|
List Of Well-known Ports (computing)
This is a list of TCP and UDP port numbers used by protocols for operation of network applications. The Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP) only need one port for duplex, bidirectional traffic. They usually use port numbers that match the services of the corresponding TCP or UDP implementation, if they exist. The Internet Assigned Numbers Authority (IANA) is responsible for maintaining the official assignments of port numbers for specific uses. However, many unofficial uses of both well-known and registered port numbers occur in practice. Similarly, many of the official assignments refer to protocols that were never or are no longer in common use. This article lists port numbers and their associated protocols that have experienced significant uptake. Table legend Well-known ports The port numbers in the range from 0 to 1023 (0 to 210 − 1) are the ''well-known ports'' or ''system ports''. They are used by system processes that provide w ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Transmission Control Protocol
The Transmission Control Protocol (TCP) is one of the main protocols of the Internet protocol suite. It originated in the initial network implementation in which it complemented the Internet Protocol (IP). Therefore, the entire suite is commonly referred to as TCP/IP. TCP provides reliable, ordered, and error-checked delivery of a stream of octets (bytes) between applications running on hosts communicating via an IP network. Major internet applications such as the World Wide Web, email, remote administration, and file transfer rely on TCP, which is part of the Transport Layer of the TCP/IP suite. SSL/TLS often runs on top of TCP. TCP is connection-oriented, and a connection between client and server is established before data can be sent. The server must be listening (passive open) for connection requests from clients before a connection is established. Three-way handshake (active open), retransmission, and error detection adds to reliability but lengthens latency. Applica ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Discard Protocol
The Discard Protocol is a service in the Internet Protocol Suite defined in RFC 863. It was designed for testing, debugging, measurement, and host-management purposes. A host may send data to a host that supports the Discard Protocol on either Transmission Control Protocol (TCP) or User Datagram Protocol (UDP) port number 9. The data sent to the server is simply discarded. No response is returned. For this reason, UDP is usually used, but TCP allows the services to be accessible on session-oriented connections (for example via HTTP proxies or some virtual private network (VPN)). Inetd implementation On most Unix-like operating systems a discard server is built into the inetd (or xinetd) daemon. The discard service is usually not enabled by default. It may be enabled by adding the following lines to the file and reloading the configuration: discard stream tcp nowait root internal discard dgram udp wait root internal The Discard Protocol is the TCP/UD ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
SSH File Transfer Protocol
In computing, the SSH File Transfer Protocol (also known as Secure File Transfer Protocol or SFTP) is a network protocol that provides file access, file transfer, and file management over any reliable data stream. It was designed by the Internet Engineering Task Force (IETF) as an extension of the Secure Shell protocol (SSH) version 2.0 to provide secure file transfer capabilities. The IETF Internet Draft states that, even though this protocol is described in the context of the SSH-2 protocol, it could be used in a number of different applications, such as secure file transfer over Transport Layer Security (TLS) and transfer of management information in VPN applications. This protocol assumes that it is run over a secure channel, such as SSH, that the server has already authenticated the client, and that the identity of the client user is available to the protocol. Capabilities Compared to the SCP protocol, which only allows file transfers, the SFTP protocol allows for a range of ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Secure Copy
Secure copy protocol (SCP) is a means of securely transferring computer files between a local host and a remote host or between two remote hosts. It is based on the Secure Shell (SSH) protocol. "SCP" commonly refers to both the Secure Copy Protocol and the program itself. According to OpenSSH developers in April 2019, SCP is outdated, inflexible and not readily fixed; they recommend the use of more modern protocols like SFTP and rsync for file transfer. As of OpenSSH version 9.0, scp client therefore uses SFTP for file transfers by default instead of the legacy SCP/RCP protocol. Secure Copy Protocol The SCP is a network protocol, based on the BSD RCP protocol, which supports file transfers between hosts on a network. SCP uses Secure Shell (SSH) for data transfer and uses the same mechanisms for authentication, thereby ensuring the authenticity and confidentiality of the data in transit. A client can send (upload) files to a server, optionally including their basic attribut ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
File Transfer
File transfer is the transmission of a computer file through a communication channel from one computer system to another. Typically, file transfer is mediated by a communications protocol. In the history of computing, numerous file transfer protocols have been designed for different contexts. Protocols A file transfer protocol is a convention that describes how to transfer files between two computing endpoints. As well as the stream of bits from a file stored as a single unit in a file system, some may also send relevant metadata such as the filename, file size and timestamp - and even file system permissions and file attributes. Some examples: * FTP is an older cross-platform file transfer protocol * SSH File Transfer Protocol a file transfer protocol secured by the Secure Shell (SSH) protocol * Secure copy (''scp'') is based on the Secure Shell (SSH) protocol * HTTP can support file transfer * Bittorrent, Gnutella and other distributed file transfers systems use peer-to-peer * ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
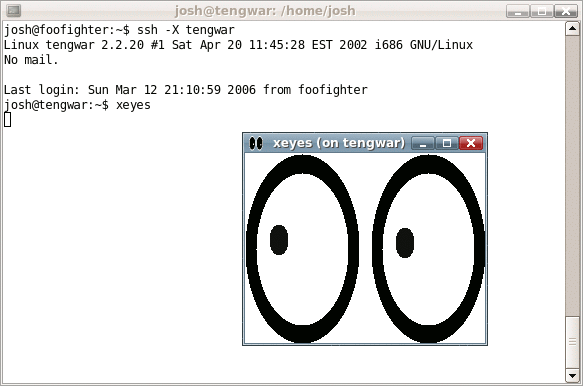
Secure Shell
The Secure Shell Protocol (SSH) is a cryptographic network protocol for operating network services securely over an unsecured network. Its most notable applications are remote login and command-line execution. SSH applications are based on a client–server architecture, connecting an SSH client instance with an SSH server. SSH operates as a layered protocol suite comprising three principal hierarchical components: the ''transport layer'' provides server authentication, confidentiality, and integrity; the ''user authentication protocol'' validates the user to the server; and the ''connection protocol'' multiplexes the encrypted tunnel into multiple logical communication channels. SSH was designed on Unix-like operating systems, as a replacement for Telnet and for unsecured remote Unix shell protocols, such as the Berkeley Remote Shell (rsh) and the related rlogin and rexec protocols, which all use insecure, plaintext transmission of authentication tokens. SSH was first de ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
File Transfer Protocol
The File Transfer Protocol (FTP) is a standard communication protocol used for the transfer of computer files from a server to a client on a computer network. FTP is built on a client–server model architecture using separate control and data connections between the client and the server. FTP users may authenticate themselves with a clear-text sign-in protocol, normally in the form of a username and password, but can connect anonymously if the server is configured to allow it. For secure transmission that protects the username and password, and encrypts the content, FTP is often secured with SSL/TLS (FTPS) or replaced with SSH File Transfer Protocol (SFTP). The first FTP client applications were command-line programs developed before operating systems had graphical user interfaces, and are still shipped with most Windows, Unix, and Linux operating systems. Many dedicated FTP clients and automation utilities have since been developed for desktops, servers, mobile devices, ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Character Generator Protocol
The Character Generator Protocol (CHARGEN) is a service of the Internet Protocol Suite defined in in 1983 by Jon Postel. It is intended for testing, debugging, and measurement purposes. The protocol is rarely used, as its design flaws allow ready misuse. A host may connect to a server that supports the Character Generator Protocol on either Transmission Control Protocol (TCP) or User Datagram Protocol (UDP) port number 19. Upon opening a TCP connection, the server starts sending arbitrary characters to the connecting host and continues until the host closes the connection. In the UDP implementation of the protocol, the server sends a UDP datagram containing a random number (between 0 and 512) of characters every time it receives a datagram from the connecting host. Any data received by the server is discarded. Inetd implementation On most Unix-like operating systems, a CHARGEN server is built into the inetd or xinetd daemon. The CHARGEN service is usually not enabled by defaul ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Message Send Protocol
The Message Send Protocol (MSP) is an application layer protocol used to send a short message between nodes on a network. The original version of the protocol was published in 1990. It was updated as Message Send Protocol 2 in 1992. TCP-based service One message send service is defined as a connection-based application on TCP. A service listens for TCP connections on port 18. Once a connection is established, a short message is transmitted from the sender to the receiver over the connection. The sender closes the connection after sending the message. UDP-based service Another message send service is defined as a datagram-based application on UDP. A service listens for UDP datagrams on port 18. When a datagram is received by the receiver, an answering datagram is sent back to the sender containing exactly the same data. See also * LAN Messenger * List of TCP and UDP port numbers * SMTP The Simple Mail Transfer Protocol (SMTP) is an Internet standard communication pr ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
QOTD
The Quote of the Day (QOTD) service is a member of the Internet protocol suite, defined in RFC 865. As indicated there, the QOTD concept predated the specification, when QOTD was used by mainframe sysadmins to broadcast a daily quote on request by a user. It was then formally codified both for prior purposes as well as for testing and measurement purposes. A host may connect to a server that supports the QOTD protocol, on either TCP or UDP port 17. To keep the quotes at a reasonable length, RFC 865 specifies a maximum of 512 octets for the quote. Although some sources indicate that the QOTD service is rarely enabled, and is in any case often firewalled to avoid denial-of-service attacks, interest continues in the pre-existing purpose of serving quotes as can be seen with web engine searches. Current testing and measurement of IP networks is more commonly done with ping and traceroute, which are more robust adaptations of the echo protocol The Echo Protocol is a service in t ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Netstat
In computing, netstat (''network statistics'') is a command-line network utility that displays network connections for Transmission Control Protocol (both incoming and outgoing), routing tables, and a number of network interface (network interface controller or software-defined network interface) and network protocol statistics. It is available on Unix, Plan 9, Inferno, and Unix-like operating systems including macOS, Linux, Solaris and BSD. It is also available on IBM OS/2 and on Microsoft Windows NT-based operating systems including Windows XP, Windows Vista, Windows 7, Windows 8 and Windows 10. It is used for finding problems in the network and to determine the amount of traffic on the network as a performance measurement. On Linux this program is mostly obsolete, although still included in many distributions. On Linux, netstat (part of "net-tools") is superseded by ss (part of iproute2). The replacement for netstat -r is ip route, the replacement for netstat -i is ip -s ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |
Daytime Protocol
The Daytime Protocol is a service in the Internet Protocol Suite, defined in 1983 in RFC 867. It is intended for testing and measurement purposes in computer networks. A host may connect to a server that supports the Daytime Protocol on either Transmission Control Protocol (TCP) or User Datagram Protocol (UDP) port 13. The server returns an ASCII character string of the current date and time in an unspecified format. Inetd implementation On UNIX-like operating systems a daytime server is usually built into the inetd (or xinetd) daemon. The service is usually not enabled by default. It may be enabled by adding the following lines to the file {{mono, /etc/inetd.conf and telling inetd to reload its configuration: daytime stream tcp nowait root internal daytime dgram udp wait root internal An example output may be: Thursday, February 2, 2006 13:45:51-PST See also * List of well-known ports * Echo Protocol * QOTD * Time Protocol The Time Protocol is a ... [...More Info...] [...Related Items...] OR: [Wikipedia] [Google] [Baidu] |