|
User Activity Monitoring
In the field of information security, user activity monitoring (UAM) is the monitoring and recording of user actions. UAM captures user actions, including the use of applications, windows opened, system commands executed, checkboxes clicked, text entered/edited, URLs visited and nearly every other on-screen event to protect data by ensuring that employees and contractors are staying within their assigned tasks, and posing no risk to the organization. User activity monitoring software can deliver video-like playback of user activity and process the videos into user activity logs that keep step-by-step records of user actions that can be searched and analyzed to investigate any out-of-scope activities. Issues The need for UAM rose due to the increase in security incidents that directly or indirectly involve user credentials, exposing company information or sensitive files. In 2014, there were 761 data breaches in the United States, resulting in over 83 million exposed customer and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Security
Information security, sometimes shortened to InfoSec, is the practice of protecting information by mitigating information risks. It is part of information risk management. It typically involves preventing or reducing the probability of unauthorized/inappropriate access to data, or the unlawful use, disclosure, disruption, deletion, corruption, modification, inspection, recording, or devaluation of information. It also involves actions intended to reduce the adverse impacts of such incidents. Protected information may take any form, e.g. electronic or physical, tangible (e.g. paperwork) or intangible (e.g. knowledge). Information security's primary focus is the balanced protection of the confidentiality, integrity, and availability of data (also known as the CIA triad) while maintaining a focus on efficient policy implementation, all without hampering organization productivity. This is largely achieved through a structured risk management process that involves: * identifying inform ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
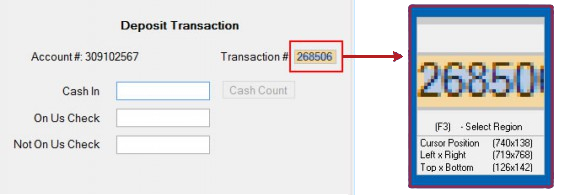
Screen Scraping
Data scraping is a technique where a computer program extracts data from human-readable output coming from another program. Description Normally, data transfer between programs is accomplished using data structures suited for automated processing by computers, not people. Such interchange formats and protocols are typically rigidly structured, well-documented, easily parsed, and minimize ambiguity. Very often, these transmissions are not human-readable at all. Thus, the key element that distinguishes data scraping from regular parsing is that the output being scraped is intended for display to an end-user, rather than as an input to another program. It is therefore usually neither documented nor structured for convenient parsing. Data scraping often involves ignoring binary data (usually images or multimedia data), display formatting, redundant labels, superfluous commentary, and other information which is either irrelevant or hinders automated processing. Data scraping is ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Security
National security, or national defence, is the security and defence of a sovereign state, including its citizens, economy, and institutions, which is regarded as a duty of government. Originally conceived as protection against military attack, national security is widely understood to include also non-military dimensions, including the security from terrorism, minimization of crime, economic security, energy security, environmental security, food security, and cyber-security. Similarly, national security risks include, in addition to the actions of other nation states, action by violent non-state actors, by narcotic cartels, and by multinational corporations, and also the effects of natural disasters. Governments rely on a range of measures, including political, economic, and military power, as well as diplomacy, to safeguard the security of a nation state. They may also act to build the conditions of security regionally and internationally by reducing transnational caus ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Crime Prevention
Crime prevention is the attempt to reduce and deter crime and criminals. It is applied specifically to efforts made by governments to reduce crime, enforce the law, and maintain criminal justice. Studies Criminologists, commissions, and research bodies such as the World Health Organization, United Nations, the United States National Research Council, the UK Audit Commission have analyzed their and others' research on what lowers rates of interpersonal crime. They agree that governments must go beyond law enforcement and criminal justice to tackle the risk factors that cause crime, because it is more cost effective and leads to greater social benefits than the standard ways of responding to crime. Multiple opinion polls also confirm public support for investment in prevention. Waller uses these materials in '' Less Law, More Order'' to propose specific measures to reduce crime as well as a crime bill. The ''World Health Organization Guide'' (2004) complements the ''World Report on ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Data Security
Data security means protecting digital data, such as those in a database, from destructive forces and from the unwanted actions of unauthorized users, such as a cyberattack or a data breach. Technologies Disk encryption Disk encryption refers to encryption technology that encrypts data on a hard disk drive. Disk encryption typically takes form in either software (see disk encryption software) or hardware (see disk encryption hardware). Disk encryption is often referred to as on-the-fly encryption (OTFE) or transparent encryption. Software versus hardware-based mechanisms for protecting data Software-based security solutions encrypt the data to protect it from theft. However, a malicious program or a hacker could corrupt the data to make it unrecoverable, making the system unusable. Hardware-based security solutions prevent read and write access to data, which provides very strong protection against tampering and unauthorized access. Hardware-based security or assiste ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
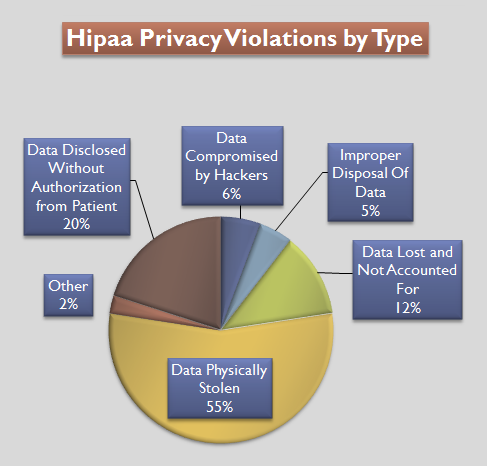
Health Insurance Portability And Accountability Act
The Health Insurance Portability and Accountability Act of 1996 (HIPAA or the Kennedy– Kassebaum Act) is a United States Act of Congress enacted by the 104th United States Congress and signed into law by President Bill Clinton on August 21, 1996. It modernized the flow of healthcare information, stipulates how personally identifiable information maintained by the healthcare and healthcare insurance industries should be protected from fraud and theft, and addressed some limitations on healthcare insurance coverage. It generally prohibits healthcare providers and healthcare businesses, called ''covered entities'', from disclosing protected information to anyone other than a patient and the patient's authorized representatives without their consent. With limited exceptions, it does not restrict patients from receiving information about themselves. It does not prohibit patients from voluntarily sharing their health information however they choose, nor does it require confidential ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Regulatory Compliance
In general, compliance means conforming to a rule, such as a specification, policy, standard or law. Compliance has traditionally been explained by reference to the deterrence theory, according to which punishing a behavior will decrease the violations both by the wrongdoer (specific deterrence) and by others (general deterrence). This view has been supported by economic theory, which has framed punishment in terms of costs and has explained compliance in terms of a cost-benefit equilibrium (Becker 1968). However, psychological research on motivation provides an alternative view: granting rewards (Deci, Koestner and Ryan, 1999) or imposing fines (Gneezy Rustichini 2000) for a certain behavior is a form of extrinsic motivation that weakens intrinsic motivation and ultimately undermines compliance. Regulatory compliance describes the goal that organizations aspire to achieve in their efforts to ensure that they are aware of and take steps to comply with relevant laws, policies, and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Session Replay
Session replay is the ability to replay a visitor's journey on a web site or within a mobile application or web application. Replay can include the user's view (browser or screen output), user input (keyboard and mouse inputs), and logs of network events or console logs. Session replay is supposed to help improve customer experience and help identify obstacles in conversion processes on websites. However, it can also be used to study a website's usability, customer behavior, and the handling of customer service questions as the customer journey, with all interactions, can be replayed. Some organizations also use this capability to analyse fraudulent behavior on websites. Some solutions augment the session replay with advanced analytics that can identify segments of customers that are struggling to use the website. This allows for the replay capability to be used much more efficiently and reduces the need to replay other customer sessions unnecessarily. There are generally tw ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Citrix
Citrix Systems, Inc. is an American multinational cloud computing and virtualization technology company that provides server, application and desktop virtualization, networking, software as a service (SaaS), and cloud computing technologies. Citrix products were claimed to be in use by over 400,000 clients worldwide, including 99% of the Fortune 100, and 98% of the Fortune 500. The company was founded in Richardson, Texas in 1989 by Ed Iacobucci, who served as chairman until his departure in 2000. It began by developing remote access products for Microsoft operating systems, licensing source code from Microsoft, and has been in partnership with the company throughout its history. By the 1990s, Citrix came to prominence as an industry leader in thin client technology, enabling purpose-built devices to access remote servers and resources. The company launched its first initial public offering in 1995 and, with few competitors, experienced large revenue increases between 1995 and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Data Breach
A data breach is a security violation, in which sensitive, protected or confidential data is copied, transmitted, viewed, stolen or used by an individual unauthorized to do so. Other terms are unintentional information disclosure, data leak, information leakage and data spill. Incidents range from concerted attacks by individuals who hack for personal gain or malice ( black hats), organized crime, political activists or national governments, to poorly configured system security or careless disposal of used computer equipment or data storage media. Leaked information can range from matters compromising national security, to information on actions which a government or official considers embarrassing and wants to conceal. A deliberate data breach by a person privy to the information, typically for political purposes, is more often described as a "leak". Data breaches may involve financial information such as credit card and debit card details, bank details, personal health info ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Database
In computing, a database is an organized collection of data stored and accessed electronically. Small databases can be stored on a file system, while large databases are hosted on computer clusters or cloud storage. The design of databases spans formal techniques and practical considerations, including data modeling, efficient data representation and storage, query languages, security and privacy of sensitive data, and distributed computing issues, including supporting concurrent access and fault tolerance. A database management system (DBMS) is the software that interacts with end users, applications, and the database itself to capture and analyze the data. The DBMS software additionally encompasses the core facilities provided to administer the database. The sum total of the database, the DBMS and the associated applications can be referred to as a database system. Often the term "database" is also used loosely to refer to any of the DBMS, the database system or an appli ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
User Behavior Analytics
User behavior analytics (UBA) is a cybersecurity process regarding the detection of insider threats, targeted attacks, and financial fraud that tracks a system's users. UBA looks at patterns of human behavior, and then analyzes observations to detect anomalies that may indicate potential threats. Purpose The purpose of UBA, according to Johna Till Johnson of Nemertes Research, is that "Security systems provide so much information that it's tough to uncover information that truly indicates a potential for real attack. Analytics tools help make sense of the vast amount of data that SIEM, IDS/IPS, system logs, and other tools gather. UBA tools use a specialized type of security analytics that focuses on the behavior of systems and the people using them. UBA technology first evolved in the field of marketing, to help companies understand and predict consumer-buying patterns. But as it turns out, UBA can be extraordinarily useful in the security context too." [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |