|
End Node Problem
The end node problem arises when individual computers are used for sensitive work and/or temporarily become part of a trusted, well-managed network/cloud and then are used for more risky activities and/or join untrusted networks. (Individual computers on the periphery of networks/clouds are called end nodes.) End nodes often are not managed to the trusted network‘s high computer security standards. End nodes often have weak/outdated software, weak security tools, excessive permissions, mis-configurations, questionable content and apps, and covert exploitations. Cross contamination and unauthorized release of data from within a computer system becomes the problem. Within the vast cyber-ecosystem, these end nodes often attach transiently to one or more clouds/networks, some trustworthy and others not. A few examples: a corporate desktop browsing the Internet, a corporate laptop checking company webmail via a coffee shop's open Wi-Fi access point, a personal computer used to telec ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Security
Computer security, cybersecurity (cyber security), or information technology security (IT security) is the protection of computer systems and networks from attack by malicious actors that may result in unauthorized information disclosure, theft of, or damage to hardware, software, or data, as well as from the disruption or misdirection of the services they provide. The field has become of significance due to the expanded reliance on computer systems, the Internet, and wireless network standards such as Bluetooth and Wi-Fi, and due to the growth of smart devices, including smartphones, televisions, and the various devices that constitute the Internet of things (IoT). Cybersecurity is one of the most significant challenges of the contemporary world, due to both the complexity of information systems and the societies they support. Security is of especially high importance for systems that govern large-scale systems with far-reaching physical effects, such as power distribution, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Strong Authentication
Strong authentication is a notion with several definitions. Strong (customer) authentication definitions Strong authentication is often confused with two-factor authentication (more generally known as multi-factor authentication), but strong authentication is not necessarily multi-factor authentication. Soliciting multiple answers to challenge questions may be considered strong authentication but, unless the process also retrieves 'something you have' or 'something you are', it would not be considered multi-factor authentication. The FFIEC issued supplemental guidance on this subject in August 2006, in which they clarified, "By definition true multifactor authentication requires the use of solutions from two or more of the three categories of factors. Using multiple solutions from the same category ... would not constitute multifactor authentication." Another commonly found class of definitions relates to a cryptographic process, or more precisely, authentication based on a ch ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Network Security
A network security policy (NSP) is a generic document that outlines rules for computer network access, determines how policies are enforced and lays out some of the basic architecture of the company security/ network security environment. The document itself is usually several pages long and written by a committee. A security policy is a complex document, meant to govern data access, web-browsing habits, use of passwords, encryption, email attachments and more. It specifies these rules for individuals or groups of individuals throughout the company. The policies could be expressed as a set of instructions that understood by special purpose network hardware dedicated for securing the network. Security policy should keep the malicious users out and also exert control over potential risky users within an organization. Understanding what information and services are available and to which users, as well as what the potential is for damage and whether any protection is already in plac ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Secure End Node
A Secure End Node is a trusted, individual computer that temporarily becomes part of a trusted, sensitive, well-managed network and later connects to many other (un)trusted networks/clouds. SEN's cannot communicate good or evil data between the various networks (e.g. exfiltrate sensitive information, ingest malware, etc.). SENs often connect through an untrusted medium (e.g. the Internet) and thus require a secure connection and strong authentication (of the device, software, user, environment, etc.). The amount of trust required (and thus operational, physical, personnel, network, and system security applied) is commensurate with the risk of piracy, tampering, and reverse engineering (within a given threat environment). An essential characteristic of SENs is they cannot persist information as they change between networks (or domains). The remote, private, and secure network might be organization's in-house network or a cloud service. A Secure End Node typically involves auth ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Node (networking)
In telecommunications networks, a node (, ‘knot’) is either a redistribution point or a communication endpoint. The definition of a node depends on the network and protocol layer referred to. A physical network node is an electronic device that is attached to a network, and is capable of creating, receiving, or transmitting information over a communication channel. A passive distribution point such as a distribution frame or patch panel is consequently not a node. Computer networks In data communication, a physical network node may either be data communication equipment (DCE) such as a modem, hub, bridge or switch; or data terminal equipment (DTE) such as a digital telephone handset, a printer or a host computer. If the network in question is a local area network (LAN) or wide area network (WAN), every LAN or WAN node that participates on the data link layer must have a network address, typically one for each network interface controller it possesses. Examples are compu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Host (network)
A network host is a computer or other device connected to a computer network. A host may work as a server offering information resources, services, and applications to users or other hosts on the network. Hosts are assigned at least one network address. A computer participating in networks that use the Internet protocol suite may also be called an IP host. Specifically, computers participating in the Internet are called Internet hosts. Internet hosts and other IP hosts have one or more IP addresses assigned to their network interfaces. The addresses are configured either manually by an administrator, automatically at startup by means of the Dynamic Host Configuration Protocol (DHCP), or by stateless address autoconfiguration methods. Network hosts that participate in applications that use the client–server model of computing, are classified as server or client systems. Network hosts may also function as nodes in peer-to-peer applications, in which all nodes share and consume ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Common Access Card
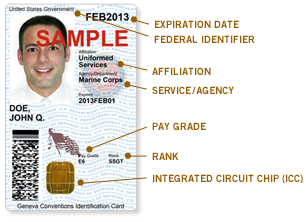
The Common Access Card, also commonly referred to as the CAC is a smart card about the size of a credit card. It is the standard identification for Active Duty United States Defense personnel, to include the Selected Reserve and National Guard, United States Department of Defense (DoD) civilian employees, United States Coast Guard (USCG) civilian employees and eligible DoD and USCG contractor personnel. It is also the principal card used to enable physical access to buildings and controlled spaces, and it provides access to defense computer networks and systems. It also serves as an identification card under the Geneva Conventions (especially the Third Geneva Convention). In combination with a personal identification number, a CAC satisfies the requirement for two-factor authentication: something the user knows combined with something the user has. The CAC also satisfies the requirements for digital signature and data encryption technologies: authentication, integrity and non-rep ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
LiveCD
A live CD (also live DVD, live disc, or live operating system) is a complete bootable computer installation including operating system which runs directly from a CD-ROM or similar storage device into a computer's memory, rather than loading from a hard disk drive. A live CD allows users to run an operating system for any purpose without installing it or making any changes to the computer's configuration. Live CDs can run on a computer without secondary storage, such as a hard disk drive, or with a corrupted hard disk drive or file system, allowing data recovery. As CD and DVD drives have been steadily phased-out, live CDs have become less popular, being replaced by live USBs, which are equivalent systems written onto USB flash drives, which have the added benefit of having writeable storage. The functionality of a live CD is also available with an external hard disk drive connected by USB. Many live CDs offer the option of persistence by writing files to a hard drive or USB fl ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Lightweight Portable Security
Lightweight Portable Security (LPS) was a Linux LiveCD (or LiveUSB) distribution, developed and publicly distributed by the United States Department of Defense’s Air Force Research Laboratory, that is designed to serve as a secure end node. The Air Force Research Laboratory actively maintained LPS and its successor, Trusted End Node Security (TENS) from 2007 to 2021. It can run on almost any x86_64 computer (PC or Mac). LPS boots only in RAM, creating a pristine, non-persistent end node. It supports DoD-approved Common Access Card (CAC) readers, as required for authenticating users into PKI-authenticated gateways to access internal DoD networks. LPS turns an untrusted system (such as a home computer) into a trusted network client. No trace of work activity (or malware) can be written to the local computer's hard drive. As of September 2011 (version 1.2.5), the LPS public distribution includes a smart card-enabled Firefox browser supporting DoD's CAC and Personal Identity Veri ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
United States Department Of Defense
The United States Department of Defense (DoD, USDOD or DOD) is an executive branch department of the federal government charged with coordinating and supervising all agencies and functions of the government directly related to national security and the United States Armed Forces. The DoD is the largest employer in the world, with over 1.34 million active-duty service members (soldiers, marines, sailors, airmen, and guardians) as of June 2022. The DoD also maintains over 778,000 National Guard and reservists, and over 747,000 civilians bringing the total to over 2.87 million employees. Headquartered at the Pentagon in Arlington, Virginia, just outside Washington, D.C., the DoD's stated mission is to provide "the military forces needed to deter war and ensure our nation's security". The Department of Defense is headed by the secretary of defense, a cabinet-level head who reports directly to the president of the United States. Beneath the Department of Defense are th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Kernel (operating System)
The kernel is a computer program at the core of a computer's operating system and generally has complete control over everything in the system. It is the portion of the operating system code that is always resident in memory and facilitates interactions between hardware and software components. A full kernel controls all hardware resources (e.g. I/O, memory, cryptography) via device drivers, arbitrates conflicts between processes concerning such resources, and optimizes the utilization of common resources e.g. CPU & cache usage, file systems, and network sockets. On most systems, the kernel is one of the first programs loaded on startup (after the bootloader). It handles the rest of startup as well as memory, peripherals, and input/output (I/O) requests from software, translating them into data-processing instructions for the central processing unit. The critical code of the kernel is usually loaded into a separate area of memory, which is protected from access by application ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Wi-Fi
Wi-Fi () is a family of wireless network protocols, based on the IEEE 802.11 family of standards, which are commonly used for local area networking of devices and Internet access, allowing nearby digital devices to exchange data by radio waves. These are the most widely used computer networks in the world, used globally in home and small office networks to link desktop and laptop computers, tablet computers, smartphones, smart TVs, printers, and smart speakers together and to a wireless router to connect them to the Internet, and in wireless access points in public places like coffee shops, hotels, libraries and airports to provide visitors with Internet access for their mobile devices. ''Wi-Fi'' is a trademark of the non-profit Wi-Fi Alliance, which restricts the use of the term ''Wi-Fi Certified'' to products that successfully complete interoperability certification testing. the Wi-Fi Alliance consisted of more than 800 companies from around the world. over 3.05 billion ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |