|
Traitor Tracing
Traitor tracing schemes help trace the source of leaks when secret or proprietary data is sold to many customers. In a traitor tracing scheme, each customer is given a different personal decryption key. (Traitor tracing schemes are often combined with conditional access systems so that, once the traitor tracing algorithm identifies a personal decryption key associated with the leak, the content distributor can revoke that personal decryption key, allowing honest customers to continue to watch pay television while the traitor and all the unauthorized users using the traitor's personal decryption key are cut off.) Traitor tracing schemes are used in pay television to discourage pirate decryption – to discourage legitimate subscribers from giving away decryption keys. Traitor tracing schemes are ineffective if the traitor rebroadcasts the entire (decrypted) original content. There are other kinds of schemes that discourages pirate rebroadcast – i.e., discourages legitimate subscr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Conditional Access
Conditional access (CA) is a term commonly used in relation to software and to digital television systems. Conditional access is that ‘just-in-time’ evaluation to ensure the person who is seeking access to content is authorized to access the content. Said another way, conditional access is a type of access management. Access is managed is by requiring certain criteria to be met before granting access to the content. In software Conditional access is a function that lets you manage people’s access to the software in question, such as email, applications, and documents. It is usually offered as SaaS (Software-as-a-Service) and deployed in organizations to keep company data safe. By setting conditions on the access to this data, the organization has more control over who accesses the data and where and in what way the information is accessed. When setting up conditional access, access can be limited to or prevented based on the policy defined by the system administrator. For ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Serial Number
A serial number is a unique identifier assigned incrementally or sequentially to an item, to ''uniquely'' identify it. Serial numbers need not be strictly numerical. They may contain letters and other typographical symbols, or may consist entirely of a character string. Applications of serial numbering Serial numbers identify otherwise identical individual units, thereby serving various practical uses. Serial numbers are a deterrent against theft and counterfeit products, as they can be recorded, and stolen or otherwise irregular goods can be identified. Banknotes and other transferable documents of value bear serial numbers to assist in preventing counterfeiting and tracing stolen ones. They are valuable in quality control, as once a defect is found in the production of a particular batch of product, the serial number will identify which units are affected. Some items with serial numbers are automobiles, firearms, electronics, and appliances. Smartphones and other S ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Applications Of Cryptography
Application may refer to: Mathematics and computing * Application software, computer software designed to help the user to perform specific tasks ** Application layer, an abstraction layer that specifies protocols and interface methods used in a communications network * Function application, in mathematics and computer science Processes and documents * Application for employment, a form or forms that an individual seeking employment must fill out * College application, the process by which prospective students apply for entry into a college or university * Patent application, a document filed at a patent office to support the grant of a patent Other uses * Application (virtue), a characteristic encapsulated in diligence * Topical application A topical medication is a medication that is applied to a particular place on or in the body. Most often topical medication means application to body surfaces such as the skin or mucous membranes to treat ailments via a large range of c ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Copy Protection
Copy protection, also known as content protection, copy prevention and copy restriction, describes measures to enforce copyright by preventing the reproduction of software, films, music, and other media. Copy protection is most commonly found on videotapes, DVDs, Blu-ray discs, HD-DVDs, computer software discs, video game discs and cartridges, audio CDs and some VCDs. Some methods of copy protection have also led to criticism because it caused inconvenience for paying consumers or secretly installed additional or unwanted software to detect copying activities on the consumer's computer. Making copy protection effective while protecting consumer rights remains a problem with media publication. Terminology Media corporations have always used the term copy protection, but critics argue that the term tends to sway the public into identifying with the publishers, who favor restriction technologies, rather than with the users. Copy prevention and copy control may be more neutral ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Canary Trap
A canary trap is a method for exposing an information leak by giving different versions of a sensitive document to each of several suspects and seeing which version gets leaked. It could be one false statement, to see whether sensitive information gets out to other people as well. Special attention is paid to the quality of the prose of the unique language, in the hopes that the suspect will repeat it verbatim in the leak, thereby identifying the version of the document. The term was coined by Tom Clancy in his novel ''Patriot Games'', although Clancy did not invent the technique. The actual method (usually referred to as a barium meal test in espionage circles) has been used by intelligence agencies for many years. The fictional character Jack Ryan describes the technique he devised for identifying the sources of leaked classified documents: Each summary paragraph has six different versions, and the mixture of those paragraphs is unique to each numbered copy of the paper. There ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Privacy
Privacy (, ) is the ability of an individual or group to seclude themselves or information about themselves, and thereby express themselves selectively. The domain of privacy partially overlaps with security, which can include the concepts of appropriate use and protection of information. Privacy may also take the form of bodily integrity. The right not to be subjected to unsanctioned invasions of privacy by the government, corporations, or individuals is part of many countries' privacy laws, and in some cases, constitutions. The concept of universal individual privacy is a modern concept primarily associated with Western culture, particularly British and North American, and remained virtually unknown in some cultures until recent times. Now, most cultures recognize the ability of individuals to withhold certain parts of personal information from wider society. With the rise of technology, the debate regarding privacy has shifted from a bodily sense to a digital sense. As the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
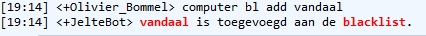
Blacklist
Blacklisting is the action of a group or authority compiling a blacklist (or black list) of people, countries or other entities to be avoided or distrusted as being deemed unacceptable to those making the list. If someone is on a blacklist, they are seen by a government or other organization as being one of a number of people who cannot be trusted or who is considered to have done something wrong. As a verb, blacklist can mean to put an individual or entity on such a list. Origins of the term The English dramatist Philip Massinger used the phrase "black list" in his 1639 tragedy ''The Unnatural Combat''. After the restoration of the English monarchy brought Charles II of England to the throne in 1660, a list of regicides named those to be punished for the execution of his father. The state papers of Charles II say "If any innocent soul be found in this black list, let him not be offended at me, but consider whether some mistaken principle or interest may not have misled ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Phoning Home
In computing, phoning home is a term often used to refer to the behavior of security systems that report network location, username, or other such data to another computer. Phoning home may be useful for the proprietor in tracking a missing or stolen computer. This type of phoning home is frequently used on mobile computers at corporations. It typically involves a software agent which is difficult to detect or remove. However, there are malicious types of phoning homes such as surreptitious communication between applications or hardware installed at end-user sites and their manufacturers or developers. The traffic may be encrypted to make it difficult or impractical for the end-user to determine what data are being transmitted. The Stuxnet attack on Iran's nuclear facilities was facilitated by phone home technology as reported by The New York Times. Legal phoning home There are some uses for the phoning home practice that are legal in some countries. For example, phoning home cou ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Digital Watermarking
A digital watermark is a kind of marker covertly embedded in a noise-tolerant signal such as audio, video or image data. It is typically used to identify ownership of the copyright of such signal. "Watermarking" is the process of hiding digital information in a carrier signal; the hidden information should,Ingemar J. Cox: ''Digital watermarking and steganography''. Morgan Kaufmann, Burlington, MA, USA, 2008 but does not need to, contain a relation to the carrier signal. Digital watermarks may be used to verify the authenticity or integrity of the carrier signal or to show the identity of its owners. It is prominently used for tracing copyright infringements and for banknote authentication. Like traditional physical watermarks, digital watermarks are often only perceptible under certain conditions, e.g. after using some algorithm.Frank Y. Shih: ''Digital watermarking and steganography: fundamentals and techniques''. Taylor & Francis, Boca Raton, FL, USA, 2008 If a digital watermark ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Database
In computing, a database is an organized collection of data stored and accessed electronically. Small databases can be stored on a file system, while large databases are hosted on computer clusters or cloud storage. The design of databases spans formal techniques and practical considerations, including data modeling, efficient data representation and storage, query languages, security and privacy of sensitive data, and distributed computing issues, including supporting concurrent access and fault tolerance. A database management system (DBMS) is the software that interacts with end users, applications, and the database itself to capture and analyze the data. The DBMS software additionally encompasses the core facilities provided to administer the database. The sum total of the database, the DBMS and the associated applications can be referred to as a database system. Often the term "database" is also used loosely to refer to any of the DBMS, the database system or an appli ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Server (computing)
In computing, a server is a piece of computer hardware or software (computer program) that provides functionality for other programs or devices, called " clients". This architecture is called the client–server model. Servers can provide various functionalities, often called "services", such as sharing data or resources among multiple clients, or performing computation for a client. A single server can serve multiple clients, and a single client can use multiple servers. A client process may run on the same device or may connect over a network to a server on a different device. Typical servers are database servers, file servers, mail servers, print servers, web servers, game servers, and application servers. Client–server systems are usually most frequently implemented by (and often identified with) the request–response model: a client sends a request to the server, which performs some action and sends a response back to the client, typically with a result or acknowledg ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Networking
A computer network is a set of computers sharing resources located on or provided by network nodes. The computers use common communication protocols over digital interconnections to communicate with each other. These interconnections are made up of telecommunication network technologies, based on physically wired, optical, and wireless radio-frequency methods that may be arranged in a variety of network topologies. The nodes of a computer network can include personal computers, servers, networking hardware, or other specialised or general-purpose hosts. They are identified by network addresses, and may have hostnames. Hostnames serve as memorable labels for the nodes, rarely changed after initial assignment. Network addresses serve for locating and identifying the nodes by communication protocols such as the Internet Protocol. Computer networks may be classified by many criteria, including the transmission medium used to carry signals, bandwidth, communications protocols ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |