|
Trade Craft
Tradecraft, within the intelligence community, refers to the techniques, methods and technologies used in modern espionage (spying) and generally, as part of the activity of intelligence assessment. This includes general topics or techniques (dead drops, for example), or the specific techniques of a nation or organization (the particular form of encryption (encoding) used by the National Security Agency, for example). Examples * Agent handling is the management of espionage agents, principal agents, and agent networks (called "assets") by intelligence officers, who are typically known as case officers. * Analytic tradecraft is the body of specific methods for intelligence analysis. * Black bag operations are covert or clandestine entries into structures or locations to obtain information for human intelligence operations. This may require breaking and entering, lock picking, safe cracking, key impressions, fingerprinting, photography, electronic surveillance (includi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Microdot Camera Markiv
A microdot is text or an image substantially reduced in size to prevent detection by unintended recipients. Microdots are normally circular and around in diameter but can be made into different shapes and sizes and made from various materials such as polyester or metal. The name comes from the fact that the microdots have often been about the size and shape of a typographical dot, such as a period or the tittle of a lowercase ''i'' or ''j''. Microdots are, fundamentally, a steganographic approach to message protection. History In 1870 during the Franco-Prussian War, Paris was under siege and messages were sent by carrier pigeon. Parisian photographer René Dagron used microfilm to permit each pigeon to carry a high volume of messages, as pigeons can carry little weight. Improvement in technology since then has made even more miniaturization possible. At the International Congress of Photography in Paris in 1925 Emanuel Goldberg presented a method of producing extreme reducti ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Fingerprint
A fingerprint is an impression left by the friction ridges of a human finger. The recovery of partial fingerprints from a crime scene is an important method of forensic science. Moisture and grease on a finger result in fingerprints on surfaces such as glass or metal. Deliberate impressions of entire fingerprints can be obtained by ink or other substances transferred from the peaks of friction ridges on the skin to a smooth surface such as paper. Fingerprint records normally contain impressions from the pad on the last joint of fingers and thumbs, though fingerprint cards also typically record portions of lower joint areas of the fingers. Human fingerprints are detailed, nearly unique, difficult to alter, and durable over the life of an individual, making them suitable as long-term markers of human identity. They may be employed by police or other authorities to identify individuals who wish to conceal their identity, or to identify people who are incapacitated or deceased and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Communications Protocol
A communication protocol is a system of rules that allows two or more entities of a communications system to transmit information via any kind of variation of a physical quantity. The protocol defines the rules, syntax, semantics and synchronization of communication and possible error recovery methods. Protocols may be implemented by hardware, software, or a combination of both. Communicating systems use well-defined formats for exchanging various messages. Each message has an exact meaning intended to elicit a response from a range of possible responses pre-determined for that particular situation. The specified behavior is typically independent of how it is to be implemented. Communication protocols have to be agreed upon by the parties involved. To reach an agreement, a protocol may be developed into a technical standard. A programming language describes the same for computations, so there is a close analogy between protocols and programming languages: ''protocols ar ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Adversary (cryptography)
In cryptography, an adversary (rarely opponent, enemy) is a malicious entity whose aim is to prevent the users of the cryptosystem from achieving their goal (primarily privacy, integrity, and availability of data). An adversary's efforts might take the form of attempting to discover secret data, corrupting some of the data in the system, spoofing the identity of a message sender or receiver, or forcing system downtime. Actual adversaries, as opposed to idealized ones, are referred to as ''attackers''. The former term predominates in the cryptographic and the latter in the computer security literature. Eve, Mallory, Oscar and Trudy are all adversarial characters widely used in both types of texts. This notion of an adversary helps both intuitive and formal reasoning about cryptosystems by casting security analysis of cryptosystems as a 'game' between the users and a ''centrally co-ordinated'' enemy. The notion of security of a cryptosystem is meaningful only with respect to parti ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Secure Communication
Secure communication is when two entities are communicating and do not want a third party to listen in. For this to be the case, the entities need to communicate in a way that is unsusceptible to eavesdropping or interception. Secure communication includes means by which people can share information with varying degrees of certainty that third parties cannot intercept what is said. Other than spoken face-to-face communication with no possible eavesdropper, it is probably safe to say that no communication is guaranteed to be secure in this sense, although practical obstacles such as legislation, resources, technical issues (interception and encryption), and the sheer volume of communication serve to limit surveillance. With many communications taking place over long distance and mediated by technology, and increasing awareness of the importance of interception issues, technology and its compromise are at the heart of this debate. For this reason, this article focuses on communicatio ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptography
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security ( data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. Cryptography prior to the modern age was effectively synonymo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Suicide
Suicide is the act of intentionally causing one's own death. Mental disorders (including depression, bipolar disorder, schizophrenia, personality disorders, anxiety disorders), physical disorders (such as chronic fatigue syndrome), and substance abuse (including alcoholism and the use of and withdrawal from benzodiazepines) are risk factors. Some suicides are impulsive acts due to stress (such as from financial or academic difficulties), relationship problems (such as breakups or divorces), or harassment and bullying. Those who have previously attempted suicide are at a higher risk for future attempts. Effective suicide prevention efforts include limiting access to methods of suicide such as firearms, drugs, and poisons; treating mental disorders and substance abuse; careful media reporting about suicide; and improving economic conditions. Although crisis hotlines are common resources, their effectiveness has not been well studied. The most commonly adopted metho ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Security
Security is protection from, or resilience against, potential harm (or other unwanted coercive change) caused by others, by restraining the freedom of others to act. Beneficiaries (technically referents) of security may be of persons and social groups, objects and institutions, ecosystems or any other entity or phenomenon vulnerable to unwanted change. Security mostly refers to protection from hostile forces, but it has a wide range of other senses: for example, as the absence of harm (e.g. freedom from want); as the presence of an essential good (e.g. food security); as resilience against potential damage or harm (e.g. secure foundations); as secrecy (e.g. a secure telephone line); as containment (e.g. a secure room or cell); and as a state of mind (e.g. emotional security). The term is also used to refer to acts and systems whose purpose may be to provide security (security companies, security forces, security guard, cyber security systems, security cameras, remote guard ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Secrecy
Secrecy is the practice of hiding information from certain individuals or groups who do not have the "need to know", perhaps while sharing it with other individuals. That which is kept hidden is known as the secret. Secrecy is often controversial, depending on the content or nature of the secret, the group or people keeping the secret, and the motivation for secrecy. Secrecy by government entities is often decried as excessive or in promotion of poor operation; excessive revelation of information on individuals can conflict with virtues of privacy and confidentiality. It is often contrasted with Transparency (social), social transparency. Secrecy can exist in a number of different ways: encoding or encryption (where mathematical and technical strategies are used to hide messages), true secrecy (where restrictions are put upon those who take part of the message, such as through Classified information, government security classification) and obfuscation, where secrets are hidd ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
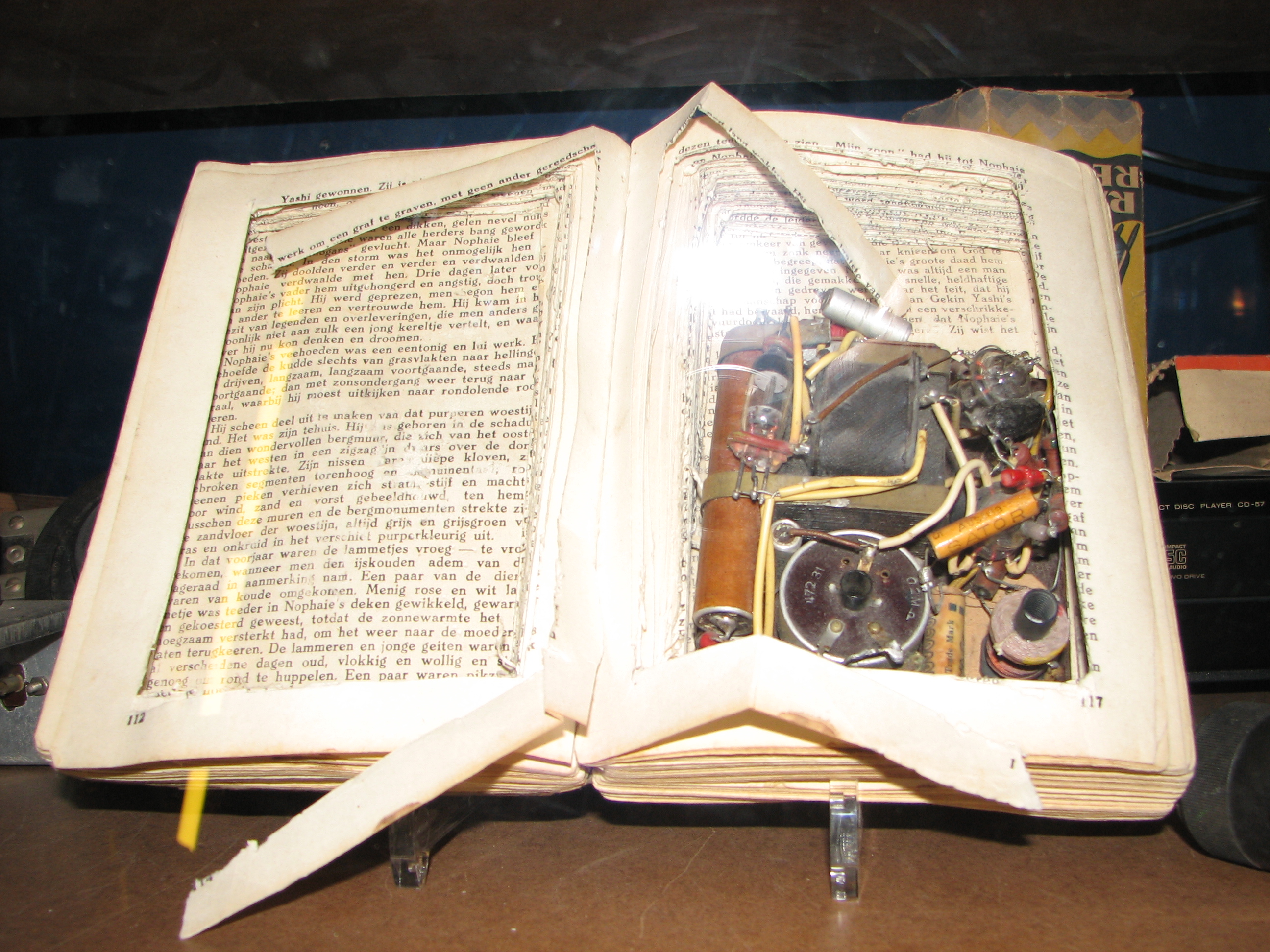
Concealment Device
Concealment devices or diversion safes are used to hide things for the purpose of secrecy or security. They are made from an ordinary household object such as a book, a soda can, a candle, a can, or something as small as a coin. The idea is that such an inconspicuous object would not be expected to contain anything of worth. Examples in espionage include dead drop spikes for transferring items to other people, and hollowed-out coins or hollowed out teeth for concealing something - such as microfilm or a suicide pill. Examples in smuggling include suitcases with false bottoms for hiding contraband. During World War II MI9 was responsible for creating many concealment devices for "escape aids" to assist prisoners of war to escape. Examples Ammunition Starting in the First World War and still continuing today, military personnel use ammunition casings to hide small amounts of critical information e.g. encryption/recognition codes or navigational grid references etc. The hiding pl ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Caltrop
A caltrop (also known as caltrap, galtrop, cheval trap, galthrap, galtrap, calthrop, jackrock or crow's foot'' Battle of Alesia'' (Caesar's conquest of Gaul in 52 BC), Battlefield Detectives program, (2006), rebroadcast: 2008-09-08 on History Channel International (13:00-14:00 hrs EDST); Note: No mention of name caltrop at all, but illustrated and given as battle key to defend Roman lines of circumvallation per recent digs evidence.) is an area denial weapon made up of two or more sharp nails or spines arranged in such a manner that one of them always points upward from a stable base (for example, a tetrahedron). Historically, caltrops were part of defences that served to slow the advance of troops, especially horses, chariots, and war elephants, and were particularly effective against the soft feet of Camel cavalry, camels. In modern times, caltrops are effective when used against wheeled vehicles with pneumatic tires. Name The modern name "caltrop" is derived from the Old Engli ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Forgery
Forgery is a white-collar crime that generally refers to the false making or material alteration of a legal instrument with the specific intent to defraud anyone (other than themself). Tampering with a certain legal instrument may be forbidden by law in some jurisdictions but such an offense is not related to forgery unless the tampered legal instrument was actually used in the course of the crime to defraud another person or entity. Copies, studio replicas, and reproductions are not considered forgeries, though they may later become forgeries through knowing and willful misrepresentations. Forging money or currency is more often called counterfeiting. But consumer goods may also be ''counterfeits'' if they are not manufactured or produced by the designated manufacturer or producer given on the label or flagged by the trademark symbol. When the object forged is a record or document it is often called a false document. This usage of "forgery" does not derive from metalwork d ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |




.jpg)