|
Data Loss Prevention Software
Data loss prevention (DLP) software detects potential data breaches/data ex-filtration transmissions and prevents them by monitoring, detecting and blocking sensitive data while ''in use'' (endpoint actions), ''in motion'' (network traffic), and ''at rest'' (data storage). The terms "data loss" and "data leak" are related and are often used interchangeably.Asaf Shabtai, Yuval Elovici, Lior Rokach,A Survey of Data Leakage Detection and Prevention Solutions Springer-Verlag New York Incorporated, 2012 Data loss incidents turn into data leak incidents in cases where media containing sensitive information is lost and subsequently acquired by an unauthorized party. However, a data leak is possible without losing the data on the originating side. Other terms associated with data leakage prevention are information leak detection and prevention (ILDP), information leak prevention (ILP), content monitoring and filtering (CMF), information protection and control (IPC) and extrusion prevention ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Data Loss
Data loss is an error condition in information systems in which information is destroyed by failures (like failed spindle motors or head crashes on hard drives) or neglect (like mishandling, careless handling or storage under unsuitable conditions) in Computer data storage, storage, data transmission, transmission, or data processing, processing. Information systems implement backup and disaster recovery equipment and processes to prevent data loss or Data recovery, restore lost data. Data loss can also occur if the physical medium containing the data is lost or stolen. Data loss is distinguished from data unavailability, which may arise from a network outage. Although the two have substantially similar consequences for users, data unavailability is temporary, while data loss may be permanent. Data loss is also distinct from data breach, an incident where data falls into the wrong hands, although the term data loss has been used in those incidents. Types *''Procedural'' * ''Intenti ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
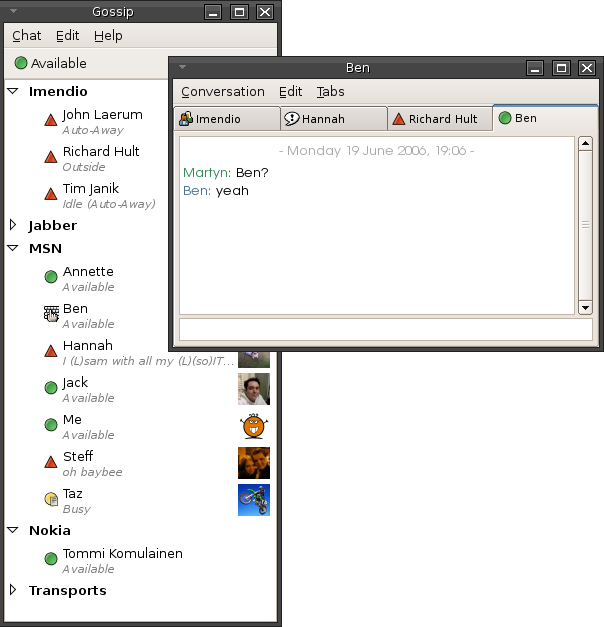
Instant Messaging
Instant messaging (IM) technology is a type of online chat allowing real-time text transmission over the Internet or another computer network. Messages are typically transmitted between two or more parties, when each user inputs text and triggers a transmission to the recipient(s), who are all connected on a common network. It differs from email in that conversations over instant messaging happen in real-time (hence "instant"). Most modern IM application (computing), applications (sometimes called "social messengers", "messaging apps" or "chat apps") use push technology and also add other features such as emojis (or graphical smileys), file transfer, chatbots, voice over IP, or Videotelephony, video chat capabilities. Instant messaging systems tend to facilitate connections between specified known users (often using a contact list also known as a "buddy list" or "friend list"), and can be standalone applications or integrated into e.g. a wider social media platform, or a website ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Endpoint Detection And Response
Endpoint detection and response (EDR), also known as endpoint threat detection and response (ETDR), is a cybersecurity technology that continually monitors an "endpoint" (e.g. mobile phone, laptop, Internet-of-Things device) to mitigate malicious cyber threats. History In 2013, Anton Chuvakin of Gartner coined the term "endpoint threat detection and response" for "tools primarily focused on detecting and investigating suspicious activities (and traces of such) other problems on hosts/endpoints". Now, it is commonly known as "endpoint detection and response". According to the ''Endpoint Detection and Response - Global Market Outlook (2017-2026)'' report, the adoption of cloud-based and on-premises EDR solutions are going to grow 26% annually, and will be valued at $7273.26 million by 2026. According to the ''Artificial Intelligence (AI) in Cyber Security Market'' report by Zion Market Research, the role of machine learning and artificial intelligence will create a $30.9 billion ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Metadata Removal Tool
Metadata removal tool or metadata scrubber is a type of privacy software built to protect the privacy of its users by removing potentially privacy-compromising metadata from files before they are shared with others, e.g., by sending them as e-mail attachments or by posting them on the Web. Overview Metadata can be found in many types of files such as documents, spreadsheets, presentations, images, and audio files. They can include information such as details on the file authors, file creation and modification dates, geographical location, document revision history, thumbnail images, and comments. Metadata may be added to files by users, but some metadata is often automatically added to files by authoring applications or by devices used to produce the files, without user intervention. Since metadata is sometimes not clearly visible in authoring applications (depending on the application and its settings), there is a risk that the user will be unaware of its existence or will forg ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
List Of Backup Software
This is a list of notable backup software that performs data backups. Archivers, transfer protocols, and version control systems are often used for backups but only software focused on backup is listed here. See Comparison of backup software for features. Free and open-source software Commercial and closed-source software Defunct software See also * Comparison of file synchronization software * Comparison of online backup services This is a comparison of online backup services. Online backup is a special kind of online storage service; however, various products that are designed for file storage may not have features or characteristics that others designed for backup have ... * Data recovery * File synchronization * List of data recovery software * Remote backup service * Tape management system Notes References {{Reflist * Backup software * ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Data In Transit
Data in transit, also referred to as data in motion and data in flight, is data en route between source and destination, typically on a computer network. Data in transit can be separated into two categories: information that flows over the public or untrusted network such as the Internet and data that flows in the confines of a private network such as a corporate or enterprise local area network (LAN). Data in transit is used as a complement to the terms '' data in use'', and '' data at rest'' which together define the three states of digital data. See also *Bandwidth-delay product In data communications, the bandwidth-delay product is the product of a data link's capacity (in bits per second) and its round-trip delay time (in seconds). The result, an amount of data measured in bits (or bytes), is equivalent to the maxim ... References Computer networks {{network-stub ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Data In Use
Data in use is an information technology term referring to active data which is stored in a non-persistent digital state typically in computer random-access memory (RAM), CPU caches, or CPU registers. Scranton, PA data scientist Daniel Allen in 1996 proposed ''Data in use'' as a complement to the terms ''data in transit'' and '' data at rest'' which together define the three states of digital data. Alternative definitions Data in use refers to data in computer memory. Some cloud software as a service (SaaS) providers refer to data in use as any data currently being processed by applications, as the CPU and memory are utilized. Concerns Because of its nature, data in use is of increasing concern to businesses, government agencies and other institutions. Data in use, or memory, can contain sensitive data including digital certificates, encryption keys, intellectual property (software algorithms, design data), and personally identifiable information. Compromising data in use ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Data Retention
Data retention defines the policies of persistent data and records management for meeting legal and business data archival requirements. Although sometimes interchangeable, it is not to be confused with the Data Protection Act 1998. The different data retention policies weigh legal and privacy concerns against economics and need-to-know concerns to determine the retention time, archival rules, data formats, and the permissible means of storage, access, and encryption. In the field of telecommunications, data retention generally refers to the storage of call detail records (CDRs) of telephony and internet traffic and transaction data ( IPDRs) by governments and commercial organisations. In the case of government data retention, the data that is stored is usually of telephone calls made and received, emails sent and received, and websites visited. Location data is also collected. The primary objective in government data retention is traffic analysis and mass surveillance. By a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Unstructured Data
Unstructured data (or unstructured information) is information that either does not have a pre-defined data model or is not organized in a pre-defined manner. Unstructured information is typically text-heavy, but may contain data such as dates, numbers, and facts as well. This results in irregularities and ambiguities that make it difficult to understand using traditional programs as compared to data stored in fielded form in databases or annotated ( semantically tagged) in documents. In 1998, Merrill Lynch said "unstructured data comprises the vast majority of data found in an organization, some estimates run as high as 80%." It's unclear what the source of this number is, but nonetheless it is accepted by some. Other sources have reported similar or higher percentages of unstructured data. , IDC and Dell EMC project that data will grow to 40 zettabytes by 2020, resulting in a 50-fold growth from the beginning of 2010. More recently, IDC and Seagate predict that the global ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cyberattack
A cyberattack is any offensive maneuver that targets computer information systems, computer networks, infrastructures, or personal computer devices. An attacker is a person or process that attempts to access data, functions, or other restricted areas of the system without authorization, potentially with malicious intent. Depending on the context, cyberattacks can be part of cyber warfare or cyberterrorism. A cyberattack can be employed by sovereign states, individuals, groups, societies or organisations and it may originate from an anonymous source. A product that facilitates a cyberattack is sometimes called a cyber weapon. Cyber attacks have increased with an alarming rate for the last few years A cyberattack may steal, alter, or destroy a specified target by hacking into a susceptible system. Cyberattacks can range from installing spyware on a personal computer to attempting to destroy the infrastructure of entire nations. Legal experts are seeking to limit the use of th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cloud-native Computing
Cloud native computing is an approach in software development that utilizes cloud computing to "build and run scalable applications in modern, dynamic environments such as public, private, and hybrid clouds". These technologies such as containers, microservices, serverless functions, cloud native processors and immutable infrastructure, deployed via declarative code are common elements of this architectural style. Cloud native technologies focus on minimizing users' operational burden. These techniques enable loosely coupled systems that are resilient, manageable, and observable. Combined with robust automation, they allow engineers to make high-impact changes frequently and predictably with minimal toil. Frequently, cloud-native applications are built as a set of microservices that run in Open Container Initiative compliant containers, such as Containerd, and may be orchestrated in Kubernetes and managed and deployed using DevOps and Git CI workflows (although there is a la ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |