|
OllyDbg
OllyDbg (named after its author, Oleh Yuschuk) was an x86 debugger that emphasizes binary code analysis, which is useful when source code is not available. It traces registers, recognizes procedures, API calls, switches, tables, constants and strings, as well as locates routines from object files and libraries. It has a user friendly interface, and its functionality can be extended by third-party plugins. Version 1.10 is the final 1.x release. Version 2.0 was released in June 2010, and OllyDbg has been rewritten from the ground up in this release. Although the current version of OllyDbg cannot disassemble binaries compiled for 64-bit processors, a 64-bit version of the debugger has been promised. License The software is free of cost, but the shareware license of version 1.x requires users to register with the author. In version 2.x, the registration requirement was dropped. The source code can be purchased from the author. The disassembler part of OllyDbg is free software, re ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Software Cracking
Software cracking (known as "breaking" mostly in the 1980s) is the modification of software to remove or disable features which are considered undesirable by the person cracking the software (software cracker), especially copy protection features (including protection against the manipulation of software, serial number, hardware key, date checks and disc check) or software annoyances like nag screens and adware. A crack refers to the means of achieving, for example a stolen serial number or a tool that performs that act of cracking. Some of these tools are called keygen, patch, loader, or no-disc crack. A keygen is a handmade product serial number generator that often offers the ability to generate working serial numbers in your own name. A patch is a small computer program that modifies the machine code of another program. This has the advantage for a cracker to not include a large executable in a release when only a few bytes are changed. A loader modifies the startup flow ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Software Cracking
Software cracking (known as "breaking" mostly in the 1980s) is the modification of software to remove or disable features which are considered undesirable by the person cracking the software (software cracker), especially copy protection features (including protection against the manipulation of software, serial number, hardware key, date checks and disc check) or software annoyances like nag screens and adware. A crack refers to the means of achieving, for example a stolen serial number or a tool that performs that act of cracking. Some of these tools are called keygen, patch, loader, or no-disc crack. A keygen is a handmade product serial number generator that often offers the ability to generate working serial numbers in your own name. A patch is a small computer program that modifies the machine code of another program. This has the advantage for a cracker to not include a large executable in a release when only a few bytes are changed. A loader modifies the startup flow ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
C (programming Language)
C (''pronounced like the letter c'') is a General-purpose language, general-purpose computer programming language. It was created in the 1970s by Dennis Ritchie, and remains very widely used and influential. By design, C's features cleanly reflect the capabilities of the targeted CPUs. It has found lasting use in operating systems, device drivers, protocol stacks, though decreasingly for application software. C is commonly used on computer architectures that range from the largest supercomputers to the smallest microcontrollers and embedded systems. A successor to the programming language B (programming language), B, C was originally developed at Bell Labs by Ritchie between 1972 and 1973 to construct utilities running on Unix. It was applied to re-implementing the kernel of the Unix operating system. During the 1980s, C gradually gained popularity. It has become one of the measuring programming language popularity, most widely used programming languages, with C compilers avail ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
GNU General Public License
The GNU General Public License (GNU GPL or simply GPL) is a series of widely used free software licenses that guarantee end users the Four Freedoms (Free software), four freedoms to run, study, share, and modify the software. The license was the first copyleft for general use and was originally written by the founder of the Free Software Foundation (FSF), Richard Stallman, for the GNU Project. The license grants the recipients of a computer program the rights of the Free Software Definition. These GPL series are all copyleft licenses, which means that any derivative work must be distributed under the same or equivalent license terms. It is more restrictive than the GNU Lesser General Public License, Lesser General Public License and even further distinct from the more widely used permissive software licenses BSD licenses, BSD, MIT License, MIT, and Apache License, Apache. Historically, the GPL license family has been one of the most popular software licenses in the free and open ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Cheat Engine
Cheat Engine (CE) is a proprietary, source available freeware memory scanner/debugger created by Eric Heijnen ("Byte, Darke") for the Windows operating system. Cheat Engine is mostly used for cheating in computer games and is sometimes modified and recompiled to support new games. It searches for values input by the user with a wide variety of options that allow the user to find and sort through the computer's memory. Cheat Engine can also create standalone trainers that can operate independently of Cheat Engine, often found on user forums or at the request of another user. While it is source-available, it is not free and open source software, as its license contains restrictions on redistribution. Features Cheat Engine can view the disassembled memory of a process and allow the addition and/or alteration of game states to give the user advantages such as infinite health, time, or ammunition. It also has some Direct3D manipulation tools, allowing vision through walls "Wallh ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Ghidra
Ghidra (pronounced gee-druh; ) is a free and open source reverse engineering tool developed by the National Security Agency (NSA) of the United States. The binaries were released at RSA Conference in March 2019; the sources were published one month later on GitHub. Ghidra is seen by many security researchers as a competitor to IDA Pro. The software is written in Java using the Swing framework for the GUI. The decompiler component is written in C++, and is therefore usable in a stand-alone form. Ghidra plugins can be developed in Java or in Python (provided via Jython). History Ghidra's existence was originally revealed to the public via WikiLeaks in March 2017, but the software itself remained unavailable until its declassification and official release two years later. In June 2019, Coreboot began to use Ghidra for its reverse engineering efforts on firmware-specific problems following the open source release of the Ghidra software suite. Ghidra can be used as a debugger sin ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Radare2
Radare2 (also known as r2) is a complete framework for reverse-engineering and analyzing binaries; composed of a set of small utilities that can be used together or independently from the command line. Built around a disassembler for computer software which generates assembly language source code from machine-executable code, it supports a variety of executable formats for different processor architectures and operating systems. History Radare2 was created in February 2006, aiming to provide a free and simple command-line interface for a hexadecimal editor supporting 64 bit offsets to make searches and recovering data from hard-disks, for forensic purposes. Since then, the project has grown with the aim changed to provide a complete framework for analyzing binaries while adhering to several principles of the Unix philosophy. In 2009, the decision was made to completely rewrite it, to get around limitations in the initial design. Since then, the project continued to grow, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Interactive Disassembler
The Interactive Disassembler (IDA) is a disassembler for computer software which generates assembly language source code from machine-executable code. It supports a variety of executable, executable formats for different Central processing unit, processors and operating systems. It also can be used as a debugger for Portable Executable, Windows PE, Mac OS X Mach-O, and Linux Executable and Linkable Format, ELF executables. A decompiler plug-in for programs compiled with a C (programming language), C/ compiler is available at extra cost. The latest full version of IDA Pro is commercial, while a less capable version is available for download free of charge (version 8.1 ). IDA performs automatic code analysis, using cross-references between code sections, knowledge of parameters of Application programming interface, API calls, and other information. However, the nature of disassembly precludes total accuracy, and a great deal of human intervention is necessarily required; ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Reverse Engineering
Reverse engineering (also known as backwards engineering or back engineering) is a process or method through which one attempts to understand through deductive reasoning how a previously made device, process, system, or piece of software accomplishes a task with very little (if any) insight into exactly how it does so. It is essentially the process of opening up or dissecting a system to see how it works, in order to duplicate or enhance it. Depending on the system under consideration and the technologies employed, the knowledge gained during reverse engineering can help with repurposing obsolete objects, doing security analysis, or learning how something works. Although the process is specific to the object on which it is being performed, all reverse engineering processes consist of three basic steps: Information extraction, Modeling, and Review. Information extraction refers to the practice of gathering all relevant information for performing the operation. Modeling refers to th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
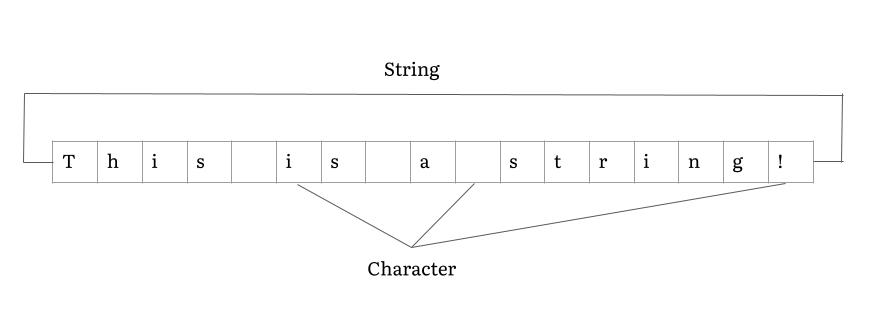
String (computer Science)
In computer programming, a string is traditionally a sequence of characters, either as a literal constant or as some kind of variable. The latter may allow its elements to be mutated and the length changed, or it may be fixed (after creation). A string is generally considered as a data type and is often implemented as an array data structure of bytes (or words) that stores a sequence of elements, typically characters, using some character encoding. ''String'' may also denote more general arrays or other sequence (or list) data types and structures. Depending on the programming language and precise data type used, a variable declared to be a string may either cause storage in memory to be statically allocated for a predetermined maximum length or employ dynamic allocation to allow it to hold a variable number of elements. When a string appears literally in source code, it is known as a string literal or an anonymous string. In formal languages, which are used in mathematical ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |