|
Stuxnet
Stuxnet is a malicious computer worm first uncovered in 2010 and thought to have been in development since at least 2005. Stuxnet targets supervisory control and data acquisition ( SCADA) systems and is believed to be responsible for causing substantial damage to the nuclear program of Iran. Although neither country has openly admitted responsibility, the worm is widely understood to be a cyberweapon built jointly by the United States and Israel in a collaborative effort known as Operation Olympic Games. The program, started during the Bush administration, was rapidly expanded within the first months of Barack Obama's presidency. Stuxnet specifically targets programmable logic controllers (PLCs), which allow the automation of electromechanical processes such as those used to control machinery and industrial processes including gas centrifuges for separating nuclear material. Exploiting four zero-day flaws, Stuxnet functions by targeting machines using the Microsoft Windows o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Equation Group
The Equation Group, classified as an advanced persistent threat, is a highly sophisticated threat actor suspected of being tied to the Tailored Access Operations (TAO) unit of the United States National Security Agency (NSA). Kaspersky Labs describes them as one of the most sophisticated cyber attack groups in the world and "the most advanced ... we have seen", operating alongside the creators of Stuxnet and Flame. Most of their targets have been in Iran, Russia, Pakistan, Afghanistan, India, Syria, and Mali. The name originated from the group's extensive use of encryption. By 2015, Kaspersky documented 500 malware infections by the group in at least 42 countries, while acknowledging that the actual number could be in the tens of thousands due to its self-terminating protocol. In 2017, WikiLeaks published a discussion held within the CIA on how it had been possible to identify the group. One commenter wrote that "the Equation Group as labeled in the report does not relate to a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Kaspersky Lab
Kaspersky Lab (; Russian: Лаборатория Касперского, tr. ''Laboratoriya Kasperskogo'') is a Russian multinational cybersecurity and anti-virus provider headquartered in Moscow, Russia, and operated by a holding company in the United Kingdom. It was founded in 1997 by Eugene Kaspersky, Natalya Kaspersky, and Alexey De-Monderik; Eugene Kaspersky is currently the CEO. Kaspersky Lab develops and sells antivirus, internet security, password management, endpoint security, and other cybersecurity products and services. Kaspersky expanded abroad from 2005 to 2010 and grew to $704 million in annual revenues by 2020, up 8% from 2016, though annual revenues were down 8% in North America due to U.S. government security concerns. As of 2016, the software has about 400 million users and has the largest market-share of cybersecurity software vendors in Europe. Kaspersky Lab ranks fourth in the global ranking of antivirus vendors by revenue. It was the first Russian company ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyberweapon
Cyberweapon is commonly defined as a malware agent employed for military, paramilitary, or intelligence objectives as part of a cyberattack. This includes computer viruses, trojans, spyware, and worms that can introduce corrupted code into existing software, causing a computer to perform actions or processes unintended by its operator. Characteristics Cyberweapon is usually sponsored or employed by a state or non-state actor, meets an objective that would otherwise require espionage or the use of force, and is employed against specific targets. A cyberweapon performs an action that would normally require a soldier or spy, and which would be considered either illegal or an act of war if performed directly by a human agent of the sponsor during peacetime. Legal issues include violating the privacy of the target and the sovereignty of its host nation. Example of such actions are surveillance, data theft and electronic or physical destruction. While a cyberweapon almost certainly resu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
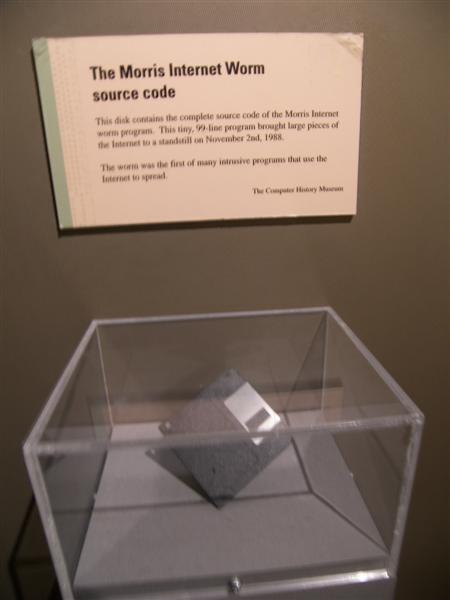
Computer Worm
A computer worm is a standalone malware computer program that replicates itself in order to spread to other computers. It often uses a computer network to spread itself, relying on security failures on the target computer to access it. It will use this machine as a host to scan and infect other computers. When these new worm-invaded computers are controlled, the worm will continue to scan and infect other computers using these computers as hosts, and this behaviour will continue. Computer worms use recursive methods to copy themselves without host programs and distribute themselves based on the law of exponential growth, thus controlling and infecting more and more computers in a short time. Worms almost always cause at least some harm to the network, even if only by consuming bandwidth, whereas viruses almost always corrupt or modify files on a targeted computer. Many worms are designed only to spread, and do not attempt to change the systems they pass through. However, as th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Operation Olympic Games
Operation Olympic Games was a covert and still unacknowledged campaign of sabotage by means of cyber disruption, directed at Iranian nuclear facilities likely by the United States and Israel. As reported, it is one of the first known uses of offensive cyber weapons. Started under the administration of George W. Bush in 2006, Olympic Games was accelerated under President Obama, who heeded Bush's advice to continue cyber attacks on the Iranian nuclear facility at Natanz. Bush believed that the strategy was the only way to prevent an Israeli conventional strike on Iranian nuclear facilities. History During Bush's second term, General James Cartwright, then head of United States Strategic Command, along with other intelligence officials presented Bush with sophisticated code that would act as an offensive cyber weapon. "The goal was to gain access to the Natanz plant's industrial computer controls ... the computer code would invade the specialized computers that command the centr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Worm
A computer worm is a standalone malware computer program that replicates itself in order to spread to other computers. It often uses a computer network to spread itself, relying on security failures on the target computer to access it. It will use this machine as a host to scan and infect other computers. When these new worm-invaded computers are controlled, the worm will continue to scan and infect other computers using these computers as hosts, and this behaviour will continue. Computer worms use recursive methods to copy themselves without host programs and distribute themselves based on the law of exponential growth, thus controlling and infecting more and more computers in a short time. Worms almost always cause at least some harm to the network, even if only by consuming bandwidth, whereas viruses almost always corrupt or modify files on a targeted computer. Many worms are designed only to spread, and do not attempt to change the systems they pass through. However, as th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SCADA
Supervisory control and data acquisition (SCADA) is a control system architecture comprising computers, networked data communications and graphical user interfaces for high-level supervision of machines and processes. It also covers sensors and other devices, such as programmable logic controllers, which interface with process plant or machinery. Explanation The operator interfaces which enable monitoring and the issuing of process commands, like controller set point changes, are handled through the SCADA computer system. The subordinated operations, e.g. the real-time control logic or controller calculations, are performed by networked modules connected to the field sensors and actuators. The SCADA concept was developed to be a universal means of remote-access to a variety of local control modules, which could be from different manufacturers and allowing access through standard automation protocols. In practice, large SCADA systems have grown to become very similar to distr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Malware
Malware (a portmanteau for ''malicious software'') is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. By contrast, software that causes harm due to some deficiency is typically described as a software bug. Malware poses serious problems to individuals and businesses on the Internet. According to Symantec's 2018 Internet Security Threat Report (ISTR), malware variants number has increased to 669,947,865 in 2017, which is twice as many malware variants as in 2016. Cybercrime, which includes malware attacks as well as other crimes committed by computer, was predicted to cost the world economy $6 trillion USD in 2021, and is increasing at a rate of 15% per year. Many types of malware exist, including computer viruses, worms, Trojan horses, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Programmable Logic Controller
A programmable logic controller (PLC) or programmable controller is an industrial computer that has been ruggedized and adapted for the control of manufacturing processes, such as assembly lines, machines, robotic devices, or any activity that requires high reliability, ease of programming, and process fault diagnosis. Dick Morley is considered as the father of PLC as he had invented the first PLC, the Modicon 084, for General Motors in 1968. PLCs can range from small modular devices with tens of inputs and outputs (I/O), in a housing integral with the processor, to large rack-mounted modular devices with thousands of I/O, and which are often networked to other PLC and SCADA systems. They can be designed for many arrangements of digital and analog I/O, extended temperature ranges, immunity to electrical noise, and resistance to vibration and impact. Programs to control machine operation are typically stored in battery-backed-up or non-volatile memory. PLCs were first devel ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Zero-day (computing)
A zero-day (also known as a 0-day) is a computer-software vulnerability previously unknown to those who should be interested in its mitigation, like the vendor of the target software. Until the vulnerability is mitigated, hackers can exploit it to adversely affect programs, data, additional computers or a network. An exploit taking advantage of a zero-day is called a zero-day exploit, or zero-day attack. The term "zero-day" originally referred to the number of days since a new piece of software was released to the public, so "zero-day software" was obtained by hacking into a developer's computer before release. Eventually the term was applied to the vulnerabilities that allowed this hacking, and to the number of days that the vendor has had to fix them. Once the vendors learn of the vulnerability, they will usually create patches or advise workarounds to mitigate it. The more recently that the vendor has become aware of the vulnerability, the more likely it is that no fix or mit ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Nuclear Program Of Iran
The nuclear program of Iran is an ongoing scientific effort by Iran to research nuclear technology that can be used to make nuclear weapons. Iran has several research sites, two uranium mines, a research reactor, and uranium processing facilities that include three known uranium enrichment plants. Iran's nuclear program was launched in the 1950s with the help of the United States under the Atoms for Peace program, and in 1970, Iran ratified the Non-Proliferation Treaty (NPT), limiting its nuclear program to peaceful use, and making its nuclear program subject to inspection by the International Atomic Energy Agency (IAEA). Western cooperation ceased following the 1979 Iranian Revolution, after which Iran continued its nuclear program on a clandestine basis. In the 2000s, the revelation of Iran's clandestine uranium enrichment program raised concerns that the program might be intended for non-peaceful uses. The IAEA launched an investigation in 2003 after an Iranian dissident gr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Gas Centrifuge
A gas centrifuge is a device that performs isotope separation of gases. A centrifuge relies on the principles of centrifugal force accelerating molecules so that particles of different masses are physically separated in a gradient along the radius of a rotating container. A prominent use of gas centrifuges is for the separation of uranium-235 (235U) from uranium-238 (238U). The gas centrifuge was developed to replace the gaseous diffusion method of uranium-235 extraction. High degrees of separation of these isotopes relies on using many individual centrifuges arranged in series, that achieve successively higher concentrations. This process yields higher concentrations of uranium-235 while using significantly less energy compared to the gaseous diffusion process. Centrifugal process The centrifuge relies on the force resulting from centrifugal acceleration to separate molecules according to their mass, and can be applied to most fluids. The dense (heavier) molecules move towards th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |