|
OTPW
OTPW is a one-time password system developed for authentication in Unix-like operating systems by Markus Kuhn (computer scientist), Markus Kuhn. A user's real password is not directly transmitted across the Computer networking, network. Rather, a series of one-time passwords is created from a short set of characters (constant secret) and a set of one-time tokens. As each single-use password can only be used once, passwords intercepted by a Packet sniffer, password sniffer or Keystroke logging, key logger are not useful to an attacker. OTPW is supported in Unix and Linux (via pluggable authentication modules), OpenBSD, NetBSD, and FreeBSD, and a generic open source implementation can be used to enable its use on other systems. OTPW, like the other one-time password systems, is sensitive to a man in the middle attack if used by itself. This could for example be solved by putting Secure Sockets Layer, SSL, SPKM or similar security protocol "under it" which authenticates the server and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
One-time Password
A one-time password (OTP), also known as a one-time PIN, one-time authorization code (OTAC) or dynamic password, is a password that is valid for only one login session or transaction, on a computer system or other digital device. OTPs avoid several shortcomings that are associated with traditional (static) password-based authentication; a number of implementations also incorporate two-factor authentication by ensuring that the one-time password requires access to ''something a person has'' (such as a small keyring fob device with the OTP calculator built into it, or a smartcard or specific cellphone) as well as ''something a person knows'' (such as a PIN). OTP generation algorithms typically make use of pseudorandomness or randomness to generate a shared key or seed, and cryptographic hash functions, which can be used to derive a value but are hard to reverse and therefore difficult for an attacker to obtain the data that was used for the hash. This is necessary because otherwise ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Markus Kuhn (computer Scientist)
Markus Guenther Kuhn (born 1971) is a German computer scientist, currently working at the Computer Laboratory, University of Cambridge and a fellow of Wolfson College, Cambridge. Education Kuhn was educated at University of Erlangen (Germany), he received his Master of Science degree at Purdue University and PhD at the University of Cambridge. Research Kuhn's main research interests include computer security, in particular the hardware and signal-processing aspects of it, and distributed systems. He is known, among other things, for his work on security microcontrollers, compromising emanations, and distance-bounding protocols. He developed the Stirmark test for digital watermarking schemes, the OTPW one-time password system, and headed the project that extended the X11 misc-fixed fonts to Unicode. In 1994, as an undergraduate student, he became known for developing several ways to circumvent the VideoCrypt encryption system, most notably the ''Season7'' smartcard emulator. ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
S/KEY
S/KEY is a one-time password system developed for authentication to Unix-like operating systems, especially from dumb terminals or untrusted public computers on which one does not want to type a long-term password. A user's real password is combined in an offline device with a short set of characters and a decrementing counter to form a single-use password. Because each password is only used once, they are useless to password sniffers. Because the short set of characters does not change until the counter reaches zero, it is possible to prepare a list of single-use passwords, in order, that can be carried by the user. Alternatively, the user can present the password, characters, and desired counter value to a local calculator to generate the appropriate one-time password that can then be transmitted over the network in the clear. The latter form is more common and practically amounts to challenge–response authentication. S/KEY is supported in Linux (via pluggable authentication mo ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
OPIE Authentication System
OPIE is the initialism of "One time Passwords In Everything". Opie is a mature, Unix-like login and password package installed on the server and the client which makes untrusted networks safer against password-sniffing packet-analysis software like dSniff and safe against Shoulder surfing. It works by circumventing the delayed attack method because the same password is never used twice after installing Opie. OPIE implements a one-time password (OTP) scheme based on S/KEY, which will require a secret passphrase (not echoed) to generate a password for the current session, or a list of passwords you can print and carry on your person. OPIE uses an MD4 or MD5 hash function to generate passwords. OPIE can restrict its logins based on IP address. It uses its own passwd and login modules. If the Enter key is pressed at the password prompt, it will turn echo on, so what is being typed can be seen when entering an unfamiliar password from a printout. OPIE will improve security when ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Hash Function
A hash function is any function that can be used to map data of arbitrary size to fixed-size values. The values returned by a hash function are called ''hash values'', ''hash codes'', ''digests'', or simply ''hashes''. The values are usually used to index a fixed-size table called a ''hash table''. Use of a hash function to index a hash table is called ''hashing'' or ''scatter storage addressing''. Hash functions and their associated hash tables are used in data storage and retrieval applications to access data in a small and nearly constant time per retrieval. They require an amount of storage space only fractionally greater than the total space required for the data or records themselves. Hashing is a computationally and storage space-efficient form of data access that avoids the non-constant access time of ordered and unordered lists and structured trees, and the often exponential storage requirements of direct access of state spaces of large or variable-length keys. Use of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Last Character Attack
A last is a mechanical form shaped like a human foot. It is used by shoemakers and cordwainers in the manufacture and repair of shoes. Lasts typically come in pairs and have been made from various materials, including hardwoods, cast iron, and high-density plastics. The term is derived from the Proto-Germanic *''laistaz'' ("track, trace, footprint"); cognates include Swedish ''läst'', Danish ''læste'', German ''Leisten''. Production Lasts come in many styles and sizes, depending on the exact job they are designed for. Common variations include simple one-size lasts used for repairing soles and heels, durable lasts used in modern mass production, and custom-made lasts used in the making of bespoke footwear. Though a last is made approximately in the shape of a human foot, the precise shape is tailored to the kind of footwear being made. For example, a boot last would be designed to hug the instep for a close fit. Modern last shapes are typically designed using dedicated compu ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Setuid
The Unix Unix (; trademarked as UNIX) is a family of multitasking, multiuser computer operating systems that derive from the original AT&T Unix, whose development started in 1969 at the Bell Labs research center by Ken Thompson, Dennis Ritchie, and ot ... access rights flags setuid and setgid (short for ''set user identity'' and ''set group identity'') allow users to run an executable with the file system permissions of the executable's owner or group respectively and to change behaviour in directories. They are often used to allow users on a computer system to run programs with temporarily elevated privileges in order to perform a specific task. While the assumed user id or group id privileges provided are not always elevated, at a minimum they are specific. The flags setuid and setgid are needed for tasks that require different privileges than what the user is normally granted, such as the ability to alter system files or databases to change their login password. Some of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
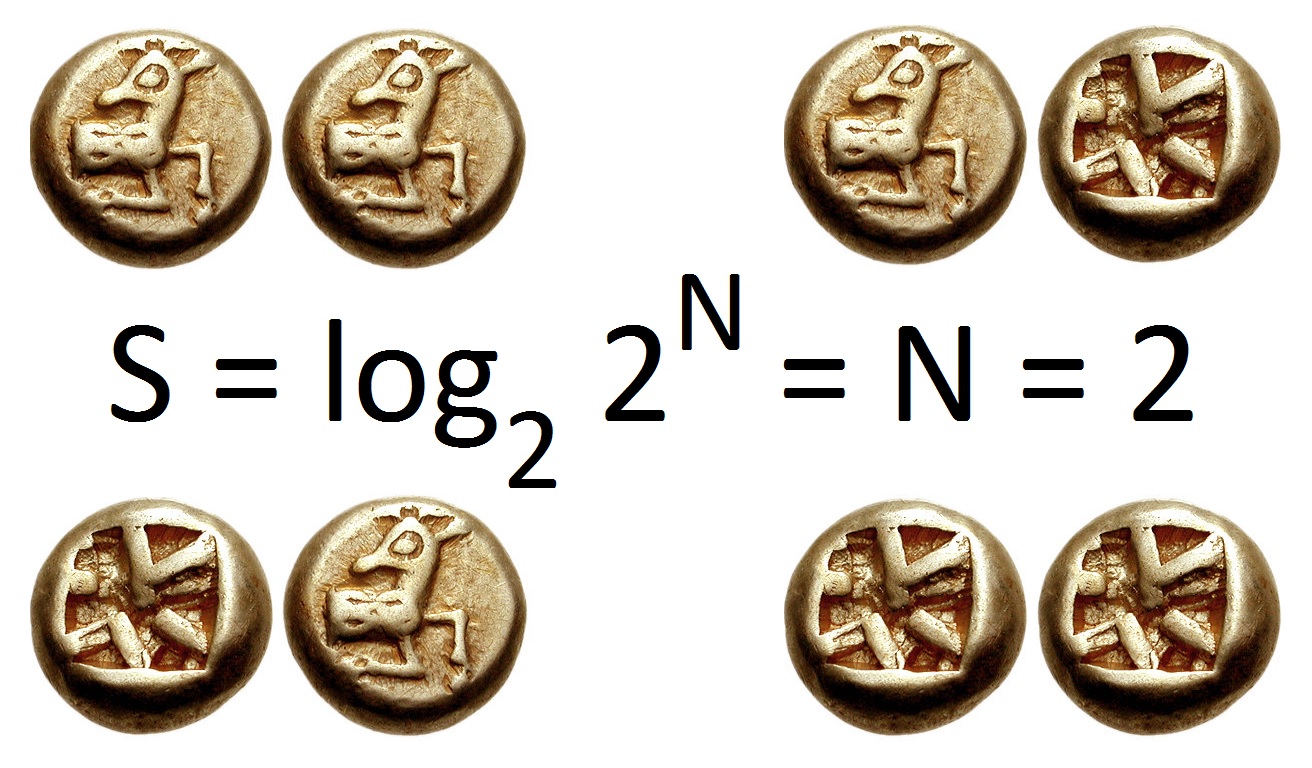
Information Entropy
In information theory, the entropy of a random variable is the average level of "information", "surprise", or "uncertainty" inherent to the variable's possible outcomes. Given a discrete random variable X, which takes values in the alphabet \mathcal and is distributed according to p: \mathcal\to , 1/math>: \Eta(X) := -\sum_ p(x) \log p(x) = \mathbb \log p(X), where \Sigma denotes the sum over the variable's possible values. The choice of base for \log, the logarithm, varies for different applications. Base 2 gives the unit of bits (or " shannons"), while base ''e'' gives "natural units" nat, and base 10 gives units of "dits", "bans", or " hartleys". An equivalent definition of entropy is the expected value of the self-information of a variable. The concept of information entropy was introduced by Claude Shannon in his 1948 paper " A Mathematical Theory of Communication",PDF archived froherePDF archived frohere and is also referred to as Shannon entropy. Shannon's theory d ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
English Language
English is a West Germanic language of the Indo-European language family, with its earliest forms spoken by the inhabitants of early medieval England. It is named after the Angles, one of the ancient Germanic peoples that migrated to the island of Great Britain. Existing on a dialect continuum with Scots, and then closest related to the Low Saxon and Frisian languages, English is genealogically West Germanic. However, its vocabulary is also distinctively influenced by dialects of France (about 29% of Modern English words) and Latin (also about 29%), plus some grammar and a small amount of core vocabulary influenced by Old Norse (a North Germanic language). Speakers of English are called Anglophones. The earliest forms of English, collectively known as Old English, evolved from a group of West Germanic (Ingvaeonic) dialects brought to Great Britain by Anglo-Saxon settlers in the 5th century and further mutated by Norse-speaking Viking settlers starting in the 8th and 9th ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Base64
In computer programming, Base64 is a group of binary-to-text encoding schemes that represent binary data (more specifically, a sequence of 8-bit bytes) in sequences of 24 bits that can be represented by four 6-bit Base64 digits. Common to all binary-to-text encoding schemes, Base64 is designed to carry data stored in binary formats across channels that only reliably support text content. Base64 is particularly prevalent on the World Wide Web where one of its uses is the ability to embed image files or other binary assets inside textual assets such as HTML and CSS files. Base64 is also widely used for sending e-mail attachments. This is required because SMTP – in its original form – was designed to transport 7-bit ASCII characters only. This encoding causes an overhead of 33–37% (33% by the encoding itself; up to 4% more by the inserted line breaks). Design Each Base64 digit can take on 64 different values, encoding 6 bits of data. Which characters are chosen to ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Shell (computing)
In computing, a shell is a computer program that exposes an operating system's services to a human user or other programs. In general, operating system shells use either a command-line interface (CLI) or graphical user interface (GUI), depending on a computer's role and particular operation. It is named a shell because it is the outermost layer around the operating system. Command-line shells require the user to be familiar with commands and their calling syntax, and to understand concepts about the shell-specific scripting language (for example, bash), while graphical shells place a low burden on beginning computer users and are characterized as being easy to use, yet most GUI-enabled operating systems also provide CLI shells, normally for performing advanced tasks. Overview Operating systems provide various services to their users, including file management, process management (running and terminating applications), batch processing, and operating system monitoring and con ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |