|
Point-to-point Encryption
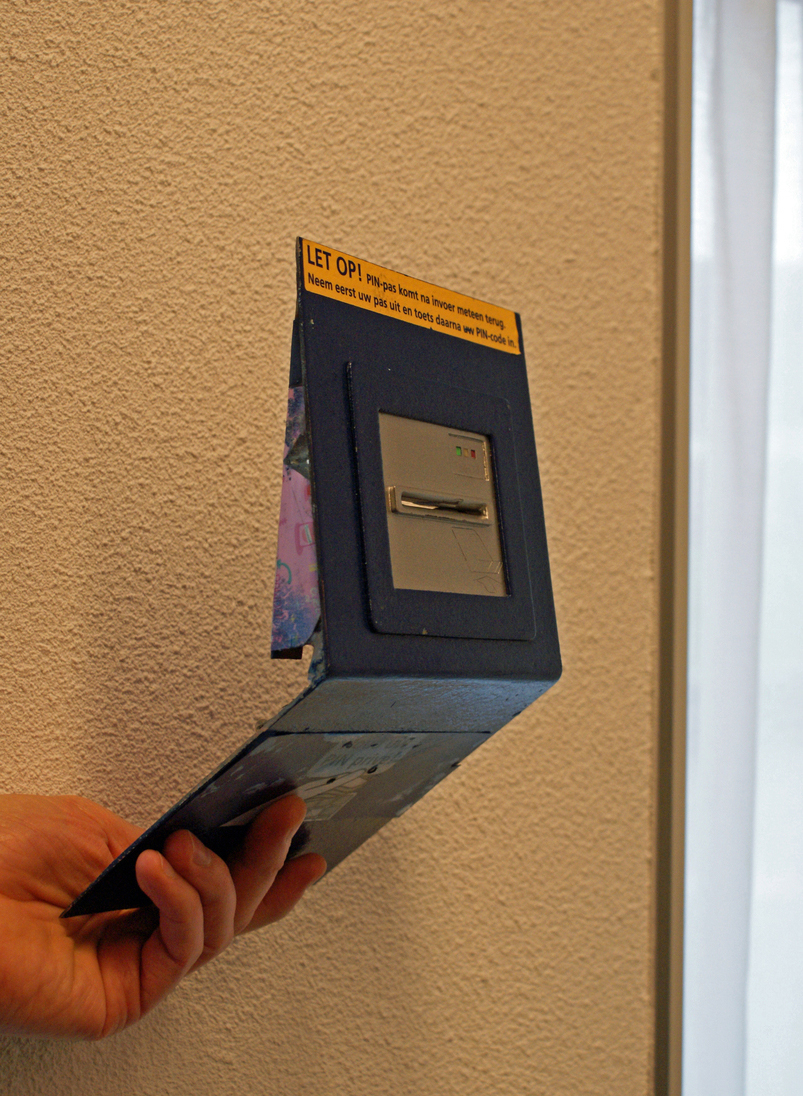
Point-to-point encryption (P2PE) is a standard established by the PCI Security Standards Council. Payment solutions that offer similar encryption but do not meet the P2PE standard are referred to as end-to-end encryption (E2EE) solutions. The objective of P2PE and E2EE is to provide a payment information security, security solution that instantaneously converts confidentiality, confidential payment card (credit and debit card) data and information into indecipherable code at the time the card is swiped, in order to prevent security hacker, hacking and fraud. It is designed to maximize the security of payment card transactions in an increasingly complex regulatory environment. The standard The P2PE Standard defines the requirements that a "solution" must meet in order to be accepted as a PCI-validated P2PE solution. A "solution" is a complete set of hardware, software, gateway, decryption, device handling, etc. Only "solutions" can be validated; individual pieces of hardware suc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
PCI Security Standards Council
The payment card industry (PCI) denotes the debit, credit, prepaid, e-purse, ATM, and POS cards and associated businesses. Overview The payment card industry consists of all the organizations which store, process and transmit cardholder data, most notably for debit cards and credit cards. The security standards are developed by the Payment Card Industry Security Standards Council which develops the Payment Card Industry Data Security Standards used throughout the industry. Individual card brands establish compliance requirements that are used by service providers and have their own compliance programs. Major card brands include American Express, Discover Financial Services, Japan Credit Bureau, Mastercard, RuPay, UnionPay and Visa. Most companies use member banks that connect and accept transactions from the card brands. Not all card brands use member banks, like American Express, these instead act as their own bank. , the United States uses a magnetic stripe on a card to proc ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
End-to-end Encryption
End-to-end encryption (E2EE) is a system of communication where only the communicating users can read the messages. In principle, it prevents potential eavesdroppers – including telecom providers, Internet providers, malicious actors, and even the provider of the communication service – from being able to access the cryptographic keys needed to decrypt the conversation. End-to-end encryption is intended to prevent data being read or secretly modified, other than by the true sender and recipient(s). The messages are encrypted by the sender but the third party does not have a means to decrypt them, and stores them encrypted. The recipients retrieve the encrypted data and decrypt it themselves. Because no third parties can decipher the data being communicated or stored, for example, companies that provide end-to-end encryption are unable to hand over texts of their customers' messages to the authorities. In 2022, the UK's Information Commissioner's Office, the government ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Information Security
Information security, sometimes shortened to InfoSec, is the practice of protecting information by mitigating information risks. It is part of information risk management. It typically involves preventing or reducing the probability of unauthorized/inappropriate access to data, or the unlawful use, disclosure, disruption, deletion, corruption, modification, inspection, recording, or devaluation of information. It also involves actions intended to reduce the adverse impacts of such incidents. Protected information may take any form, e.g. electronic or physical, tangible (e.g. paperwork) or intangible (e.g. knowledge). Information security's primary focus is the balanced protection of the confidentiality, integrity, and availability of data (also known as the CIA triad) while maintaining a focus on efficient policy implementation, all without hampering organization productivity. This is largely achieved through a structured risk management process that involves: * identify ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Confidentiality
Confidentiality involves a set of rules or a promise usually executed through confidentiality agreements that limits the access or places restrictions on certain types of information. Legal confidentiality By law, lawyers are often required to keep confidential anything pertaining to the representation of a client. The duty of confidentiality is much broader than the attorney–client evidentiary privilege, which only covers ''communications'' between the attorney and the client. Both the privilege and the duty serve the purpose of encouraging clients to speak frankly about their cases. This way, lawyers can carry out their duty to provide clients with zealous representation. Otherwise, the opposing side may be able to surprise the lawyer in court with something he did not know about his client, which may weaken the client's position. Also, a distrustful client might hide a relevant fact he thinks is incriminating, but that a skilled lawyer could turn to the client's advanta ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Debit Card
A debit card, also known as a check card or bank card is a payment card that can be used in place of cash to make purchases. The term ''#Plastic card, plastic card'' includes the above and as an identity document. These are similar to a credit card, but unlike a credit card, the money for the purchase must be in the cardholder's bank account at the time of a purchase and is immediately transferred directly from that account to the merchant's account to pay for the purchase. Some debit cards carry a Stored-value card, stored value with which a payment is made (prepaid card), but most relay a message to the cardholder's bank to withdraw funds from the cardholder's designated bank account. In some cases, the payment card number is assigned exclusively for use on the Internet and there is no physical card. This is referred to as a virtual card. In many countries, the use of debit cards has become so widespread they have overtaken cheque, checks in volume, or have entirely replace ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Security Hacker
A security hacker is someone who explores methods for breaching defenses and exploiting weaknesses in a computer system or network. Hackers may be motivated by a multitude of reasons, such as profit, protest, information gathering, challenge, recreation, or evaluation of a system weaknesses to assist in formulating defenses against potential hackers. The subculture that has evolved around hackers is often referred to as the "computer underground". Longstanding controversy surrounds the meaning of the term " hacker." In this controversy, computer programmers reclaim the term ''hacker'', arguing that it refers simply to someone with an advanced understanding of computers and computer networks and that ''cracker'' is the more appropriate term for those who break into computers, whether computer criminals (black hats) or computer security experts ( white hats). A 2014 article noted that "the black-hat meaning still prevails among the general public". History Birth of subcul ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Fraud
In law, fraud is intentional deception to secure unfair or unlawful gain, or to deprive a victim of a legal right. Fraud can violate civil law (e.g., a fraud victim may sue the fraud perpetrator to avoid the fraud or recover monetary compensation) or criminal law (e.g., a fraud perpetrator may be prosecuted and imprisoned by governmental authorities), or it may cause no loss of money, property, or legal right but still be an element of another civil or criminal wrong. The purpose of fraud may be monetary gain or other benefits, for example by obtaining a passport, travel document, or driver's license, or mortgage fraud, where the perpetrator may attempt to qualify for a mortgage by way of false statements. Internal fraud, also known as "insider fraud", is fraud committed or attempted by someone within an organisation such as an employee. A hoax is a distinct concept that involves deliberate deception without the intention of gain or of materially damaging or depriving a v ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Point Of Interaction
The point of sale (POS) or point of purchase (POP) is the time and place at which a retail transaction is completed. At the point of sale, the merchant calculates the amount owed by the customer, indicates that amount, may prepare an invoice for the customer (which may be a cash register printout), and indicates the options for the customer to make payment. It is also the point at which a customer makes a payment to the merchant in exchange for goods or after provision of a service. After receiving payment, the merchant may issue a receipt for the transaction, which is usually printed but can also be dispensed with or sent electronically. To calculate the amount owed by a customer, the merchant may use various devices such as weighing scales, barcode scanners, and cash registers (or the more advanced "POS cash registers", which are sometimes also called "POS systems"). To make a payment, payment terminals, touch screens, and other hardware and software options are available. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
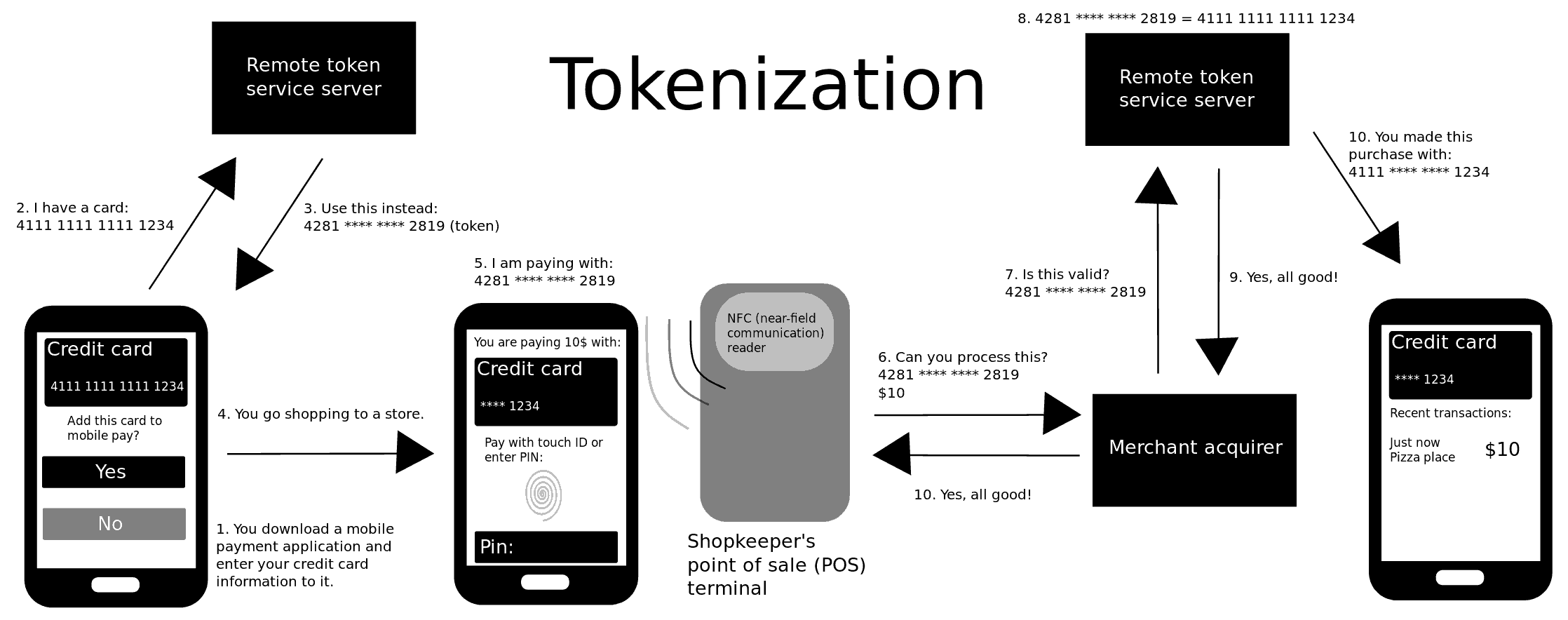
Tokenization (data Security)
Tokenization, when applied to data security, is the process of substituting a sensitive data element with a non-sensitive equivalent, referred to as a token, that has no intrinsic or exploitable meaning or value. The token is a reference (i.e. identifier) that maps back to the sensitive data through a tokenization system. The mapping from original data to a token uses methods that render tokens infeasible to reverse in the absence of the tokenization system, for example using tokens created from random numbers. A one-way cryptographic function is used to convert the original data into tokens, making it difficult to recreate the original data without obtaining entry to the tokenization system's resources. To deliver such services, the system maintains a vault database of tokens that are connected to the corresponding sensitive data. Protecting the system vault is vital to the system, and improved processes must be put in place to offer database integrity and physical security. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Payment Card Industry Data Security Standard
The Payment Card Industry Data Security Standard (PCI DSS) is an information security standard used to handle credit cards from major card brands. The standard is administered by the Payment Card Industry Security Standards Council and its use is mandated by the card brands. The standard was created to better control cardholder data and reduce credit card fraud. Validation of compliance is performed annually or quarterly, by a method suited to the volume of transactions handled: * Self-Assessment Questionnaire (SAQ) * Firm-specific Internal Security Assessor (ISA) * External Qualified Security Assessor (QSA) History Originally, the major card brands started five different security programs: * Visa's Cardholder Information Security Program * MasterCard's Site Data Protection *American Express's Data Security Operating Policy *Discover's Information Security and Compliance *JCB's Data Security Program The intentions of each were roughly similar: to create an additional level of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
.jpg)