|
Network Time Security
The Network Time Protocol (NTP) is a networking protocol for clock synchronization between computer systems over packet-switched, variable- latency data networks. In operation since before 1985, NTP is one of the oldest Internet protocols in current use. NTP was designed by David L. Mills of the University of Delaware. NTP is intended to synchronize all participating computers to within a few milliseconds of Coordinated Universal Time (UTC). It uses the intersection algorithm, a modified version of Marzullo's algorithm, to select accurate time servers and is designed to mitigate the effects of variable network latency. NTP can usually maintain time to within tens of milliseconds over the public Internet, and can achieve better than one millisecond accuracy in local area networks under ideal conditions. Asymmetric routes and network congestion can cause errors of 100 ms or more. The protocol is usually described in terms of a client–server model, but can as easily be use ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
David L
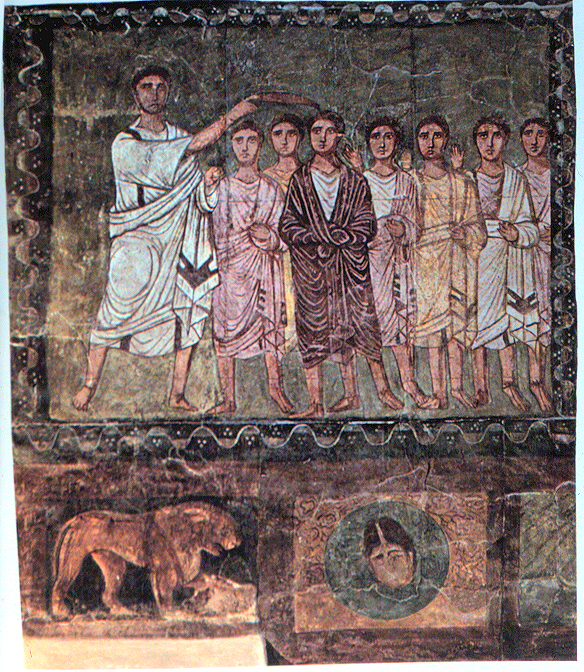
David (; , "beloved one") (traditional spelling), , ''Dāwūd''; grc-koi, Δαυΐδ, Dauíd; la, Davidus, David; gez , ዳዊት, ''Dawit''; xcl, Դաւիթ, ''Dawitʿ''; cu, Давíдъ, ''Davidŭ''; possibly meaning "beloved one". was, according to the Hebrew Bible, the third king of the United Kingdom of Israel. In the Books of Samuel, he is described as a young shepherd and harpist who gains fame by slaying Goliath, a champion of the Philistines, in southern Canaan. David becomes a favourite of Saul, the first king of Israel; he also forges a notably close friendship with Jonathan, a son of Saul. However, under the paranoia that David is seeking to usurp the throne, Saul attempts to kill David, forcing the latter to go into hiding and effectively operate as a fugitive for several years. After Saul and Jonathan are both killed in battle against the Philistines, a 30-year-old David is anointed king over all of Israel and Judah. Following his rise to power, David ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Client–server Model
The client–server model is a distributed application structure that partitions tasks or workloads between the providers of a resource or service, called servers, and service requesters, called clients. Often clients and servers communicate over a computer network on separate hardware, but both client and server may reside in the same system. A server host runs one or more server programs, which share their resources with clients. A client usually does not share any of its resources, but it requests content or service from a server. Clients, therefore, initiate communication sessions with servers, which await incoming requests. Examples of computer applications that use the client–server model are email, network printing, and the World Wide Web. Client and server role The "client–server" characteristic describes the relationship of cooperating programs in an application. The server component provides a function or service to one or many clients, which initiate requests for s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Authenticated Encryption
Authenticated Encryption (AE) and Authenticated Encryption with Associated Data (AEAD) are forms of encryption which simultaneously assure the confidentiality and authenticity of data. Programming interface A typical application programming interface, programming interface for an AE implementation provides the following functions: * Encryption ** Input: ''plaintext'', ''key'', and optionally a ''header'' in plaintext that will not be encrypted, but will be covered by authenticity protection. ** Output: ''ciphertext'' and ''authentication tag'' (message authentication code or MAC). * Decryption ** Input: ''ciphertext'', ''key'', ''authentication tag'', and optionally a ''header'' (if used during the encryption). ** Output: ''plaintext'', or an error if the ''authentication tag'' does not match the supplied ''ciphertext'' or ''header''. The ''header'' part is intended to provide authenticity and integrity protection for networking or storage metadata for which confidentiality is ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Transport Layer Security
Transport Layer Security (TLS) is a cryptographic protocol designed to provide communications security over a computer network. The protocol is widely used in applications such as email, instant messaging, and voice over IP, but its use in securing HTTPS remains the most publicly visible. The TLS protocol aims primarily to provide security, including privacy (confidentiality), integrity, and authenticity through the use of cryptography, such as the use of certificates, between two or more communicating computer applications. It runs in the presentation layer and is itself composed of two layers: the TLS record and the TLS handshake protocols. The closely related Datagram Transport Layer Security (DTLS) is a communications protocol providing security to datagram-based applications. In technical writing you often you will see references to (D)TLS when it applies to both versions. TLS is a proposed Internet Engineering Task Force (IETF) standard, first defined in 1999, and the c ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Backward Compatibility
Backward compatibility (sometimes known as backwards compatibility) is a property of an operating system, product, or technology that allows for interoperability with an older legacy system, or with input designed for such a system, especially in telecommunications and computing. Modifying a system in a way that does not allow backward compatibility is sometimes called " breaking" backward compatibility. A complementary concept is forward compatibility. A design that is forward-compatible usually has a roadmap for compatibility with future standards and products. A related term from programming jargon is hysterical reasons or hysterical raisins (near-homophones for "historical reasons"), as the purpose of some software features may be solely to support older hardware or software versions. Usage In hardware A simple example of both backward and forward compatibility is the introduction of FM radio in stereo. FM radio was initially mono, with only one audio channel represented ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Daylight Saving Time
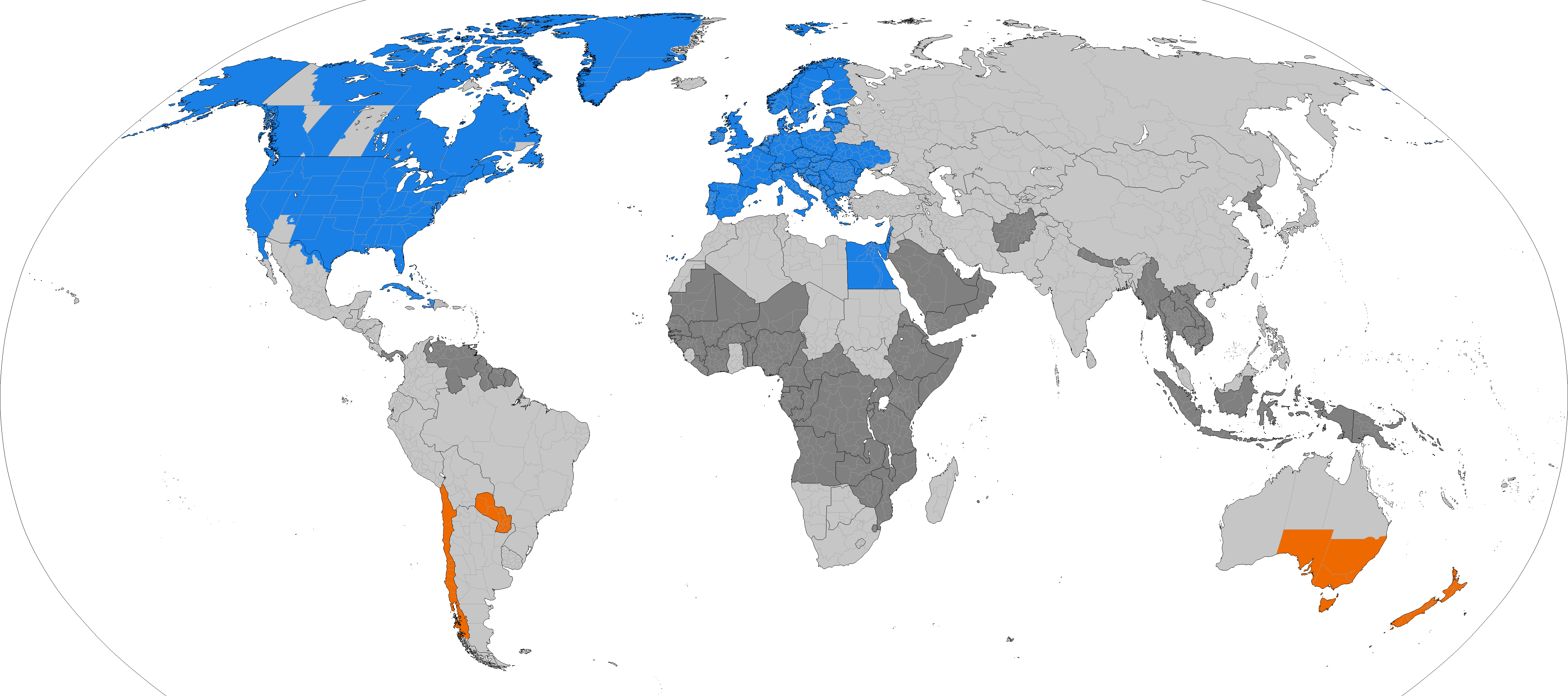
Daylight saving time (DST), also referred to as daylight savings time or simply daylight time (United States, Canada, and Australia), and summer time (United Kingdom, European Union, and others), is the practice of advancing clocks (typically by one hour) during warmer months so that darkness falls at a later clock time. The typical implementation of DST is to set clocks forward by one hour in the spring ("spring forward"), and to set clocks back by one hour in the fall ("fall back") to return to standard time. As a result, there is one 23-hour day in early spring and one 25-hour day in the middle of autumn. The idea of aligning waking hours to daylight hours to conserve candles was first proposed in 1784 by U.S. polymath Benjamin Franklin. In a satirical letter to the editor of ''The Journal of Paris'', Franklin suggested that waking up earlier in the summer would economize on candle usage; and calculated considerable savings. In 1895, New Zealand entomologist and astronome ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Time Zone
A time zone is an area which observes a uniform standard time for legal, Commerce, commercial and social purposes. Time zones tend to follow the boundaries between Country, countries and their Administrative division, subdivisions instead of strictly following longitude, because it is convenient for areas in frequent communication to keep the same time. All time zones are defined as offsets from Coordinated Universal Time (UTC), ranging from UTC−12:00 to UTC+14:00. The UTC offset, offsets are usually a whole number of hours, but a few zones are offset by an additional 30 or 45 minutes, such as in Indian Standard Time, India, Time in Australia, South Australia and Nepal Time, Nepal. Some areas of higher latitude use daylight saving time for about half of the year, typically by adding one hour to local time during spring (season), spring and summer. List of UTC offsets In the table below, the locations that use daylight saving time (DST) are listed in their UTC offse ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Leap Second
A leap second is a one-second adjustment that is occasionally applied to Coordinated Universal Time (UTC), to accommodate the difference between precise time (International Atomic Time (TAI), as measured by atomic clocks) and imprecise observed solar time (UT1), which varies due to irregularities and long-term slowdown in the Earth's rotation. The UTC time standard, widely used for international timekeeping and as the reference for civil time in most countries, uses TAI and consequently would run ahead of observed solar time unless it is reset to UT1 as needed. The leap second facility exists to provide this adjustment. The leap second was introduced in 1972 and since then 27 leap seconds have been added to UTC. Because the Earth's rotation speed varies in response to climatic and geological events, UTC leap seconds are irregularly spaced and unpredictable. Insertion of each UTC leap second is usually decided about six months in advance by the International Earth Rotation and ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Multicasting
In computer networking, multicast is group communication where data transmission is addressed to a group of destination computers simultaneously. Multicast can be one-to-many or many-to-many distribution. Multicast should not be confused with physical layer point-to-multipoint communication. Group communication may either be application layer multicast or network-assisted multicast, where the latter makes it possible for the source to efficiently send to the group in a single transmission. Copies are automatically created in other network elements, such as routers, switches and cellular network base stations, but only to network segments that currently contain members of the group. Network assisted multicast may be implemented at the data link layer using one-to-many addressing and switching such as Ethernet multicast addressing, Asynchronous Transfer Mode (ATM), point-to-multipoint virtual circuits (P2MP) or InfiniBand multicast. Network-assisted multicast may also be impl ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Broadcasting (networking)
In computer networking, telecommunication and information theory, broadcasting is a method of transferring a message to all recipients simultaneously. Broadcasting can be performed as a high-level operation in a program, for example, broadcasting in Message Passing Interface, or it may be a low-level networking operation, for example broadcasting on Ethernet. All-to-all communication is a computer communication method in which each sender transmits messages to all receivers within a group. In networking this can be accomplished using broadcast or multicast. This is in contrast with the point-to-point method in which each sender communicates with one receiver. Addressing methods There are four principal addressing methods in the Internet Protocol: Overview In computer networking, broadcasting refers to transmitting a packet that will be received by every device on the network. In practice, the scope of the broadcast is limited to a broadcast domain. Broadcasting is the ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Port Number
In computer networking, a port is a number assigned to uniquely identify a connection endpoint and to direct data to a specific service. At the software level, within an operating system, a port is a logical construct that identifies a specific process or a type of network service. A port is identified for each transport protocol and address combination by a 16-bit unsigned number, known as the port number. The most common transport protocols that use port numbers are the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP). A port number is always associated with an IP address of a host and the type of transport protocol used for communication. It completes the destination or origination network address of a message. Specific port numbers are reserved to identify specific services so that an arriving packet can be easily forwarded to a running application. For this purpose, port numbers lower than 1024 identify the historically most commonly used services a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |