|
Parrot OS
Parrot OS is a Linux distribution based on Debian with a focus on security, privacy, and development. Core Parrot is based on Debian's "testing" branch, with a Linux 5.10 kernel. It follows a rolling release development model. The desktop environments is MATE, and the default display manager is LightDM. The system is certified to run on devices which have a minimum of 256MB of RAM, and it is suitable for both 32-bit (i386) and 64-bit (amd64) processor architectures. Moreover, the project is available for ARMv7 (armhf) architectures. In June 2017, the Parrot Team announced they were considering to change from Debian to Devuan, mainly because of problems with systemd. As of January 21st, 2019, the Parrot team has begun to phase out the development of their 32-bit (i386) ISO. In August 2020, the Parrot OS officially supports Lightweight Xfce Desktop. Editions Parrot has multiple editions that are based upon Debian, with various desktop environments available. Parrot Secu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Linux
Linux ( or ) is a family of open-source Unix-like operating systems based on the Linux kernel, an operating system kernel first released on September 17, 1991, by Linus Torvalds. Linux is typically packaged as a Linux distribution, which includes the kernel and supporting system software and libraries, many of which are provided by the GNU Project. Many Linux distributions use the word "Linux" in their name, but the Free Software Foundation uses the name "GNU/Linux" to emphasize the importance of GNU software, causing some controversy. Popular Linux distributions include Debian, Fedora Linux, and Ubuntu, the latter of which itself consists of many different distributions and modifications, including Lubuntu and Xubuntu. Commercial distributions include Red Hat Enterprise Linux and SUSE Linux Enterprise. Desktop Linux distributions include a windowing system such as X11 or Wayland, and a desktop environment such as GNOME or KDE Plasma. Distributions intended for ser ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Systemd
systemd is a software suite that provides an array of system components for Linux operating systems. Its main aim is to unify service configuration and behavior across Linux distributions; Its primary component is a "system and service manager"—an init system used to bootstrap user space and manage user processes. It also provides replacements for various daemons and utilities, including device management, login management, network connection management, and event logging. The name ''systemd'' adheres to the Unix convention of naming daemons by appending the letter ''d''. It also plays on the term "System D", which refers to a person's ability to adapt quickly and improvise to solve problems. Since 2015, the majority of Linux distributions have adopted systemd, having replaced other init systems such as SysV init. It has been praised by developers and users of distributions that adopted it for providing a stable, fast out-of-the-box solution for issues that had existed i ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Security-focused Operating System
This is a list of operating systems specifically focused on security. Operating systems for general-purpose usage may be secure without having a specific focus on security. Similar concepts include security-evaluated operating systems that have achieved certification from an auditing organization, and trusted operating systems that provide sufficient support for multilevel security and evidence of correctness to meet a particular set of requirements. Linux Android-based * Android in general is very secure, having many security features such as taking advantage of SELinux and Verified Boot. * CalyxOS is a free and open source privacy and security focused Android Custom ROM * DivestOS is a free and open source privacy and security focused Android Custom ROM * GrapheneOS is an open source privacy and security focused Android Custom ROM * Kali NetHunter is a free and open source Kali Linux based Android Custom ROM for penetration testing Debian-based * Subgraph is a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
List Of Digital Forensics Tools
During the 1980s, most digital forensic investigations consisted of "live analysis", examining digital media directly using non-specialist tools. In the 1990s, several freeware and other proprietary tools (both hardware and software) were created to allow investigations to take place without modifying media. This first set of tools mainly focused on computer forensics, although in recent years similar tools have evolved for the field of mobile device forensics. This list includes notable examples of digital forensic tools. Forensics-focused operating systems Debian-based * Kali Linux is a Debian-derived Linux distribution designed for digital forensics and penetration testing, formerly known as BackTrack. * Parrot Security OS is a cloud-oriented Linux distribution based on Debian and designed to perform security and penetration tests, do forensic analysis, or act in anonymity. It uses the MATE Desktop Environment, Linux Kernel 4.6 or higher and it is available as a live li ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
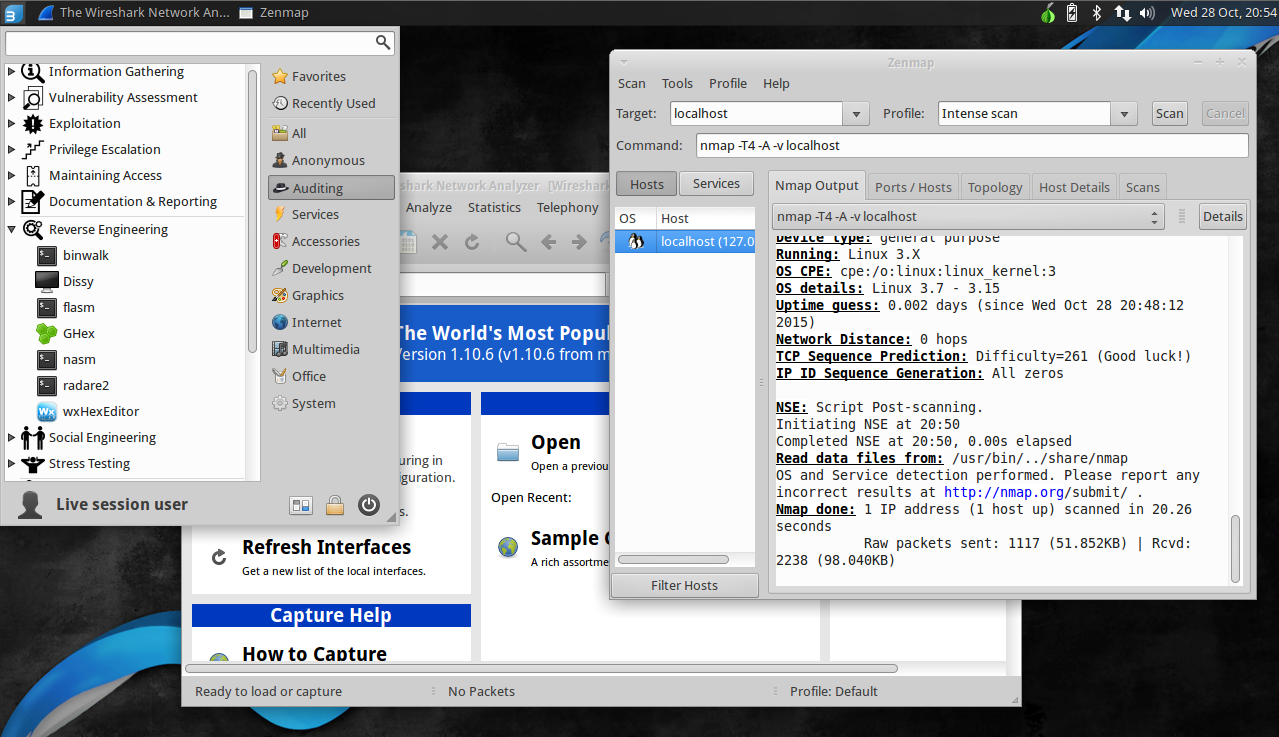
Kali Linux
Kali Linux is a Debian-derived Linux distribution designed for digital forensics and penetration testing. It is maintained and funded by Offensive Security. Kali Linux has around 600 penetration-testing programs (tools), including Armitage (a graphical cyber attack management tool), Nmap (a port scanner), Wireshark (a packet analyzer), metasploit (penetration testing framework), John the Ripper (a password cracker), sqlmap (automatic SQL injection and database takeover tool), Aircrack-ng (a software suite for penetration-testing wireless LANs), Burp suite and OWASP ZAP web application security scanners, etc. It was developed by Mati Aharoni and Devon Kearns of Offensive Security through the rewrite of BackTrack, their previous information security testing Linux distribution based on Knoppix. The name was inspired by the Hindu goddess Kali. Kali Linux is based on the Debian ''Testing'' branch. Most packages Kali uses are imported from the Debian repositories. Kali Linux's pop ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
BackBox
BackBox is a penetration test and security assessment oriented Ubuntu-based Linux distribution providing a network and informatic systems analysis toolkit. It includes a complete set of tools required for ethical hacking and security testing. Contents The main aim of BackBox is providing an alternative, highly customizable and well performing system. BackBox uses the light window manager Xfce. It delivers a fast, effective, customizable and complete experience. It also has a very helpful community behind it. It includes some of the most used security and analysis Linux tools, aiming for a wide spread of goals, ranging from web application analysis to network analysis, from stress tests to sniffing, also including vulnerability assessment, computer forensic analysis and exploitation. Part of the power of this distribution comes from its Launchpad repository core, constantly updated to the latest stable version of the most known and used ethical hacking tools. The integrat ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Tor (anonymity Network)
Tor, short for The Onion Router, is free and open-source software for enabling anonymous communication. It directs Internet traffic through a free, worldwide, volunteer overlay network, consisting of more than seven thousand relays, to conceal a user's location and usage from anyone performing network surveillance or traffic analysis. Using Tor makes it more difficult to trace a user's Internet activity. Tor's intended use is to protect the personal privacy of its users, as well as their freedom and ability to communicate confidentially through IP address anonymity using Tor exit nodes. History The core principle of Tor, onion routing, was developed in the mid-1990s by United States Naval Research Laboratory employees, mathematician Paul Syverson, and computer scientists Michael G. Reed and David Goldschlag, to protect American intelligence communications online. Onion routing is implemented by means of encryption in the application layer of the communication protocol stack ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Anonymous Web Browsing
Private browsing is a privacy feature in some web browsers. When operating in such a mode, the browser creates a temporary session that is isolated from the browser's main session and user data. Browsing history is not saved, and local data associated with the session, such as Cookies, Web cache, are cleared when the session is closed. These modes are designed primarily to prevent data and history associated with a particular browsing session from persisting on the device, or being discovered by another user of the same device. In web development, it can be used to quickly test displaying pages as they appear to first-time visitors. Private browsing modes do not necessarily protect users from being tracked by other websites or their Internet service provider (ISP). Furthermore, there is a possibility that identifiable traces of activity could be leaked from private browsing sessions by means of the operating system, security flaws in the browser, or via malicious browser ex ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Computer Forensics
Computer forensics (also known as computer forensic science) is a branch of digital forensic science pertaining to evidence found in computers and digital storage media. The goal of computer forensics is to examine digital media in a forensically sound manner with the aim of identifying, preserving, recovering, analyzing and presenting facts and opinions about the digital information. Although it is most often associated with the investigation of a wide variety of computer crime, computer forensics may also be used in civil proceedings. The discipline involves similar techniques and principles to data recovery, but with additional guidelines and practices designed to create a legal audit trail. Evidence from computer forensics investigations is usually subjected to the same guidelines and practices of other digital evidence. It has been used in a number of high-profile cases and is accepted as reliable within U.S. and European court systems. Overview In the early 1980s person ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Vulnerability Assessment
A vulnerability assessment is the process of identifying, quantifying, and prioritizing (or ranking) the vulnerabilities in a system. Examples of systems for which vulnerability assessments are performed include, but are not limited to, information technology systems, energy supply systems, water supply systems, transportation systems, and communication systems. Such assessments may be conducted on behalf of a range of different organizations, from small businesses up to large regional infrastructures. Vulnerability from the perspective of disaster management means assessing the threats from potential hazards to the population and to infrastructure. It may be conducted in the political, social, economic or environmental fields. Vulnerability assessment has many things in common with risk assessment. Assessments are typically performed according to the following steps: # Cataloging assets and capabilities (resources) in a system. # Assigning quantifiable value (or at least rank o ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
.jpg)