|
Rubber Hose Cryptanalysis
In cryptography, rubber-hose cryptanalysis is a euphemism for the extraction of cryptographic secrets (e.g. the password to an encrypted file) from a person by coercion or torture—such as beating that person with a rubber hose, hence the name—in contrast to a mathematical or technical cryptanalytic attack. Details According to Amnesty International and the UN, many countries in the world routinely torture people. It is therefore logical to assume that at least some of those countries use (or would be willing to use) some form of rubber-hose cryptanalysis. In practice, psychological coercion can prove as effective as physical torture. Not physically violent but highly intimidating methods include such tactics as the threat of harsh legal penalties. The incentive to cooperate may be some form of plea bargain, such as an offer to drop or reduce criminal charges against a suspect in return for full co-operation with investigators. Alternatively, in some countries threats ma ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptography
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security ( data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. Cryptography prior to the modern age was effectively synonymo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptographic Protocol
A security protocol (cryptographic protocol or encryption protocol) is an abstract or concrete protocol that performs a security-related function and applies cryptographic methods, often as sequences of cryptographic primitives. A protocol describes how the algorithms should be used and includes details about data structures and representations, at which point it can be used to implement multiple, interoperable versions of a program. Cryptographic protocols are widely used for secure application-level data transport. A cryptographic protocol usually incorporates at least some of these aspects: * Key agreement or establishment * Entity authentication * Symmetric encryption and message authentication material construction * Secured application-level data transport * Non-repudiation methods * Secret sharing methods * Secure multi-party computation For example, Transport Layer Security (TLS) is a cryptographic protocol that is used to secure web (HTTPS) connections. It has an ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Espionage Techniques
Espionage, spying, or intelligence gathering is the act of obtaining secret or confidential information (intelligence) from non-disclosed sources or divulging of the same without the permission of the holder of the information for a tangible benefit. A person who commits espionage is called an ''espionage agent'' or ''spy''. Any individual or spy ring (a cooperating group of spies), in the service of a government, company, criminal organization, or independent operation, can commit espionage. The practice is clandestine, as it is by definition unwelcome. In some circumstances, it may be a legal tool of law enforcement and in others, it may be illegal and punishable by law. Espionage is often part of an institutional effort by a government or commercial concern. However, the term tends to be associated with state spying on potential or actual enemies for military purposes. Spying involving corporations is known as industrial espionage. One of the most effective ways to ga ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptographic Attacks
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security ( data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. Cryptography prior to the modern age was effectively synonymous with ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cory Doctorow
Cory Efram Doctorow (; born July 17, 1971) is a Canadian-British blogger, journalist, and science fiction author who served as co-editor of the blog '' Boing Boing''. He is an activist in favour of liberalising copyright laws and a proponent of the Creative Commons organization, using some of their licences for his books. Some common themes of his work include digital rights management, file sharing, and post-scarcity economics. Life and career Cory Efram Doctorow was born in Toronto, Ontario, on 17 July 1971. He is of Eastern European Jewish descent. His paternal grandfather was born in what is now Poland and his paternal grandmother was from Leningrad. Both fled Nazi Germany's advance eastward during World War II, and as a result Doctorow's father was born in a displaced persons camp near Baku, Azerbaijan. His grandparents and father emigrated to Canada from the Soviet Union. Doctorow's mother's family were Ukrainian-Russian Romanians. Doctorow was a friend of Columbia law ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
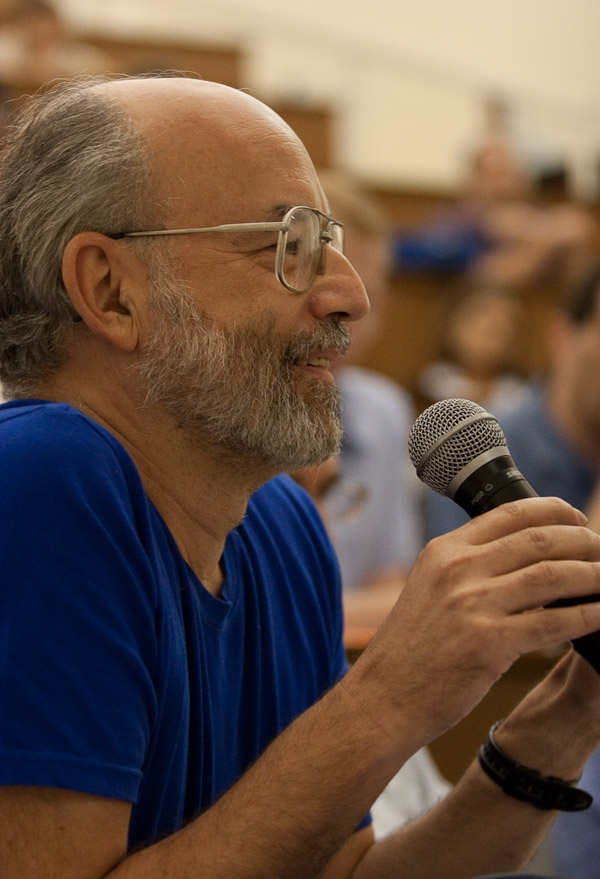
Bruce Schneier
Bruce Schneier (; born January 15, 1963) is an American cryptographer, computer security professional, privacy specialist, and writer. Schneier is a Lecturer in Public Policy at the Harvard Kennedy School and a Fellow at the Berkman Klein Center for Internet & Society as of November, 2013. He is a board member of the Electronic Frontier Foundation, Access Now, and The Tor Project; and an advisory board member of Electronic Privacy Information Center and VerifiedVoting.org. He is the author of several books on general security topics, computer security and cryptography and is a squid enthusiast. In 2015, Schneier received the EPIC Lifetime Achievement Award from Electronic Privacy Information Center. Early life Bruce Schneier is the son of Martin Schneier, a Brooklyn Supreme Court judge. He grew up in the Flatbush neighborhood of Brooklyn, New York, attending P.S. 139 and Hunter College High School. After receiving a physics bachelor's degree from the University of Rocheste ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
RSA (cryptosystem)
RSA (Rivest–Shamir–Adleman) is a public-key cryptosystem that is widely used for secure data transmission. It is also one of the oldest. The acronym "RSA" comes from the surnames of Ron Rivest, Adi Shamir and Leonard Adleman, who publicly described the algorithm in 1977. An equivalent system was developed secretly in 1973 at Government Communications Headquarters (GCHQ) (the British signals intelligence agency) by the English mathematician Clifford Cocks. That system was declassified in 1997. In a public-key cryptosystem, the encryption key is public and distinct from the decryption key, which is kept secret (private). An RSA user creates and publishes a public key based on two large prime numbers, along with an auxiliary value. The prime numbers are kept secret. Messages can be encrypted by anyone, via the public key, but can only be decoded by someone who knows the prime numbers. The security of RSA relies on the practical difficulty of factoring the product o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Xkcd
''xkcd'', sometimes styled ''XKCD'', is a webcomic created in 2005 by American author Randall Munroe. The comic's tagline describes it as "a webcomic of romance, sarcasm, math, and language". Munroe states on the comic's website that the name of the comic is not an initialism but "just a word with no phonetic pronunciation". The subject matter of the comic varies from statements on life and love to mathematical, programming, and scientific in-jokes. Some strips feature simple humor or pop-culture references. It has a cast of stick figures, and the comic occasionally features landscapes, graphs, charts, and intricate mathematical patterns such as fractals. New cartoons are added three times a week, on Mondays, Wednesdays, and Fridays. Munroe has released five spinoff books from the comic. The first book, published in 2010 and entitled ''xkcd: volume 0'', was a series of select comics from his website. His 2014 book '' What If?'' is based on his blog of the same name that an ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Kenyan General Election, 2017
General elections were held in Kenya on 8 August 2017 to elect the President, members of the National Assembly and Senate. They coincided with the 2017 Kenyan local elections which elected Governors and representatives in the devolved governments. The published results showed that incumbent President Uhuru Kenyatta of the Jubilee Party had been re-elected with 54% of the vote. However, his main opponent, Raila Odinga of the Orange Democratic Movement, refused to accept the results and contested them in the Supreme Court. The results of the presidential election were subsequently annulled by the court and fresh presidential elections was ordered to be held within 60 days. It was later announced that the elections would be held in October. The results of the parliamentary and local elections remained valid. The Jubilee Party retained its majority in the Senate, winning 34 of the 67 seats, and remained the largest party in the National Assembly with 171 of the 341 seats. The O ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Key (cryptography)
A key in cryptography is a piece of information, usually a string of numbers or letters that are stored in a file, which, when processed through a cryptographic algorithm, can encode or decode cryptographic data. Based on the used method, the key can be different sizes and varieties, but in all cases, the strength of the encryption relies on the security of the key being maintained. A key’s security strength is dependent on its algorithm, the size of the key, the generation of the key, and the process of key exchange. Scope The key is what is used to encrypt data from plaintext to ciphertext. There are different methods for utilizing keys and encryption. Symmetric cryptography Symmetric cryptography refers to the practice of the same key being used for both encryption and decryption. Asymmetric cryptography Asymmetric cryptography has separate keys for encrypting and decrypting. These keys are known as the public and private keys, respectively. Purpose Since the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
The Guardian
''The Guardian'' is a British daily newspaper. It was founded in 1821 as ''The Manchester Guardian'', and changed its name in 1959. Along with its sister papers ''The Observer'' and ''The Guardian Weekly'', ''The Guardian'' is part of the Guardian Media Group, owned by the Scott Trust Limited, Scott Trust. The trust was created in 1936 to "secure the financial and editorial independence of ''The Guardian'' in perpetuity and to safeguard the journalistic freedom and liberal values of ''The Guardian'' free from commercial or political interference". The trust was converted into a limited company in 2008, with a constitution written so as to maintain for ''The Guardian'' the same protections as were built into the structure of the Scott Trust by its creators. Profits are reinvested in journalism rather than distributed to owners or shareholders. It is considered a newspaper of record in the UK. The editor-in-chief Katharine Viner succeeded Alan Rusbridger in 2015. Since 2018, th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |