|
Tradecraft
Tradecraft, within the intelligence community, refers to the techniques, methods and technologies used in modern espionage (spying) and generally, as part of the activity of intelligence assessment. This includes general topics or techniques ( dead drops, for example), or the specific techniques of a nation or organization (the particular form of encryption (encoding) used by the National Security Agency, for example). Examples * Agent handling is the management of espionage agents, principal agents, and agent networks (called "assets") by intelligence officers, who are typically known as case officers. * Analytic tradecraft is the body of specific methods for intelligence analysis. * Black bag operations are covert or clandestine entries into structures or locations to obtain information for human intelligence operations. This may require breaking and entering, lock picking, safe cracking, key impressions, fingerprinting, photography, electronic surveillance (including a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Agent Handling
In intelligence organizations, agent handling is the management of so-called agents (called secret agents or spies in common parlance), principal agents, and agent networks (called "assets") by intelligence officers typically known as case officers. Human intelligence A primary purpose of intelligence organizations is to penetrate a target with a human agent, or a network of human agents. Such agents can either infiltrate the target, or be recruited "in place". Case officers are professionally trained employees of intelligence organizations that manage human agents and human agent networks. Intelligence that derives from such human sources is known by the abbreviation HUMINT. Sometimes, agent handling is done indirectly, through "principal agents" that serve as proxies for case officers. It is not uncommon, for example, for a case officer to manage a number of principal agents, who in turn handle agent networks, which are preferably organized in a cellular fashion. In such ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
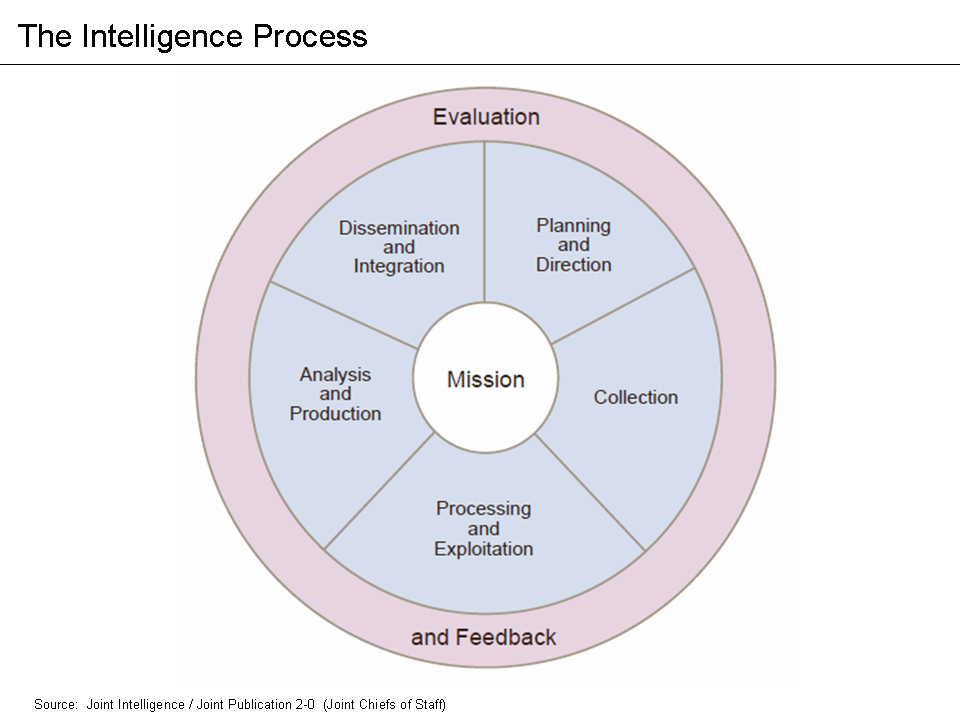
Intelligence Analysis
Intelligence analysis is the application of individual and collective cognitive methods to weigh data and test hypotheses within a secret socio-cultural context. The descriptions are drawn from what may only be available in the form of deliberately deceptive information; the analyst must correlate the similarities among deceptions and extract a common truth. Although its practice is found in its purest form inside national intelligence agencies, its methods are also applicable in fields such as business intelligence or competitive intelligence. Overview Intelligence analysis is a way of reducing the ambiguity of highly ambiguous situations. Many analysts prefer the middle-of-the-road explanation, rejecting high or low probability explanations. Analysts may use their own standard of proportionality as to the risk acceptance of the opponent, rejecting that the opponent may take an extreme risk to achieve what the analyst regards as a minor gain. The analyst must avoid the special ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Dead Drop
A dead drop or dead letter box is a method of espionage tradecraft used to pass items or information between two individuals (e.g., a case officer and an agent, or two agents) using a secret location. By avoiding direct meetings, individuals can maintain operational security. This method stands in contrast to the live drop, so-called because two persons meet to exchange items or information. Spies and their handlers have been known to perform dead drops using various techniques to hide items (such as money, secrets or instructions) and to signal that the drop has been made. Although the signal and location by necessity must be agreed upon in advance, the signal may or may not be located close to the dead drop itself. The operatives may not necessarily know one another or ever meet. Considerations The location and nature of the dead drop must enable retrieval of the hidden item without the operatives being spotted by a member of the public, the police, or other security forces� ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Espionage
Espionage, spying, or intelligence gathering is the act of obtaining secret or confidential information (intelligence) from non-disclosed sources or divulging of the same without the permission of the holder of the information for a tangible benefit. A person who commits espionage is called an ''espionage agent'' or ''spy''. Any individual or spy ring (a cooperating group of spies), in the service of a government, company, criminal organization, or independent operation, can commit espionage. The practice is clandestine, as it is by definition unwelcome. In some circumstances, it may be a legal tool of law enforcement and in others, it may be illegal and punishable by law. Espionage is often part of an institutional effort by a government or commercial concern. However, the term tends to be associated with state spying on potential or actual enemies for military purposes. Spying involving corporations is known as industrial espionage. One of the most effective ways to gath ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Microdot Camera Markiv
A microdot is text or an image substantially reduced in size to prevent detection by unintended recipients. Microdots are normally circular and around in diameter but can be made into different shapes and sizes and made from various materials such as polyester or metal. The name comes from the fact that the microdots have often been about the size and shape of a typographical dot, such as a period or the tittle of a lowercase ''i'' or ''j''. Microdots are, fundamentally, a steganographic approach to message protection. History In 1870 during the Franco-Prussian War, Paris was under siege and messages were sent by carrier pigeon. Parisian photographer René Dagron used microfilm to permit each pigeon to carry a high volume of messages, as pigeons can carry little weight. Improvement in technology since then has made even more miniaturization possible. At the International Congress of Photography in Paris in 1925 Emanuel Goldberg presented a method of producing extreme reducti ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Security
Security is protection from, or resilience against, potential harm (or other unwanted coercive change) caused by others, by restraining the freedom of others to act. Beneficiaries (technically referents) of security may be of persons and social groups, objects and institutions, ecosystems or any other entity or phenomenon vulnerable to unwanted change. Security mostly refers to protection from hostile forces, but it has a wide range of other senses: for example, as the absence of harm (e.g. freedom from want); as the presence of an essential good (e.g. food security); as resilience against potential damage or harm (e.g. secure foundations); as secrecy (e.g. a secure telephone line); as containment (e.g. a secure room or cell); and as a state of mind (e.g. emotional security). The term is also used to refer to acts and systems whose purpose may be to provide security (security companies, security forces, security guard, cyber security systems, security cameras, remote guard ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Forgery
Forgery is a white-collar crime that generally refers to the false making or material alteration of a legal instrument with the specific intent to defraud anyone (other than themself). Tampering with a certain legal instrument may be forbidden by law in some jurisdictions but such an offense is not related to forgery unless the tampered legal instrument was actually used in the course of the crime to defraud another person or entity. Copies, studio replicas, and reproductions are not considered forgeries, though they may later become forgeries through knowing and willful misrepresentations. Forging money or currency is more often called counterfeiting. But consumer goods may also be ''counterfeits'' if they are not manufactured or produced by the designated manufacturer or producer given on the label or flagged by the trademark symbol. When the object forged is a record or document it is often called a false document. This usage of "forgery" does not derive from metalwork d ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Caltrop
A caltrop (also known as caltrap, galtrop, cheval trap, galthrap, galtrap, calthrop, jackrock or crow's foot'' Battle of Alesia'' (Caesar's conquest of Gaul in 52 BC), Battlefield Detectives program, (2006), rebroadcast: 2008-09-08 on History Channel International (13:00-14:00 hrs EDST); Note: No mention of name caltrop at all, but illustrated and given as battle key to defend Roman lines of circumvallation per recent digs evidence.) is an area denial weapon made up of two or more sharp nails or spines arranged in such a manner that one of them always points upward from a stable base (for example, a tetrahedron). Historically, caltrops were part of defences that served to slow the advance of troops, especially horses, chariots, and war elephants, and were particularly effective against the soft feet of Camel cavalry, camels. In modern times, caltrops are effective when used against wheeled vehicles with pneumatic tires. Name The modern name "caltrop" is derived from the Old Engli ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
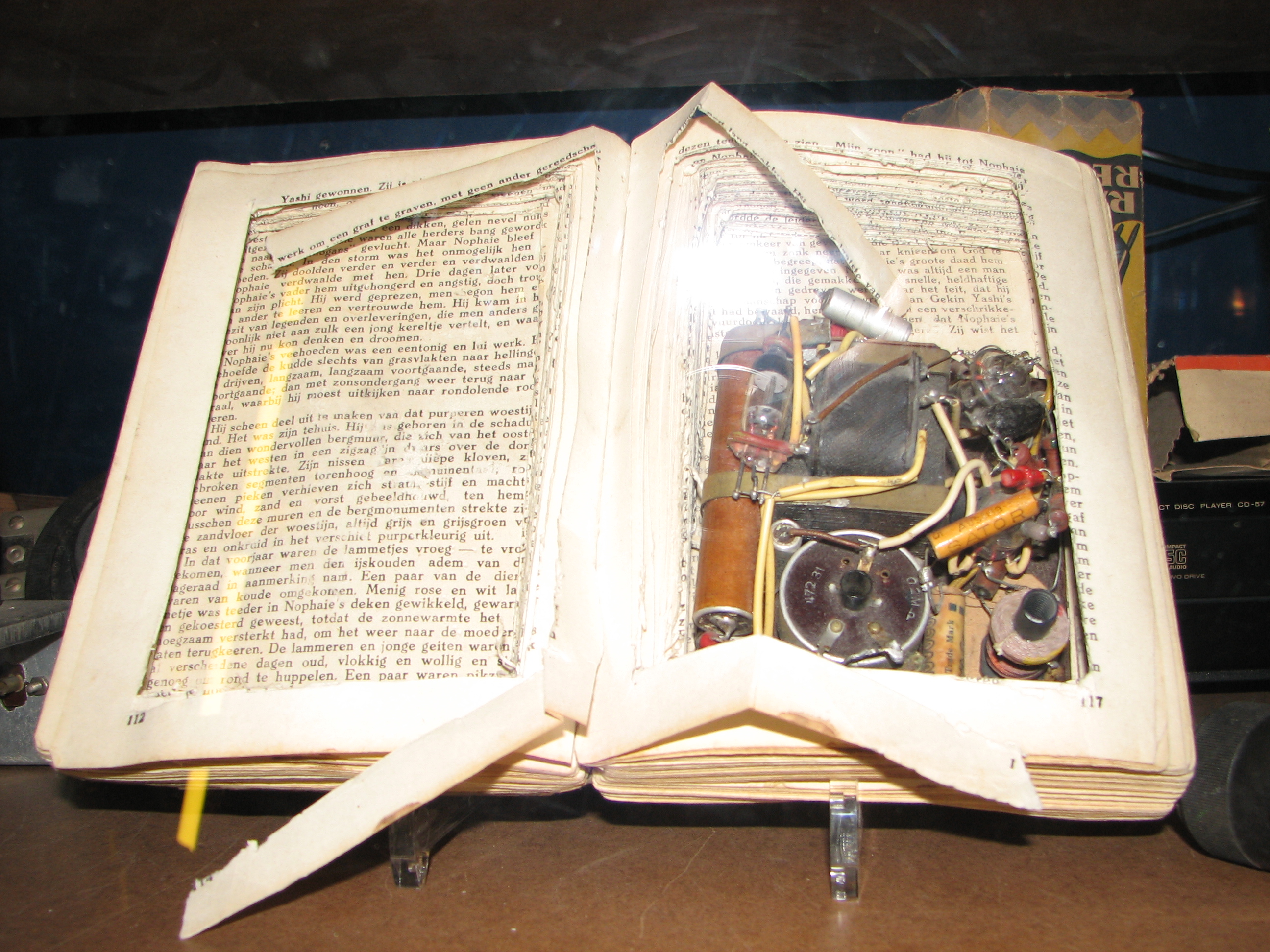
Concealment Device
Concealment devices or diversion safes are used to hide things for the purpose of secrecy or security. They are made from an ordinary household object such as a book, a soda can, a candle, a can, or something as small as a coin. The idea is that such an inconspicuous object would not be expected to contain anything of worth. Examples in espionage include dead drop spikes for transferring items to other people, and hollowed-out coins or hollowed out teeth for concealing something - such as microfilm or a suicide pill. Examples in smuggling include suitcases with false bottoms for hiding contraband. During World War II MI9 was responsible for creating many concealment devices for "escape aids" to assist prisoners of war to escape. Examples Ammunition Starting in the First World War and still continuing today, military personnel use ammunition casings to hide small amounts of critical information e.g. encryption/recognition codes or navigational grid references etc. The hiding pl ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Secrecy
Secrecy is the practice of hiding information from certain individuals or groups who do not have the "need to know", perhaps while sharing it with other individuals. That which is kept hidden is known as the secret. Secrecy is often controversial, depending on the content or nature of the secret, the group or people keeping the secret, and the motivation for secrecy. Secrecy by government entities is often decried as excessive or in promotion of poor operation; excessive revelation of information on individuals can conflict with virtues of privacy and confidentiality. It is often contrasted with Transparency (social), social transparency. Secrecy can exist in a number of different ways: encoding or encryption (where mathematical and technical strategies are used to hide messages), true secrecy (where restrictions are put upon those who take part of the message, such as through Classified information, government security classification) and obfuscation, where secrets are hidd ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cryptography
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security ( data confidentiality, data integrity, authentication, and non-repudiation) are also central to cryptography. Practical applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. Cryptography prior to the modern age was effectively synonymo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Suicide
Suicide is the act of intentionally causing one's own death. Mental disorders (including depression, bipolar disorder, schizophrenia, personality disorders, anxiety disorders), physical disorders (such as chronic fatigue syndrome), and substance abuse (including alcoholism and the use of and withdrawal from benzodiazepines) are risk factors. Some suicides are impulsive acts due to stress (such as from financial or academic difficulties), relationship problems (such as breakups or divorces), or harassment and bullying. Those who have previously attempted suicide are at a higher risk for future attempts. Effective suicide prevention efforts include limiting access to methods of suicide such as firearms, drugs, and poisons; treating mental disorders and substance abuse; careful media reporting about suicide; and improving economic conditions. Although crisis hotlines are common resources, their effectiveness has not been well studied. The most commonly adopted metho ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |









.jpg)