When a 'stop' was found the machine over-ran as it slowed, reversed to the position found and printed it out before restarting. The running time for a 4-rotor run was about 20 minutes, and for a 3-rotor run, about 50 seconds. Each machine was wide, high, deep and weighed 2.5 tons.
The first machine was completed and tested on 3 May 1943. By 22 June, the first two machines, called 'Adam' and 'Eve' broke a particularly difficult German naval cipher, the ''Offizier'' settings for 9 and 10 June. A P Mahon, who had joined the Naval Section in Hut 8 in 1941, reported in his official 1945 "History of Hut Eight 1939-1945":
These bombes were faster, and soon more available, than the British bombes at Bletchley Park and its outstations. Consequently, they were put to use for Hut 6 as well as Hut 8 work. In Alexander's "Cryptographic History of Work on German Naval Enigma", he wrote as follows.
Production was stopped in September 1944 after 121 bombes had been made. The last-manufactured US Navy bombe is on display at the US National Cryptologic Museum
The National Cryptologic Museum (NCM) is an American museum of cryptologic history that is affiliated with the National Security Agency (NSA). The first public museum in the U.S. Intelligence Community, NCM is located in the former Colony Sev ...
. Jack Ingram, former Curator of the museum, describes being told of the existence of a second bombe and searching for it but not finding it whole. Whether it remains in storage in pieces, waiting to be discovered, or no longer exists, is unknown.
US Army Bombe
The US Army Bombe was physically very different from the British and US Navy bombes. The contract for its creation was signed withBell Labs
Nokia Bell Labs, originally named Bell Telephone Laboratories (1925–1984),
then AT&T Bell Laboratories (1984–1996)
and Bell Labs Innovations (1996–2007),
is an American industrial research and scientific development company owned by mult ...
on 30 September 1942. The machine was designed to analyse 3-rotor, not 4-rotor traffic. It was known as "003" or "Madame X". It did not use drums to represent the Enigma rotors, using instead telephone-type relays. It could, however, handle one problem that the bombes with drums could not. The set of ten bombes consisted of a total of 144 Enigma-equivalents, each mounted on a rack approximately long high and wide. There were 12 control stations which could allocate any of the Enigma-equivalents into the desired configuration by means of plugboards. Rotor order changes did not require the mechanical process of changing drums, but was achieved in about half a minute by means of push buttons. A 3-rotor run took about 10 minutes.
Bombe rebuild
In 1994 a group led by John Harper of the BCS Computer Conservation Society started a project to build a working replica of a bombe. The project required detailed research, and took thirteen years of effort before the replica was completed, which was then put on display at the Bletchley Park museum. In March 2009 it won an Engineering Heritage Award. The Bombe rebuild was relocated toThe National Museum of Computing
The National Museum of Computing is a museum in the United Kingdom dedicated to collecting and restoring historic computer systems. The museum is based in rented premises at Bletchley Park in Milton Keynes, Buckinghamshire and opened in 2007. ...
on Bletchley Park in May 2018, the new gallery officially re-opening on 23 June 2018.
Simulators
Virtual Bombe - Online 3D simulation of a Turing-Welchman Bombe
Turing Bombe and US Navy Bombe simulator
See also
*Cryptanalysis of the Enigma
Cryptanalysis of the Enigma ciphering system enabled the western Allies in World War II to read substantial amounts of Morse-coded radio communications of the Axis powers that had been enciphered using Enigma machines. This yielded military in ...
* Colossus computer
Colossus was a set of computers developed by British codebreakers in the years 1943–1945 to help in the cryptanalysis of the Lorenz cipher. Colossus used thermionic valves (vacuum tubes) to perform Boolean and counting operations. Colossus ...
* Heath Robinson
William Heath Robinson (31 May 1872 – 13 September 1944) was an English cartoonist, illustrator and artist, best known for drawings of whimsically elaborate machines to achieve simple objectives.
In the UK, the term "Heath Robinson contr ...
* Jean Valentine (bombe operator)
Notes
References
* * * * * * * * * * * * * * * * * * * * * New updated edition of '' with an ''addendum'' consisting of a 1986 paper written by Welchman that corrects his misapprehensions in the 1982 edition. * * (also National Archives and Records Administration Record Group 457, File 35701.) * * *External links
{{Commons category, BombeA bombe simulator (in Javascript)
Museum of Learning - Bombe: The Challenge Of The Four Rotor Enigma Machine
by N. Shaylor, 17 April 1997. Includes a simulator (a
Java applet
Java applets were small applications written in the Java programming language, or another programming language that compiles to Java bytecode, and delivered to users in the form of Java bytecode. The user launched the Java applet from a ...
and C)
Dayton Codebreakers
— documentary on the US Navy's Bombe; information on Desch, personnel of the US Naval Computing Machine Laboratory.
A simulator for both Turing and US Navy Bombes
Breaking German Navy Ciphers - The U534 Enigma M4 messages: Cracked with a Turing Bombe software
at Crypto Museum. 1930s computers Computer-related introductions in 1939 Cryptanalytic devices Electro-mechanical computers Early British computers English inventions World War II military equipment of the United Kingdom Bletchley Park Alan Turing NCR Corporation