|
Crond
The cron command-line utility is a job scheduler on Unix-like operating systems. Users who set up and maintain software environments use cron to schedule jobs (commands or shell scripts), also known as cron jobs, to run periodically at fixed times, dates, or intervals. It typically automates system maintenance or administration—though its general-purpose nature makes it useful for things like downloading files from the Internet and downloading email at regular intervals. Cron is most suitable for scheduling repetitive tasks. Scheduling one-time tasks can be accomplished using the associated at (command), ''at'' utility. Cron's name originates from ''chronos'', the Greek word for time. Overview The actions of cron are driven by a crontab (cron table) file, a configuration file that specifies Unix shell, shell commands to run periodically on a given schedule. The crontab files are stored where the lists of jobs and other instructions to the cron Daemon (computer software), ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
AT&T Bell Laboratories
Nokia Bell Labs, originally named Bell Telephone Laboratories (1925–1984), then AT&T Bell Laboratories (1984–1996) and Bell Labs Innovations (1996–2007), is an American industrial research and scientific development company owned by multinational company Nokia. With headquarters located in Murray Hill, New Jersey, the company operates several laboratories in the United States and around the world. Researchers working at Bell Laboratories are credited with the development of radio astronomy, the transistor, the laser, the photovoltaic cell, the charge-coupled device (CCD), information theory, the Unix operating system, and the programming languages B, C, C++, S, SNOBOL, AWK, AMPL, and others. Nine Nobel Prizes have been awarded for work completed at Bell Laboratories. Bell Labs had its origin in the complex corporate organization of the Bell System telephone conglomerate. In the late 19th century, the laboratory began as the Western Electric Engineering Department, l ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Paul Vixie
Paul Vixie is an American computer scientist whose technical contributions include Domain Name System (DNS) protocol design and procedure, mechanisms to achieve operational robustness of DNS implementations, and significant contributions to open source software principles and methodology. He also created and launched the first successful commercial anti-spam service. He authored the standard UNIX system programs ''SENDS'', ''proxynet'', ''rtty'' and Vixie cron. At one point he ran his own consulting business, Vixie Enterprises. Career Vixie was a software engineer at Digital Equipment Corporation (DEC) from 1988 to 1993. After he left DEC in 1994, he founded Internet Software Consortium (ISC) in 1996 together with Rick Adams and Carl Malamud to support BIND and other software for the Internet. The activities of ISC were assumed by a new company, Internet Systems Consortium in 2004. Although ISC operates the F root name server, Vixie at one point joined the Open Root Server Netw ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Discrete Event Simulation
A discrete-event simulation (DES) models the operation of a system as a (discrete) sequence of events in time. Each event occurs at a particular instant in time and marks a change of state in the system. Between consecutive events, no change in the system is assumed to occur; thus the simulation time can directly jump to the occurrence time of the next event, which is called next-event time progression. In addition to next-event time progression, there is also an alternative approach, called incremental time progression, where time is broken up into small time slices and the system state is updated according to the set of events/activities happening in the time slice. Because not every time slice has to be simulated, a next-event time simulation can typically run faster than a corresponding incremental time simulation. Both forms of DES contrast with continuous simulation in which the system state is changed continuously over time on the basis of a set of differential equations def ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Analysis Of Algorithms
In computer science, the analysis of algorithms is the process of finding the computational complexity of algorithms—the amount of time, storage, or other resources needed to execute them. Usually, this involves determining a function that relates the size of an algorithm's input to the number of steps it takes (its time complexity) or the number of storage locations it uses (its space complexity). An algorithm is said to be efficient when this function's values are small, or grow slowly compared to a growth in the size of the input. Different inputs of the same size may cause the algorithm to have different behavior, so best, worst and average case descriptions might all be of practical interest. When not otherwise specified, the function describing the performance of an algorithm is usually an upper bound, determined from the worst case inputs to the algorithm. The term "analysis of algorithms" was coined by Donald Knuth. Algorithm analysis is an important part of a broader ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Communications Of The ACM
''Communications of the ACM'' is the monthly journal of the Association for Computing Machinery (ACM). It was established in 1958, with Saul Rosen as its first managing editor. It is sent to all ACM members. Articles are intended for readers with backgrounds in all areas of computer science and information systems. The focus is on the practical implications of advances in information technology and associated management issues; ACM also publishes a variety of more theoretical journals. The magazine straddles the boundary of a science magazine, trade magazine, and a scientific journal. While the content is subject to peer review, the articles published are often summaries of research that may also be published elsewhere. Material published must be accessible and relevant to a broad readership. From 1960 onward, ''CACM'' also published algorithms, expressed in ALGOL. The collection of algorithms later became known as the Collected Algorithms of the ACM. See also * ''Journal of the A ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Instructions Per Second
Instructions per second (IPS) is a measure of a computer's processor speed. For complex instruction set computers (CISCs), different instructions take different amounts of time, so the value measured depends on the instruction mix; even for comparing processors in the same family the IPS measurement can be problematic. Many reported IPS values have represented "peak" execution rates on artificial instruction sequences with few branches and no cache contention, whereas realistic workloads typically lead to significantly lower IPS values. Memory hierarchy also greatly affects processor performance, an issue barely considered in IPS calculations. Because of these problems, synthetic benchmarks such as Dhrystone are now generally used to estimate computer performance in commonly used applications, and raw IPS has fallen into disuse. The term is commonly used in association with a metric prefix (k, M, G, T, P, or E) to form kilo instructions per second (kIPS), million instructions p ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
UNIX System V
Unix System V (pronounced: "System Five") is one of the first commercial versions of the Unix operating system. It was originally developed by AT&T and first released in 1983. Four major versions of System V were released, numbered 1, 2, 3, and 4. System V Release 4 (SVR4) was commercially the most successful version, being the result of an effort, marketed as ''Unix System Unification'', which solicited the collaboration of the major Unix vendors. It was the source of several common commercial Unix features. System V is sometimes abbreviated to SysV. , the AT&T-derived Unix market is divided between four System V variants: IBM's AIX, Hewlett Packard Enterprise's HP-UX and Oracle's Solaris, plus the free-software illumos forked from OpenSolaris. Overview Introduction System V was the successor to 1982's UNIX System III. While AT&T developed and sold hardware that ran System V, most customers ran a version from a reseller, based on AT&T's reference implementation. A s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Purdue University
Purdue University is a public land-grant research university in West Lafayette, Indiana, and the flagship campus of the Purdue University system. The university was founded in 1869 after Lafayette businessman John Purdue donated land and money to establish a college of science, technology, and agriculture in his name. The first classes were held on September 16, 1874, with six instructors and 39 students. It has been ranked as among the best public universities in the United States by major institutional rankings, and is renowned for its engineering program. The main campus in West Lafayette offers more than 200 majors for undergraduates, over 70 masters and doctoral programs, and professional degrees in pharmacy, veterinary medicine, and doctor of nursing practice. In addition, Purdue has 18 intercollegiate sports teams and more than 900 student organizations. Purdue is the founding member of the Big Ten Conference and enrolls the largest student body of any individual univer ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Superuser
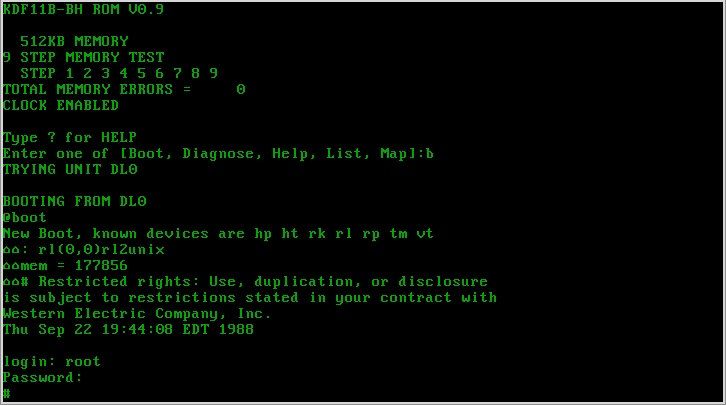
In computing, the superuser is a special user account used for system administration. Depending on the operating system (OS), the actual name of this account might be root, administrator, admin or supervisor. In some cases, the actual name of the account is not the determining factor; on Unix-like systems, for example, the user with a user identifier (UID) of zero is the superuser, regardless of the name of that account; and in systems which implement a role based security model, any user with the role of superuser (or its synonyms) can carry out all actions of the superuser account. The principle of least privilege recommends that most users and applications run under an ordinary account to perform their work, as a superuser account is capable of making unrestricted, potentially adverse, system-wide changes. Unix and Unix-like In Unix-like computer OSes (such as Linux), ''root'' is the conventional name of the user who has all rights or permissions (to all files and programs) i ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Algorithm
In mathematics and computer science, an algorithm () is a finite sequence of rigorous instructions, typically used to solve a class of specific Computational problem, problems or to perform a computation. Algorithms are used as specifications for performing calculations and data processing. More advanced algorithms can perform automated deductions (referred to as automated reasoning) and use mathematical and logical tests to divert the code execution through various routes (referred to as automated decision-making). Using human characteristics as descriptors of machines in metaphorical ways was already practiced by Alan Turing with terms such as "memory", "search" and "stimulus". In contrast, a Heuristic (computer science), heuristic is an approach to problem solving that may not be fully specified or may not guarantee correct or optimal results, especially in problem domains where there is no well-defined correct or optimal result. As an effective method, an algorithm ca ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Daemon (computing)
In computer multitasking, multitasking computer operating systems, a daemon ( or ) is a computer program that runs as a background process, rather than being under the direct control of an interactive user. Traditionally, the process names of a daemon end with the letter ''d'', for clarification that the process is in fact a daemon, and for differentiation between a daemon and a normal computer program. For example, is a daemon that implements system logging facility, and is a daemon that serves incoming Secure Shell, SSH connections. In a Unix environment, the parent process of a daemon is often, but not always, the init process. A daemon is usually created either by a process Fork (operating system), forking a child process and then immediately exiting, thus causing init to adopt the child process, or by the init process directly launching the daemon. In addition, a daemon launched by forking and exiting typically must perform other operations, such as dissociating the proce ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Version 7 Unix
Seventh Edition Unix, also called Version 7 Unix, Version 7 or just V7, was an important early release of the Unix operating system. V7, released in 1979, was the last Bell Laboratories release to see widespread distribution before the commercialization of Unix by AT&T Corporation in the early 1980s. V7 was originally developed for Digital Equipment Corporation's PDP-11 minicomputers and was later ported to other platforms. Overview Unix versions from Bell Labs were designated by the edition of the user's manual with which they were accompanied. Released in 1979, the Seventh Edition was preceded by Sixth Edition, which was the first version licensed to commercial users. Development of the Research Unix line continued with the Eighth Edition, which incorporated development from 4.1BSD, through the Tenth Edition, after which the Bell Labs researchers concentrated on developing Plan 9. V7 was the first readily portable version of Unix. As this was the era of minicomputers, with ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |