|
Open Relay
An open mail relay is a Simple Mail Transfer Protocol (SMTP) server configured in such a way that it allows anyone on the Internet to send e-mail through it, not just mail destined to or originating from known users. This used to be the default configuration in many mail servers; indeed, it was the way the Internet was initially set up, but open mail relays have become unpopular because of their exploitation by spammers and worms. Many relays were closed, or were placed on blacklists by other servers. History and technology Until the 1990s, mail servers were commonly intentionally configured as open relays; in fact, this was frequently the installation default setting. The traditional store and forward method of relaying e-mail to its destination required that it was passed from computer to computer (through and beyond the Internet) via modems on telephone lines. For many early networks, such as UUCPNET, FidoNet and BITNET, lists of machines that were open relays were a core par ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Email
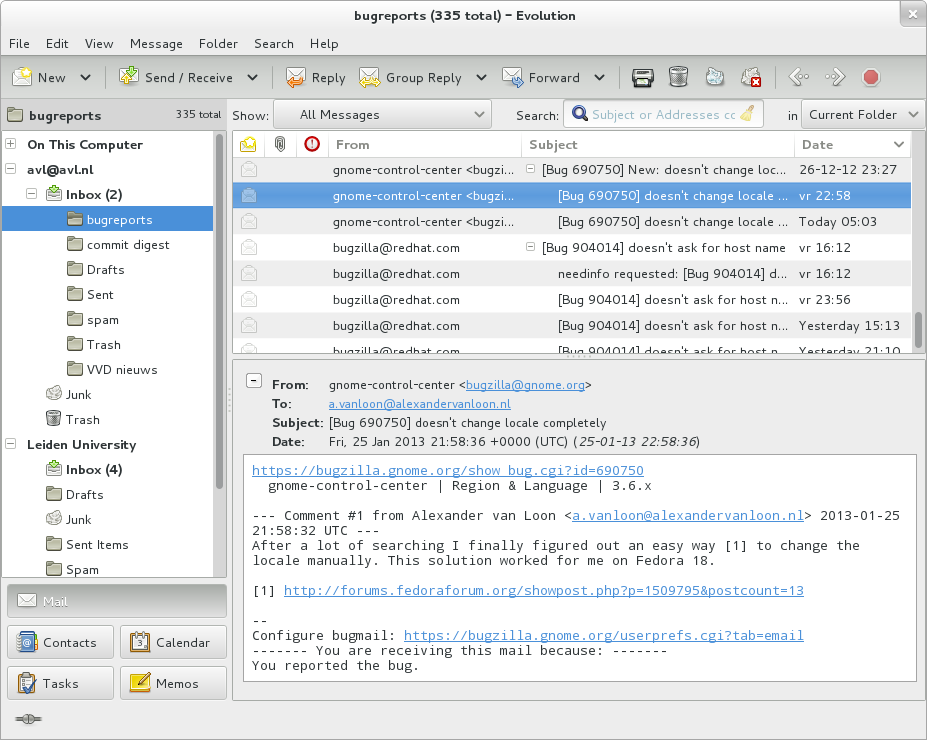
Electronic mail (email or e-mail) is a method of exchanging messages ("mail") between people using electronic devices. Email was thus conceived as the electronic ( digital) version of, or counterpart to, mail, at a time when "mail" meant only physical mail (hence '' e- + mail''). Email later became a ubiquitous (very widely used) communication medium, to the point that in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries. ''Email'' is the medium, and each message sent therewith is also called an ''email.'' The term is a mass noun. Email operates across computer networks, primarily the Internet, and also local area networks. Today's email systems are based on a store-and-forward model. Email servers accept, forward, deliver, and store messages. Neither the users nor their computers are required to be online simu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hash Buster
A hash buster is a program which randomly adds characters to data in order to change the data's hash sum. This is typically used to add words to spam e-mails, to bypass hash filters. As the e-mail's hash sum is different from the sum of e-mails previously defined as spam, the e-mail is not considered spam and therefore delivered as if it were a normal message. Hash busters can also be used to randomly add content to any kind of file until the hash sum becomes a certain sum. In e-mail context, this could be used to bypass a filter which only accepts e-mails with a certain sum. Initially spams containing "white noise" from hash busters tended to simply exhibit 'paragraphs' of literally random words, but increasingly these are now appearing somewhat grammatical. See also * Cryptographic hash function * Bayesian poisoning Bayesian poisoning is a technique used by e-mail spammers to attempt to degrade the effectiveness of spam filters that rely on Bayesian spam filtering. Bayesi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Best Current Practice
A Best Current Practice (BCP) is a ''de facto'' level of performance in engineering and information technology. It is more flexible than a standard, since techniques and tools are continually evolving. The Internet Engineering Task Force publishes Best Current Practice documents in a numbered document series. Each document in this series is paired with the currently valid Request for Comments (RFC) document. BCP was introduced in RFC-1818.rfc:1818 BCPs are document guidelines, processes, methods, and other matters not suitable for standardization. The Internet standards process itself is defined in a series of BCPs, as is the formal organizational structure of the IETF, Internet Engineering Steering Group, Internet Architecture Board, and other groups involved in that process. IETF's separate Standard Track (STD) document series defines the fully standardized network protocols of the Internet, such as the Internet Protocol, the Transmission Control Protocol, and the Domai ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Engineering Task Force
The Internet Engineering Task Force (IETF) is a standards organization for the Internet and is responsible for the technical standards that make up the Internet protocol suite (TCP/IP). It has no formal membership roster or requirements and all its participants are volunteers. Their work is usually funded by employers or other sponsors. The IETF was initially supported by the federal government of the United States but since 1993 has operated under the auspices of the Internet Society, an international non-profit organization. Organization The IETF is organized into a large number of working groups and birds of a feather informal discussion groups, each dealing with a specific topic. The IETF operates in a bottom-up task creation mode, largely driven by these working groups. Each working group has an appointed chairperson (or sometimes several co-chairs); a charter that describes its focus; and what it is expected to produce, and when. It is open to all who want to partic ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Virtual Private Network
A virtual private network (VPN) extends a private network across a public network and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network. The benefits of a VPN include increases in functionality, security, and management of the private network. It provides access to resources that are inaccessible on the public network and is typically used for remote workers. Encryption is common, although not an inherent part of a VPN connection. A VPN is created by establishing a virtual point-to-point connection through the use of dedicated circuits or with tunneling protocols over existing networks. A VPN available from the public Internet can provide some of the benefits of a wide area network (WAN). From a user perspective, the resources available within the private network can be accessed remotely. Types Virtual private networks may be classified into several categories: ;Remote a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
POP Before SMTP
POP before SMTP or SMTP after POP is a method of authentication used by mail server software which helps allow users the option to send e-mail from any location, as long as they can demonstrably also fetch their mail from the same place. The POP before SMTP approach has been superseded by SMTP Authentication. Technically, users are allowed to use SMTP from an IP address as long as they have previously made a successful login into the POP service at the same mail hosting provider, from the same address, within a predefined timeout period. The main advantage of this process is that it was generally transparent to the average user who will be connecting with an email client, which almost always attempted to fetch new mail before sending new mail. The disadvantages include a potentially complex setup for the mail hosting provider (requiring some sort of communication channel between the POP service and the SMTP service) and uncertainty as to how much time users will take to connect ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SMTP Authentication
SMTP Authentication, often abbreviated SMTP AUTH, is an extension of the Simple Mail Transfer Protocol (SMTP) whereby a client may log in using any authentication mechanism supported by the server. It is mainly used by submission servers, where authentication is mandatory. History SMTP as specified by Jon Postel in the 1970s did not provide for using passwords for sending email messages; each server was by design an open mail relay. As a result, spam and worms, while not initially a problem, had become a plague by the late '90s. Before SMTP AUTH, a ''relay client'' had to be identified by IP address, which is only practical for email services provided by the same Internet service provider (ISP) supplying the connection, or else using specific hacks, such as POP before SMTP. John Gardiner Myers published the first draft of SMTP AUTH in 1995, and it has been successively developed and discussed in the IETF along with mail submission protocol, Extended SMTP (ESMTP), and Simple Auth ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Smart Host
A smart host or smarthost is an email server via which third parties can send emails and have them forwarded on to the email recipients' email servers. Smarthosts were originally open mail relays, but most providers now requiring authentication from the sender, to verify that the sender is authorised - for example, an ISP might run a smarthost for their paying customers only. Use in spam control efforts In an effort to reduce email spam originating from their customer's IP addresses, some internet service providers (ISPs), will not allow their customers to communicate out directly with recipient mailservers via the default SMTP port number 25. Instead, often they will set up a smarthost to which their customers can direct all their outward mail - or customers could alternatively use one of the commercial smarthost services. Sometimes, even if outward port 25 is not blocked, an individual or organisation's normal external IP address has difficulty getting SMTP mail accepted. This c ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Service Provider
An Internet service provider (ISP) is an organization that provides services for accessing, using, or participating in the Internet. ISPs can be organized in various forms, such as commercial, community-owned, non-profit, or otherwise privately owned. Internet services typically provided by ISPs can include Internet access, Internet transit, domain name registration, web hosting, Usenet service, and colocation. An ISP typically serves as the access point or the gateway that provides a user access to everything available on the Internet. Such a network can also be called as an eyeball network. History The Internet (originally ARPAnet) was developed as a network between government research laboratories and participating departments of universities. Other companies and organizations joined by direct connection to the backbone, or by arrangements through other connected companies, sometimes using dialup tools such as UUCP. By the late 1980s, a process was set in place ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Zombie (computing)
In computing, a zombie is a computer connected to the Internet that has been compromised by a hacker via a computer virus, computer worm, or trojan horse program and can be used to perform malicious tasks under the remote direction of the hacker. Zombie computers often coordinate together in a botnet controlled by the hacker, and are used for activities such as spreading e-mail spam and launching distributed denial-of-service attacks (DDoS attacks) against web servers. Most victims are unaware that their computers have become zombies. The concept is similar to the zombie of Haitian Voodoo folklore, which refers to a corpse resurrected by a sorcerer via magic and enslaved to the sorcerer's commands, having no free will of its own. A coordinated DDoS attack by multiple botnet machines also resembles a "zombie horde attack", as depicted in fictional zombie films. Advertising Zombie computers have been used extensively to send e-mail spam; as of 2005, an estimated 50&ndash ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Botnet
A botnet is a group of Internet-connected devices, each of which runs one or more bots. Botnets can be used to perform Distributed Denial-of-Service (DDoS) attacks, steal data, send spam, and allow the attacker to access the device and its connection. The owner can control the botnet using command and control (C&C) software. The word "botnet" is a portmanteau of the words "robot" and "network". The term is usually used with a negative or malicious connotation. Overview A botnet is a logical collection of Internet-connected devices, such as computers, smartphones or Internet of things (IoT) devices whose security have been breached and control ceded to a third party. Each compromised device, known as a "bot," is created when a device is penetrated by software from a ''malware'' (malicious software) distribution. The controller of a botnet is able to direct the activities of these compromised computers through communication channels formed by standards-based network protocols, suc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Mail Consortium
The Internet Mail Consortium (IMC) was an organization between 1996 and 2002 that claimed to be the only international organization focused on cooperatively managing and promoting the rapidly expanding world of electronic mail on the Internet. The goals of the IMC included greatly expanding the role of mail on the Internet into areas such as commerce and entertainment, advancing new Internet mail technologies, and making it easier for all Internet users, particularly novices, to get the most out of the growing communications medium. It did this by providing information about all the Internet mail standards and technologies. They also prepared reports that supplemented the Internet Engineering Task Force's RFCs. Headquartered in Santa Cruz, California, the IMC was founded by Paul E. Hoffman about 1996 and ceased activity in 2002. See also * Versit Consortium The versit Consortium was a multivendor initiative founded by Apple Computer, AT&T, IBM and Siemens in the early 1990s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |