|
Vectra Networks Inc.
Vectra AI, Inc. is a cybersecurity company headquartered in San Jose, California. History Vectra was founded in 2010 as TraceVector LLC in New York City and was incorporated in 2012 under the name Vectra Networks. Products The Cognito platform from Vectra provides continuous, automated threat surveillance designed to expose cyberattacks that actively spread inside networks. Threat behaviors and cyberattack techniques detected by Cognito include botnet command-and-control communications, botnet monetization, internal reconnaissance, lateral movement, and data theft, or exfiltration. Vectra offers three applications on the Cognito platform to address use cases: * Cognito Stream delivers enterprise-scale network metadata with security insights in Zeek format to data lakes and security information and event management (SIEM) applications without the complexity, constant tuning and scale limitation of open-source Zeek. * Cognito Recall gives security analysts a logical star ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Security
Information security, sometimes shortened to InfoSec, is the practice of protecting information by mitigating information risks. It is part of information risk management. It typically involves preventing or reducing the probability of unauthorized/inappropriate access to data, or the unlawful use, disclosure, disruption, deletion, corruption, modification, inspection, recording, or devaluation of information. It also involves actions intended to reduce the adverse impacts of such incidents. Protected information may take any form, e.g. electronic or physical, tangible (e.g. paperwork) or intangible (e.g. knowledge). Information security's primary focus is the balanced protection of the confidentiality, integrity, and availability of data (also known as the CIA triad) while maintaining a focus on efficient policy implementation, all without hampering organization productivity. This is largely achieved through a structured risk management process that involves: * identifying inform ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
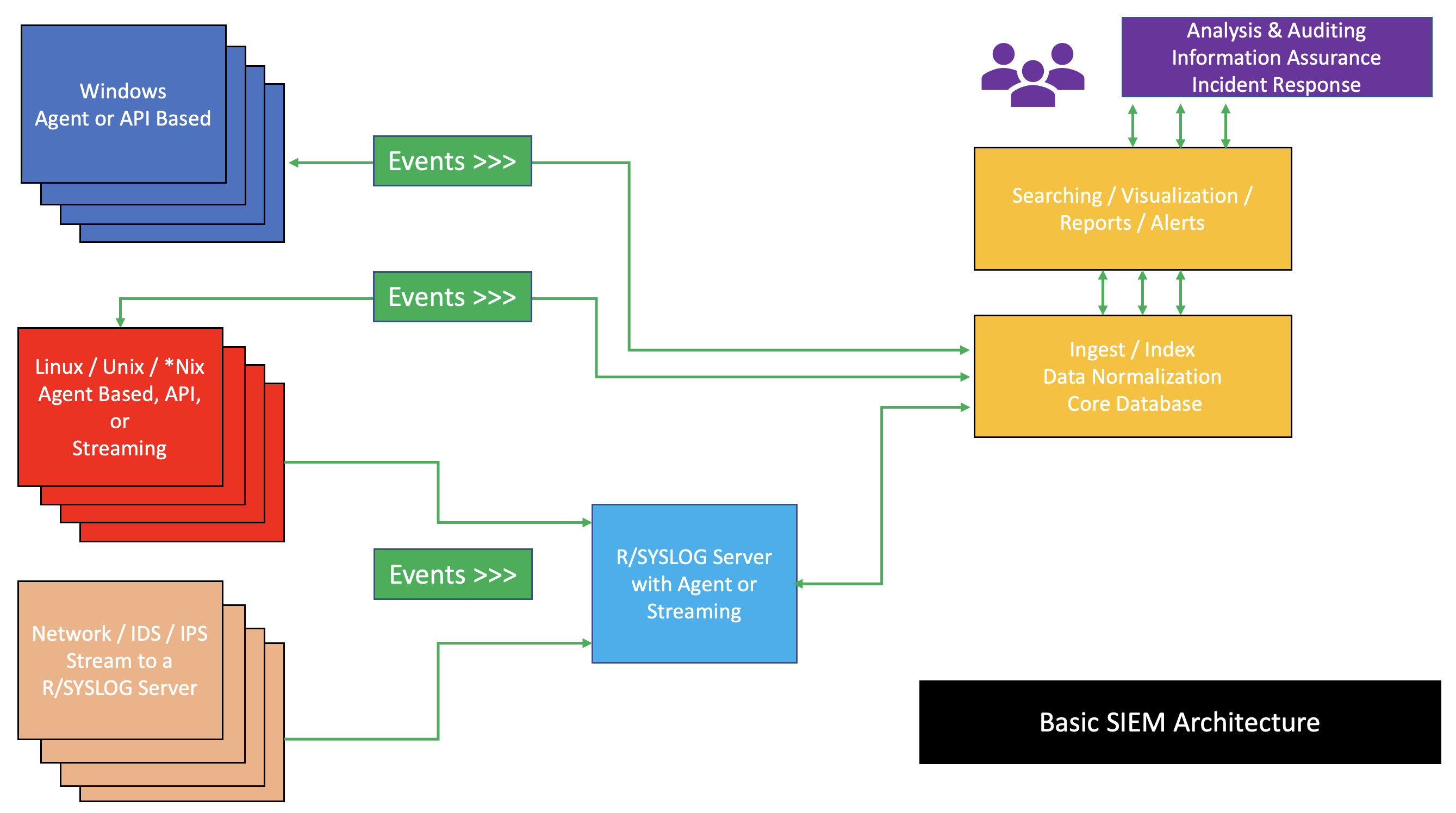
Security Information And Event Management
Security information and event management (SIEM) is a field within the field of computer security, where software products and services combine security information management (SIM) and security event management (SEM). They provide real-time analysis of security alerts generated by applications and network hardware. Vendors sell SIEM as software, as appliances, or as managed services; these products are also used to log security data and generate reports for compliance purposes. The term and the initialism SIEM was coined by Mark Nicolett and Amrit Williams of Gartner in 2005. History Monitoring system logs has grown more prevalent as complex cyber-attacks force compliance and regulatory mechanisms to mandate logging security controls within a Risk Management Framework. Logging levels of a system started with the primary function of troubleshooting system errors or debugging code compiled and run. As operating systems and networks have increased in complexity, so has the event ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Security Companies
A computer is a machine that can be programmed to carry out sequences of arithmetic or logical operations (computation) automatically. Modern digital electronic computers can perform generic sets of operations known as programs. These programs enable computers to perform a wide range of tasks. A computer system is a nominally complete computer that includes the hardware, operating system (main software), and peripheral equipment needed and used for full operation. This term may also refer to a group of computers that are linked and function together, such as a computer network or computer cluster. A broad range of industrial and consumer products use computers as control systems. Simple special-purpose devices like microwave ovens and remote controls are included, as are factory devices like industrial robots and computer-aided design, as well as general-purpose devices like personal computers and mobile devices like smartphones. Computers power the Internet, which links bil ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
American Companies Established In 2012
American(s) may refer to: * American, something of, from, or related to the United States of America, commonly known as the "United States" or "America" ** Americans, citizens and nationals of the United States of America ** American ancestry, people who self-identify their ancestry as "American" ** American English, the set of varieties of the English language native to the United States ** Native Americans in the United States, indigenous peoples of the United States * American, something of, from, or related to the Americas, also known as "America" ** Indigenous peoples of the Americas * American (word), for analysis and history of the meanings in various contexts Organizations * American Airlines, U.S.-based airline headquartered in Fort Worth, Texas * American Athletic Conference, an American college athletic conference * American Recordings (record label), a record label previously known as Def American * American University, in Washington, D.C. Sports teams Soccer * B ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Companies Based In San Jose, California
A company, abbreviated as co., is a legal entity representing an association of people, whether natural, legal or a mixture of both, with a specific objective. Company members share a common purpose and unite to achieve specific, declared goals. Companies take various forms, such as: * voluntary associations, which may include nonprofit organizations * business entities, whose aim is generating profit * financial entities and banks * programs or educational institutions A company can be created as a legal person so that the company itself has limited liability as members perform or fail to discharge their duty according to the publicly declared incorporation, or published policy. When a company closes, it may need to be liquidated to avoid further legal obligations. Companies may associate and collectively register themselves as new companies; the resulting entities are often known as corporate groups. Meanings and definitions A company can be defined as an "artificial per ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Application Programming Interface
An application programming interface (API) is a way for two or more computer programs to communicate with each other. It is a type of software interface, offering a service to other pieces of software. A document or standard that describes how to build or use such a connection or interface is called an ''API specification''. A computer system that meets this standard is said to ''implement'' or ''expose'' an API. The term API may refer either to the specification or to the implementation. In contrast to a user interface, which connects a computer to a person, an application programming interface connects computers or pieces of software to each other. It is not intended to be used directly by a person (the end user) other than a computer programmer who is incorporating it into the software. An API is often made up of different parts which act as tools or services that are available to the programmer. A program or a programmer that uses one of these parts is said to ''call'' that ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Network Access Control
Network access control (NAC) is an approach to computer security that attempts to unify endpoint security technology (such as antivirus, host intrusion prevention, and vulnerability assessment), user or system authentication and network security enforcement. Description Network access control is a computer networking solution that uses a set of protocols to define and implement a policy that describes how to secure access to network nodes by devices when they initially attempt to access the network. NAC might integrate the automatic remediation process (fixing non-compliant nodes before allowing access) into the network systems, allowing the network infrastructure such as routers, switches and firewalls to work together with back office servers and end user computing equipment to ensure the information system is operating securely before interoperability is allowed. A basic form of NAC is the 802.1X standard. Network access control aims to do exactly what the name implies— ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Endpoint Security
Endpoint security or endpoint protection is an approach to the protection of computer networks that are remotely bridged to client devices. The connection of endpoint devices such as laptops, tablets, mobile phones, Internet-of-things devices, and other wireless devices to corporate networks creates attack paths for security threats. Endpoint security attempts to ensure that such devices follow a definite level of compliance to standards. The endpoint security space has evolved during the 2010s away from limited antivirus software and into a more advanced, comprehensive defense. This includes next-generation antivirus, threat detection, investigation, and response, device management, data leak protection (DLP), and other considerations to face evolving threats. Corporate network security Endpoint security management is a software approach that helps to identify and manage the users' computer and data access over a corporate network. This allows the network administrator to re ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Firewall (computing)
In computing, a firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. A firewall typically establishes a barrier between a trusted network and an untrusted network, such as the Internet. History The term ''firewall'' originally referred to a wall intended to confine a fire within a line of adjacent buildings. Later uses refer to similar structures, such as the metal sheet separating the engine compartment of a vehicle or aircraft from the passenger compartment. The term was applied in the late 1980s to network technology that emerged when the Internet was fairly new in terms of its global use and connectivity. The predecessors to firewalls for network security were routers used in the late 1980s. Because they already segregated networks, routers could apply filtering to packets crossing them. Before it was used in real-life computing, the term appeared in the 1983 computer-hacking movie ' ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
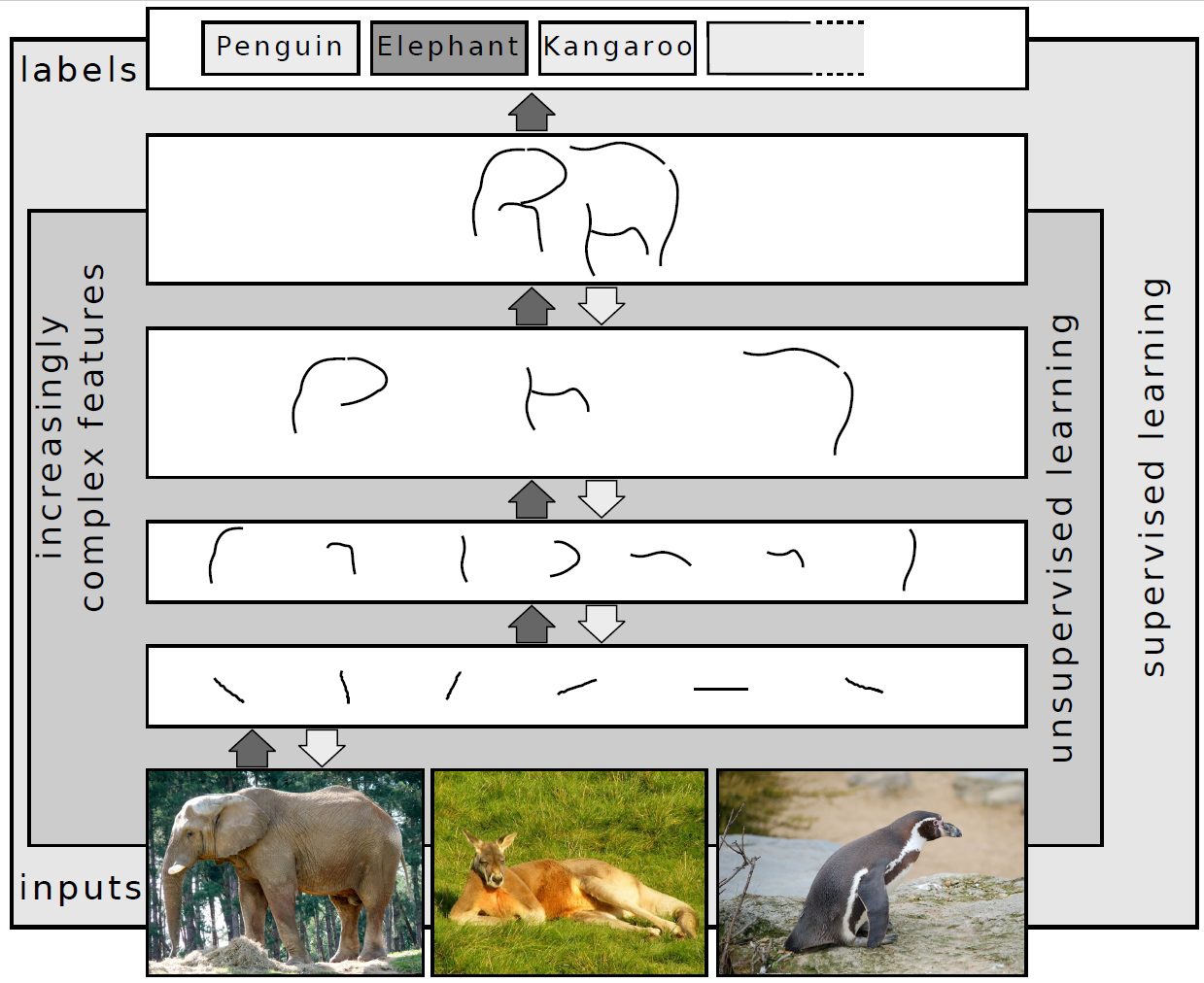
Deep Learning
Deep learning (also known as deep structured learning) is part of a broader family of machine learning methods based on artificial neural networks with representation learning. Learning can be supervised, semi-supervised or unsupervised. Deep-learning architectures such as deep neural networks, deep belief networks, deep reinforcement learning, recurrent neural networks, convolutional neural networks and Transformers have been applied to fields including computer vision, speech recognition, natural language processing, machine translation, bioinformatics, drug design, medical image analysis, Climatology, climate science, material inspection and board game programs, where they have produced results comparable to and in some cases surpassing human expert performance. Artificial neural networks (ANNs) were inspired by information processing and distributed communication nodes in biological systems. ANNs have various differences from biological brains. Specifically, artificial ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
San Jose, California
San Jose, officially San José (; ; ), is a major city in the U.S. state of California that is the cultural, financial, and political center of Silicon Valley and largest city in Northern California by both population and area. With a 2020 population of 1,013,240, it is the most populous city in both the Bay Area and the San Jose–San Francisco–Oakland, CA Combined Statistical Area, San Jose-San Francisco-Oakland Combined Statistical Area, which contain 7.7 million and 9.7 million people respectively, the List of largest California cities by population, third-most populous city in California (after Los Angeles and San Diego and ahead of San Francisco), and the List of United States cities by population, tenth-most populous in the United States. Located in the center of the Santa Clara Valley on the southern shore of San Francisco Bay, San Jose covers an area of . San Jose is the county seat of Santa Clara County, California, Santa Clara County and the main component of the San ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
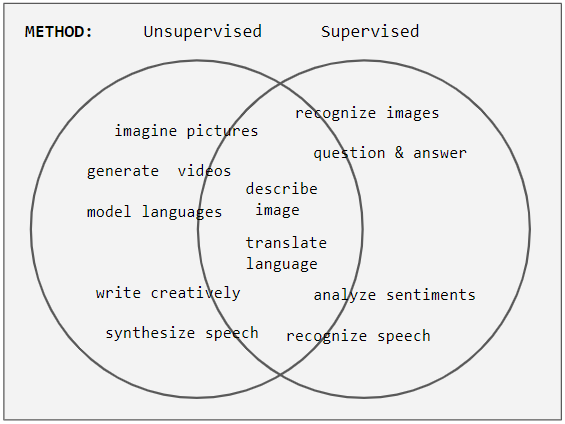
Unsupervised Machine Learning
Unsupervised learning is a type of algorithm that learns patterns from untagged data. The hope is that through mimicry, which is an important mode of learning in people, the machine is forced to build a concise representation of its world and then generate imaginative content from it. In contrast to supervised learning where data is tagged by an expert, e.g. tagged as a "ball" or "fish", unsupervised methods exhibit self-organization that captures patterns as probability densities or a combination of neural feature preferences encoded in the machine's weights and activations. The other levels in the supervision spectrum are reinforcement learning where the machine is given only a numerical performance score as guidance, and semi-supervised learning where a small portion of the data is tagged. Neural networks Tasks vs. methods Neural network tasks are often categorized as discriminative (recognition) or generative (imagination). Often but not always, discriminative tas ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |