|
Timing Channels
In computer security, a covert channel is a type of attack that creates a capability to transfer information objects between processes that are not supposed to be allowed to communicate by the computer security policy. The term, originated in 1973 by Butler Lampson, is defined as channels "not intended for information transfer at all, such as the service program's effect on system load," to distinguish it from ''legitimate'' channels that are subjected to access controls by COMPUSEC. Characteristics A covert channel is so called because it is hidden from the access control mechanisms of secure operating systems since it does not use the legitimate data transfer mechanisms of the computer system (typically, read and write), and therefore cannot be detected or controlled by the security mechanisms that underlie secure operating systems. Covert channels are exceedingly hard to install in real systems, and can often be detected by monitoring system performance. In addition, they su ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Security
Computer security, cybersecurity (cyber security), or information technology security (IT security) is the protection of computer systems and networks from attack by malicious actors that may result in unauthorized information disclosure, theft of, or damage to hardware, software, or data, as well as from the disruption or misdirection of the services they provide. The field has become of significance due to the expanded reliance on computer systems, the Internet, and wireless network standards such as Bluetooth and Wi-Fi, and due to the growth of smart devices, including smartphones, televisions, and the various devices that constitute the Internet of things (IoT). Cybersecurity is one of the most significant challenges of the contemporary world, due to both the complexity of information systems and the societies they support. Security is of especially high importance for systems that govern large-scale systems with far-reaching physical effects, such as power distribu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
United States Department Of Defense
The United States Department of Defense (DoD, USDOD or DOD) is an executive branch department of the federal government charged with coordinating and supervising all agencies and functions of the government directly related to national security and the United States Armed Forces. The DoD is the largest employer in the world, with over 1.34 million active-duty service members (soldiers, marines, sailors, airmen, and guardians) as of June 2022. The DoD also maintains over 778,000 National Guard and reservists, and over 747,000 civilians bringing the total to over 2.87 million employees. Headquartered at the Pentagon in Arlington, Virginia, just outside Washington, D.C., the DoD's stated mission is to provide "the military forces needed to deter war and ensure our nation's security". The Department of Defense is headed by the secretary of defense, a cabinet-level head who reports directly to the president of the United States. Beneath the Department of Defense are t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Multics
Multics ("Multiplexed Information and Computing Service") is an influential early time-sharing operating system based on the concept of a single-level memory.Dennis M. Ritchie, "The Evolution of the Unix Time-sharing System", Communications of the ACM, Vol. 17, 1984, pp. 365-375. Nathan Gregory writes that Multics "has influenced all modern operating systems since, from microcomputers to mainframes." Initial planning and development for Multics started in 1964, in Cambridge, Massachusetts. Originally it was a cooperative project led by MIT ( Project MAC with Fernando Corbató) along with General Electric and Bell Labs. It was developed on the GE 645 computer, which was specially designed for it; the first one was delivered to MIT in January 1967. GE offered their earlier 635 systems with an early timesharing system known as "Mark I" and intended to offer the 645 with Multics as a larger successor. Bell withdrew from the project in 1969 as it became clear it would not deliver ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Network Steganography
Network, networking and networked may refer to: Science and technology * Network theory, the study of graphs as a representation of relations between discrete objects * Network science, an academic field that studies complex networks Mathematics * Networks, a graph with attributes studied in network theory ** Scale-free network, a network whose degree distribution follows a power law ** Small-world network, a mathematical graph in which most nodes are not neighbors, but have neighbors in common * Flow network, a directed graph where each edge has a capacity and each edge receives a flow Biology * Biological network, any network that applies to biological systems * Ecological network, a representation of interacting species in an ecosystem * Neural network, a network or circuit of neurons Technology and communication * Artificial neural network, a computing system inspired by animal brains * Broadcast network, radio stations, television stations, or other electronic media o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
OSI Layer
The Open Systems Interconnection model (OSI model) is a conceptual model that 'provides a common basis for the coordination of SOstandards development for the purpose of systems interconnection'. In the OSI reference model, the communications between a computing system are split into seven different abstraction layers: Physical, Data Link, Network, Transport, Session, Presentation, and Application. The model partitions the flow of data in a communication system into seven abstraction layers to describe networked communication from the physical implementation of transmitting bits across a communications medium to the highest-level representation of data of a distributed application. Each intermediate layer serves a class of functionality to the layer above it and is served by the layer below it. Classes of functionality are realized in all software development through all and any standardized communication protocols. Each layer in the OSI model has its own well-defined functio ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Port Knocking
In computer networking, port knocking is a method of externally opening ports on a firewall by generating a connection attempt on a set of prespecified closed ports. Once a correct sequence of connection attempts is received, the firewall rules are dynamically modified to allow the host which sent the connection attempts to connect over specific port(s). A variant called single packet authorization (SPA) exists, where only a single "knock" is needed, consisting of an encrypted packet. The primary purpose of port knocking is to prevent an attacker from scanning a system for potentially exploitable services by doing a port scan, because unless the attacker sends the correct knock sequence, the protected ports will appear closed. Overview Port knocking is usually implemented by configuring a daemon to watch the firewall log file for connection attempts to certain points, and then to modify the firewall configuration accordingly. It can also be performed on the kernel level (using ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Network
A computer network is a set of computers sharing resources located on or provided by network nodes. The computers use common communication protocols over digital interconnections to communicate with each other. These interconnections are made up of telecommunication network technologies, based on physically wired, optical, and wireless radio-frequency methods that may be arranged in a variety of network topologies. The nodes of a computer network can include personal computers, servers, networking hardware, or other specialised or general-purpose hosts. They are identified by network addresses, and may have hostnames. Hostnames serve as memorable labels for the nodes, rarely changed after initial assignment. Network addresses serve for locating and identifying the nodes by communication protocols such as the Internet Protocol. Computer networks may be classified by many criteria, including the transmission medium used to carry signals, bandwidth, communications ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Timing Channels
In computer security, a covert channel is a type of attack that creates a capability to transfer information objects between processes that are not supposed to be allowed to communicate by the computer security policy. The term, originated in 1973 by Butler Lampson, is defined as channels "not intended for information transfer at all, such as the service program's effect on system load," to distinguish it from ''legitimate'' channels that are subjected to access controls by COMPUSEC. Characteristics A covert channel is so called because it is hidden from the access control mechanisms of secure operating systems since it does not use the legitimate data transfer mechanisms of the computer system (typically, read and write), and therefore cannot be detected or controlled by the security mechanisms that underlie secure operating systems. Covert channels are exceedingly hard to install in real systems, and can often be detected by monitoring system performance. In addition, they su ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Storage Channels
Storage may refer to: Goods Containers * Dry cask storage, for storing high-level radioactive waste * Food storage * Intermodal container, cargo shipping * Storage tank Facilities * Garage (residential), a storage space normally used to store cars * Mail storage, storage by mail or delivery service * Self storage, a public storage facility * Warehouse, a commercial building for storage of goods Technology *Cloud storage *Computer data storage, a means to retain digital data *Data storage, general recording and retention of information * Energy storage *Specific storage, of groundwater in an aquifer Arts and entertainment * ''Storage'' (film), a 2009 Australian horror film * ''The Storage'', a 2011 Finnish film * ''Storage'' (album), a 1988 album by Merzbow * ''Storage Wars'', a reality television show * "Storage Wars", an episode of ''One Day at a Time'' (2017 TV series) Other * Storage (memory), a psychological and physiological process See also * * * Container (disamb ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
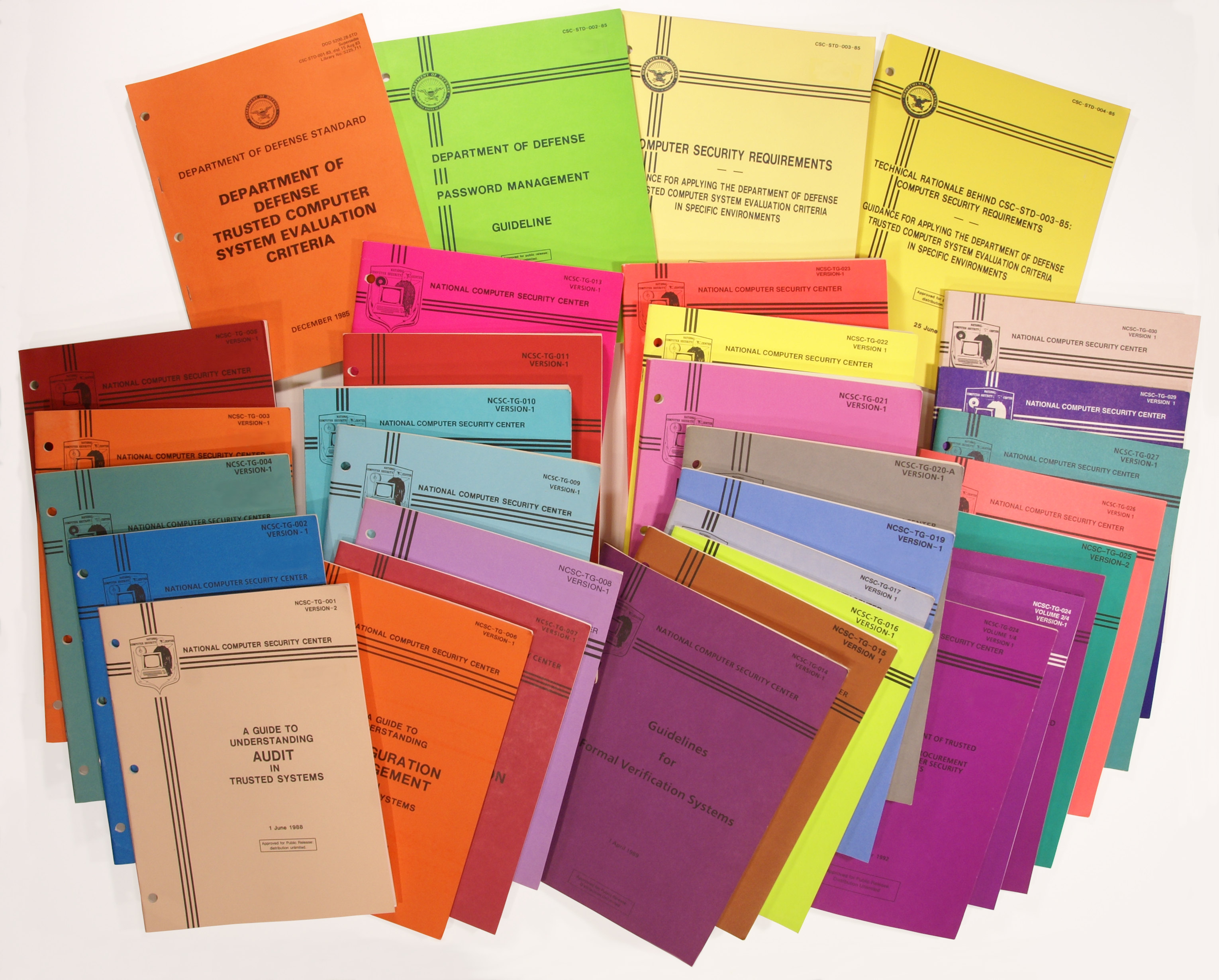
Rainbow Series
The Rainbow Series (sometimes known as the Rainbow Books) is a series of computer security standards and guidelines published by the United States government in the 1980s and 1990s. They were originally published by the U.S. Department of Defense Computer Security Center, and then by the National Computer Security Center. Objective These standards describe a process of evaluation for trusted systems. In some cases, U.S. government entities (as well as private firms) would require formal validation of computer technology using this process as part of their procurement criteria. Many of these standards have influenced, and have been superseded by, the Common Criteria. The books have nicknames based on the color of its cover. For example, the Trusted Computer System Evaluation Criteria was referred to as "The Orange Book." In the book entitled ''Applied Cryptography'', security expert Bruce Schneier states of NCSC-TG-021 that he "can't even begin to describe the color of hec ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
National Security Agency
The National Security Agency (NSA) is a national-level intelligence agency of the United States Department of Defense, under the authority of the Director of National Intelligence (DNI). The NSA is responsible for global monitoring, collection, and processing of information and data for foreign and domestic intelligence and counterintelligence purposes, specializing in a discipline known as signals intelligence (SIGINT). The NSA is also tasked with the Information assurance, protection of U.S. communications networks and information systems. The NSA relies on a variety of measures to accomplish its mission, the majority of which are clandestine operations, clandestine. The existence of the NSA was not revealed until 1975. The NSA has roughly 32,000 employees. Originating as a unit to decipher coded communications in World War II, it was officially formed as the NSA by President Harry S. Truman in 1952. Between then and the end of the Cold War, it became the largest of the U.S. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |