|
SIP Responses
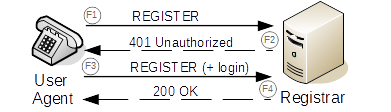
The Session Initiation Protocol (SIP) is a signalling (telecommunications), signalling communications protocol, protocol used for controlling communication sessions such as Voice over IP telephone calls. SIP is based on request/response transactions, in a similar manner to the Hypertext Transfer Protocol (HTTP). Each transaction consists of a SIP request (which will be one of several List of SIP request methods, request methods), and at least one response. SIP requests and responses may be generated by any SIP user agent; user agents are divided into clients (UACs), which initiate requests, and servers (UASes), which respond to them. A single user agent may act as both UAC and UAS for different transactions: for example, a SIP phone is a user agent that will be a UAC when making a call, and a UAS when receiving one. Additionally, some devices will act as both UAC and UAS for a single transaction; these are called Back-to-Back User Agents (B2BUAs). SIP responses specify a three-digi ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Session Initiation Protocol
The Session Initiation Protocol (SIP) is a signaling protocol used for initiating, maintaining, and terminating communication sessions that include voice, video and messaging applications. SIP is used in Internet telephony, in private IP telephone systems, as well as mobile phone calling over LTE (VoLTE). The protocol defines the specific format of messages exchanged and the sequence of communications for cooperation of the participants. SIP is a text-based protocol, incorporating many elements of the Hypertext Transfer Protocol (HTTP) and the Simple Mail Transfer Protocol (SMTP). A call established with SIP may consist of multiple media streams, but no separate streams are required for applications, such as text messaging, that exchange data as payload in the SIP message. SIP works in conjunction with several other protocols that specify and carry the session media. Most commonly, media type and parameter negotiation and media setup are performed with the Session Description ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
List Of HTTP Status Codes
This is a list of Hypertext Transfer Protocol (HTTP) response status codes. Status codes are issued by a server in response to a client's request made to the server. It includes codes from IETF Request for Comments (RFCs), other specifications, and some additional codes used in some common applications of the HTTP. The first digit of the status code specifies one of five standard classes of responses. The optional message phrases shown are typical, but any human-readable alternative may be provided, or none at all. Unless otherwise stated, the status code is part of the HTTP standard (). The Internet Assigned Numbers Authority (IANA) maintains the official registry of HTTP status codes. All HTTP response status codes are separated into five classes or categories. The first digit of the status code defines the class of response, while the last two digits do not have any classifying or categorization role. There are five classes defined by the standard: * ''1xx informational re ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
VoIP Protocols
Voice over Internet Protocol (VoIP), also called IP telephony, is a method and group of technologies for the delivery of voice communications and multimedia sessions over Internet Protocol (IP) networks, such as the Internet. The terms Internet telephony, broadband telephony, and broadband phone service specifically refer to the provisioning of communications services (voice, fax, SMS, voice-messaging) over the Internet, rather than via the public switched telephone network (PSTN), also known as plain old telephone service (POTS). Overview The steps and principles involved in originating VoIP telephone calls are similar to traditional digital telephony and involve signaling, channel setup, digitization of the analog voice signals, and encoding. Instead of being transmitted over a circuit-switched network, the digital information is packetized and transmission occurs as IP packets over a packet-switched network. They transport media streams using special media delivery protocols th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Proxy Server
In computer networking, a proxy server is a server application that acts as an intermediary between a client requesting a resource and the server providing that resource. Instead of connecting directly to a server that can fulfill a request for a resource, such as a file or web page, the client directs the request to the proxy server, which evaluates the request and performs the required network transactions. This serves as a method to simplify or control the complexity of the request, or provide additional benefits such as load balancing, privacy, or security. Proxies were devised to add structure and encapsulation to distributed systems. A proxy server thus functions on behalf of the client when requesting service, potentially masking the true origin of the request to the resource server. Types A proxy server may reside on the user's local computer, or at any point between the user's computer and destination servers on the Internet. A proxy server that passes unmodified r ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Digest Authentication
Digest access authentication is one of the agreed-upon methods a web server can use to negotiate credentials, such as username or password, with a user's web browser. This can be used to confirm the identity of a user before sending sensitive information, such as online banking transaction history. It applies a hash function to the username and password before sending them over the network. In contrast, basic access authentication uses the easily reversible Base64 encoding instead of hashing, making it non-secure unless used in conjunction with TLS. Technically, digest authentication is an application of MD5 cryptographic hashing with usage of nonce values to prevent replay attacks. It uses the HTTP protocol. This standard is obsolete since July 2011. Overview Digest access authentication was originally specified by RFC 2069 (''An Extension to HTTP: Digest Access Authentication''). RFC 2069 specifies roughly a traditional digest authentication scheme with security maintaine ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Request For Comments
A Request for Comments (RFC) is a publication in a series from the principal technical development and standards-setting bodies for the Internet, most prominently the Internet Engineering Task Force (IETF). An RFC is authored by individuals or groups of engineers and computer scientists in the form of a memorandum describing methods, behaviors, research, or innovations applicable to the working of the Internet and Internet-connected systems. It is submitted either for peer review or to convey new concepts, information, or, occasionally, engineering humor. The IETF adopts some of the proposals published as RFCs as Internet Standards. However, many RFCs are informational or experimental in nature and are not standards. The RFC system was invented by Steve Crocker in 1969 to help record unofficial notes on the development of ARPANET. RFCs have since become official documents of Internet specifications, communications protocols, procedures, and events. According to Crocker, the doc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Engineering Task Force
The Internet Engineering Task Force (IETF) is a standards organization for the Internet and is responsible for the technical standards that make up the Internet protocol suite (TCP/IP). It has no formal membership roster or requirements and all its participants are volunteers. Their work is usually funded by employers or other sponsors. The IETF was initially supported by the federal government of the United States but since 1993 has operated under the auspices of the Internet Society, an international non-profit organization. Organization The IETF is organized into a large number of working groups and birds of a feather informal discussion groups, each dealing with a specific topic. The IETF operates in a bottom-up task creation mode, largely driven by these working groups. Each working group has an appointed chairperson (or sometimes several co-chairs); a charter that describes its focus; and what it is expected to produce, and when. It is open to all who want to particip ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Internet Assigned Numbers Authority
The Internet Assigned Numbers Authority (IANA) is a standards organization that oversees global IP address allocation, autonomous system number allocation, root zone management in the Domain Name System (DNS), media types, and other Internet Protocol-related symbols and Internet numbers. Currently it is a function of ICANN, a nonprofit private American corporation established in 1998 primarily for this purpose under a United States Department of Commerce contract. ICANN managed IANA directly from 1998 through 2016, when it was transferred to Public Technical Identifiers (PTI), an affiliate of ICANN that operates IANA today. Before it, IANA was administered principally by Jon Postel at the Information Sciences Institute (ISI) of the University of Southern California (USC) situated at Marina Del Rey (Los Angeles), under a contract USC/ISI had with the United States Department of Defense. In addition, five regional Internet registries delegate number resources to their custo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SIP Phone
A VoIP phone or IP phone uses voice over IP technologies for placing and transmitting telephone calls over an IP network, such as the Internet. This is in contrast to a standard phone which uses the traditional public switched telephone network (PSTN). Digital IP-based telephone service uses control protocols such as the Session Initiation Protocol (SIP), Skinny Client Control Protocol (SCCP) or various other proprietary protocols. Types VoIP phones can be simple software-based softphones or purpose-built hardware devices that appear much like an ordinary telephone or a cordless phone. Traditional PSTN phones can be used as VoIP phones with analog telephone adapters (ATA). A VoIP phone or application may have many features an analog phone doesn't support, such as e-mail-like IDs for contacts that may be easier to remember than names or phone numbers, or easy sharing of contact lists among multiple accounts. Generally the features of VoIP phones follow those of Skype and other ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Signalling (telecommunications)
In telecommunication, signaling is the use of signals for controlling communications. This may constitute an information exchange concerning the establishment and control of a telecommunication circuit and the management of the network. Classification Signaling systems may be classified based on several principal characteristics. In-band and out-of-band signaling In the public switched telephone network (PSTN), in-band signaling is the exchange of call control information within the same physical channel, or within the same frequency band, that the telephone call itself is using. An example is dual-tone multi-frequency signaling (DTMF), which is used on most telephone lines to customer premises. Out-of-band signaling is telecommunication signaling on a dedicated channel separate from that used for the telephone call. Out-of-band signaling has been used since Signaling System No. 6 (SS6) was introduced in the 1970s, and also in Signalling System No. 7 (SS7) in 1980 which became ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
User Agent
In computing, a user agent is any software, acting on behalf of a user, which "retrieves, renders and facilitates end-user interaction with Web content". A user agent is therefore a special kind of software agent. Some prominent examples of user agents are web browsers and email readers. Often, a user agent acts as the client in a client–server system. In some contexts, such as within the Session Initiation Protocol (SIP), the term ''user agent'' refers to both end points of a communications session. User agent identification When a software agent operates in a network protocol, it often identifies itself, its application type, operating system, device model, software vendor, or software revision, by submitting a characteristic identification string to its operating peer. In HTTP, SIP,RFC 3261, ''SIP: Session Initiation Protocol'', IETF, The Internet Society (2002) and NNTP protocols, this identification is transmitted in a header field ''User-Agent''. Bots, such as Web ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
List Of SIP Request Methods
The Session Initiation Protocol (SIP) is a signaling protocol used for initiating, maintaining, and terminating communication sessions that include voice, video and messaging applications. SIP is used in Internet telephony, in private IP telephone systems, as well as mobile phone calling over LTE (VoLTE). The protocol defines the specific format of messages exchanged and the sequence of communications for cooperation of the participants. SIP is a text-based protocol, incorporating many elements of the Hypertext Transfer Protocol (HTTP) and the Simple Mail Transfer Protocol (SMTP). A call established with SIP may consist of multiple media streams, but no separate streams are required for applications, such as text messaging, that exchange data as payload in the SIP message. SIP works in conjunction with several other protocols that specify and carry the session media. Most commonly, media type and parameter negotiation and media setup are performed with the Session Description ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |