|
Broadcasting (computing)
In computer networking, telecommunication and information theory, broadcasting is a method of transferring a message to all recipients simultaneously. Broadcasting can be performed as a high-level operation in a program, for example, broadcasting in Message Passing Interface, or it may be a low-level networking operation, for example broadcasting on Ethernet. All-to-all communication is a computer communication method in which each sender Message passing, transmits messages to all receivers within a group. In networking this can be accomplished using broadcast or multicast. This is in contrast with the Point-to-point (telecommunications), point-to-point method in which each sender communicates with one receiver. Addressing methods There are four principal addressing methods in the Internet Protocol: Overview In computer networking, broadcasting refers to transmitting a packet (information technology), packet that will be received by every device on the network. In practice, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Broadcast
Broadcasting is the data distribution, distribution of sound, audio audiovisual content to dispersed audiences via a electronic medium (communication), mass communications medium, typically one using the electromagnetic spectrum (radio waves), in a :wikt:one-to-many, one-to-many model. Broadcasting began with AM radio, which came into popular use around 1920 with the spread of vacuum tube radio transmitters and radio receiver, receivers. Before this, most implementations of electronic communication (early radio, telephone, and telegraph) were wikt:one-to-one, one-to-one, with the message intended for a single recipient. The term ''broadcasting'' evolved from its use as the agricultural method of sowing seeds in a field by casting them broadly about. It was later adopted for describing the widespread distribution of information by printed materials or by telegraph. Examples applying it to "one-to-many" radio transmissions of an individual station to multiple listeners appeared as ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IPv4
Internet Protocol version 4 (IPv4) is the first version of the Internet Protocol (IP) as a standalone specification. It is one of the core protocols of standards-based internetworking methods in the Internet and other packet-switched networks. IPv4 was the first version deployed for production on SATNET in 1982 and on the ARPANET in January 1983. It is still used to route most Internet traffic today, even with the ongoing deployment of Internet Protocol version 6 (IPv6), its successor. IPv4 uses a 32-bit address space which provides 4,294,967,296 (232) unique addresses, but large blocks are reserved for special networking purposes. Purpose The Internet Protocol ("IP") is the protocol that defines and enables internetworking at the internet layer of the Internet Protocol Suite. It gives the Internet a global-scale logical addressing system which allows the routing of IP Network packet, data packets from a source host to the next router that is one Hop (networking), hop closer t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Terminating Reliable Broadcast
Terminating Reliable Broadcast (TRB) is a problem in distributed computing Distributed computing is a field of computer science that studies distributed systems, defined as computer systems whose inter-communicating components are located on different networked computers. The components of a distributed system commu ... that encapsulates the task of ''broadcasting'' a message to a set of receiving processes in the presence of ''faults''. In particular, the sender and any other process might fail ("crash") at any time. Problem description A TRB protocol typically organizes the system into a sending process and a set of receiving processes, which may include the sender itself. A process is called "correct" if it does not fail at any point during its execution. The goal of the protocol is to transfer data (the "message") from the sender to the set of receiving processes. A process may perform many I/O operations during protocol execution, but eventually "delivers" a message ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Point-to-multipoint Communication
In telecommunications, point-to-multipoint communication (P2MP, PTMP or PMP) is communication which is accomplished via a distinct type of one-to-many connection, providing multiple paths from a single location to multiple locations. Point-to-multipoint telecommunications is typically used in wireless Internet and IP telephony via gigahertz radio frequencies. P2MP systems have been designed with and without a return channel from the multiple receivers. A central antenna or antenna array broadcasts to several receiving antennas and the system uses a form of time-division multiplexing to allow for the return channel traffic. Modern point-to-multipoint links In contemporary usage, the term point-to-multipoint wireless communications relates to fixed wireless data communications for Internet or voice over IP via radio or microwave frequencies in the gigahertz range. Point-to-multipoint is the most popular approach for wireless communications that have a large number of n ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
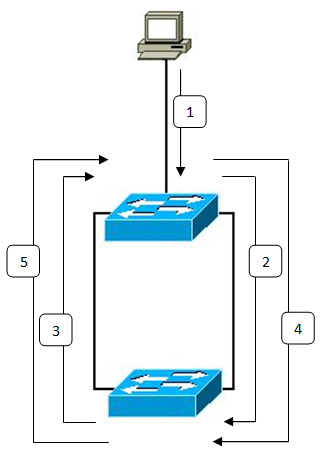
Broadcast Radiation
A broadcast storm or broadcast radiation is the accumulation of Broadcasting (networking), broadcast and multicast traffic on a computer network. Extreme amounts of broadcast traffic constitute a ''broadcast storm''. It can consume sufficient network resources so as to render the network unable to transport normal traffic. A Network packet, packet that induces such a storm is occasionally nicknamed a Chernobyl packet. Causes Most commonly the cause is a switching loop in the Ethernet network topology (i.e. two or more paths exist between switches). A simple example is both ends of a single Ethernet patch cable connected to a switch. As broadcasts and multicasts are forwarded by switches out of every Computer port (hardware), port, the switch or switches will repeatedly rebroadcast broadcast messages and flood the network. Since the layer-2 header does not support a time to live (TTL) value, if a Frame (networking), frame is sent into a looped topology, it can loop forever. In s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Smurf Attack
A Smurf attack is a distributed denial-of-service attack in which large numbers of Internet Control Message Protocol (ICMP) packets with the intended victim's spoofed source IP are broadcast to a computer network using an IP broadcast address. Most devices on a network will, by default, respond to this by sending a reply to the source IP address. If the number of machines on the network that receive and respond to these packets is very large, the victim's computer will be flooded with traffic. This can slow down the victim's computer to the point where it becomes impossible to work on. History The original tool for creating a Smurf attack was written by Dan Moschuk (alias TFreak) in 1997. In the late 1990s, many IP networks would participate in Smurf attacks if prompted (that is, they would respond to ICMP requests sent to broadcast addresses). The name comes from the idea of very small, but numerous attackers overwhelming a much larger opponent (see Smurfs). Today, administra ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Denial-of-service Attack
In computing, a denial-of-service attack (DoS attack) is a cyberattack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to a network. Denial of service is typically accomplished by flooding the targeted machine or resource with superfluous requests in an attempt to overload systems and prevent some or all legitimate requests from being fulfilled. The range of attacks varies widely, spanning from inundating a server with millions of requests to slow its performance, overwhelming a server with a substantial amount of invalid data, to submitting requests with an illegitimate IP address. In a distributed denial-of-service attack (DDoS attack), the incoming traffic flooding the victim originates from many different sources. More sophisticated strategies are required to mitigate this type of attack; simply attempting to block a single source is insuffic ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IEEE 802
IEEE 802 is a family of Institute of Electrical and Electronics Engineers (IEEE) standards for local area networks (LANs), personal area networks (PANs), and metropolitan area networks (MANs). The IEEE 802 LAN/MAN Standards Committee (LMSC) maintains these standards. The IEEE 802 family of standards has had twenty-four members, numbered 802.1 through 802.24, with a working group of the LMSC devoted to each. However, not all of these working groups are currently active. The IEEE 802 standards are restricted to computer networks carrying variable-size packets, unlike cell relay networks, for example, in which data is transmitted in short, uniformly sized units called cells. Isochronous signal networks, in which data is transmitted as a steady stream of octet (computing), octets, or groups of octets, at regular time intervals, are also outside the scope of the IEEE 802 standards. The number 802 has no significance: it was simply the next number in the sequence that the IEEE used fo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Broadcast Address
A broadcast address is a network address used to transmit to all devices connected to a multiple-access communications network. A message sent to a broadcast address may be received by all network-attached hosts. In contrast, a multicast address is used to address a specific group of devices, and a unicast address is used to address a single device. For network layer communications, a broadcast address may be a specific IP address. At the data link layer on Ethernet networks, it is a specific MAC address. IP networking In Internet Protocol version 4 (IPv4) networks, broadcast addresses are special values in the host-identification part of an IP address. The all-ones value was established as the standard broadcast address for networks that support broadcast. This method of using the all-ones address was first proposed by R. Gurwitz and R. Hinden in 1982. The later introduction of subnets and Classless Inter-Domain Routing changed this slightly, so that the all-ones value b ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
IPv6
Internet Protocol version 6 (IPv6) is the most recent version of the Internet Protocol (IP), the communication protocol, communications protocol that provides an identification and location system for computers on networks and routes traffic across the Internet. IPv6 was developed by the Internet Engineering Task Force (IETF) to deal with the long-anticipated problem of IPv4 address exhaustion, and was intended to replace IPv4. In December 1998, IPv6 became a Draft Standard for the IETF, which subsequently ratified it as an Internet Standard on 14 July 2017. Devices on the Internet are assigned a unique IP address for identification and location definition. With the rapid growth of the Internet after commercialization in the 1990s, it became evident that far more addresses would be needed to connect devices than the 4,294,967,296 (232) IPv4 address space had available. By 1998, the IETF had formalized the successor protocol, IPv6 which uses 128-bit addresses, theoretically all ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Wide Area Network
A wide area network (WAN) is a telecommunications network that extends over a large geographic area. Wide area networks are often established with leased telecommunication circuits. Businesses, as well as schools and government entities, use wide area networks to relay data to staff, students, clients, buyers and suppliers from various locations around the world. In essence, this mode of telecommunication allows a business to effectively carry out its daily function regardless of location. The Internet may be considered a WAN. Many WANs are, however, built for one particular organization and are private. WANs can be separated from local area networks (LANs) in that the latter refers to physically proximal networks. Design options The textbook definition of a WAN is a computer network spanning regions, countries, or even the world. However, in terms of the application of communication protocols and concepts, it may be best to view WANs as computer networking technologies used ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |