|
Stack Buffer Overflow
In software, a stack buffer overflow or stack buffer overrun occurs when a program writes to a memory address on the program's call stack outside of the intended data structure, which is usually a fixed-length buffer. Stack buffer overflow bugs are caused when a program writes more data to a buffer located on the stack than what is actually allocated for that buffer. This almost always results in corruption of adjacent data on the stack, and in cases where the overflow was triggered by mistake, will often cause the program to crash or operate incorrectly. Stack buffer overflow is a type of the more general programming malfunction known as buffer overflow (or buffer overrun). Overfilling a buffer on the stack is more likely to derail program execution than overfilling a buffer on the heap because the stack contains the return addresses for all active function calls. A stack buffer overflow can be caused deliberately as part of an attack known as . If the affected program is runni ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Memory
Computer memory stores information, such as data and programs, for immediate use in the computer. The term ''memory'' is often synonymous with the terms ''RAM,'' ''main memory,'' or ''primary storage.'' Archaic synonyms for main memory include ''core'' (for magnetic core memory) and ''store''. Main memory operates at a high speed compared to mass storage which is slower but less expensive per bit and higher in capacity. Besides storing opened programs and data being actively processed, computer memory serves as a Page cache, mass storage cache and write buffer to improve both reading and writing performance. Operating systems borrow RAM capacity for caching so long as it is not needed by running software. If needed, contents of the computer memory can be transferred to storage; a common way of doing this is through a memory management technique called ''virtual memory''. Modern computer memory is implemented as semiconductor memory, where data is stored within memory cell (com ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Superuser
In computing, the superuser is a special user account used for system administration. Depending on the operating system (OS), the actual name of this account might be root, administrator, admin or supervisor. In some cases, the actual name of the account is not the determining factor; on Unix-like systems, for example, the user with a user identifier (UID) of zero is the superuser .e., uid=0 regardless of the name of that account; and in systems which implement a r model, any user with the role of superuser (or its synonyms) can carry out all actions of the superuser account. The principle of least privilege recommends that most users and applications run under an ordinary account to perform their work, as a superuser account is capable of making unrestricted, potentially adverse, system-wide changes. Unix and Unix-like In Unix-like computer OSes (such as Linux), ''root'' is the conventional name of the user who has all rights or permissions (to all files and programs) in all mod ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Unix
Unix (, ; trademarked as UNIX) is a family of multitasking, multi-user computer operating systems that derive from the original AT&T Unix, whose development started in 1969 at the Bell Labs research center by Ken Thompson, Dennis Ritchie, and others. Initially intended for use inside the Bell System, AT&T licensed Unix to outside parties in the late 1970s, leading to a variety of both academic and commercial Unix variants from vendors including University of California, Berkeley ( BSD), Microsoft (Xenix), Sun Microsystems ( SunOS/ Solaris), HP/ HPE ( HP-UX), and IBM ( AIX). The early versions of Unix—which are retrospectively referred to as " Research Unix"—ran on computers such as the PDP-11 and VAX; Unix was commonly used on minicomputers and mainframes from the 1970s onwards. It distinguished itself from its predecessors as the first portable operating system: almost the entire operating system is written in the C programming language (in 1973), which allows U ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
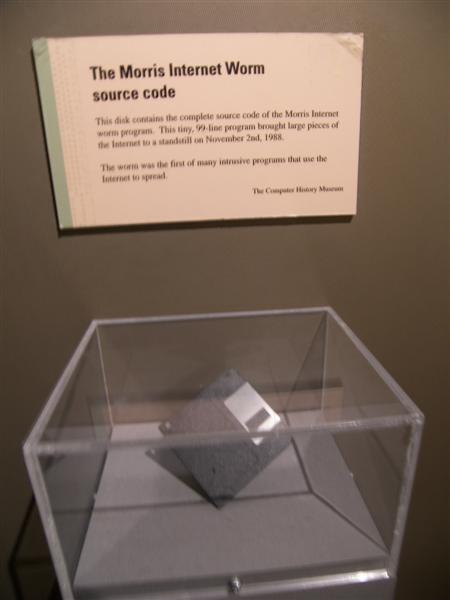
Morris Worm
The Morris worm or Internet worm of November 2, 1988, is one of the oldest computer worms distributed via the Internet, and the first to gain significant mainstream media attention. It resulted in the first felony conviction in the US under the 1986 Computer Fraud and Abuse Act. It was written by Robert Tappan Morris, a graduate student at Cornell University, and launched on 8:30 p.m. November 2, 1988, from the Massachusetts Institute of Technology network. Architecture The worm's creator, Robert Tappan Morris, is the son of cryptographer Robert Morris, who worked at the NSA. A friend of Morris said that he created the worm simply to see if it could be done, and released it from the Massachusetts Institute of Technology (MIT) in the hope of suggesting that its creator studied there, instead of Cornell. Clifford Stoll, author of '' The Cuckoo's Egg'', wrote that "Rumors have it that orrisworked with a friend or two at Harvard's computing department (Harvard student Paul ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Code Segment
In computing, a code segment, also known as a text segment or simply as text, is a portion of an object file or the corresponding section of the program's virtual address space that contains executable instructions. Segment The term "segment" comes from the memory segment, which is a historical approach to memory management that has been succeeded by paging. When a program is stored in an object file, the code segment is a part of this file; when the loader places a program into memory so that it may be executed, various memory regions are allocated (in particular, as pages), corresponding to both the segments in the object files and to segments only needed at run time. For example, the code segment of an object file is loaded into a corresponding code segment in memory. The code segment in memory is typically read-only and has a fixed size, so on embedded systems it can usually be placed in read-only memory (ROM), without the need for loading. If the code segment is not read- ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Data Execution Prevention
In computer security, executable-space protection marks memory regions as non-executable, such that an attempt to execute machine code in these regions will cause an exception. It relies on hardware features such as the NX bit (no-execute bit), or on software emulation when hardware support is unavailable. Software emulation often introduces a performance cost, or overhead (extra processing time or resources), while hardware-based NX bit implementations have no measurable performance impact. The Burroughs large systems, starting with the Burroughs 5000 introduced in 1961, implemented executable-space protection using a tagged architecture. All accesses to code and data took place through descriptors, which had memory tags preventing them from being modified; descriptors for code did not allow the code to be modified, and descriptors for data did not allow the data ta be executed as code. Today, operating systems use executable-space protection to mark writable memory areas, s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Format String Vulnerability
Uncontrolled format string is a type of code injection vulnerability discovered around 1989 that can be used in security exploits. Originally thought harmless, format string exploits can be used to crash a program or to execute harmful code. The problem stems from the use of unchecked user input as the format string parameter in certain C functions that perform formatting, such as printf(). A malicious user may use the %s and %x format tokens, among others, to print data from the call stack or possibly other locations in memory. One may also write arbitrary data to arbitrary locations using the %n format token, which commands printf() and similar functions to write the number of bytes formatted to an address stored on the stack. Details A typical exploit uses a combination of these techniques to take control of the instruction pointer (IP) of a process, for example by forcing a program to overwrite the address of a library function or the return address on the stack with a poi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Position-independent Code
In computing, position-independent code (PIC) or position-independent executable (PIE) is a body of machine code that executes properly regardless of its memory address. PIC is commonly used for shared libraries, so that the same library code can be loaded at a location in each program's address space where it does not overlap with other memory in use by, for example, other shared libraries. PIC was also used on older computer systems that lacked an MMU, so that the operating system could keep applications away from each other even within the single address space of an MMU-less system. Position-independent code can be executed at any memory address without modification. This differs from absolute code, which must be loaded at a specific location to function correctly, and load-time locatable (LTL) code, in which a linker or program loader modifies a program before execution, so it can be run only from a particular memory location. The latter terms are sometimes referred to as ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
ASLR
Address space layout randomization (ASLR) is a computer security technique involved in preventing exploitation of memory corruption vulnerabilities. In order to prevent an attacker from reliably redirecting code execution to, for example, a particular exploited function in memory, ASLR randomly arranges the address space positions of key data areas of a process, including the base of the executable and the positions of the stack, heap and libraries. When applied to the kernel, this technique is called ''kernel address space layout randomization'' (''KASLR''). History The Linux PaX project first coined the term "ASLR", and published the first design and implementation of ASLR in July 2001 as a patch for the Linux kernel. It is seen as a complete implementation, providing a patch for kernel stack randomization since October 2002. The first mainstream operating system to support ASLR by default was OpenBSD version 3.4 in 2003, followed by Linux in 2005. Benefits Address ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Return-oriented Programming
Return-oriented programming (ROP) is a computer security exploit technique that allows an attacker to execute code in the presence of security defenses such as executable-space protection and code signing. In this technique, an attacker gains control of the call stack to hijack program control flow and then executes carefully chosen machine instruction sequences that are already present in the machine's memory, called "gadgets". Each gadget typically ends in a return instruction and is located in a subroutine within the existing program and/or shared library code. Chained together, these gadgets allow an attacker to perform arbitrary operations on a machine employing defenses that thwart simpler attacks. Background Return-oriented programming is an advanced version of a stack smashing attack. Generally, these types of attacks arise when an adversary manipulates the call stack by taking advantage of a software bug, bug in the program, often a buffer overrun. In a buffer overrun ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Return-to-libc Attack
A "return-to-libc" attack is a computer security attack usually starting with a buffer overflow in which a subroutine return address on a call stack is replaced by an address of a subroutine that is already present in the process executable memory, bypassing the no-execute bit feature (if present) and ridding the attacker of the need to inject their own code. The first example of this attack in the wild was contributed by Alexander Peslyak on the Bugtraq mailing list in 1997. On POSIX-compliant operating systems the C standard library ("libc") is commonly used to provide a standard runtime environment for programs written in the C programming language. Although the attacker could make the code return anywhere, libc is the most likely target, as it is almost always linked to the program, and it provides useful calls for an attacker (such as the system function used to execute shell commands). Protection from return-to-libc attacks A non-executable stack can prevent some buffe ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Animal Sentinel
Sentinel species are organisms, often animals, used to detect risks to humans by providing advance warning of a danger. The terms primarily apply in the context of environmental hazards rather than those from other sources. Some animals can act as sentinels because they may be more susceptible or have greater exposure to a particular hazard than humans in the same environment. People have long observed animals for signs of impending hazards or evidence of environmental threats. Plants and other living organisms have also been used for these purposes. Historical examples Many observations of animals point to toxicity in food, water or air that would or could harm humans. Canaries The classic example is the " canary in the coal mine". The idea of placing a warm-blooded animal in a mine to detect carbon monoxide was first proposed by John Scott Haldane in 1895, and canaries were used as early as 1896. Countries such as Britain, the United States, and Canada used canaries a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |