|
Multilevel Security
Multilevel security or multiple levels of security (MLS) is the application of a computer system to process information with incompatible classifications (i.e., at different security levels), permit access by users with different security clearances and needs-to-know, and prevent users from obtaining access to information for which they lack authorization. There are two contexts for the use of multilevel security. One context is to refer to a system that is adequate to protect itself from subversion and has robust mechanisms to separate information domains, that is, trustworthy. Another context is to refer to an application of a computer that will require the computer to be strong enough to protect itself from subversion, and have adequate mechanisms to separate information domains, that is, a system we must trust. This distinction is important because systems that need to be trusted are not necessarily trustworthy. Trusted operating systems An MLS operating environment often r ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Classified Information In The United States
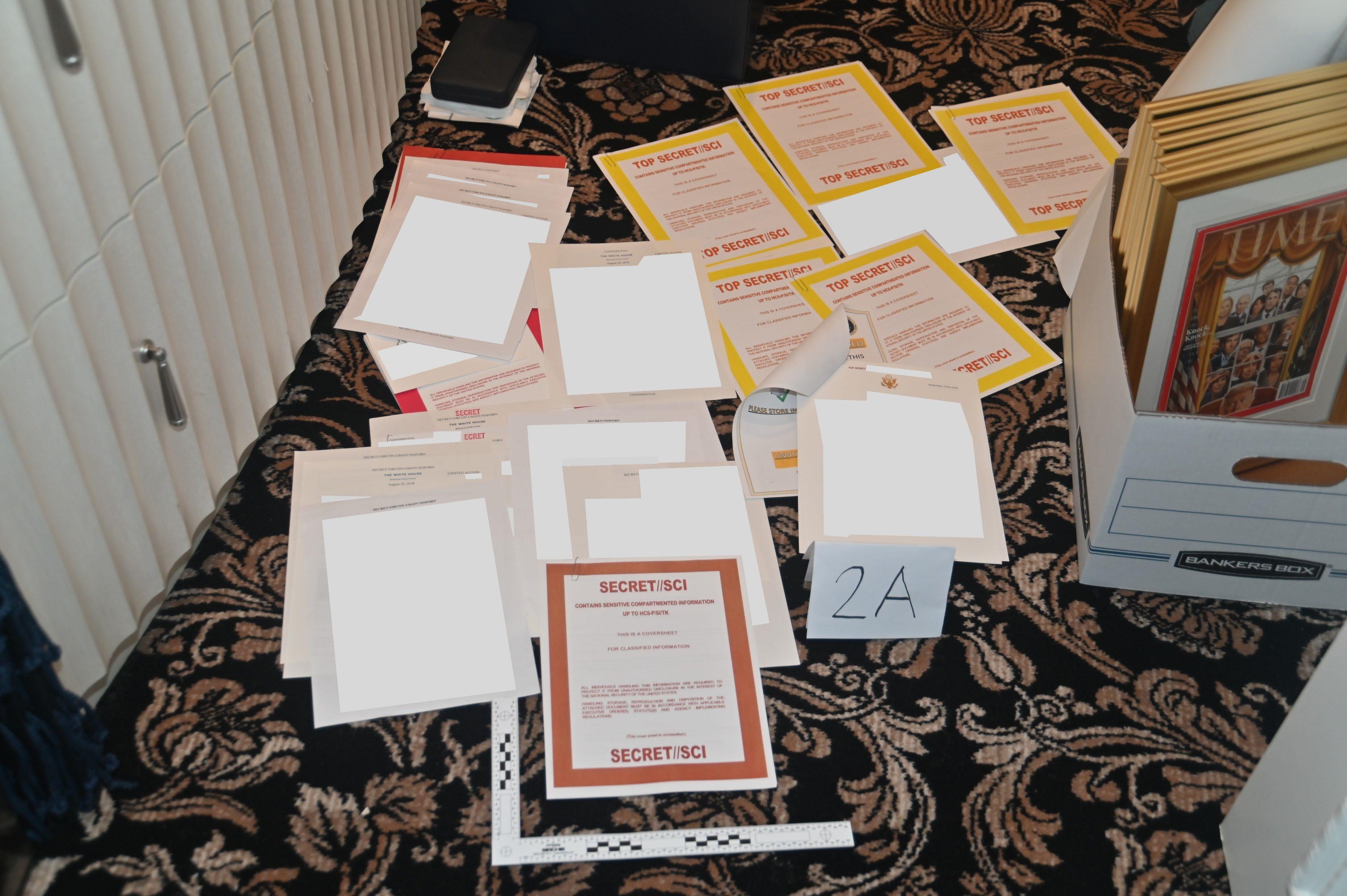
The United States government classification system is established under Executive Order 13526, the latest in a long series of executive orders on the topic of classified information beginning in 1951. Issued by President Barack Obama in 2009, Executive Order 13526 replaced earlier executive orders on the topic and modified the regulations codified to 32 C.F.R. 2001. It lays out the system of classification, declassification, and handling of national security information generated by the U.S. government and its employees and contractors, as well as information received from other governments. The desired degree of secrecy about such information is known as its sensitivity. Sensitivity is based upon a calculation of the damage to national security that the release of the information would cause. The United States has three levels of classification: Confidential, Secret, and Top Secret. Each level of classification indicates an increasing degree of sensitivity. Thus, if one holds ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
FreeBSD
FreeBSD is a free-software Unix-like operating system descended from the Berkeley Software Distribution (BSD). The first version was released in 1993 developed from 386BSD, one of the first fully functional and free Unix clones on affordable home-class hardware, and has since continuously been the most commonly used BSD-derived operating system. FreeBSD maintains a complete system, delivering a kernel, device drivers, userland utilities, and documentation, as opposed to Linux only delivering a kernel and drivers, and relying on third-parties such as GNU for system software. The FreeBSD source code is generally released under a permissive BSD license, as opposed to the copyleft GPL used by Linux. The project includes a security team overseeing all software shipped in the base distribution. Third-party applications may be installed using the pkg package management system or from source via FreeBSD Ports. The project is supported and promoted by the FreeBSD Foundation ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
BAE Systems
BAE Systems plc is a British Multinational corporation, multinational Aerospace industry, aerospace, military technology, military and information security company, based in London. It is the largest manufacturer in Britain as of 2017. It is the largest defence contractor in Europe and the seventh largest in the world based on applicable 2021 revenues. Its largest operations are in the United Kingdom and in the United States, where its BAE Systems Inc. subsidiary is one of the six largest suppliers to the United States Department of Defense, US Department of Defense. Its next biggest markets are Saudi Arabia, then Australia; other major markets include Canada, Japan, India, Turkey, Qatar, Oman and Sweden. The company was formed on 30 November 1999 by the British pound sterling, £7.7 billion purchase of and merger of Marconi Electronic Systems (MES), the defence electronics and naval shipbuilding subsidiary of the General Electric Company plc (GEC), with British Aerospace ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Covert Channel
In computer security, a covert channel is a type of attack that creates a capability to transfer information objects between processes that are not supposed to be allowed to communicate by the computer security policy. The term, originated in 1973 by Butler Lampson, is defined as channels "not intended for information transfer at all, such as the service program's effect on system load," to distinguish it from ''legitimate'' channels that are subjected to access controls by COMPUSEC. Characteristics A covert channel is so called because it is hidden from the access control mechanisms of secure operating systems since it does not use the legitimate data transfer mechanisms of the computer system (typically, read and write), and therefore cannot be detected or controlled by the security mechanisms that underlie secure operating systems. Covert channels are exceedingly hard to install in real systems, and can often be detected by monitoring system performance. In addition, they ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
X Window System
The X Window System (X11, or simply X) is a windowing system for bitmap displays, common on Unix-like operating systems. X originated as part of Project Athena at Massachusetts Institute of Technology (MIT) in 1984. The X protocol has been at version 11 (hence "X11") since September 1987. The X.Org Foundation leads the X project, with the current reference implementation, X.Org Server, available as free and open-source software under the MIT License and similar permissive licenses. Purpose and abilities X is an architecture-independent system for remote graphical user interfaces and input device capabilities. Each person using a networked computer terminal, terminal has the ability to interact with the display with any type of user input device. In its standard distribution it is a complete, albeit simple, display and interface solution which delivers a standard widget toolkit, toolkit and protocol stack for building graphical user interfaces on most Unix-like operating syst ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
OpenSolaris
OpenSolaris () is a discontinued open-source computer operating system for SPARC and x86 based systems, created by Sun Microsystems and based on Solaris. Its development began in the mid 2000s and ended in 2010. OpenSolaris was developed as a combination of several software ''consolidations'' that were open sourced starting with Solaris 10. It includes a variety of free software, including popular desktop and server software. It is a descendant of the UNIX System V Release 4 (SVR4) code base developed by Sun and AT&T in the late 1980s and is the only version of the System V variant of UNIX available as open source. After Oracle's acquisition of Sun Microsystems in 2010, Oracle discontinued development of OpenSolaris in house, pivoting to focus exclusively on the development of the proprietary Solaris Express (now Oracle Solaris). Prior to Oracle's close-sourcing Solaris, a group of former OpenSolaris developers began efforts to fork the core software under the name ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Solaris (operating System)
Oracle Solaris is a proprietary software, proprietary Unix operating system offered by Oracle Corporation, Oracle for SPARC and x86-64 based workstations and server (computing), servers. Originally developed by Sun Microsystems as Solaris, it superseded the company's earlier SunOS in 1993 and became known for its scalability, especially on SPARC systems, and for originating many innovative features such as DTrace, ZFS and Time Slider. After the Acquisition of Sun Microsystems by Oracle Corporation, Sun acquisition by Oracle in 2010, it was renamed Oracle Solaris. Solaris was registered as compliant with the Single UNIX Specification until April 29, 2019. Historically, Solaris was developed as proprietary software. In June 2005, Sun Microsystems released most of the codebase under the CDDL license, and founded the OpenSolaris Open-source software, open-source project. Sun aimed to build a developer and user community with OpenSolaris; after the Oracle acquisition in 2010, the Open ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Solaris Trusted Extensions
Solaris Trusted Extensions is a set of security extensions incorporated in the Solaris 10 operating system by Sun Microsystems, featuring a mandatory access control model. It succeeds Trusted Solaris, a family of security-evaluated operating systems based on earlier versions of Solaris. Solaris 10 5/09 is Common Criteria certified at Evaluation Assurance Level EAL4+ against the CAPP, RBACPP, and LSPP protection profiles. Overview Certain Trusted Solaris features, such as fine-grained privileges, are now part of the standard Solaris 10 release. Beginning with Solaris 10 11/06, Solaris now includes a component called Solaris Trusted Extensions which gives it the additional features necessary to position it as the successor to Trusted Solaris. Inclusion of these features in the mainstream Solaris release marks a significant change from Trusted Solaris, as it is no longer necessary to use a different Solaris release with a modified kernel for labeled security environments. Solaris ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Oracle Corporation
Oracle Corporation is an American Multinational corporation, multinational computer technology company headquartered in Austin, Texas. Co-founded in 1977 in Santa Clara, California, by Larry Ellison, who remains executive chairman, Oracle was the List of the largest software companies, third-largest software company in the world in 2020 by revenue and market capitalization. The company's 2023 ranking in the Forbes Global 2000, ''Forbes'' Global 2000 was 80. The company sells Database, database software, particularly Oracle Database, and cloud computing. Oracle's core application software is a suite of enterprise software products, such as enterprise resource planning (ERP) software, human capital management (HCM) software, customer relationship management (CRM) software, enterprise performance management (EPM) software, Customer Experience Commerce (CX Commerce) and supply chain management (SCM) software. History Larry Ellison, Bob Miner, and Ed Oates co-founded Oracle in ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Sun Microsystems
Sun Microsystems, Inc., often known as Sun for short, was an American technology company that existed from 1982 to 2010 which developed and sold computers, computer components, software, and information technology services. Sun contributed significantly to the evolution of several key computing technologies, among them Unix, Reduced instruction set computer, RISC processors, thin client computing, and virtualization, virtualized computing. At its height, the Sun headquarters were in Santa Clara, California (part of Silicon Valley), on the former west campus of the Agnews Developmental Center. Sun products included computer servers and workstations built on its own Reduced instruction set computer, RISC-based SPARC processor architecture, as well as on x86-based AMD Opteron and Intel Xeon processors. Sun also developed its own computer storage, storage systems and a suite of software products, including the Unix-based SunOS and later Solaris operating system, Solaris operating s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Superuser
In computing, the superuser is a special user account used for system administration. Depending on the operating system (OS), the actual name of this account might be root, administrator, admin or supervisor. In some cases, the actual name of the account is not the determining factor; on Unix-like systems, for example, the user with a user identifier (UID) of zero is the superuser .e., uid=0 regardless of the name of that account; and in systems which implement a r model, any user with the role of superuser (or its synonyms) can carry out all actions of the superuser account. The principle of least privilege recommends that most users and applications run under an ordinary account to perform their work, as a superuser account is capable of making unrestricted, potentially adverse, system-wide changes. Unix and Unix-like In Unix-like computer OSes (such as Linux), ''root'' is the conventional name of the user who has all rights or permissions (to all files and programs) in all mod ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Biba Model
The Biba Model or Biba Integrity Model developed by Kenneth J. Biba in 1975, is a formal state transition system of computer security policy describing a set of access control rules designed to ensure data integrity. Data and subjects are grouped into ordered levels of integrity. The model is designed so that subjects may not corrupt data in a level ranked higher than the subject, or be corrupted by data from a lower level than the subject. In general the model was developed to address integrity as the core principle, which is the direct inverse of the Bell–LaPadula model which focuses on confidentiality. Features In general, preservation of data ''integrity'' has three goals: * Prevent data modification by unauthorized parties * Prevent unauthorized data modification by authorized parties * Maintain internal and external consistency (i.e. data reflects the real world) This security model is directed toward data ''integrity'' (rather than ''confidentiality'') and is characte ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |