|
Bifid Cipher
In classical cryptography, the bifid cipher is a cipher which combines the Polybius square with transposition, and uses fractionation to achieve diffusion. It was invented around 1901 by Felix Delastelle. Operation First, a mixed alphabet Polybius square is drawn up, where the I and the J share their position: 1 2 3 4 5 1 B G W K Z 2 Q P N D S 3 I O A X E 4 F C L U M 5 T H Y V R The message is converted to its coordinates in the usual manner, but they are written vertically beneath: F L E E A T O N C E 4 4 3 3 3 5 3 2 4 3 1 3 5 5 3 1 2 3 2 5 They are then read out in rows: 4 4 3 3 3 5 3 2 4 3 1 3 5 5 3 1 2 3 2 5 Then divided up into pairs again, and the pairs turned back into letters using the square: 44 33 35 32 43 13 55 31 23 25 U A E O L W R I N S In this way, each ciphertext character depends on two plaintext characters, so the bifid is a digraphic cipher, like the Playfair cipher. To decrypt, the procedure is simply reversed. Longer messages are fir ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
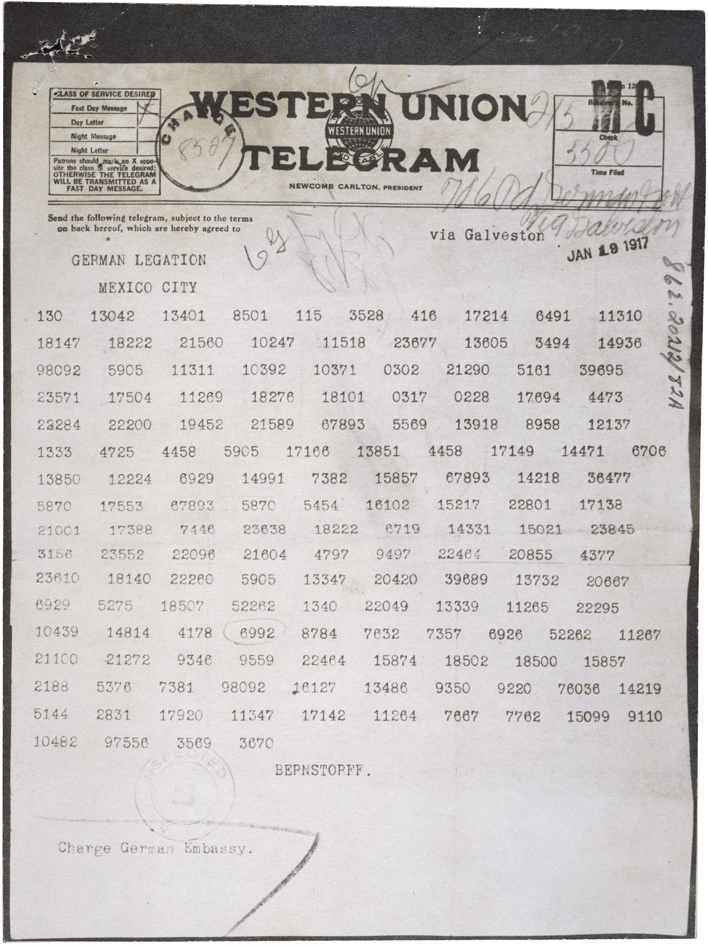
Cryptography
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security ( data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. Cryptography prior to the modern age was effectively synonymo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
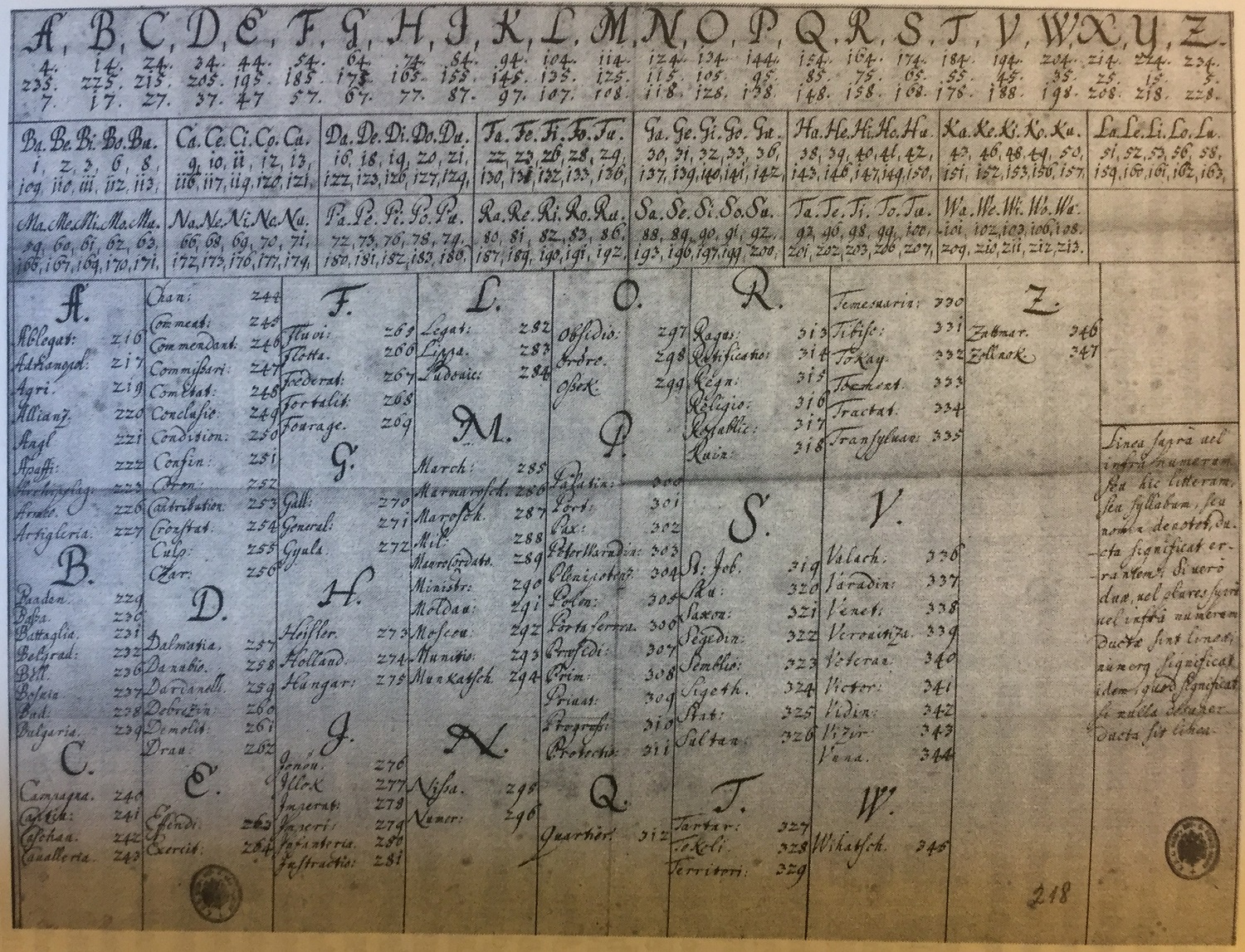
Polybius Square
The Polybius square, also known as the Polybius checkerboard, is a device invented by the ancient Greeks Cleoxenus and Democleitus, and made famous by the historian and scholar Polybius. The device is used for fractionating plaintext characters so that they can be represented by a smaller set of symbols, which is useful for telegraphy, steganography, and cryptography. The device was originally used for fire signalling, allowing for the coded transmission of any message, not just a finite amount of predetermined options as was the convention before. Basic form According to Polybius' ''Histories,'' the device was invented by Cleoxenus and Democleitus, and further developed by Polybius himself. The device partitioned the alphabet into five tablets with five letters each (except for the last one with only four). There are no surviving tablets from antiquity. Letters are represented by two numbers from one to five, allowing the representation of 25 characters using only 5 numeric sym ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Transposition Cipher
In cryptography, a transposition cipher is a method of encryption which scrambles the positions of characters (''transposition'') without changing the characters themselves. Transposition ciphers reorder units of plaintext (typically characters or groups of characters) according to a regular system to produce a ciphertext which is a permutation of the plaintext. They differ from substitution ciphers, which do not change the position of units of plaintext but instead change the units themselves. Despite the difference between transposition and substitution operations, they are often combined, as in historical ciphers like the ADFGVX cipher or complex high-quality encryption methods like the modern Advanced Encryption Standard (AES). General principle Plaintexts can be rearranged into a ciphertext using a key, scrambling the order of characters like the shuffled pieces of a jigsaw puzzle. The resulting message is hard to decipher without the key because there are many ways the char ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Confusion And Diffusion
In cryptography, confusion and diffusion are two properties of the operation of a secure cipher identified by Claude Shannon in his 1945 classified report ''A Mathematical Theory of Cryptography'.'' These properties, when present, work to thwart the application of statistics and other methods of cryptanalysis. These concepts are also important in the design of secure hash functions and pseudorandom number generators where decorrelation of the generated values is the main feature. Definition Confusion Confusion means that each binary digit (bit) of the ciphertext should depend on several parts of the key, obscuring the connections between the two. The property of confusion hides the relationship between the ciphertext and the key. This property makes it difficult to find the key from the ciphertext and if a single bit in a key is changed, the calculation of most or all of the bits in the ciphertext will be affected. Confusion increases the ambiguity of ciphertext and it is ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Felix Delastelle
Felix may refer to: * Felix (name), people and fictional characters with the name Places * Arabia Felix is the ancient Latin name of Yemen * Felix, Spain, a municipality of the province Almería, in the autonomous community of Andalusia, Spain * St. Felix, Prince Edward Island, a rural community in Prince County, Prince Edward Island, Canada. * Felix, Ontario, an unincorporated place and railway point in Northeastern Ontario, Canada * St. Felix, South Tyrol, a village in South Tyrol, in northern Italy. * Felix, California, an unincorporated community in Calaveras County Music * Felix (band), a British band * Felix (musician), British DJ * Félix Award, a Quebec music award named after Félix Leclerc Business * Felix (pet food), a brand of cat food sold in most European countries * AB Felix, a Swedish food company * Felix Bus Services of Derbyshire, England * Felix Airways, an airline based in Yemen Science and technology * Apache Felix, an open source OSGi framewor ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Substitution Cipher
In cryptography, a substitution cipher is a method of encrypting in which units of plaintext are replaced with the ciphertext, in a defined manner, with the help of a key; the "units" may be single letters (the most common), pairs of letters, triplets of letters, mixtures of the above, and so forth. The receiver deciphers the text by performing the inverse substitution process to extract the original message. Substitution ciphers can be compared with transposition ciphers. In a transposition cipher, the units of the plaintext are rearranged in a different and usually quite complex order, but the units themselves are left unchanged. By contrast, in a substitution cipher, the units of the plaintext are retained in the same sequence in the ciphertext, but the units themselves are altered. There are a number of different types of substitution cipher. If the cipher operates on single letters, it is termed a simple substitution cipher; a cipher that operates on larger groups of letters ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cartesian Coordinate System
A Cartesian coordinate system (, ) in a plane is a coordinate system that specifies each point uniquely by a pair of numerical coordinates, which are the signed distances to the point from two fixed perpendicular oriented lines, measured in the same unit of length. Each reference coordinate line is called a ''coordinate axis'' or just ''axis'' (plural ''axes'') of the system, and the point where they meet is its ''origin'', at ordered pair . The coordinates can also be defined as the positions of the perpendicular projections of the point onto the two axes, expressed as signed distances from the origin. One can use the same principle to specify the position of any point in three-dimensional space by three Cartesian coordinates, its signed distances to three mutually perpendicular planes (or, equivalently, by its perpendicular projection onto three mutually perpendicular lines). In general, ''n'' Cartesian coordinates (an element of real ''n''-space) specify the point in an ' ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Ciphertext
In cryptography, ciphertext or cyphertext is the result of encryption performed on plaintext using an algorithm, called a cipher. Ciphertext is also known as encrypted or encoded information because it contains a form of the original plaintext that is unreadable by a human or computer without the proper cipher to decrypt it. This process prevents the loss of sensitive information via hacking. Decryption, the inverse of encryption, is the process of turning ciphertext into readable plaintext. Ciphertext is not to be confused with codetext because the latter is a result of a code, not a cipher. Conceptual underpinnings Let m\! be the plaintext message that Alice wants to secretly transmit to Bob and let E_k\! be the encryption cipher, where _k\! is a cryptographic key. Alice must first transform the plaintext into ciphertext, c\!, in order to securely send the message to Bob, as follows: : c = E_k(m). \! In a symmetric-key system, Bob knows Alice's encryption key. Once the m ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Plaintext
In cryptography, plaintext usually means unencrypted information pending input into cryptographic algorithms, usually encryption algorithms. This usually refers to data that is transmitted or stored unencrypted. Overview With the advent of computing, the term ''plaintext'' expanded beyond human-readable documents to mean any data, including binary files, in a form that can be viewed or used without requiring a key or other decryption device. Information—a message, document, file, etc.—if to be communicated or stored in an unencrypted form is referred to as plaintext. Plaintext is used as input to an encryption algorithm; the output is usually termed ciphertext, particularly when the algorithm is a cipher. Codetext is less often used, and almost always only when the algorithm involved is actually a code. Some systems use multiple layers of encryption, with the output of one encryption algorithm becoming "plaintext" input for the next. Secure handling Insecure handling of p ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Playfair Cipher
The Playfair cipher or Playfair square or Wheatstone–Playfair cipher is a manual symmetric encryption technique and was the first literal digram substitution cipher. The scheme was invented in 1854 by Charles Wheatstone, but bears the name of Lord Playfair for promoting its use. The technique encrypts pairs of letters (''bigrams'' or ''digrams''), instead of single letters as in the simple substitution cipher and rather more complex Vigenère cipher systems then in use. The Playfair is thus significantly harder to break since the frequency analysis used for simple substitution ciphers does not work with it. The frequency analysis of bigrams is possible, but considerably more difficult. With 600 possible bigrams rather than the 26 possible monograms (single symbols, usually letters in this context), a considerably larger cipher text is required in order to be useful. History The Playfair cipher was the first cipher to encrypt pairs of letters in cryptologic history. Wheat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Four-square Cipher
The four-square cipher is a manual symmetric encryption technique. It was invented by the French cryptographer Felix Delastelle. The technique encrypts pairs of letters (''digraphs''), and thus falls into a category of ciphers known as polygraphic substitution ciphers. This adds significant strength to the encryption when compared with monographic substitution ciphers which operate on single characters. The use of digraphs makes the four-square technique less susceptible to frequency analysis attacks, as the analysis must be done on 676 possible digraphs rather than just 26 for monographic substitution. The frequency analysis of digraphs is possible, but considerably more difficult - and it generally requires a much larger ciphertext in order to be useful. Using four-square The four-square cipher uses four 5 by 5 (5x5) matrices arranged in a square. Each of the 5 by 5 matrices contains the letters of the alphabet (usually omitting "Q" or putting both "I" and "J" in the same ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Trifid Cipher
The trifid cipher is a classical cipher invented by Félix Delastelle and described in 1902. Extending the principles of Delastelle's earlier bifid cipher, it combines the techniques of fractionation and transposition to achieve a certain amount of confusion and diffusion: each letter of the ciphertext depends on three letters of the plaintext and up to three letters of the key. The trifid cipher uses a table to ''fractionate'' each plaintext letter into a trigram, mixes the constituents of the trigrams, and then applies the table in reverse to turn these mixed trigrams into ciphertext letters. Delastelle notes that the most practical system uses three symbols for the trigrams:In order to split letters into three parts, it is necessary to represent them by a group of three signs or numbers. Knowing that ''n'' objects, combined in trigrams in all possible ways, give ''n'' × ''n'' × ''n'' = ''n''3, we recognize that three is the only value for ''n''; two would only give 23 = ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |


.png)