|
Rogue Application
Rogue security software is a form of malicious software and internet fraud that misleads users into believing there is a virus on their computer and aims to convince them to pay for a fake malware removal tool that actually installs malware on their computer. It is a form of scareware that manipulates users through fear, and a form of ransomware. Rogue security software has been a serious security threat in desktop computing since 2008. An early example that gained infamy was SpySheriff and its clones. Propagation Rogue security software mainly relies on social engineering (fraud) to defeat the security built into modern operating system and browser software and install itself onto victims' computers. A website may, for example, display a fictitious warning dialog stating that someone's machine is infected with a computer virus, and encourage them through manipulation to install or purchase scareware in the belief that they are purchasing genuine antivirus software. Most ha ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Rogue Security Software
Rogue security software is a form of malicious software and internet fraud that misleads users into believing there is a virus on their computer and aims to convince them to pay for a fake malware removal tool that actually installs malware on their computer. It is a form of scareware that manipulates users through fear, and a form of ransomware. Rogue security software has been a serious security threat in desktop computing since 2008. An early example that gained infamy was SpySheriff and its clones. Propagation Rogue security software mainly relies on social engineering ( fraud) to defeat the security built into modern operating system and browser software and install itself onto victims' computers. A website may, for example, display a fictitious warning dialog stating that someone's machine is infected with a computer virus, and encourage them through manipulation to install or purchase scareware in the belief that they are purchasing genuine antivirus software. Mo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Antivirus Software
Antivirus software (abbreviated to AV software), also known as anti-malware, is a computer program used to prevent, detect, and remove malware. Antivirus software was originally developed to detect and remove computer viruses, hence the name. However, with the proliferation of other malware, antivirus software started to protect from other computer threats. In particular, modern antivirus software can protect users from malicious browser helper objects (BHOs), browser hijackers, ransomware, keyloggers, backdoors, rootkits, trojan horses, worms, malicious LSPs, dialers, fraud tools, adware, and spyware. Some products also include protection from other computer threats, such as infected and malicious URLs, spam, scam and phishing attacks, online identity (privacy), online banking attacks, social engineering techniques, advanced persistent threat (APT), and botnet DDoS attacks. History 1949–1980 period (pre-antivirus days) Although the roots of the computer ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
EWeek
''eWeek'' (''Enterprise Newsweekly'', stylized as ''eWEEK''), formerly PCWeek, is a technology and business magazine. Previously owned by QuinStreet; Nashville, Tennessee marketing company TechnologyAdvice acquired eWeek in 2020. The print edition ceased in 2012, "and eWeek became an all-digital publication"), at which time Quinstreet acquired the magazine from Internet company Ziff Davis, along with Baseline.com, ChannelInsider.com, CIOInsight.com, and WebBuyersGuide.com. ''eWeek'' was started under the name ''PCWeek'' on Feb. 28, 1984. The magazine was called ''PCWeek'' until 2000, during which time it covered the rise of business computing in America; as ''eWeek'', it increased its online presence and covers more kinds of worldwide technologies. History The magazine was started by Ziff Davis to cover the use of computers as business tools. Team members that started ''PCWeek'' included John Dodge, the first news editor; Lois Paul, the first features editor; and Sam Whit ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
F-Secure
F-Secure Corporation is a global cyber security and privacy company, which has its headquarters in Helsinki, Finland. The company has offices in Denmark, Finland, France, Germany, India, Italy, Japan, Malaysia, Netherlands, Norway, Poland, Sweden, the United Kingdom and the United States, with a presence in more than 100 countries, and Security Lab operations in Helsinki and in Kuala Lumpur, Malaysia. F-Secure develops and sells antivirus, VPN, password management, and other consumer cyber security products and services for computers, mobile devices, smart TVs and internet of things devices. The company also offers several free-to-use tools on its website. History F-Secure was first established under the name Data Fellows by Petri Allas and Risto Siilasmaa on May 16, 1988. Data Fellows trained computer users and built customized databases. Three years later, the company launched its first major software project and developed the first heuristic scanner for antivirus products. F- ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Spamdexing
Spamdexing (also known as search engine spam, search engine poisoning, black-hat search engine optimization, search spam or web spam) is the deliberate manipulation of search engine indexes. It involves a number of methods, such as link building and repeating unrelated phrases, to manipulate the relevance or prominence of resources indexed, in a manner inconsistent with the purpose of the indexing system."Word Spy - spamdexing" (definition), March 2003, webpagWordSpy-spamdexing. Spamdexing could be considered to be a part of search engine optimization, although there are many search engine optimization methods that improve the quality and appearance of the content of web sites and serve content useful to many users. Overview Search engines use a variety of algorithms to determine relevancy ranking. Some of these include determining whether the search term appears in the body text or URL of a web page. Many search engines check for instances of spamdexing and will remove susp ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Vulnerability (computing)
Vulnerabilities are flaws in a computer system that weaken the overall security of the device/system. Vulnerabilities can be weaknesses in either the hardware itself, or the software that runs on the hardware. Vulnerabilities can be exploited by a threat actor, such as an attacker, to cross privilege boundaries (i.e. perform unauthorized actions) within a computer system. To exploit a vulnerability, an attacker must have at least one applicable tool or technique that can connect to a system weakness. In this frame, vulnerabilities are also known as the attack surface. Vulnerability management is a cyclical practice that varies in theory but contains common processes which include: discover all assets, prioritize assets, assess or perform a complete vulnerability scan, report on results, remediate vulnerabilities, verify remediation - repeat. This practice generally refers to software vulnerabilities in computing systems. Agile vulnerability management refers preventing attacks by ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Drive-by Download
Drive-by download is of two types, each concerning the unintended download of computer software from the Internet: # Authorized drive-by downloads are downloads which a person has authorized but without understanding the consequences (e.g. downloads which install an unknown or counterfeit executable program In computing, executable code, an executable file, or an executable program, sometimes simply referred to as an executable or binary, causes a computer "to perform indicated tasks according to encoded instructions", as opposed to a data file ..., ActiveX component, or Java applet). # Unauthorized drive-by downloads are downloads which happen without a person's knowledge, often a computer virus, spyware, malware, or crimeware. Drive-by downloads may happen when visiting a website, opening an Email attachment, e-mail attachment or clicking a link, or clicking on a deceptive pop-up window: by clicking on the window in the mistaken belief that, for example, an error repor ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
NortonLifeLock
Gen Digital Inc. (formerly Symantec Corporation and NortonLifeLock) is a multinational software company co-headquartered in Tempe, Arizona and Prague, Czech Republic. The company provides cybersecurity software and services. Gen is a Fortune 500 company and a member of the S&P 500 stock-market index. The company also has development centers in Pune, Chennai and Bangalore. Its portfolio includes Norton, Avast, LifeLock, Avira, AVG, ReputationDefender, and CCleaner. On October 9, 2014, Symantec declared it would split into two independent publicly traded companies by the end of 2015. One company would focus on security, the other on information management. On January 29, 2016, Symantec sold its information-management subsidiary, named Veritas Technologies, and which Symantec had acquired in 2004, to The Carlyle Group. On August 9, 2019, Broadcom Inc. announced they would be acquiring the Enterprise Security software division of Symantec for $10.7 billion, and the company became ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Peer-to-peer
Peer-to-peer (P2P) computing or networking is a distributed application architecture that partitions tasks or workloads between peers. Peers are equally privileged, equipotent participants in the network. They are said to form a peer-to-peer network of nodes. Peers make a portion of their resources, such as processing power, disk storage or network bandwidth, directly available to other network participants, without the need for central coordination by servers or stable hosts. Peers are both suppliers and consumers of resources, in contrast to the traditional client–server model in which the consumption and supply of resources are divided. While P2P systems had previously been used in many application domains, the architecture was popularized by the file sharing system Napster, originally released in 1999. The concept has inspired new structures and philosophies in many areas of human interaction. In such social contexts, peer-to-peer as a meme refers to the egalitarian so ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Video Clip
Video clips refer to mostly short videos, most of the time called memes, which are short videos of silly jokes and funny clips, most of the time coming from movies or any entertainment videos such as YouTube. The term is also used more loosely to mean any video program, including a full program, uploaded onto a website or other medium. They are usually taken out of context and have many gags in them. On the Internet Video clips are very popular online. there were millions of video clips available online, with new websites springing up focusing entirely on offering free video clips to users and many established corporate sites added the ability to clip existing video content on their websites. While most of this content is non-exclusive and available on competing sites, some companies produce their own videos and do not need to rely on the work of outside companies or amateurs. While some video clips are taken from established media sources, community and individually produce ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Codec
A codec is a device or computer program that encodes or decodes a data stream or signal. ''Codec'' is a portmanteau of coder/decoder. In electronic communications, an endec is a device that acts as both an encoder and a decoder on a signal or data stream, and hence is a type of codec. ''Endec'' is a portmanteau of encoder/decoder. A coder or encoder encodes a data stream or a signal for transmission or storage, possibly in encrypted form, and the decoder function reverses the encoding for playback or editing. Codecs are used in videoconferencing, streaming media, and video editing applications. History In the mid-20th century, a codec was a device that coded analog signals into digital form using pulse-code modulation (PCM). Later, the name was also applied to software for converting between digital signal formats, including companding functions. Examples An audio codec converts analog audio signals into digital signals for transmission or encodes them for storage. A receiv ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
E-mail
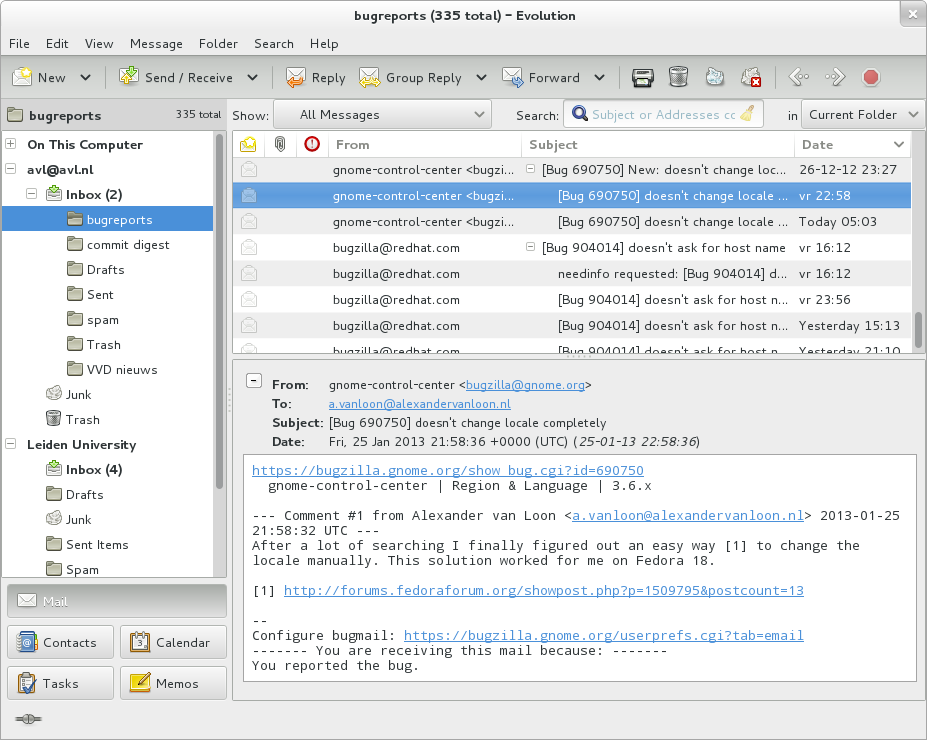
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic ( digital) version of, or counterpart to, mail, at a time when "mail" meant only physical mail (hence '' e- + mail''). Email later became a ubiquitous (very widely used) communication medium, to the point that in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries. ''Email'' is the medium, and each message sent therewith is also called an ''email.'' The term is a mass noun. Email operates across computer networks, primarily the Internet, and also local area networks. Today's email systems are based on a store-and-forward model. Email servers accept, forward, deliver, and store messages. Neither the users nor their computers are required to be online simult ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |